LOK-IT Technical Overview
LOK-IT Technical Overview
LOK-IT Technical Overview
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
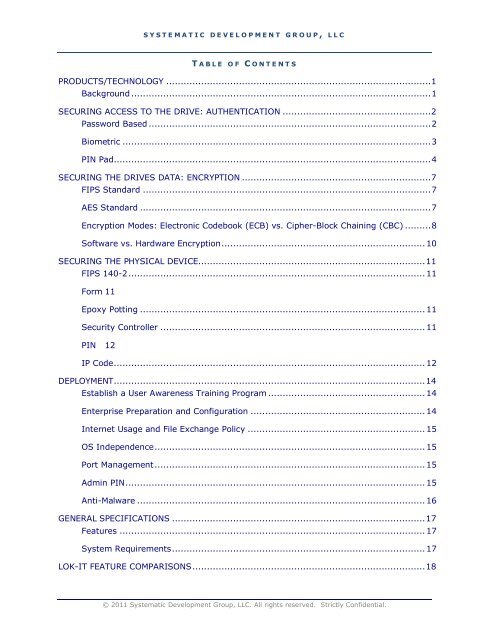
S Y S T E M A T I C D E V E L O P M E N T G R O U P , L L C<br />
T A B L E O F C O N T E N T S<br />
PRODUCTS/TECHNOLOGY ...........................................................................................1<br />
Background .......................................................................................................1<br />
SECURING ACCESS TO THE DRIVE: AUTHENTICATION ...................................................2<br />
Password Based .................................................................................................2<br />
Biometric ..........................................................................................................3<br />
PIN Pad.............................................................................................................4<br />
SECURING THE DRIVES DATA: ENCRYPTION .................................................................7<br />
FIPS Standard ...................................................................................................7<br />
AES Standard ....................................................................................................7<br />
Encryption Modes: Electronic Codebook (ECB) vs. Cipher-Block Chaining (CBC) .........8<br />
Software vs. Hardware Encryption...................................................................... 10<br />
SECURING THE PHYSICAL DEVICE..............................................................................11<br />
FIPS 140-2...................................................................................................... 11<br />
Form 11<br />
Epoxy Potting .................................................................................................. 11<br />
Security Controller ........................................................................................... 11<br />
PIN 12<br />
IP Code........................................................................................................... 12<br />
DEPLOYMENT...........................................................................................................14<br />
Establish a User Awareness Training Program ...................................................... 14<br />
Enterprise Preparation and Configuration ............................................................ 14<br />
Internet Usage and File Exchange Policy ............................................................. 15<br />
OS Independence............................................................................................. 15<br />
Port Management............................................................................................. 15<br />
Admin PIN....................................................................................................... 15<br />
Anti-Malware ................................................................................................... 16<br />
GENERAL SPECIFICATIONS .......................................................................................17<br />
Features ......................................................................................................... 17<br />
System Requirements....................................................................................... 17<br />
<strong>LOK</strong>-<strong>IT</strong> FEATURE COMPARISONS................................................................................18<br />
© 2011 Systematic Development Group, LLC. All rights reserved. Strictly Confidential.