Chapter 3 Linear Block Codes ∑
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
<strong>Chapter</strong> 3<br />
<strong>Linear</strong> <strong>Block</strong> <strong>Codes</strong><br />
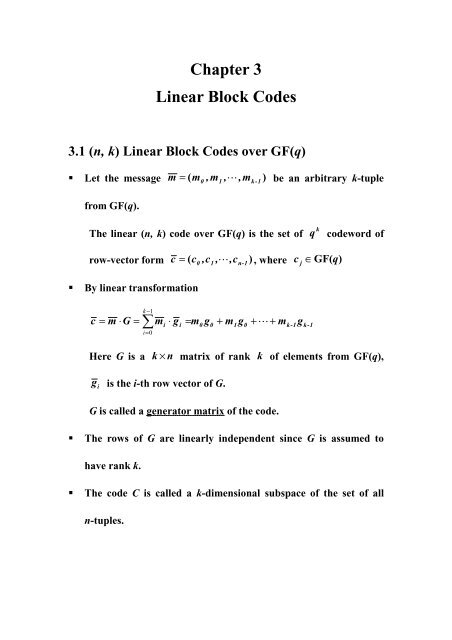
3.1 (n, k) <strong>Linear</strong> <strong>Block</strong> <strong>Codes</strong> over GF(q)<br />
Let the message m = m ,m , L,<br />
) be an arbitrary k-tuple<br />
from GF(q).<br />
(<br />
0 1<br />
mk-1<br />
The linear (n, k) codeoverGF(q) isthesetof<br />
k<br />
q<br />
codeword of<br />
row-vector form c = c ,c , L,<br />
) ,where c j<br />
∈GF(q)<br />
(<br />
0 1<br />
cn-1<br />
<br />
By linear transformation<br />
k<br />
1<br />
c = m ⋅G<br />
= <strong>∑</strong> − mi<br />
⋅ gi<br />
= m0<br />
g0<br />
+ m1g0<br />
+ L+<br />
m<br />
i=<br />
0<br />
k-1<br />
g<br />
k-1<br />
Here G is a<br />
k × n<br />
matrix of rank k of elements from GF(q),<br />
gi<br />
is the i-th row vector of G.<br />
G is called a generator matrix of the code.<br />
<br />
The rows of G are linearly independent since G is assumed to<br />
have rank k.<br />
<br />
The code C is called a k-dimensional subspace of the set of all<br />
n-tuples.
Example:<br />
(7, 4) Hamming code over GF(2)<br />
The encoding equation for this code is given by<br />
c<br />
c<br />
c<br />
c<br />
c<br />
c<br />
c<br />
0<br />
1<br />
2<br />
3<br />
4<br />
5<br />
6<br />
= m<br />
= m<br />
= m<br />
= m<br />
= m<br />
= m<br />
= m<br />
that is,<br />
0<br />
1<br />
2<br />
3<br />
0<br />
1<br />
0<br />
+ m<br />
+ m<br />
+ m<br />
1<br />
2<br />
1<br />
+ m<br />
+ m<br />
+ m<br />
2<br />
3<br />
3<br />
⎡1<br />
⎢<br />
0<br />
G = ⎢<br />
⎢0<br />
⎢<br />
⎣0<br />
0<br />
1<br />
0<br />
0<br />
0<br />
0<br />
1<br />
0<br />
0<br />
0<br />
0<br />
1<br />
1<br />
1<br />
1<br />
0<br />
0<br />
1<br />
1<br />
1<br />
1⎤<br />
1<br />
⎥<br />
⎥<br />
0⎥<br />
⎥<br />
1⎦<br />
<br />
An (n, k) block code is said to be linear if the vector sum of two<br />
codeword is a codeword.<br />
<br />
<strong>Linear</strong> Systematic <strong>Block</strong> Code:<br />
In systematic from the codeword C is comprised of an<br />
information segment and a set of n-k symbols that are linear<br />
combinations of certain information symbols, determined by the<br />
P matrix. That is
c = ;for 0 ≤ i < k<br />
i<br />
m i<br />
k<br />
1<br />
= <strong>∑</strong> − c<br />
i<br />
m<br />
j<br />
p<br />
j, n-k-i ;for k ≤ i < n<br />
j=<br />
0<br />
message<br />
codeword<br />
( m0 ,m1<br />
, ,mk-1<br />
) ↔ ( m0<br />
,m1<br />
, L,mk-1,<br />
ck<br />
,ck<br />
1<br />
, L,<br />
cn-1<br />
)<br />
L<br />
+<br />
The second set of equations, given above, is called the set of<br />
parity-check equations.<br />
An (n, k) linear systematic code is completely specified by a k × n<br />
generator matrix of the following form<br />
⎡ g<br />
⎢<br />
g<br />
G = ⎢<br />
⎢ M<br />
⎢<br />
⎣g<br />
0<br />
1<br />
k-1<br />
⎤<br />
⎥<br />
⎥ =<br />
⎥<br />
⎥<br />
⎦<br />
[ I P]<br />
k<br />
where<br />
I<br />
k is the k × k<br />
identity matrix<br />
⎡ p<br />
⎢<br />
p<br />
P = ⎢<br />
⎢<br />
⎢<br />
⎣ p(<br />
0, ( n-k-1)<br />
1, ( n-k-1)<br />
M<br />
k-1)<br />
,(<br />
n-k-1)<br />
p<br />
p<br />
p<br />
0, ( n-k-2)<br />
1, ( n-k-2)<br />
( k-1)<br />
,(<br />
n-k-2)<br />
P -matrix is a k × ( n - k)<br />
M<br />
L<br />
L<br />
O<br />
L<br />
matrix.<br />
p<br />
p<br />
p<br />
0,0<br />
1,0<br />
M<br />
( k-1)<br />
,0<br />
⎤<br />
⎥<br />
⎥<br />
⎥<br />
⎥<br />
⎦
Parity-check matrix<br />
An (n, k) linear code can also be specified by an<br />
( n - k)<br />
× k<br />
matrix H.<br />
Let c = c ,c , L,<br />
) be an n-tuple<br />
(<br />
0 1<br />
cn-1<br />
then c is a codeword if and only if<br />
T<br />
c ⋅ H = ( 0,0,<br />
14243<br />
L ,0)<br />
n−k<br />
i.e. the inner product of c and each row of H is zero.<br />
The matrix H is called a parity-check matrix.<br />
Since G = [ I P]<br />
k<br />
we can see that H = [ P ]<br />
T I<br />
n-k<br />
where<br />
T<br />
P<br />
is the transpose of P<br />
and G ⋅ H<br />
T = 0 .<br />
Note: For any given generator matrix G, many solution for H are<br />
possible.
Example:<br />
A(6, 3) code is generated by<br />
⎡1<br />
G =<br />
⎢<br />
0<br />
⎢<br />
⎢⎣<br />
0<br />
0<br />
1<br />
0<br />
0<br />
0<br />
1<br />
1<br />
1<br />
0<br />
1<br />
0<br />
1<br />
1⎤<br />
1<br />
⎥<br />
⎥<br />
1⎥⎦<br />
The parity-check matrix is given by<br />
H<br />
⎡1<br />
=<br />
⎢<br />
1<br />
⎢<br />
⎢⎣<br />
1<br />
1<br />
0<br />
1<br />
0<br />
1<br />
1<br />
1<br />
0<br />
0<br />
0<br />
1<br />
0<br />
0⎤<br />
0<br />
⎥<br />
⎥<br />
1⎥⎦<br />
A code generated by H is called the dual code of the code<br />
generated by G.<br />
A dual code is denoted as<br />
⊥<br />
C .
3.2 Hamming Distance of <strong>Linear</strong> <strong>Block</strong> Code and<br />
Error Protection Properties<br />
<br />
Distance between two n-symbol vectors<br />
u<br />
v<br />
= ( u ,u , L,<br />
) 1<br />
0 1<br />
un-<br />
= ( v ,v , L,<br />
) 1<br />
0 1<br />
vn-<br />
(a) Euclidean distance<br />
d<br />
E<br />
( u, v ) =<br />
n-1<br />
<strong>∑</strong><br />
i=<br />
0<br />
( u<br />
i<br />
- v )<br />
i<br />
2<br />
(b) Hamming distance<br />
d<br />
H<br />
( u, v ) = { i | u ≠ v , i = 0,1, L,n - 1 }<br />
i<br />
i<br />
i.e. the number of places where u and v differ.<br />
<br />
Hamming weight and Hamming distance of codewords<br />
(a) For a linear code C, the Hamming distance between any two<br />
codewords is simply described by<br />
d<br />
H<br />
( c1<br />
, c2<br />
) = wt(<br />
c1<br />
- c2<br />
) = wt(<br />
c3<br />
)<br />
where c3<br />
is the difference between c1<br />
and c<br />
2 .<br />
wt( c 3<br />
) is the Hamming weights of c<br />
3 , or the number of<br />
nonzero positions of c<br />
3 .
(b) Triangle inequality<br />
For codeword a , b and c<br />
d<br />
H<br />
( a, c ) + d ( c, b ) ≥ d ( a, b )<br />
H<br />
H<br />
c<br />
a<br />
b<br />
(c) d H<br />
( a, b ) = wt(<br />
a + b )
3.3 Minimum distance of a <strong>Block</strong> code<br />
Let C be a linear block code. The minimum distance of C,<br />
denoted as<br />
d<br />
min , is defined as follows:<br />
d min<br />
≡ min{ d(<br />
v, u) : v, u ∈C,<br />
v ≠ u}<br />
The minimum weight of C, denoted as<br />
w<br />
min<br />
, is defined as<br />
follows:<br />
w min<br />
≡ min{ w(<br />
v ) : v ∈C,<br />
v ≠ 0 }<br />
Exercise:<br />
Show that<br />
d = w<br />
min<br />
min<br />
Proof:<br />
d<br />
min<br />
≡ min{<br />
d(<br />
v, u) : v, u ∈C,<br />
v ≠ u}<br />
= min{<br />
d(<br />
v + u) :<br />
= min{<br />
w(<br />
x) : x ∈C,<br />
= w<br />
min<br />
v, u<br />
∈C,<br />
v ≠ u}<br />
x ≠ 0 }
3.4 maximum Error-Correction Capability of a <strong>Block</strong><br />
Code<br />
Suppose that c0<br />
is selected for transmission and that the closest<br />
codeword is<br />
dmin<br />
in Hamming distance, as shown below (Fig. 3.5<br />
page 87)<br />
<br />
<br />
<br />
<br />
<br />
c 1<br />
c 1<br />
c 2<br />
c 0<br />
<br />
<br />
<br />
<br />
<br />
<br />
<br />
<br />
<br />
c 0<br />
e<br />
c<br />
r = c +<br />
e<br />
e<br />
c<br />
= ( e ,e , L,<br />
) 1 : error pattern.<br />
0 1<br />
en-<br />
= ( c ,c , L,<br />
) 1 : codeword transmitted.<br />
0 1<br />
cn-<br />
r = ( r ,r , L,<br />
) 1 : received word.<br />
0 1<br />
rn-
If the channel-error pattern e has<br />
t<br />
⎢d<br />
=<br />
⎢<br />
⎣<br />
min<br />
− 1⎥<br />
2 ⎥ or fewer errors,<br />
⎦<br />
one is guaranteed that<br />
r = c + 0<br />
e remains closer in Hamming<br />
distance to c0<br />
than to any other codeword and thus is decoded<br />
correctly.<br />
⎢dmin<br />
− 1⎥<br />
As a consequence, t =<br />
⎢ ⎥<br />
⎣ 2 ⎦<br />
is called the maximum<br />
error-correction capability of the code.<br />
<br />
Error-detection Capability<br />
Suppose that the decoder’s task is only to detect the presence of<br />
errors, and if errors are detected, to label the codeword (received<br />
word) is unreliable.<br />
The detector’s function can fail only if e takes the transmitted<br />
codeword c 0 into another codeword c<br />
1 ,thatis c<br />
0<br />
+ e = c1<br />
.<br />
This cannot occur if there are d min<br />
− 1<br />
or fewer errors in the n<br />
positions of the code.<br />
That is, d min<br />
− 1<br />
is the guaranteed error detection capability of<br />
the code.
Hybrid modes of error control<br />
One can correct t errors and still detect up to<br />
t d<br />
errors provided<br />
that<br />
t + t d<br />
< d .<br />
min<br />
3.5 Weight Distribution<br />
Let C be an (n, k) linear block code and<br />
wmin<br />
denotes the<br />
number of codewords in C with Hamming weight i .<br />
Define<br />
n<br />
<strong>∑</strong><br />
W ( z)<br />
i<br />
= w z i as the weight enumerator polynomial.<br />
i=<br />
0<br />
Clearly, w 0<br />
= 1<br />
w =<br />
k<br />
0<br />
+ w1<br />
+ L+<br />
wn<br />
2<br />
Exercise:<br />
Find the weight enumerator polynomial of the (7, 4) Hamming<br />
code generated by<br />
⎡1<br />
⎢<br />
0<br />
G = ⎢<br />
⎢0<br />
⎢<br />
⎣0<br />
0<br />
1<br />
0<br />
0<br />
0<br />
0<br />
1<br />
0<br />
0<br />
0<br />
0<br />
1<br />
1<br />
1<br />
1<br />
0<br />
0<br />
1<br />
1<br />
1<br />
1⎤<br />
1<br />
⎥<br />
⎥<br />
0⎥<br />
⎥<br />
1⎦<br />
Answer:<br />
3 4<br />
W ( z)<br />
= 1 + 7z + 7z +<br />
z<br />
7
3.6 Some Commonly-used Modifications of <strong>Linear</strong><br />
<strong>Codes</strong><br />
<br />
Shortened code<br />
A code is shortened by deleting some message symbols (bits) from<br />
the encoding process.<br />
For example, by deleting one message symbol (or bit), an (n, k)<br />
code becomes an (n-1, k-1)code.<br />
Extended code<br />
A code is extended by adding some additional redundant symbols<br />
(or bits).<br />
For example, by adding one parity symbol, a (n, k) codebecomes<br />
a (n+1, k) code.<br />
In general, the error-control capability of the extended code can<br />
be increased.
Punctured Code<br />
A code is punctured by deleting some of its parity symbols (or<br />
bits).<br />
For example, by deleting one parity symbol, a (n, k) code<br />
becomes (n-1, k)code.<br />
In general, the error-control capability is reduced, but the code<br />
rate is increased.