Effect of Noise on image steganography based on LSB ... - IOSRJEN
Effect of Noise on image steganography based on LSB ... - IOSRJEN
Effect of Noise on image steganography based on LSB ... - IOSRJEN
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
IOSR Journal <str<strong>on</strong>g>of</str<strong>on</strong>g> Engineering<br />
Mar. 2012, Vol. 2(3) pp: 473-477<br />
When these <strong>image</strong>s are transmitted through AWGN channel,<br />
noises are introduced in it, thereby this stego <strong>image</strong>s may be<br />
corrupted by noise and also hidden secret data bits are affected<br />
by that noise. The experimental results have shown in table 4,<br />
5, and 6 that how much stego bits and data bits are corrupted<br />
by noise. The size <str<strong>on</strong>g>of</str<strong>on</strong>g> <strong>image</strong> is 256x256 i.e.65536 total no <str<strong>on</strong>g>of</str<strong>on</strong>g><br />
pixels or 524288 data streams are transmitted through noisy<br />
channel. Additive white Gaussian noises are used in this<br />
experiment. The characteristic <str<strong>on</strong>g>of</str<strong>on</strong>g> this communicati<strong>on</strong> system<br />
with bit error rate (BER) versus signal noise ratio (SNR, E b /N 0 ,<br />
dB), where E 0 is energy per bit and N 0 is noise spectral<br />
density. Such a c<strong>on</strong>trolled noise was added in every channel<br />
and that stego <strong>image</strong> is transmitted over the channel bit by bit.<br />
The number <str<strong>on</strong>g>of</str<strong>on</strong>g> error bits was measured at every c<strong>on</strong>trolled<br />
noise level to obtain BERs for test <strong>image</strong> during the stego<br />
<strong>image</strong> transmissi<strong>on</strong>. The received stego bits are used to<br />
rec<strong>on</strong>struct the stego <strong>image</strong>, and extract secret data bits by<br />
using decrypti<strong>on</strong> algorithm. The error correcti<strong>on</strong> results <str<strong>on</strong>g>of</str<strong>on</strong>g> the<br />
proposed method are given in the table 4, 5, 6.<br />
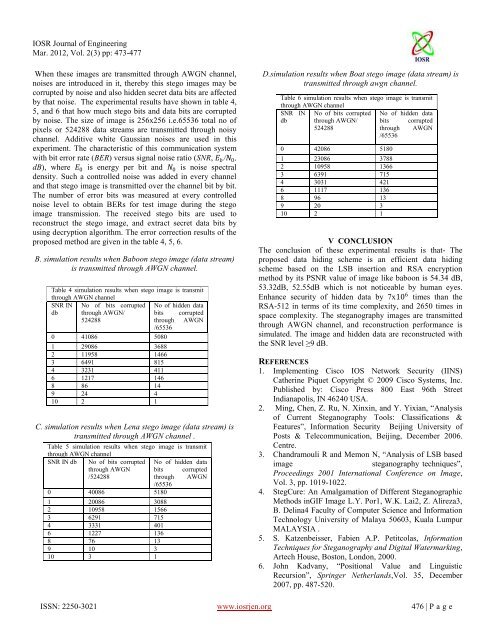
B. simulati<strong>on</strong> results when Babo<strong>on</strong> stego <strong>image</strong> (data stream)<br />
is transmitted through AWGN channel.<br />
Table 4 simulati<strong>on</strong> results when stego <strong>image</strong> is transmit<br />
through AWGN channel<br />
SNR IN No <str<strong>on</strong>g>of</str<strong>on</strong>g> bits corrupted No <str<strong>on</strong>g>of</str<strong>on</strong>g> hidden data<br />
db through AWGN/ bits corrupted<br />
524288<br />
through AWGN<br />
/65536<br />
0 41086 5080<br />
1 29086 3688<br />
2 11958 1466<br />
3 6491 815<br />
4 3231 411<br />
6 1217 146<br />
8 86 14<br />
9 24 4<br />
10 2 1<br />
C. simulati<strong>on</strong> results when Lena stego <strong>image</strong> (data stream) is<br />
transmitted through AWGN channel .<br />
Table 5 simulati<strong>on</strong> results when stego <strong>image</strong> is transmit<br />
through AWGN channel<br />
SNR IN db No <str<strong>on</strong>g>of</str<strong>on</strong>g> bits corrupted No <str<strong>on</strong>g>of</str<strong>on</strong>g> hidden data<br />
through AWGN bits corrupted<br />
/524288<br />
through AWGN<br />
/65536<br />
0 40086 5180<br />
1 20086 3088<br />
2 10958 1566<br />
3 6291 715<br />
4 3331 401<br />
6 1227 136<br />
8 76 13<br />
9 10 3<br />
10 3 1<br />
D.simulati<strong>on</strong> results when Boat stego <strong>image</strong> (data stream) is<br />
transmitted through awgn channel.<br />
Table 6 simulati<strong>on</strong> results when stego <strong>image</strong> is transmit<br />
through AWGN channel<br />
SNR IN No <str<strong>on</strong>g>of</str<strong>on</strong>g> bits corrupted No <str<strong>on</strong>g>of</str<strong>on</strong>g> hidden data<br />
db through AWGN/ bits corrupted<br />
524288<br />
through AWGN<br />
/65536<br />
0 42086 5180<br />
1 23086 3788<br />
2 10958 1366<br />
3 6391 715<br />
4 3031 421<br />
6 1117 136<br />
8 96 13<br />
9 20 3<br />
10 2 1<br />
V CONCLUSION<br />
The c<strong>on</strong>clusi<strong>on</strong> <str<strong>on</strong>g>of</str<strong>on</strong>g> these experimental results is that- The<br />
proposed data hiding scheme is an efficient data hiding<br />
scheme <strong>based</strong> <strong>on</strong> the <strong>LSB</strong> inserti<strong>on</strong> and RSA encrypti<strong>on</strong><br />
method by its PSNR value <str<strong>on</strong>g>of</str<strong>on</strong>g> <strong>image</strong> like babo<strong>on</strong> is 54.34 dB,<br />
53.32dB, 52.55dB which is not noticeable by human eyes.<br />
Enhance security <str<strong>on</strong>g>of</str<strong>on</strong>g> hidden data by 7x10 6 times than the<br />
RSA-512 in terms <str<strong>on</strong>g>of</str<strong>on</strong>g> its time complexity, and 2650 times in<br />
space complexity. The <strong>steganography</strong> <strong>image</strong>s are transmitted<br />
through AWGN channel, and rec<strong>on</strong>structi<strong>on</strong> performance is<br />
simulated. The <strong>image</strong> and hidden data are rec<strong>on</strong>structed with<br />
the SNR level ≥9 dB.<br />
REFERENCES<br />
1. Implementing Cisco IOS Network Security (IINS)<br />
Catherine Piquet Copyright © 2009 Cisco Systems, Inc.<br />
Published by: Cisco Press 800 East 96th Street<br />
Indianapolis, IN 46240 USA.<br />
2. Ming, Chen, Z. Ru, N. Xinxin, and Y. Yixian, “Analysis<br />
<str<strong>on</strong>g>of</str<strong>on</strong>g> Current Steganography Tools: Classificati<strong>on</strong>s &<br />
Features”, Informati<strong>on</strong> Security Beijing University <str<strong>on</strong>g>of</str<strong>on</strong>g><br />
Posts & Telecommunicati<strong>on</strong>, Beijing, December 2006.<br />
Centre.<br />
3. Chandramouli R and Mem<strong>on</strong> N, “Analysis <str<strong>on</strong>g>of</str<strong>on</strong>g> <strong>LSB</strong> <strong>based</strong><br />
<strong>image</strong><br />
<strong>steganography</strong> techniques”,<br />
Proceedings 2001 Internati<strong>on</strong>al C<strong>on</strong>ference <strong>on</strong> Image,<br />
Vol. 3, pp. 1019-1022.<br />
4. StegCure: An Amalgamati<strong>on</strong> <str<strong>on</strong>g>of</str<strong>on</strong>g> Different Steganographic<br />
Methods inGIF Image L.Y. Por1, W.K. Lai2, Z. Alireza3,<br />
B. Delina4 Faculty <str<strong>on</strong>g>of</str<strong>on</strong>g> Computer Science and Informati<strong>on</strong><br />
Technology University <str<strong>on</strong>g>of</str<strong>on</strong>g> Malaya 50603, Kuala Lumpur<br />
MALAYSIA .<br />
5. S. Katzenbeisser, Fabien A.P. Petitcolas, Informati<strong>on</strong><br />
Techniques for Steganography and Digital Watermarking,<br />
Artech House, Bost<strong>on</strong>, L<strong>on</strong>d<strong>on</strong>, 2000.<br />
6. John Kadvany, “Positi<strong>on</strong>al Value and Linguistic<br />
Recursi<strong>on</strong>”, Springer Netherlands,Vol. 35, December<br />
2007, pp. 487-520.<br />
ISSN: 2250-3021 www.iosrjen.org 476 | P a g e