Hong Kong's leading CIOs of 2011 - enterpriseinnovation.net
Hong Kong's leading CIOs of 2011 - enterpriseinnovation.net
Hong Kong's leading CIOs of 2011 - enterpriseinnovation.net
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
SPECIAL: CLOUDCOMPUTING<br />
4 continued from page 24<br />
Injection; cross-site scripting; and broken<br />
authentication and session management.<br />
Clients need to take a more farsighted<br />
view <strong>of</strong> application development, said<br />
Lim. “Organizations want their new applications<br />
fast and cheap, but if they are<br />
fast and good, they can’t be cheap, and<br />
if they are fast and cheap, they can’t be<br />
good. Developers are not educated in secure<br />
coding and they forget that firewalls<br />
don’t stop application attacks.”<br />
Data leakage must be carefully guarded<br />
against when retaining cloud services.<br />
In some cases, cloud providers may outsource<br />
capacity so that users’ data may<br />
be processed by a 3rd party. “The worst<br />
thing is when your data is stored by a<br />
third party provider. If a hacker steals<br />
your customer data from the 3rd party,<br />
you are in big trouble—you may go to<br />
jail, but the cloud provider is in South<br />
America.”<br />
SLA issues<br />
Cloud SLAs should include continuity<br />
in case <strong>of</strong> catastrophe, said Lim.<br />
“For example, when Lehman Brothers<br />
suddenly closed in 2009, the IT<br />
staff who looked after hard disks full<br />
<strong>of</strong> transactions and customer data lost<br />
their jobs. So where did the data go—is<br />
it for sale on eBay”<br />
Another issue is data that is usually<br />
encrypted, so that when it is transmitted<br />
across the <strong>net</strong>work, it needs policy-based<br />
secure email, said Lim. “Paper documents<br />
should be protected by a classification<br />
label indicating their sensitivity,<br />
supported by a corporate policy on classified<br />
emails. Classified emails should<br />
be kept in an envelope when transported.<br />
And to guarantee that the email is authentic<br />
and has not been changed, we<br />
need to add a digital signature to important<br />
documents that are transmitted.”<br />
Lim advocates “intuitive email security”,<br />
using the same security classification<br />
and controls as for paper documents.<br />
“This minimizes user training,<br />
and provides centralized control through<br />
a security policy, logged entries that can<br />
be audited, and centralized key and certificate<br />
management.”<br />
Lim also drew attention to security<br />
education and standards, including a<br />
key facilitator for secure s<strong>of</strong>tware, the<br />
CSSLP Certification for Application Development<br />
Teams.<br />
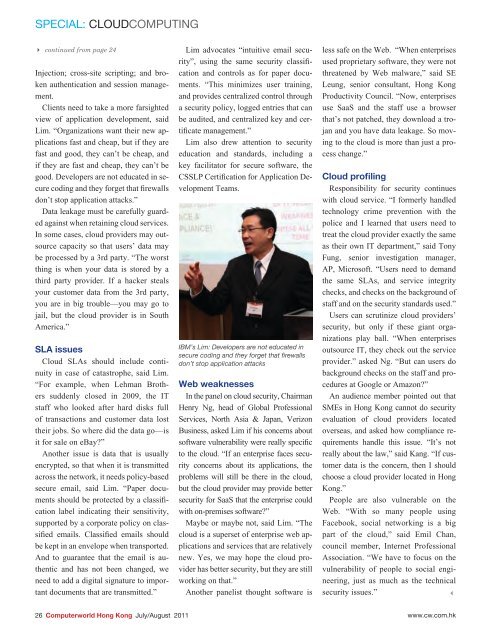
IBM’s Lim: Developers are not educated in<br />
secure coding and they forget that firewalls<br />
don’t stop application attacks<br />
Web weaknesses<br />
In the panel on cloud security, Chairman<br />
Henry Ng, head <strong>of</strong> Global Pr<strong>of</strong>essional<br />
Services, North Asia & Japan, Verizon<br />
Business, asked Lim if his concerns about<br />
s<strong>of</strong>tware vulnerability were really specific<br />
to the cloud. “If an enterprise faces security<br />
concerns about its applications, the<br />
problems will still be there in the cloud,<br />
but the cloud provider may provide better<br />
security for SaaS that the enterprise could<br />
with on-premises s<strong>of</strong>tware”<br />
Maybe or maybe not, said Lim. “The<br />
cloud is a superset <strong>of</strong> enterprise web applications<br />
and services that are relatively<br />
new. Yes, we may hope the cloud provider<br />
has better security, but they are still<br />
working on that.”<br />
Another panelist thought s<strong>of</strong>tware is<br />
less safe on the Web. “When enterprises<br />
used proprietary s<strong>of</strong>tware, they were not<br />
threatened by Web malware,” said SE<br />
Leung, senior consultant, <strong>Hong</strong> Kong<br />
Productivity Council. “Now, enterprises<br />
use SaaS and the staff use a browser<br />
that’s not patched, they download a trojan<br />
and you have data leakage. So moving<br />
to the cloud is more than just a process<br />
change.”<br />
Cloud pr<strong>of</strong>iling<br />
Responsibility for security continues<br />
with cloud service. “I formerly handled<br />
technology crime prevention with the<br />
police and I learned that users need to<br />
treat the cloud provider exactly the same<br />
as their own IT department,” said Tony<br />
Fung, senior investigation manager,<br />
AP, Micros<strong>of</strong>t. “Users need to demand<br />
the same SLAs, and service integrity<br />
checks, and checks on the background <strong>of</strong><br />
staff and on the security standards used.”<br />
Users can scrutinize cloud providers’<br />
security, but only if these giant organizations<br />
play ball. “When enterprises<br />
outsource IT, they check out the service<br />
provider.” asked Ng. “But can users do<br />
background checks on the staff and procedures<br />
at Google or Amazon”<br />
An audience member pointed out that<br />
SMEs in <strong>Hong</strong> Kong cannot do security<br />
evaluation <strong>of</strong> cloud providers located<br />
overseas, and asked how compliance requirements<br />
handle this issue. “It’s not<br />
really about the law,” said Kang. “If customer<br />
data is the concern, then I should<br />
choose a cloud provider located in <strong>Hong</strong><br />
Kong.”<br />
People are also vulnerable on the<br />
Web. “With so many people using<br />
Facebook, social <strong>net</strong>working is a big<br />
part <strong>of</strong> the cloud,” said Emil Chan,<br />
council member, Inter<strong>net</strong> Pr<strong>of</strong>essional<br />
Association. “We have to focus on the<br />
vulnerability <strong>of</strong> people to social engineering,<br />
just as much as the technical<br />
security issues.” 3<br />
C<br />
M<br />
Y<br />
CM<br />
MY<br />
CY<br />
CMY<br />
K<br />
26 Computerworld <strong>Hong</strong> Kong July/August <strong>2011</strong> www.cw.com.hk