IBM Class Author book content - IBM Learner Portal
IBM Class Author book content - IBM Learner Portal
IBM Class Author book content - IBM Learner Portal
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
V5.4<br />
Uempty<br />
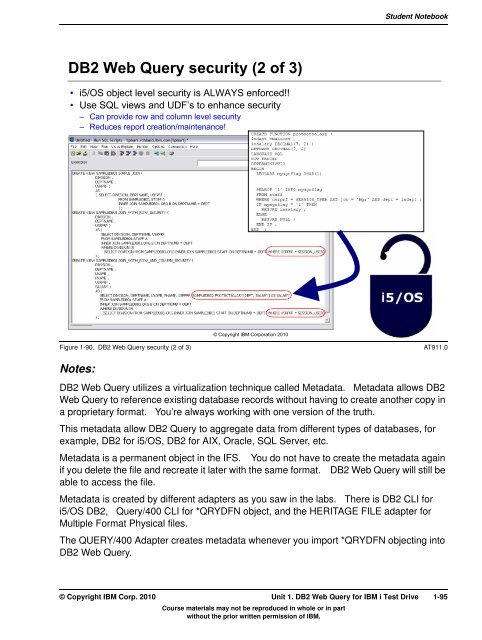
DB2 Web Query security (2 of 3)<br />
• i5/OS object level security is ALWAYS enforced!!<br />
• Use SQL views and UDF’s to enhance security<br />
– Can provide row and column level security<br />
– Reduces report creation/maintenance!<br />
Course materials may not be reproduced in whole or in part<br />
without the prior written permission of <strong>IBM</strong>.<br />
Student Note<strong>book</strong><br />
Figure 1-90. DB2 Web Query security (2 of 3) AT911.0<br />
Notes:<br />
© Copyright <strong>IBM</strong> Corporation 2010<br />
DB2 Web Query utilizes a virtualization technique called Metadata. Metadata allows DB2<br />
Web Query to reference existing database records without having to create another copy in<br />
a proprietary format. You’re always working with one version of the truth.<br />
This metadata allow DB2 Query to aggregate data from different types of databases, for<br />
example, DB2 for i5/OS, DB2 for AIX, Oracle, SQL Server, etc.<br />
Metadata is a permanent object in the IFS. You do not have to create the metadata again<br />
if you delete the file and recreate it later with the same format. DB2 Web Query will still be<br />
able to access the file.<br />
Metadata is created by different adapters as you saw in the labs. There is DB2 CLI for<br />
i5/OS DB2, Query/400 CLI for *QRYDFN object, and the HERITAGE FILE adapter for<br />
Multiple Format Physical files.<br />
The QUERY/400 Adapter creates metadata whenever you import *QRYDFN objecting into<br />
DB2 Web Query.<br />
© Copyright <strong>IBM</strong> Corp. 2010 Unit 1. DB2 Web Query for <strong>IBM</strong> i Test Drive 1-95