ossim - AlienVault
ossim - AlienVault
ossim - AlienVault
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
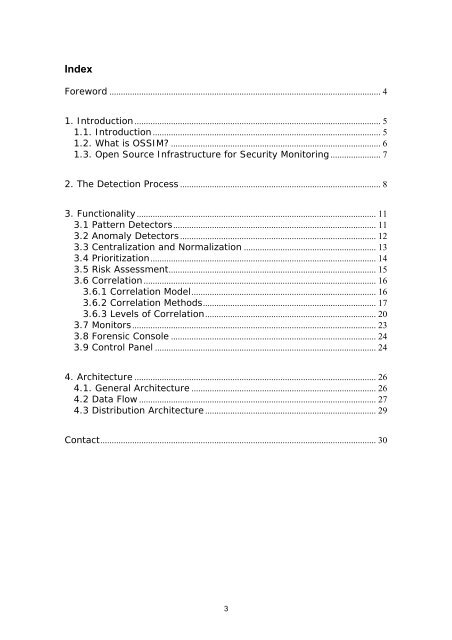
Index<br />
Foreword ....................................................................................................................... 4<br />
1. Introduction ............................................................................................................ 5<br />
1.1. Introduction .................................................................................................... 5<br />
1.2. What is OSSIM? ............................................................................................ 6<br />
1.3. Open Source Infrastructure for Security Monitoring ...................... 7<br />
2. The Detection Process ........................................................................................ 8<br />
3. Functionality ......................................................................................................... 11<br />
3.1 Pattern Detectors......................................................................................... 11<br />
3.2 Anomaly Detectors ...................................................................................... 12<br />
3.3 Centralization and Normalization .......................................................... 13<br />
3.4 Prioritization................................................................................................... 14<br />
3.5 Risk Assessment........................................................................................... 15<br />
3.6 Correlation ...................................................................................................... 16<br />
3.6.1 Correlation Model................................................................................. 16<br />
3.6.2 Correlation Methods............................................................................ 17<br />
3.6.3 Levels of Correlation........................................................................... 20<br />
3.7 Monitors........................................................................................................... 23<br />
3.8 Forensic Console .......................................................................................... 24<br />
3.9 Control Panel ................................................................................................. 24<br />
4. Architecture .......................................................................................................... 26<br />
4.1. General Architecture ................................................................................. 26<br />
4.2 Data Flow ........................................................................................................ 27<br />
4.3 Distribution Architecture ........................................................................... 29<br />
Contact......................................................................................................................... 30<br />
3