Building Collector Plugins 1.1 - AlienVault
Building Collector Plugins 1.1 - AlienVault
Building Collector Plugins 1.1 - AlienVault
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
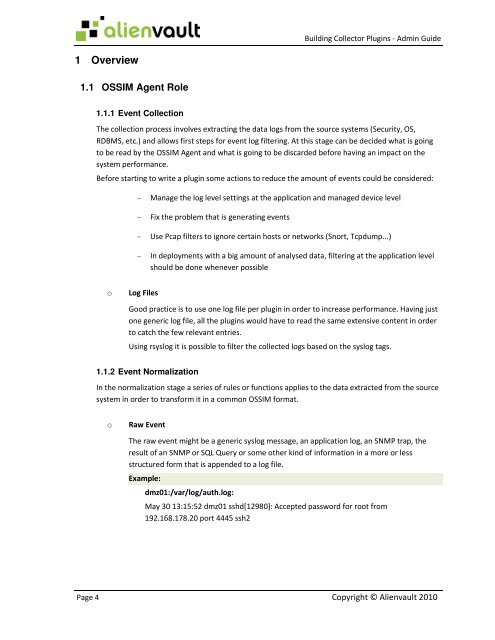
<strong>Building</strong> <strong>Collector</strong> <strong>Plugins</strong> - Admin Guide<br />
1 Overview<br />
<strong>1.1</strong> OSSIM Agent Role<br />
<strong>1.1</strong>.1 Event Collection<br />
The collection process involves extracting the data logs from the source systems (Security, OS,<br />
RDBMS, etc.) and allows first steps for event log filtering. At this stage can be decided what is going<br />
to be read by the OSSIM Agent and what is going to be discarded before having an impact on the<br />
system performance.<br />
Before starting to write a plugin some actions to reduce the amount of events could be considered:<br />
- Manage the log level settings at the application and managed device level<br />
- Fix the problem that is generating events<br />
- Use Pcap filters to ignore certain hosts or networks (Snort, Tcpdump...)<br />
- In deployments with a big amount of analysed data, filtering at the application level<br />
should be done whenever possible<br />
o<br />
Log Files<br />
Good practice is to use one log file per plugin in order to increase performance. Having just<br />
one generic log file, all the plugins would have to read the same extensive content in order<br />
to catch the few relevant entries.<br />
Using rsyslog it is possible to filter the collected logs based on the syslog tags.<br />
<strong>1.1</strong>.2 Event Normalization<br />
In the normalization stage a series of rules or functions applies to the data extracted from the source<br />
system in order to transform it in a common OSSIM format.<br />
o<br />
Raw Event<br />
The raw event might be a generic syslog message, an application log, an SNMP trap, the<br />
result of an SNMP or SQL Query or some other kind of information in a more or less<br />
structured form that is appended to a log file.<br />
Example:<br />
dmz01:/var/log/auth.log:<br />
May 30 13:15:52 dmz01 sshd[12980]: Accepted password for root from<br />
192.168.178.20 port 4445 ssh2<br />
Page 4 Copyright © Alienvault 2010