Building Collector Plugins 1.1 - AlienVault
Building Collector Plugins 1.1 - AlienVault
Building Collector Plugins 1.1 - AlienVault
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
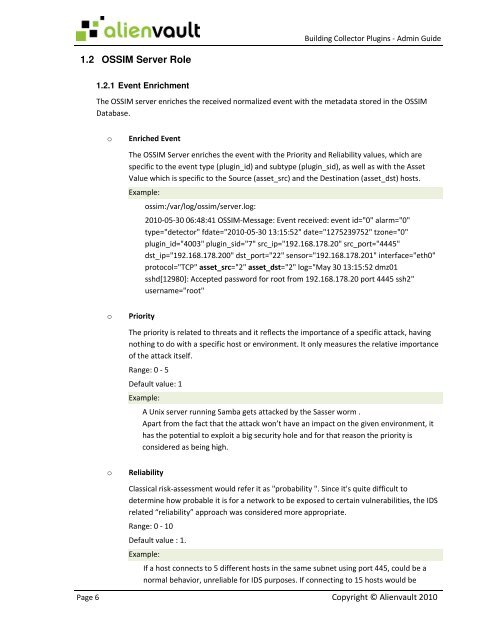
<strong>Building</strong> <strong>Collector</strong> <strong>Plugins</strong> - Admin Guide<br />
1.2 OSSIM Server Role<br />
1.2.1 Event Enrichment<br />
The OSSIM server enriches the received normalized event with the metadata stored in the OSSIM<br />
Database.<br />
o<br />
Enriched Event<br />
The OSSIM Server enriches the event with the Priority and Reliability values, which are<br />
specific to the event type (plugin_id) and subtype (plugin_sid), as well as with the Asset<br />
Value which is specific to the Source (asset_src) and the Destination (asset_dst) hosts.<br />
Example:<br />
ossim:/var/log/ossim/server.log:<br />
2010-05-30 06:48:41 OSSIM-Message: Event received: event id="0" alarm="0"<br />
type="detector" fdate="2010-05-30 13:15:52" date="1275239752" tzone="0"<br />
plugin_id="4003" plugin_sid="7" src_ip="192.168.178.20" src_port="4445"<br />
dst_ip="192.168.178.200" dst_port="22" sensor="192.168.178.201" interface="eth0"<br />
protocol="TCP" asset_src="2" asset_dst="2" log="May 30 13:15:52 dmz01<br />
sshd[12980]: Accepted password for root from 192.168.178.20 port 4445 ssh2"<br />
username="root"<br />
o<br />
Priority<br />
The priority is related to threats and it reflects the importance of a specific attack, having<br />
nothing to do with a specific host or environment. It only measures the relative importance<br />
of the attack itself.<br />
Range: 0 - 5<br />
Default value: 1<br />
Example:<br />
A Unix server running Samba gets attacked by the Sasser worm .<br />
Apart from the fact that the attack won’t have an impact on the given environment, it<br />
has the potential to exploit a big security hole and for that reason the priority is<br />
considered as being high.<br />
o<br />
Reliability<br />
Classical risk-assessment would refer it as "probability ". Since it's quite difficult to<br />
determine how probable it is for a network to be exposed to certain vulnerabilities, the IDS<br />
related “reliability” approach was considered more appropriate.<br />
Range: 0 - 10<br />
Default value : 1.<br />
Example:<br />
If a host connects to 5 different hosts in the same subnet using port 445, could be a<br />
normal behavior, unreliable for IDS purposes. If connecting to 15 hosts would be<br />
Page 6 Copyright © Alienvault 2010