ACHIEVING MISSION ASSURANCE - Raytheon
ACHIEVING MISSION ASSURANCE - Raytheon
ACHIEVING MISSION ASSURANCE - Raytheon
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
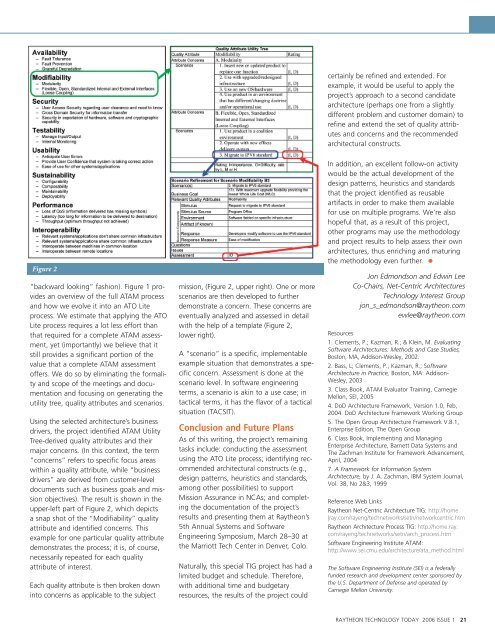
Figure 2<br />
“backward looking” fashion). Figure 1 provides<br />
an overview of the full ATAM process<br />
and how we evolve it into an ATO Lite<br />
process. We estimate that applying the ATO<br />
Lite process requires a lot less effort than<br />
that required for a complete ATAM assessment,<br />
yet (importantly) we believe that it<br />
still provides a significant portion of the<br />
value that a complete ATAM assessment<br />
offers. We do so by eliminating the formality<br />
and scope of the meetings and documentation<br />
and focusing on generating the<br />
utility tree, quality attributes and scenarios.<br />
Using the selected architecture’s business<br />
drivers, the project identified ATAM Utility<br />
Tree-derived quality attributes and their<br />
major concerns. (In this context, the term<br />
“concerns” refers to specific focus areas<br />
within a quality attribute, while “business<br />
drivers” are derived from customer-level<br />
documents such as business goals and mission<br />
objectives). The result is shown in the<br />
upper-left part of Figure 2, which depicts<br />
a snap shot of the “Modifiability” quality<br />
attribute and identified concerns. This<br />
example for one particular quality attribute<br />
demonstrates the process; it is, of course,<br />
necessarily repeated for each quality<br />
attribute of interest.<br />
Each quality attribute is then broken down<br />
into concerns as applicable to the subject<br />
mission, (Figure 2, upper right). One or more<br />
scenarios are then developed to further<br />
demonstrate a concern. These concerns are<br />
eventually analyzed and assessed in detail<br />
with the help of a template (Figure 2,<br />
lower right).<br />
A “scenario” is a specific, implementable<br />
example situation that demonstrates a specific<br />
concern. Assessment is done at the<br />
scenario level. In software engineering<br />
terms, a scenario is akin to a use case; in<br />
tactical terms, it has the flavor of a tactical<br />
situation (TACSIT).<br />
Conclusion and Future Plans<br />
As of this writing, the project’s remaining<br />
tasks include: conducting the assessment<br />
using the ATO Lite process; identifying recommended<br />
architectural constructs (e.g.,<br />
design patterns, heuristics and standards,<br />
among other possibilities) to support<br />
Mission Assurance in NCAs; and completing<br />
the documentation of the project’s<br />
results and presenting them at <strong>Raytheon</strong>’s<br />
5th Annual Systems and Software<br />
Engineering Symposium, March 28–30 at<br />
the Marriott Tech Center in Denver, Colo.<br />
Naturally, this special TIG project has had a<br />
limited budget and schedule. Therefore,<br />
with additional time and budgetary<br />
resources, the results of the project could<br />
certainly be refined and extended. For<br />
example, it would be useful to apply the<br />
project’s approach to a second candidate<br />
architecture (perhaps one from a slightly<br />
different problem and customer domain) to<br />
refine and extend the set of quality attributes<br />
and concerns and the recommended<br />
architectural constructs.<br />
In addition, an excellent follow-on activity<br />
would be the actual development of the<br />
design patterns, heuristics and standards<br />
that the project identified as reusable<br />
artifacts in order to make them available<br />
for use on multiple programs. We’re also<br />
hopeful that, as a result of this project,<br />
other programs may use the methodology<br />
and project results to help assess their own<br />
architectures, thus enriching and maturing<br />
the methodology even further.<br />
Jon Edmondson and Edwin Lee<br />
Co-Chairs, Net-Centric Architectures<br />
Technology Interest Group<br />
jon_s_edmondson@raytheon.com<br />
ewlee@raytheon.com<br />
Resources<br />
1. Clements, P.; Kazman, R.; & Klein, M. Evaluating<br />
Software Architectures: Methods and Case Studies,<br />
Boston, MA, Addison-Wesley, 2002.<br />
2. Bass, L; Clements, P.; Kazman, R.; Software<br />
Architecture in Practice, Boston, MA: Addison-<br />
Wesley, 2003<br />
3. Class Book, ATAM Evaluator Training, Carnegie<br />
Mellon, SEI, 2005<br />
4. DoD Architecture Framework, Version 1.0, Feb,<br />
2004. DoD Architecture Framework Working Group<br />
5. The Open Group Architecture Framework V.8.1,<br />
Enterprise Edition, The Open Group<br />
6. Class Book, Implementing and Managing<br />
Enterprise Architecture, Barnett Data Systems and<br />
The Zachman Institute for Framework Advancement,<br />
April, 2004<br />
7. A Framework for Information System<br />
Architecture, by J. A. Zachman, IBM System Journal,<br />
Vol. 38, No 2&3, 1999<br />
Reference Web Links<br />
<strong>Raytheon</strong> Net-Centric Architecture TIG: http://home.<br />
|ray.com/rayeng/technetworks/setn/networkcentric.htm<br />
<strong>Raytheon</strong> Architecture Process TIG: http://home.ray.<br />
com/rayeng/technetworks/setn/arch_process.htm<br />
Software Engineering Institute ATAM:<br />
http://www.sei.cmu.edu/architecture/ata_method.html<br />
The Software Engineering Institute (SEI) is a federally<br />
funded research and development center sponsored by<br />
the U.S. Department of Defense and operated by<br />
Carnegie Mellon University.<br />
RAYTHEON TECHNOLOGY TODAY 2006 ISSUE 1 21