Since joining UTD in October 2004, she has continued to provide leadership to government programs bygiving present<strong>at</strong>ions on semantic web and d<strong>at</strong>a security as well as on d<strong>at</strong>a analytics to IARPA’s(Intelligence Advanced Research Projects Activity) KDD (Knowledge Discovery and Dissemin<strong>at</strong>ion)Program, Air Force Research Labor<strong>at</strong>ory, <strong>The</strong> Central Intelligence Agency and also the Department <strong>of</strong>Homeland Security’s USVISIT program. She has continued to give present<strong>at</strong>ions and tutorials <strong>at</strong> severalAir Force Bases including <strong>at</strong> Offut, Eglin, Lackland, Edwards and Kirkland as well as to the Navy inNorfolk, VA. In addition to advising the US Government and establishing research programs,Thuraisingham has also influenced the field by giving over 70 keynote addresses <strong>at</strong> major intern<strong>at</strong>ionalconferences since 1994. She has also provided services as an expert witness and has consulted to thefederal government through corpor<strong>at</strong>ions.Thuraisingham’s tireless efforts have benefitted her research <strong>at</strong> UTD a gre<strong>at</strong> deal. Together with hercolleagues, she has established a strong research and educ<strong>at</strong>ion program <strong>at</strong> UTD in Cyber Security th<strong>at</strong>includes DoD MURI, NSF Career, AFOSR YIP and NSF SFS (Scholarship for Service) awards. <strong>The</strong> teamhas also received grants from NIH, ONR, IARPA, NGA and NASA. Thuraisingham’s current efforts arein developing research, infrastructure and educ<strong>at</strong>ion programs in assured cloud computing. She promotesa strong customer-focused, team-oriented collabor<strong>at</strong>ive culture and she is working on bringing togetherthe vast number <strong>of</strong> DFW Corpor<strong>at</strong>ions to work on interdisciplinary research programs. Most recently, sheis heading an intern<strong>at</strong>ional collabor<strong>at</strong>ive effort on assured sharing in a cloud environment.She promotes M<strong>at</strong>h and Science to high school students as well as to women and underrepresentedminorities, and is a member <strong>of</strong> the Society <strong>of</strong> Women Engineers (SWE). She has given fe<strong>at</strong>ured addresses<strong>at</strong> conferences sponsored by WITI (Women in Technology Intern<strong>at</strong>ional) and SWE and received the 2001Woman <strong>of</strong> Color Research Leadership Award from Career Communic<strong>at</strong>ions Inc. Articles on her effortsand her vision, as well as her team’s research, have appeared in multiple magazines including the <strong>Dallas</strong>Morning News, the Boston Globe, ABC News, D Magazine, MITRE M<strong>at</strong>ters the DFW MetroplexTechnology magazine. She has also appeared on DFW television giving her view on cyber security. Shehas particip<strong>at</strong>ed in panels on educ<strong>at</strong>ion-rel<strong>at</strong>ed issues including one on protecting children frominappropri<strong>at</strong>e content on the Internet chaired by Hon. Dick Thornburgh in 2000. She is continuing withthese efforts and recently particip<strong>at</strong>ed in EastWest Institute’s 1 st Worldwide Security Summit panel onprotecting children in cyberspace.14
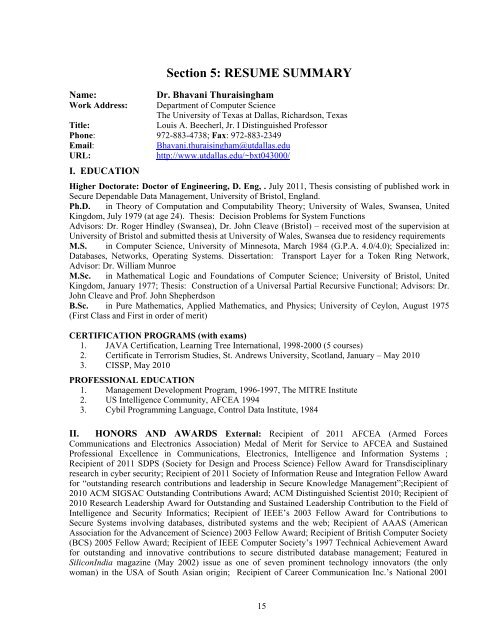
Section 5: RESUME SUMMARYName:Dr. Bhavani ThuraisinghamWork Address: Department <strong>of</strong> Computer Science<strong>The</strong> <strong>University</strong> <strong>of</strong> <strong>Texas</strong> <strong>at</strong> <strong>Dallas</strong>, Richardson, <strong>Texas</strong>Title:Louis A. Beecherl, Jr. I Distinguished Pr<strong>of</strong>essorPhone: 972-883-4738; Fax: 972-883-2349Email:Bhavani.thuraisingham@utdallas.eduURL:http://www.utdallas.edu/~bxt043000/I. EDUCATIONHigher Doctor<strong>at</strong>e: Doctor <strong>of</strong> Engineering, D. Eng, . July 2011, <strong>The</strong>sis consisting <strong>of</strong> published work inSecure Dependable D<strong>at</strong>a Management, <strong>University</strong> <strong>of</strong> Bristol, England.Ph.D. in <strong>The</strong>ory <strong>of</strong> Comput<strong>at</strong>ion and Computability <strong>The</strong>ory; <strong>University</strong> <strong>of</strong> Wales, Swansea, UnitedKingdom, July 1979 (<strong>at</strong> age 24). <strong>The</strong>sis: Decision Problems for System FunctionsAdvisors: Dr. Roger Hindley (Swansea), Dr. John Cleave (Bristol) – received most <strong>of</strong> the supervision <strong>at</strong><strong>University</strong> <strong>of</strong> Bristol and submitted thesis <strong>at</strong> <strong>University</strong> <strong>of</strong> Wales, Swansea due to residency requirementsM.S. in Computer Science, <strong>University</strong> <strong>of</strong> Minnesota, March 1984 (G.P.A. 4.0/4.0); Specialized in:D<strong>at</strong>abases, Networks, Oper<strong>at</strong>ing Systems. Dissert<strong>at</strong>ion: Transport Layer for a Token Ring Network,Advisor: Dr. William MunroeM.Sc. in M<strong>at</strong>hem<strong>at</strong>ical Logic and Found<strong>at</strong>ions <strong>of</strong> Computer Science; <strong>University</strong> <strong>of</strong> Bristol, UnitedKingdom, January 1977; <strong>The</strong>sis: Construction <strong>of</strong> a Universal Partial Recursive Functional; Advisors: Dr.John Cleave and Pr<strong>of</strong>. John ShepherdsonB.Sc. in Pure M<strong>at</strong>hem<strong>at</strong>ics, Applied M<strong>at</strong>hem<strong>at</strong>ics, and Physics; <strong>University</strong> <strong>of</strong> Ceylon, August 1975(First Class and First in order <strong>of</strong> merit)CERTIFICATION PROGRAMS (with exams)1. JAVA Certific<strong>at</strong>ion, Learning Tree Intern<strong>at</strong>ional, 1998-2000 (5 courses)2. Certific<strong>at</strong>e in Terrorism Studies, St. Andrews <strong>University</strong>, Scotland, January – May 20103. CISSP, May 2010PROFESSIONAL EDUCATION1. Management Development Program, 1996-1997, <strong>The</strong> MITRE Institute2. US Intelligence Community, AFCEA 19943. Cybil Programming Language, Control D<strong>at</strong>a Institute, 1984II. HONORS AND AWARDS External: Recipient <strong>of</strong> 2011 AFCEA (Armed ForcesCommunic<strong>at</strong>ions and Electronics Associ<strong>at</strong>ion) Medal <strong>of</strong> Merit for Service to AFCEA and SustainedPr<strong>of</strong>essional Excellence in Communic<strong>at</strong>ions, Electronics, Intelligence and Inform<strong>at</strong>ion Systems ;Recipient <strong>of</strong> 2011 SDPS (Society for Design and Process Science) Fellow Award for Transdisciplinaryresearch in cyber security; Recipient <strong>of</strong> 2011 Society <strong>of</strong> Inform<strong>at</strong>ion Reuse and Integr<strong>at</strong>ion Fellow Awardfor “outstanding research contributions and leadership in Secure Knowledge Management”;Recipient <strong>of</strong>2010 ACM SIGSAC Outstanding Contributions Award; ACM Distinguished Scientist 2010; Recipient <strong>of</strong>2010 Research Leadership Award for Outstanding and Sustained Leadership Contribution to the Field <strong>of</strong>Intelligence and Security Inform<strong>at</strong>ics; Recipient <strong>of</strong> IEEE’s 2003 Fellow Award for Contributions toSecure Systems involving d<strong>at</strong>abases, distributed systems and the web; Recipient <strong>of</strong> AAAS (AmericanAssoci<strong>at</strong>ion for the Advancement <strong>of</strong> Science) 2003 Fellow Award; Recipient <strong>of</strong> British Computer Society(BCS) 2005 Fellow Award; Recipient <strong>of</strong> IEEE Computer Society’s 1997 Technical Achievement Awardfor outstanding and innov<strong>at</strong>ive contributions to secure distributed d<strong>at</strong>abase management; Fe<strong>at</strong>ured inSiliconIndia magazine (May 2002) issue as one <strong>of</strong> seven prominent technology innov<strong>at</strong>ors (the onlywoman) in the USA <strong>of</strong> South Asian origin; Recipient <strong>of</strong> Career Communic<strong>at</strong>ion Inc.’s N<strong>at</strong>ional 200115
- Page 1: Curriculum VitaeBhavani Thuraisingh
- Page 5 and 6: EXTERNALSection 2: MAJOR AWARDSBest
- Page 7 and 8: Section 3: SYNOPSIS OF RESEARCHMy r
- Page 9 and 10: the concepts in semantic nets and c
- Page 11 and 12: secure query processing for cloud.
- Page 13: Section 4: RESEARCH LEADERSHIPhttp:
- Page 17 and 18: Army, NSA, and CIA as well as consu
- Page 19 and 20: Section 6: INDUSTRY/GOVERNMENT EXPE
- Page 21 and 22: management to discuss projects as w
- Page 23 and 24: Current (2004 - Present)The Univers
- Page 25 and 26: Object Databases (1 day course taug
- Page 27 and 28: Section 8: ACADEMIC RESEARCH SUPERV
- Page 29 and 30: Thesis Committees: Serving/served o
- Page 31 and 32: Section 9: RESEARCH FUNDINGI have o
- Page 33 and 34: PI: L. KhanAmount: $260,00020. Nati
- Page 35 and 36: 3. CIA: As manager of fifteen resea
- Page 37 and 38: 15. Multilevel Security Issues in D
- Page 39 and 40: 48. E-Mail Worm Detection Using Dat
- Page 41 and 42: 79. Information Demands Drive Data
- Page 43 and 44: 2. Foundations of Multilevel Databa
- Page 45 and 46: 32. Parallel Processing and Trusted
- Page 47 and 48: 66. Privacy Preserving Data Mining,
- Page 49 and 50: 99. Data Mining for Cyber Security
- Page 51 and 52: 130. Object-oriented Implementation
- Page 53 and 54: 161. XIMKON- An Expert Simulation a
- Page 55 and 56: 194. Ontology Alignment Using Multi
- Page 57 and 58: 225. RETRO: A Framework for Semanti
- Page 59 and 60: 5. Inference Problem in Database Se
- Page 61 and 62: I. JOURNAL SPECIAL ISSUES EDITEDSec
- Page 63 and 64: 12. Proceedings ISI Conference, IEE
- Page 65 and 66:
Bhavani ThuraisinghamUTDCS-45-06UTD
- Page 67 and 68:
UTDCS-32-08A Practical Approach to
- Page 69 and 70:
UTDCS-27-11Towards the Design and I
- Page 71 and 72:
29. A Seminar on Real-time Database
- Page 73 and 74:
14. Concurrency Control in Real-tim
- Page 75 and 76:
17. Data Management Systems Evoluti
- Page 77 and 78:
54. Data Mining for National Securi
- Page 79 and 80:
5. Recent Developments in Some Trus
- Page 81 and 82:
44. Data Engineering Directions, IE
- Page 83 and 84:
6. Towards a Global Multilevel Data
- Page 85 and 86:
19. Object Technology for C4I Appli
- Page 87 and 88:
59. Assured Cloud Computing, AFOSR
- Page 89 and 90:
2. A Seminar on Secure Database Sys
- Page 91 and 92:
VIII. The University of Texas at Da
- Page 93 and 94:
5. Secure Distributed Query Process
- Page 95 and 96:
Simulated algorithms for informatio
- Page 97 and 98:
1. Geospatial Proximity Algorithm,
- Page 99 and 100:
Section 16: INTELLECTUAL PROPERTY A
- Page 101 and 102:
Section 17: DISCUSSION OF PUBLISHED
- Page 103 and 104:
conceptual structures (e.g., semant
- Page 105 and 106:
1990s, we designed and implemented
- Page 107 and 108:
inference problem. Back in the earl
- Page 109 and 110:
9. A Semantic Web Based Framework f
- Page 111 and 112:
Policy management: While discretion
- Page 113 and 114:
Section 18: DISCUSSION OF COMPLETE
- Page 115 and 116:
Publications: Several journal publi
- Page 117 and 118:
Research and Technology Transfer in
- Page 119 and 120:
13. IEEE WORDS Workshop, Santa Barb
- Page 121 and 122:
82. AAAI, Vancouver, BC, Canada, Ju
- Page 123 and 124:
http://findarticles.com/p/articles/
- Page 125 and 126:
NSF Grants to Help Create Next-Gene
- Page 127:
SECTION 21. CYBER SECURITY RESEARCH