Biometric Cryptography
Biometric Cryptography
Biometric Cryptography
- No tags were found...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
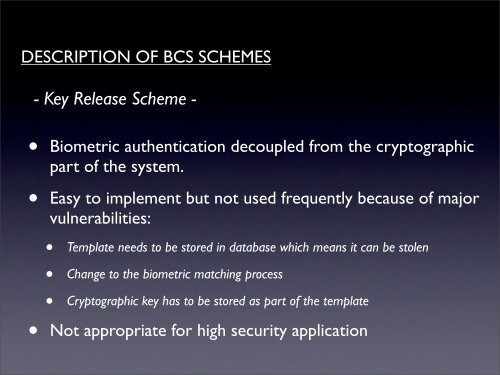
DESCRIPTION OF BCS SCHEMES- Key Release Scheme -• <strong>Biometric</strong> authentication decoupled from the cryptographicpart of the system.• Easy to implement but not used frequently because of majorvulnerabilities:• Template needs to be stored in database which means it can be stolen• Change to the biometric matching process• Cryptographic key has to be stored as part of the template• Not appropriate for high security application