Biometric Cryptography
Biometric Cryptography
Biometric Cryptography
- No tags were found...
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
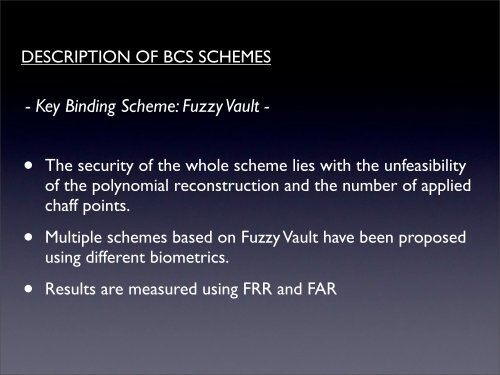
DESCRIPTION OF BCS SCHEMES- Key Binding Scheme: Fuzzy Vault -• The security of the whole scheme lies with the unfeasibilityof the polynomial reconstruction and the number of appliedchaff points.• Multiple schemes based on Fuzzy Vault have been proposedusing different biometrics.• Results are measured using FRR and FAR