Biometric Cryptography
Biometric Cryptography
Biometric Cryptography
- No tags were found...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
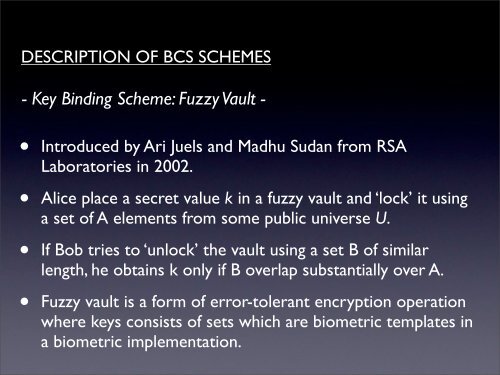
DESCRIPTION OF BCS SCHEMES- Key Binding Scheme: Fuzzy Vault -• Introduced by Ari Juels and Madhu Sudan from RSALaboratories in 2002.• Alice place a secret value k in a fuzzy vault and ‘lock’ it usinga set of A elements from some public universe U.• If Bob tries to ‘unlock’ the vault using a set B of similarlength, he obtains k only if B overlap substantially over A.• Fuzzy vault is a form of error-tolerant encryption operationwhere keys consists of sets which are biometric templates ina biometric implementation.