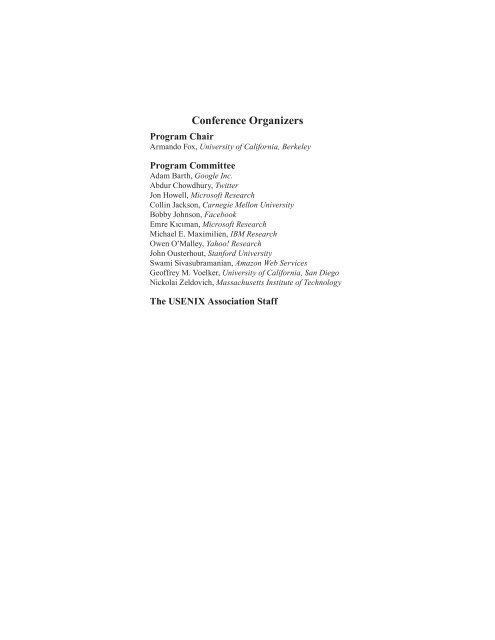
<str<strong>on</strong>g>C<strong>on</strong>ference</str<strong>on</strong>g> Organizers Program Chair Armando Fox, University of California, Berkeley Program Committee Adam Barth, Google Inc. Abdur Chowdhury, Twitter J<strong>on</strong> Howell, Microsoft Research Collin Jacks<strong>on</strong>, Carnegie Mell<strong>on</strong> University Bobby Johns<strong>on</strong>, Facebook Emre Kıcıman, Microsoft Research Michael E. Maximilien, IBM Research Owen O’Malley, Yahoo! Research John Ousterhout, Stanford University Swami Sivasubramanian, Amaz<strong>on</strong> <strong>Web</strong> Services Geoffrey M. Voelker, University of California, San Diego Nickolai Zeldovich, Massachusetts Institute of Technology The <str<strong>on</strong>g>USENIX</str<strong>on</strong>g> Associati<strong>on</strong> Staff
<strong>Web</strong>Apps ’11: <str<strong>on</strong>g>2nd</str<strong>on</strong>g> <str<strong>on</strong>g>USENIX</str<strong>on</strong>g> <str<strong>on</strong>g>C<strong>on</strong>ference</str<strong>on</strong>g> <strong>on</strong> <strong>Web</strong> Applicati<strong>on</strong> <strong>Development</strong> June 15–16, 2011 Portland, OR, USA Message from the Program Chair . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . v Wednesday, June 15 10:30–No<strong>on</strong> GuardRails: A Data-Centric <strong>Web</strong> Applicati<strong>on</strong> Security Framework . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .1 J<strong>on</strong>athan Burket, Patrick Mutchler, Michael Weaver, Muzzammil Zaveri, and David Evans, University of Virginia PHP Aspis: Using Partial Taint Tracking to Protect Against Injecti<strong>on</strong> Attacks . . . . . . . . . . . . . . . . . . . . . . . . . . . . .13 Ioannis Papagiannis, Matteo Migliavacca, and Peter Pietzuch, Imperial College L<strong>on</strong>d<strong>on</strong> Secure Data Preservers for <strong>Web</strong> Services . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .25 Jayanthkumar Kannan, Google Inc.; Petros Maniatis, Intel Labs; Byung-G<strong>on</strong> Chun, Yahoo! Research 1:00–2:30 BenchLab: An Open Testbed for Realistic Benchmarking of <strong>Web</strong> Applicati<strong>on</strong>s . . . . . . . . . . . . . . . . . . . . . . . . . . . .37 Emmanuel Cecchet, Veena Udayabhanu, Timothy Wood, and Prashant Shenoy, University of Massachusetts Amherst Resource Provisi<strong>on</strong>ing of <strong>Web</strong> Applicati<strong>on</strong>s in Heterogeneous Clouds . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .49 Jiang Dejun, VU University Amsterdam and Tsinghua University Beijing; Guillaume Pierre, VU University Amsterdam; Chi-Hung Chi, Tsinghua University Beijing C3: An Experimental, Extensible, Rec<strong>on</strong>figurable Platform for HTML-based Applicati<strong>on</strong>s . . . . . . . . . . . . . . . . . .61 Benjamin S. Lerner and Brian Burg, University of Washingt<strong>on</strong>; Herman Venter and Wolfram Schulte, Microsoft Research 3:00–4:30 The Effectiveness of Applicati<strong>on</strong> Permissi<strong>on</strong>s . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .75 Adrienne Porter Felt, Kate Greenwood, and David Wagner, University of California, Berkeley Experiences <strong>on</strong> a Design Approach for Interactive <strong>Web</strong> Applicati<strong>on</strong>s . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .87 Janne Kuuskeri, Tampere University of Technology Exploring the Relati<strong>on</strong>ship Between <strong>Web</strong> Applicati<strong>on</strong> <strong>Development</strong> Tools and Security . . . . . . . . . . . . . . . . . . . . .99 Matthew Finifter and David Wagner, University of California, Berkeley Thursday, June 16 1:00–2:30 Integrating L<strong>on</strong>g Polling with an MVC <strong>Web</strong> Framework . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .113 Eric Stratmann, John Ousterhout, and Sameer Madan, Stanford University Detecting Malicious <strong>Web</strong> Links and Identifying Their Attack Types . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .125 Hyunsang Choi, Korea University; Bin B. Zhu, Microsoft Research Asia; Heejo Lee, Korea University Maverick: Providing <strong>Web</strong> Applicati<strong>on</strong>s with Safe and Flexible Access to Local Devices . . . . . . . . . . . . . . . . . . . .137 David W. Richards<strong>on</strong> and Steven D. Gribble, University of Washingt<strong>on</strong>