- Page 1:
Faculteit WetenschappenInformaticaE
- Page 6 and 7:
Chapter 0. Nederlandse samenvatting
- Page 8:
Chapter 0. Nederlandse samenvatting
- Page 11:
Chapter 0. English summaryalgorithm
- Page 14 and 15:
Chapter 0. List of publications8. S
- Page 16 and 17:
Contents1.6 Publications . . . . .
- Page 18 and 19:
Contents7.3.3 Blocking Problem (BP)
- Page 20 and 21: Contents12 A cross-layer PHY-MAC pr
- Page 22 and 23: List of Tables8.1 Examples of CW mi
- Page 24 and 25: List of Figures3.6 CFP/ CP periods
- Page 26 and 27: List of Figures8.10 (Lw)(Upp)Bounds
- Page 29 and 30: List of AcronymsAC Access CategoryA
- Page 31 and 32: Chapter 0. List of AcronymsFND Firs
- Page 35 and 36: CHAPTER1Introduction1.1 State-of-th
- Page 37 and 38: 1.1. State-of-the-art in wireless n
- Page 39 and 40: 1.1. State-of-the-art in wireless n
- Page 41 and 42: 1.1. State-of-the-art in wireless n
- Page 43 and 44: 1.2. Wireless technologies organiza
- Page 45 and 46: 1.3. IEEE 802 and 802.11 familyfami
- Page 47 and 48: 1.4. Ad hoc network definition and
- Page 49 and 50: 1.4. Ad hoc network definition and
- Page 51 and 52: 1.4. Ad hoc network definition and
- Page 53 and 54: 1.4. Ad hoc network definition and
- Page 55 and 56: 1.5 Outline and main research contr
- Page 57 and 58: 1.5. Outline and main research cont
- Page 59 and 60: 1.6. Publications1.6 PublicationsPa
- Page 61 and 62: CHAPTER2Interaction between MAC lay
- Page 63 and 64: 2.1. Wireless environment -interact
- Page 65 and 66: 2.1. Wireless environment -interact
- Page 67 and 68: CHAPTER3IEEE 802.11 standardThe IEE
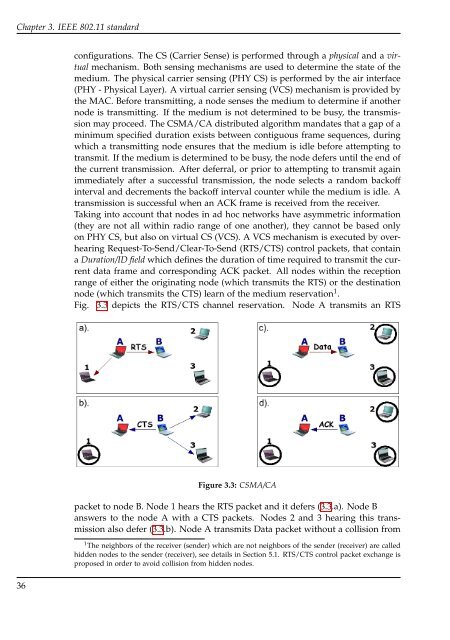
- Page 69: 3.2. IEEE 802.11 DCF mechanismTable
- Page 73 and 74: 3.4. Interframe space periods and b
- Page 75 and 76: 3.5. Random backoff time and Binary
- Page 77: 3.6. Power management in ad hoc net
- Page 80 and 81: Chapter 4. MAC protocols for ad hoc
- Page 82 and 83: Chapter 4. MAC protocols for ad hoc
- Page 84 and 85: Chapter 4. MAC protocols for ad hoc
- Page 86 and 87: Chapter 4. MAC protocols for ad hoc
- Page 88 and 89: Chapter 4. MAC protocols for ad hoc
- Page 90 and 91: Chapter 4. MAC protocols for ad hoc
- Page 92 and 93: Chapter 4. MAC protocols for ad hoc
- Page 94 and 95: Chapter 4. MAC protocols for ad hoc
- Page 96 and 97: Chapter 4. MAC protocols for ad hoc
- Page 98 and 99: Chapter 5. IEEE 802.11 problems and
- Page 100 and 101: Chapter 5. IEEE 802.11 problems and
- Page 102 and 103: Chapter 5. IEEE 802.11 problems and
- Page 104 and 105: Chapter 5. IEEE 802.11 problems and
- Page 106 and 107: Chapter 5. IEEE 802.11 problems and
- Page 108 and 109: Chapter 5. IEEE 802.11 problems and
- Page 111 and 112: CHAPTER6Simulation environmentThe N
- Page 113 and 114: 6.2. Simulation parameters• PDF -
- Page 115 and 116: 6.2. Simulation parametersour simul
- Page 117 and 118: 6.2. Simulation parametersSince it
- Page 119: 6.2. Simulation parameters(a) The p
- Page 122 and 123:
Chapter 7. Blocking problem and con
- Page 124 and 125:
Chapter 7. Blocking problem and con
- Page 126 and 127:
Chapter 7. Blocking problem and con
- Page 128 and 129:
Chapter 7. Blocking problem and con
- Page 130 and 131:
Chapter 7. Blocking problem and con
- Page 132 and 133:
Chapter 7. Blocking problem and con
- Page 134 and 135:
Chapter 7. Blocking problem and con
- Page 136 and 137:
Chapter 7. Blocking problem and con
- Page 138 and 139:
Chapter 7. Blocking problem and con
- Page 140 and 141:
Chapter 7. Blocking problem and con
- Page 142 and 143:
Chapter 7. Blocking problem and con
- Page 144 and 145:
Chapter 7. Blocking problem and con
- Page 146 and 147:
Chapter 7. Blocking problem and con
- Page 148 and 149:
Chapter 7. Blocking problem and con
- Page 150 and 151:
Chapter 8. Contention Window contro
- Page 152 and 153:
Chapter 8. Contention Window contro
- Page 154 and 155:
Chapter 8. Contention Window contro
- Page 156 and 157:
Chapter 8. Contention Window contro
- Page 158 and 159:
Chapter 8. Contention Window contro
- Page 160 and 161:
Chapter 8. Contention Window contro
- Page 162 and 163:
Chapter 8. Contention Window contro
- Page 164 and 165:
Chapter 8. Contention Window contro
- Page 166 and 167:
Chapter 8. Contention Window contro
- Page 168 and 169:
Chapter 8. Contention Window contro
- Page 170 and 171:
Chapter 8. Contention Window contro
- Page 172 and 173:
Chapter 8. Contention Window contro
- Page 175 and 176:
CHAPTER9Contention Window resetting
- Page 177 and 178:
9.1. Dynamic Resetting Algorithm (D
- Page 179 and 180:
9.1. Dynamic Resetting Algorithm (D
- Page 181 and 182:
9.2. Evaluation of the dynamic rese
- Page 183 and 184:
9.2. Evaluation of the dynamic rese
- Page 185 and 186:
9.2. Evaluation of the dynamic rese
- Page 187 and 188:
9.2. Evaluation of the dynamic rese
- Page 189 and 190:
9.3. Neighbor and Interferences Awa
- Page 191 and 192:
9.3. Neighbor and Interferences Awa
- Page 193 and 194:
9.4. Performance evaluation of the
- Page 195 and 196:
9.4. Performance evaluation of the
- Page 197 and 198:
9.5 The eDRA versus the NIAMac prot
- Page 199 and 200:
9.6. MobiNIAMac protocolthe results
- Page 201 and 202:
9.7. Comparison of eDRA, NIAMac and
- Page 203 and 204:
9.7. Comparison of eDRA, NIAMac and
- Page 205 and 206:
CHAPTER10Enhanced selection Bounds
- Page 207 and 208:
10.1. Performance evaluation of the
- Page 209 and 210:
10.1. Performance evaluation of the
- Page 211 and 212:
10.1. Performance evaluation of the
- Page 213 and 214:
10.1. Performance evaluation of the
- Page 215 and 216:
10.1. Performance evaluation of the
- Page 217 and 218:
10.1. Performance evaluation of the
- Page 219 and 220:
10.1. Performance evaluation of the
- Page 221 and 222:
10.1. Performance evaluation of the
- Page 223 and 224:
10.1. Performance evaluation of the
- Page 225:
10.1. Performance evaluation of the
- Page 228 and 229:
Chapter 11. Basic and enhanced powe
- Page 230 and 231:
Chapter 11. Basic and enhanced powe
- Page 232 and 233:
Chapter 11. Basic and enhanced powe
- Page 234 and 235:
Chapter 11. Basic and enhanced powe
- Page 236 and 237:
Chapter 11. Basic and enhanced powe
- Page 238 and 239:
Chapter 11. Basic and enhanced powe
- Page 240 and 241:
Chapter 11. Basic and enhanced powe
- Page 242 and 243:
Chapter 11. Basic and enhanced powe
- Page 244 and 245:
Chapter 11. Basic and enhanced powe
- Page 246 and 247:
Chapter 11. Basic and enhanced powe
- Page 248 and 249:
Chapter 11. Basic and enhanced powe
- Page 250 and 251:
Chapter 11. Basic and enhanced powe
- Page 252 and 253:
Chapter 11. Basic and enhanced powe
- Page 254 and 255:
Chapter 11. Basic and enhanced powe
- Page 256 and 257:
Chapter 12. A cross-layer PHY-MAC p
- Page 258 and 259:
Chapter 12. A cross-layer PHY-MAC p
- Page 260 and 261:
Chapter 12. A cross-layer PHY-MAC p
- Page 262 and 263:
Chapter 12. A cross-layer PHY-MAC p
- Page 264 and 265:
Chapter 12. A cross-layer PHY-MAC p
- Page 266 and 267:
Chapter 12. A cross-layer PHY-MAC p
- Page 268 and 269:
Chapter 12. A cross-layer PHY-MAC p
- Page 270 and 271:
Chapter 12. A cross-layer PHY-MAC p
- Page 272 and 273:
Chapter 12. A cross-layer PHY-MAC p
- Page 274 and 275:
Chapter 12. A cross-layer PHY-MAC p
- Page 276 and 277:
Chapter 12. A cross-layer PHY-MAC p
- Page 278 and 279:
Chapter 12. A cross-layer PHY-MAC p
- Page 280 and 281:
Chapter 12. A cross-layer PHY-MAC p
- Page 282 and 283:
Chapter 12. A cross-layer PHY-MAC p
- Page 284 and 285:
Chapter 12. A cross-layer PHY-MAC p
- Page 286 and 287:
Chapter 12. A cross-layer PHY-MAC p
- Page 288 and 289:
Chapter 12. A cross-layer PHY-MAC p
- Page 290 and 291:
Chapter 12. A cross-layer PHY-MAC p
- Page 293 and 294:
CHAPTER13Conclusions and Perspectiv
- Page 295 and 296:
Chapter 13. Conclusion and Perspect
- Page 297 and 298:
Chapter 13. Conclusion and Perspect
- Page 299:
Chapter 13. Conclusion and Perspect
- Page 302 and 303:
References[11] HSPA Mobile broadban
- Page 304 and 305:
References[43] Intelligent Transpor
- Page 306 and 307:
References[71] Chane L. Fullmer J.
- Page 308 and 309:
References[101] Mort Naraghi-Pour.
- Page 310 and 311:
References[130] P.K. Varshney J. De
- Page 312 and 313:
References[158] Q. Lindsey D. Lymbe