- Page 1: More Tricks For Defeating SSL InPra
- Page 7 and 8: Certificate ChainingVeriSignInterme
- Page 9 and 10: What they say:●●●●Verify th
- Page 11 and 12: VeriSignWhat if...IntermediateCAInt
- Page 13 and 14: What they say:●●●●Verify th
- Page 15 and 16: But we just created a valid certifi
- Page 17: ...is a somewhat obscure field.Moxi
- Page 21 and 22: sslsniffMoxie MarlinspikeInstitute
- Page 24 and 25: Lately, I've been talking aboutSSL
- Page 26 and 27: Moxie MarlinspikeInstitute For Disr
- Page 28 and 29: In the context of web browsing●
- Page 30 and 31: Moxie MarlinspikeInstitute For Disr
- Page 32 and 33: We Can Attack SSLBefore We Even Get
- Page 34 and 35: sslstripMoxie MarlinspikeInstitute
- Page 36 and 37: sslstrip●Watch HTTP traffic go by
- Page 38 and 39: How Does It Look?
- Page 40 and 41: How Does It Look?
- Page 43 and 44: The sites themselves confuse us.
- Page 45 and 46: Some sites provide no visible diffe
- Page 47 and 48: Other Little Tricks:
- Page 49 and 50: Where do we need to go from here?Mo
- Page 51 and 52: What's with certificates, anyways?X
- Page 53 and 54: What's with certificates, anyways?X
- Page 55 and 56: Moxie MarlinspikeInstitute For Disr
- Page 57 and 58: SSL/TLS Handshake BeginningsClientH
- Page 59 and 60: The Problems For Us BeginAttackerCl
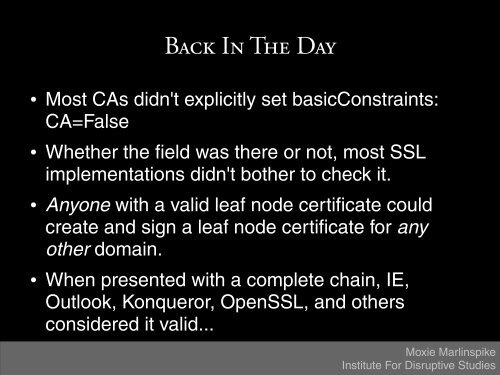
- Page 61 and 62: In 2000, things were different.Moxi
- Page 63 and 64: Identification!Moxie MarlinspikeIns
- Page 65 and 66: Actual people involved...Moxie Marl
- Page 67 and 68: These days it's all about:online do
- Page 69 and 70:
Moxie MarlinspikeInstitute For Disr
- Page 71 and 72:
PKCS #10CertificateRequestVersionSu
- Page 73 and 74:
PKCS #10CertificateRequestVersionSu
- Page 75 and 76:
PKCS #10CertificateRequestVersionSu
- Page 77 and 78:
PKCS #10CertificateRequestVersionSu
- Page 79 and 80:
PKCS #10CertificateRequestVersionSu
- Page 81 and 82:
SubjectsDistinguishedNameCountrySta
- Page 83 and 84:
SubjectsDistinguishedNameCountrySta
- Page 85 and 86:
CNcommonName ::=SEQUENCE { { 2 5 4
- Page 87 and 88:
PKCS #10 SubjectDistinguishedNameCo
- Page 89 and 90:
PKCS #10 SubjectCommon Nameverisign
- Page 91 and 92:
PKCS #10 SubjectCommon Namewww.payp
- Page 93 and 94:
PKCS #10 Certificate SigningRequest
- Page 95 and 96:
Our Original ScenarioX509Certificat
- Page 97 and 98:
In memory, though...char *destinati
- Page 99 and 100:
In the eyes of most SSLimplementati
- Page 101 and 102:
A First Cut: updated sslsniffsslsni
- Page 103 and 104:
How does it look?Moxie MarlinspikeI
- Page 105 and 106:
How does it look?Moxie MarlinspikeI
- Page 107 and 108:
1) Targeted attacks are kind of lam
- Page 109 and 110:
Moxie MarlinspikeInstitute For Disr
- Page 111 and 112:
Moxie MarlinspikeInstitute For Disr
- Page 113 and 114:
Moxie MarlinspikeInstitute For Disr
- Page 115 and 116:
Universal Wildcard*~.thoughtcrime.o
- Page 117 and 118:
And... your remote exploit.● 144
- Page 119 and 120:
And... your remote exploit.● 144
- Page 121 and 122:
And... your remote exploit.(AAAAAAA
- Page 123 and 124:
And... your remote exploit.(AAAAAAA
- Page 125 and 126:
A Second Cut: sslsniff withwildcard
- Page 127 and 128:
What do we have to worry about?Moxi
- Page 129 and 130:
What do we have to worry about?1) C
- Page 131 and 132:
Moxie MarlinspikeInstitute For Disr
- Page 133 and 134:
Defeating OCSPOCSPResponse ::= SEQU
- Page 135 and 136:
Defeating OCSPOCSPResponse ::= SEQU
- Page 137 and 138:
Defeating OCSPOCSPResponse ::= SEQU
- Page 139 and 140:
Defeating OCSPOCSPResponse ::= SEQU
- Page 141 and 142:
Defeating OCSPOCSPResponse ::= SEQU
- Page 143 and 144:
A Third Cut: ocsp-aware sslsniffssl
- Page 145 and 146:
What do we have to worry about?2) U
- Page 147 and 148:
Firefox/Thunderbird: A Case StudyUp
- Page 149 and 150:
Firefox/Thunderbird: A Case Study
- Page 151 and 152:
A Fourth Cut: update-aware sslsniff
- Page 153 and 154:
Postscript:Stripping NULL is no sol
- Page 155 and 156:
Conclusion●●●●●●We have