Automated vulnerability scanning and exploitation
Automated vulnerability scanning and exploitation - Index of
Automated vulnerability scanning and exploitation - Index of
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
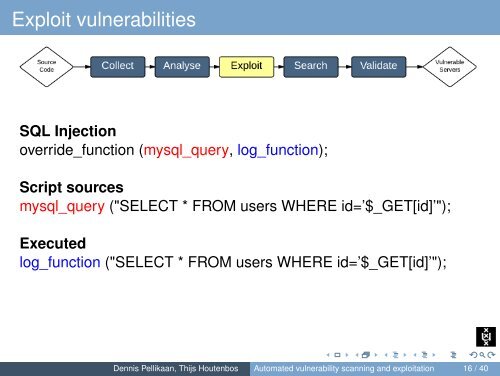
Exploit vulnerabilitiesSQL Injectionoverride_function (mysql_query, log_function);Script sourcesmysql_query ("SELECT * FROM users WHERE id=’$_GET[id]’");Executedlog_function ("SELECT * FROM users WHERE id=’$_GET[id]’");Dennis Pellikaan, Thijs Houtenbos <strong>Automated</strong> <strong>vulnerability</strong> <strong>scanning</strong> <strong>and</strong> <strong>exploitation</strong> 16 / 40