Automated vulnerability scanning and exploitation
Automated vulnerability scanning and exploitation - Index of
Automated vulnerability scanning and exploitation - Index of
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
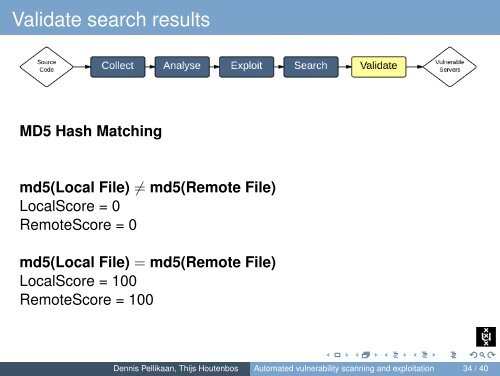
Validate search resultsMD5 Hash Matchingmd5(Local File) ≠ md5(Remote File)LocalScore = 0RemoteScore = 0md5(Local File) = md5(Remote File)LocalScore = 100RemoteScore = 100Dennis Pellikaan, Thijs Houtenbos <strong>Automated</strong> <strong>vulnerability</strong> <strong>scanning</strong> <strong>and</strong> <strong>exploitation</strong> 34 / 40