Automated vulnerability scanning and exploitation
Automated vulnerability scanning and exploitation - Index of
Automated vulnerability scanning and exploitation - Index of
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
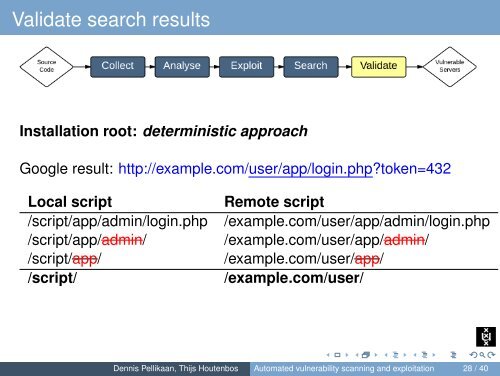
Validate search resultsInstallation root: deterministic approachGoogle result: http://example.com/user/app/login.php?token=432Local script/script/app/admin/login.php/script/app/admin//script/app//script/Remote script/example.com/user/app/admin/login.php/example.com/user/app/admin//example.com/user/app//example.com/user/Dennis Pellikaan, Thijs Houtenbos <strong>Automated</strong> <strong>vulnerability</strong> <strong>scanning</strong> <strong>and</strong> <strong>exploitation</strong> 28 / 40