BATTLE OF SKM AND IUM
blackhat2015
blackhat2015
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
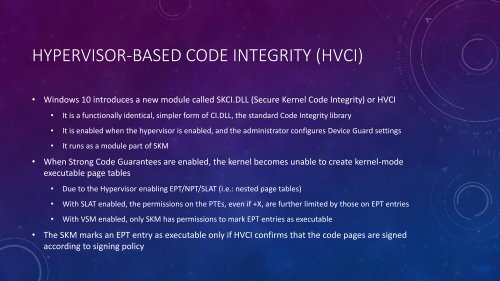
HYPERVISOR-BASED CODE INTEGRITY (HVCI)<br />
• Windows 10 introduces a new module called SKCI.DLL (Secure Kernel Code Integrity) or HVCI<br />
• It is a functionally identical, simpler form of CI.DLL, the standard Code Integrity library<br />
• It is enabled when the hypervisor is enabled, and the administrator configures Device Guard settings<br />
• It runs as a module part of <strong>SKM</strong><br />
• When Strong Code Guarantees are enabled, the kernel becomes unable to create kernel-mode<br />
executable page tables<br />
• Due to the Hypervisor enabling EPT/NPT/SLAT (i.e.: nested page tables)<br />
• With SLAT enabled, the permissions on the PTEs, even if +X, are further limited by those on EPT entries<br />
• With VSM enabled, only <strong>SKM</strong> has permissions to mark EPT entries as executable<br />
• The <strong>SKM</strong> marks an EPT entry as executable only if HVCI confirms that the code pages are signed<br />
according to signing policy