BATTLE OF SKM AND IUM
blackhat2015
blackhat2015
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
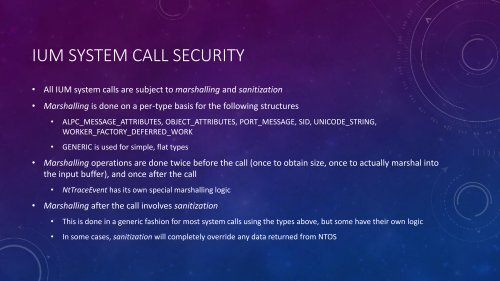
<strong>IUM</strong> SYSTEM CALL SECURITY<br />
• All <strong>IUM</strong> system calls are subject to marshalling and sanitization<br />
• Marshalling is done on a per-type basis for the following structures<br />
• ALPC_MESSAGE_ATTRIBUTES, OBJECT_ATTRIBUTES, PORT_MESSAGE, SID, UNICODE_STRING,<br />
WORKER_FACTORY_DEFERRED_WORK<br />
• GENERIC is used for simple, flat types<br />
• Marshalling operations are done twice before the call (once to obtain size, once to actually marshal into<br />
the input buffer), and once after the call<br />
• NtTraceEvent has its own special marshalling logic<br />
• Marshalling after the call involves sanitization<br />
• This is done in a generic fashion for most system calls using the types above, but some have their own logic<br />
• In some cases, sanitization will completely override any data returned from NTOS