October/November 2015 Digital Edition
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
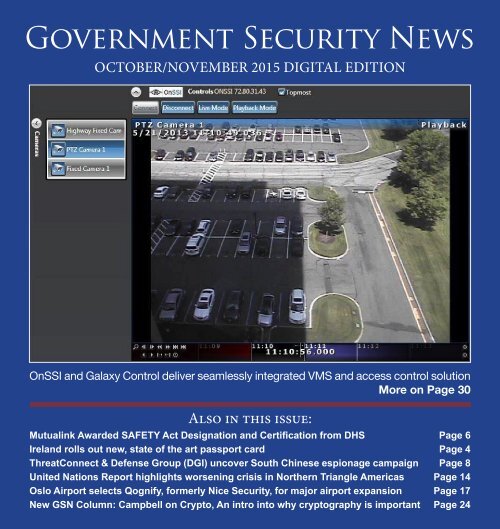
Government Security News<br />
<strong>October</strong>/<strong>November</strong> <strong>2015</strong> <strong>Digital</strong> <strong>Edition</strong><br />
OnSSI and Galaxy Control deliver seamlessly integrated VMS and access control solution<br />
More on Page 30<br />
Also in this issue:<br />
Mutualink Awarded SAFETY Act Designation and Certification from DHS Page 6<br />
Ireland rolls out new, state of the art passport card Page 4<br />
ThreatConnect & Defense Group (DGI) uncover South Chinese espionage campaign Page 8<br />
United Nations Report highlights worsening crisis in Northern Triangle Americas Page 14<br />
Oslo Airport selects Qognify, formerly Nice Security, for major airport expansion Page 17<br />
New GSN Column: Campbell on Crypto, An intro into why cryptography is important Page 24
gSN <strong>October</strong>/<strong>November</strong> <strong>Digital</strong> edition<br />
table of contents<br />
GSN TECHNOLOGY SPOTLIGHT<br />
Under the leadership of CEO Mark Hatten, privately held Mutualink, Inc.<br />
has been awarded the SAFETY Act Designation and Certification from<br />
DHS and is now designated as a Qualified Anti-Terrorism Technology<br />
(QUATT). The company’s interoperable communications platform enables<br />
community-wide sharing of push to talk radio, voice, text, video,<br />
data files and telecommunications in a secure environment. Mutualink<br />
is the only multi-media interoperable communications product certified<br />
under the SAFETY Act. Its products are deployed by hundreds of public<br />
and private entities worldwide, including homeland security and defense<br />
installations. A hands-on demonstration will take place on <strong>November</strong> 3-4<br />
in Alexandria, VA. Read more on Page 6.<br />
Al Bovic, Engineering Chair at the University of Texas, has received an<br />
EMMY for inventing a tool that allows broadcasters and streaming video<br />
sites to compress and distribute video with minimum distortion. Two of<br />
Bovic’s former students, Zhou Wang and Hamed Sheikh and collaborator<br />
NYU University Professor Eero Simonelli were also honored. Their<br />
“SSIM Index” has become a de facto standard in television broadcasting<br />
and has been widely commercialized, and is part of the global ITU standard<br />
H.264 video coding reference software. Read more on Page 27.<br />
2
NEWS AND FEATURES<br />
Ireland rolls out new, state-of-the-art<br />
Passport Card Page 4<br />
Mutualink awarded SAFETY Act<br />
Designation/Certification from Department of<br />
Homeland Security Page 6<br />
ThreatConnect, Inc & Defense Group uncover<br />
extensive South Chinese espionage campaign<br />
targeting South China Sea interests Page 8<br />
FAA Administrator Huerta announces<br />
UAS Registration Task Force Members Page 10<br />
Cloud security trending as preferred<br />
approach for states and other government<br />
agencies Page 12<br />
UN Report Highlights Worsening Refugee<br />
Crisis in the Americas Page 14<br />
NICE Systems now Qognify as Battery Ventures<br />
completes acquisition of physical security unit<br />
Page 16<br />
Oslo Airport selects Qognify,<br />
formerly NICE security, for major airport expansion<br />
project Page 17<br />
Police officers receive life-saving training from<br />
the University of Louisville to help accident and crime<br />
victims Page 20<br />
NTSB confirms wreckage discovered to be<br />
El Faro Page 21<br />
America’s Flagship, The SS United States,<br />
may only have weeks left afloat Page 22<br />
Campbell on Crypto – What comes after perimeter<br />
protection? An intro to why cryptography is important<br />
Page 24<br />
Intelligent Video Surveillance<br />
____________________________________<br />
NSF-supported engineer and vision scientist<br />
Al Bovic awarded Emmy for tool that predicts<br />
perceived video quality Page 27<br />
OnSSI and Galaxy Control deliver seamlessly<br />
integrated VMS and access control solution Provides<br />
Heightened Situational Awareness and Streamlined<br />
Investigations Page 30<br />
PureTech Systems supports upgrade of<br />
Remote Video Surveillance System for Customs and<br />
Border Protection Page 32<br />
Milestone goes wide with new device pack<br />
Page 34<br />
Using video intelligence to protect critical<br />
public infrastructure Page 36<br />
Louroe CEO discusses emerging surveillance<br />
technologies: Audio Analytics Page 38<br />
3
Ireland rolls out new, state-of-the-art<br />
Passport Card<br />
mONtreal, <strong>October</strong> 12, <strong>2015</strong><br />
– international civil aviation Organization<br />
(icaO) eleventh Symposium<br />
and exhibition – DlrS<br />
limited, the leading security printing<br />
company in ireland, today announced<br />
the successful roll-out of<br />
the irish Passport card.<br />
DlrS limited joined forces with<br />
HiD global® ireland teoranta, a<br />
worldwide leader in secure identity<br />
solutions, together with absolute<br />
graphics and Purple Pod, to implement<br />
the irish Passport card project.<br />
Working together, the companies<br />
are providing an end-to-end<br />
solution including enrolment via<br />
mobile app, highly secure icaOcompliant<br />
smart cards, card personalization<br />
and production management.<br />
“The introduction of the passport<br />
card is a significant innovation that<br />
will enhance the travel experience<br />
for irish people as they go on holidays<br />
or business trips to 30 countries<br />
throughout europe,” said minister<br />
for Foreign affairs and trade,<br />
mr. charlie Flanagan t.D, speaking<br />
at the card’s launch in Dublinon<br />
monday 5/10/15.”<br />
DlrS, a leader in security printing,<br />
is the prime<br />
contractor for the<br />
project. additionally,<br />
DlrS provided the<br />
security design, app<br />
development and<br />
security numbering<br />
alongside its partners<br />
HiD global, absolute<br />
graphics and<br />
Purple Pod.<br />
“We have delivered<br />
a state-of the-art Passport card solution,<br />
which leads the way in secure<br />
mrtD deployment and further<br />
demonstrates that ireland is<br />
at the cutting edge of innovation in<br />
the technological arena,” said David<br />
O’connor, Sales Director, DlrS.<br />
The Passport card enrolment process<br />
relies on cutting-edge technology<br />
that adheres to the highest levels<br />
of security. This process allows<br />
users to submit a passport-compliant<br />
photo taken on mobile phones<br />
or upload a suitable photo to the<br />
website, where advanced biometric<br />
algorithms test each one to ensure<br />
icaO standards are reached. Once<br />
all verification checks have been<br />
achieved, the user can pay their fees<br />
through the secure elavon payment<br />
4<br />
gateway (powered by realex Payments).<br />
The new irish Passport card is a<br />
highly sophisticated secure polycarbonate<br />
card with embedded<br />
hologram, crack prevention and<br />
Dbondtm technology, supplied by<br />
HiD global in galway, ireland.<br />
“We are proud to extend our partnership<br />
with DlrS to deliver this<br />
ground-breaking solution to the<br />
Department of Foreign affairs and<br />
the citizens of ireland.” said rob<br />
Haslam, vice president of government<br />
iD Solutions for HiD global.<br />
“The irish Passport card heralds a<br />
new standard in security and durability<br />
for smart cards. This bespoke<br />
implementation of our OSm multitech<br />
technology, combined with the
unique design and mobile applications,<br />
make this a truly exceptional<br />
credential program.”<br />
About HID Global<br />
HiD global is the trusted source<br />
for innovative products, services,<br />
solutions, and know-how related to<br />
the creation, management, and use<br />
of secure identities for millions of<br />
customers around the world. The<br />
company’s served markets include<br />
physical and logical access control,<br />
including strong authentication<br />
and credential management;<br />
card printing and personalization;<br />
visitor management systems; highly<br />
secure government and citizen iD;<br />
and identification rFiD technologies<br />
used in animal iD and industry<br />
and logistics applications. The<br />
company’s primary brands include<br />
activiD®, easylobby®, FargO®,<br />
identrust®, lasercard®, lumidigm®,<br />
Quantum Secure, and HiD®. Headquartered<br />
in austin, texas, HiD<br />
global has over 2,200 employees<br />
worldwide and operates international<br />
offices that support more<br />
than 100 countries. HiD global® is<br />
an aSSa ablOY group brand.<br />
For more information, visit http://<br />
www.hidglobal.com.<br />
About Absolute Graphics<br />
and Purple Pod<br />
absolute graphics is an internationally<br />
recognised design company<br />
specializing in the Passport and<br />
secure documents sector. Having<br />
won regional iD Document of the<br />
Year at the High Security Printing<br />
conference 2014 in milan for the<br />
irish Passport production, absolute<br />
graphics is a well-established player<br />
in the secure document design arena.<br />
Purple Pod is an irish technology<br />
company with considerable experience<br />
in the development of highly<br />
secure mobile applications. They<br />
also specialise in standards based<br />
and bespoke biometric facial recognition<br />
enrolment solutions and have<br />
expertise in every facet of development<br />
technologies from low level<br />
firmware coding to bespoke mobile<br />
app development.<br />
These two companies joined forces<br />
to provide the design and frontend<br />
solutions for the irish Passport<br />
card project.<br />
About DLRS Group<br />
5<br />
DLRS Group Security concepts<br />
is ireland’s largest security printer.<br />
established since 1976, the company<br />
has a production facility in the<br />
republic of ireland servicing the<br />
needs of major financial and government<br />
bodies. DLRS Group Security<br />
concepts is the market leader<br />
in security printed products, with<br />
over 25 years’ experience in passport<br />
manufacture and design. The<br />
company’s reputation for quality<br />
and service is matched only by its<br />
reputation for unrivalled integrity,<br />
developed through working closely<br />
with governments for over 30 years.<br />
DLRS Group Security concepts<br />
is accredited to iSO9001:2008 the<br />
quality standard, iSO14001:2004:<br />
environmental management and<br />
iSO27001:2013: the iS security standard<br />
and cWa 14641:2009 the intergraf<br />
Security Printing Standard.<br />
DLRS Group is a member of the<br />
Smurfit Kappa group, world-leader<br />
in paper based packaging. Operating<br />
in 22 countries in europe,<br />
Smurfit Kappa group is the european<br />
leader in containerboard, solid<br />
board, corrugated and solid board<br />
packaging and has a key position in<br />
several other paper packaging market<br />
segments. The group also operates<br />
in 9 countries in latin america<br />
where it is the only pan-european<br />
operator. More information can be<br />
found at: www.dlrsgroup.com; www.<br />
smurfitkappa.com.<br />
For more information, please contact<br />
salesdlrsgroup@smurfitkappa.ie
Mutualink awarded SAFETY Act<br />
Designation/Certification from<br />
Department of Homeland Security<br />
WalliNgFOrD, conn., <strong>November</strong><br />
2, <strong>2015</strong> – mutualink today announced<br />
that the company’s secure<br />
communications platform for realtime<br />
collaboration has received<br />
Designation and certification from<br />
the U.S. Department of Homeland<br />
Security (DHS) under the SaFetY<br />
act (Support anti-terrorism by<br />
Fostering effective technology).<br />
mutualink is the only multimedia<br />
interoperable communications<br />
product certified under the SaFetY<br />
act and included on the “approved<br />
Products list for Homeland<br />
Security.” mutualink’s DHS Designation<br />
and certification are effective<br />
through <strong>October</strong> 31, 2020.<br />
The SaFetY act, which was authorized<br />
as part of the Homeland<br />
Security act of 2002, provides legal<br />
liability protections to providers<br />
of anti-terrorism technologies that<br />
could save lives in the event of a terrorist<br />
attack. mutualink’s certification<br />
is the highest level of certification<br />
available under the SaFetY<br />
act and requires an extensive and<br />
rigorous product review process involving<br />
product quality assurance,<br />
operational effectiveness and product<br />
capability and reliability verifi-<br />
6<br />
Mark Hatten<br />
cation, among other criteria. Having<br />
achieved this, customers using<br />
mutualink’s certified technology<br />
now have protection under<br />
the SaFetY act from<br />
lawsuits or claims arising<br />
from acts of terrorism.<br />
mutualink – now designated<br />
as a Qualified antiterrorism<br />
technology<br />
(QUatt) – is an iP-based<br />
interoperable multimedia<br />
sharing platform that<br />
securely connects disparate communications<br />
systems for real-time<br />
voice collaboration and real-time<br />
video and information sharing. it<br />
provides agencies, departments<br />
and commercial entities with the<br />
ability to link incompatible land<br />
mobile radio systems together to<br />
share voice, as well as video, data<br />
and geolocation in emergency situations<br />
and daily operations.<br />
“We worked very hard to achieve<br />
SaFetY act certification from<br />
DHS, and we are extremely proud<br />
to be the only multimedia interoperable<br />
communications solution of<br />
its kind to receive this certification,”<br />
said mark Hatten, mutualink’s<br />
ceO. “This will give our customers<br />
continued confidence and assurance<br />
that our technology is not<br />
only effective but can be deployed<br />
without risks of incurring<br />
costly litigation or liability<br />
in the aftermath of a<br />
terror event.”<br />
mutualink’s DHS certification<br />
follows a similar<br />
award from the U.S.<br />
Department of Defense<br />
(DoD) last year. The<br />
company’s multimedia<br />
communications interoperability<br />
solution was granted Joint interoperability<br />
test command (Jitc)<br />
certification for both information<br />
assurance (ia) and interoperability<br />
(iO). mutualink’s multimedia gateway<br />
solution is listed in the DoD’s<br />
approved Products list (aPl) and<br />
is authorized for use by all Services<br />
and agencies of the DoD. mutualink<br />
is also the interoperability communications<br />
platform of choice of
NATO Special Operations Forces<br />
and its command, NSHQ.<br />
Mutualink will offer hands-on<br />
demonstration opportunities at the<br />
National Fusion Center Association<br />
Annual Training Event <strong>November</strong> 3<br />
– 5, <strong>2015</strong>, in Alexandria, VA.<br />
About Mutualink<br />
Mutualink, Inc. has developed an<br />
interoperable communications platform<br />
that enables community-wide<br />
multimedia sharing of push to talk<br />
radio, voice, text, video, data files<br />
and telephone communications in<br />
a secure environment. Mutualink’s<br />
system is currently deployed by<br />
hundreds of public and private entities<br />
worldwide, including homeland<br />
security and defense installations,<br />
NATO Special Operations Forces,<br />
police and fire departments, transit<br />
authorities, hospitals, schools, universities,<br />
shopping malls, casinos,<br />
and more. Mutualink is a privately-held<br />
company headquartered in<br />
Wallingford, Conn., with R&D facilities<br />
in Westford, Mass. and Mayagüez,<br />
Puerto Rico, and Defense<br />
Services office near Washington,<br />
DC. For more information please<br />
visit www.mutualink.net.<br />
DATA CENTER<br />
SECURITY SOLUTIONS<br />
AMERISTARSECURITY.COM | 866-467-2773<br />
7
ThreatConnect, Inc & Defense Group (DGI) uncover<br />
extensive South Chinese espionage campaign targeting<br />
South China Sea interests<br />
Arlington, VA – September<br />
24, <strong>2015</strong> – ThreatConnect, Inc.,<br />
creator of the most widely adopted<br />
Threat Intelligence Platform (TIP),<br />
and open source cyber intelligence<br />
company Defense Group Inc.<br />
(DGI) today unveiled a report attributing<br />
a sophisticated cyber espionage<br />
campaign,<br />
orchestrated by an<br />
Advanced Persistent<br />
Threat (APT)<br />
group known as<br />
“Naikon,” with interests<br />
in the South<br />
China Sea to a<br />
Chinese People’s<br />
Liberation Army<br />
(PLA) unit. Revealing<br />
the scope<br />
of how extensive<br />
cyber campaigns<br />
are readily applied<br />
to ongoing regional<br />
disputes and conflicts, Threat-<br />
Connect and DGI’s joint report,<br />
“Project CAMERASHY: Closing the<br />
Aperture on China’s Unit 78020”<br />
documents Chinese efforts to gain<br />
the upper hand in a geopolitical<br />
stand-off by capturing information<br />
on regional rivals’ negotiating postures,<br />
economies and military capabilities.<br />
The security community has been<br />
aware of Naikon for some time, but<br />
ThreatConnect researchers decided<br />
to take a closer look at this activity<br />
following recent breaches in the<br />
Fiery Cross Reef buildup; Images by <strong>Digital</strong>Globe, via the New York Times, CSIS Asia<br />
Maritime Transparency Initiative, and CNES, via Airbus DS and IHS Jane’s.<br />
U.S. with key similarities. As businesses<br />
are being affected globally by<br />
this malicious activity, ThreatConnect<br />
and DGI felt a responsibility<br />
to inform their global user base and<br />
bring the findings to light for public<br />
consideration. In today’s security<br />
8<br />
landscape, and in a time where the<br />
adversary is often ahead of target,<br />
it is critical to share threat intelligence<br />
that organizations can use to<br />
defend their assets and sensitive information<br />
from malicious attacks.<br />
“At ThreatConnect we are committed<br />
to analyzing intelligence<br />
within our platform<br />
that is associated<br />
with malicious<br />
activity in<br />
order to help arm<br />
others with the<br />
critical knowledge<br />
they need<br />
to protect themselves,”<br />
said Adam<br />
Vincent, CEO of<br />
ThreatConnect.<br />
“Along with DGI,<br />
we followed widely<br />
available and<br />
public evidence<br />
for several months not knowing<br />
where it would lead us. This research<br />
is a perfect example of how true<br />
threat intelligence is highly informative<br />
and offers organizations a powerful<br />
glimpse into just how sophisticated<br />
cyber campaigns operate.”
Key takeaways from the<br />
research report include:<br />
For nearly five years PLA Unit 78020<br />
used an array of global midpoint infrastructure<br />
to proxy the command<br />
and control of customized malware<br />
variants embedded within malicious<br />
attachments or document exploits.<br />
Targets include government entities<br />
in Cambodia, Indonesia, Laos,<br />
Malaysia, Nepal, Philippines, Singapore,<br />
Thailand and Vietnam as<br />
well as international bodies such<br />
as United Nations Development<br />
Programme (UNDP) and the Association<br />
of Southeast Asian Nations<br />
(ASEAN).<br />
Strategic implications for the<br />
United States include cyber threats<br />
against not only military alliances<br />
and security partnerships in the region,<br />
but risks to interests in a major<br />
artery of international commerce<br />
through which trillions of dollars in<br />
global trade traverse annually.<br />
This report stands out from previous<br />
APT reports given the collaborative<br />
nature of the research,<br />
aggregation and analysis of multiple<br />
data sources, application of statisti-<br />
More on page 33<br />
POWER UTILITY<br />
SECURITY SOLUTIONS<br />
AMERISTARSECURITY.COM | 866-467-2773<br />
9
FAA Administrator Huerta announces<br />
UAS Registration Task Force Members<br />
Federal Aviation Administration (FAA) Administrator<br />
Michael Huerta today announced the membership<br />
of the Unmanned Aircraft Systems (UAS)<br />
Registration Task Force. Earl Lawrence, Director of<br />
the FAA’s UAS Integration Office, and Dave Vos of<br />
Google X will co-chair the group.<br />
Department of Transportation (DOT) Secretary<br />
Anthony Foxx and Administrator Huerta announced<br />
the formation of the Task Force last week. The Task<br />
Force membership represents a range of stakeholder<br />
viewpoints, interests and knowledge of the objectives<br />
and scope. Task Force membership was by invitation<br />
only and participation is voluntary.<br />
Interested parties who are not members of the Task<br />
SECURE CARD READERS<br />
FOR ANY NEED<br />
The CHERRY line of secure keyboards and card readers<br />
offer a broad selection to suit your exact needs!<br />
SMART CARD READERS<br />
Contact, contactless and<br />
combination options.<br />
USB SMART CARD READERS<br />
FIPS 201 certified; standalone unit<br />
with weighted base.<br />
SMART CARD KEYBOARDS<br />
FIPS 210 certified, PC/SC smart card<br />
reader and secure PIN entry.<br />
BASIC USE<br />
HEAVY USE<br />
MAXIMUM USE<br />
FREE<br />
WHITE<br />
PAPER<br />
THE TRENDS AND<br />
BENEFITS OF SMART CARD<br />
AND BIOMETRIC DEVICES.<br />
http://bit.ly/1C1pnlY<br />
1-800-844-0797<br />
www.cherrycorp.com/cid<br />
© <strong>2015</strong> ZF ELECTRONIC SYSTEMS PLEASANT PRAIRIE, LLC<br />
10
FAA Administrator<br />
Michael Huerta<br />
Force may submit comments to<br />
the public docket. The Federal<br />
register notice is available for<br />
viewing here.<br />
Sec. Foxx set a deadline of<br />
Nov. 20 for the task Force to<br />
complete its recommendations<br />
and work is already underway.<br />
The group will meet formally<br />
from Nov. 3-5 before developing<br />
recommendations on a<br />
streamlined registration process and minimum requirements<br />
on which unmanned aircraft should be<br />
registered. given the urgency of this issue, the DOt<br />
and Faa will move expeditiously to consider the<br />
task Force’s recommendations.<br />
TASK FORCE MEMBERS INCLUDE:<br />
Nancy Egan – 3D robotics<br />
Richard Hanson – academy of model aeronautics<br />
George Novak – aerospace industries association<br />
Chuck Hogeman and Randy Kenagy – air line Pilots<br />
association<br />
Jim Coon – aircraft Owners and Pilots association<br />
Sean Cassidy – amazon Prime air<br />
Ben Gielow – amazon retail<br />
Justin Towles – american association of airport<br />
executives<br />
Brian Wynne – association of Unmanned vehicle<br />
Systems international<br />
Parker Brugge – best buy<br />
Douglas Johnson – consumer electronics association<br />
Brendan Schulman – DJi<br />
Paul Feldman – general aviation manufacturers<br />
association<br />
Dave Vos – googleX (co-chair)<br />
Tony Bates – goPro<br />
Matt Zuccaro – Helicopter association international<br />
Mike Fergus – international association of<br />
chiefs of Police<br />
John Perry – management association for Private<br />
Photogrammetric Surveyors<br />
Brandon Declet – measure<br />
Randall Burdett – National association of State<br />
aviation Officials<br />
Sarah Wolf – National business aviation association<br />
Baptiste Tripard – Parrot<br />
Tyler Collins – PrecisionHawk<br />
Gregory McNeal – Small Uav coalition<br />
Thomas Head – Walmart<br />
along with the Faa and DOt, the following federal<br />
agencies will provide expert support to the task Force:<br />
Department of Commerce<br />
Department of Defense<br />
Department of Homeland Security<br />
Department of the Interior<br />
Office of Management and Budget<br />
National Aeronautics and Space Administration<br />
Department of State<br />
11
Cloud security trending as preferred approach<br />
for states and other government agencies<br />
By Jayne Freidland Holland<br />
NIC Inc<br />
Cloud computing appears to<br />
be trending as a preferred approach<br />
to enterprise IT, even<br />
for government. State agencies<br />
increasingly are moving to the<br />
cloud – or at least considering it as a<br />
viable option.<br />
It has been reported that some<br />
states, including Kentucky, Ohio,<br />
Utah and Alabama, have embraced<br />
cloud computing as a way to reduce<br />
IT costs and deliver services and applications<br />
to the marketplace more<br />
quickly. Other states, however, remain<br />
skeptical about whether perceived<br />
security risks outweigh the<br />
cost and customer service advantages.<br />
The Cloud’s Benefits and Risks<br />
As cloud computing has gained<br />
credibility, government agencies<br />
have recognized benefits of moving<br />
to the cloud, as well as drawbacks.<br />
Moving data to the cloud can lower<br />
costs because you are paying only for<br />
the capacity and services used. This<br />
reduces the need for onsite personnel<br />
and support and eliminates the<br />
maintenance of hardware,<br />
software and<br />
IT infrastructure associated<br />
with relocating<br />
data. In addition,<br />
cloud resources can be<br />
added relatively inexpensively<br />
in real time,<br />
and data can be shared on demand<br />
anywhere, anytime via the Internet.<br />
On the other hand, the cloud may<br />
offer less control over infrastructure<br />
management and data. It also can<br />
increase the susceptibility to a single<br />
point of failure. And, it can create<br />
risks related to multi-tenancy. For<br />
example, if data is not properly segregated,<br />
an attack on one company’s<br />
data may affect others on the same<br />
server.<br />
When weighing the benefits and<br />
risks of moving to the cloud, one of<br />
the first steps is to carefully analyze<br />
the proposed cloud services agreement.<br />
Service-level agreements vary<br />
widely, differ by provider and often<br />
are non-negotiable. A thorough review<br />
of the agreement will be necessary<br />
to make sure your agency’s<br />
needs and concerns are covered.<br />
Here are some of the key things<br />
to consider when reviewing a cloud<br />
12<br />
services agreement:<br />
• Where will the data reside and<br />
who can access it? It is important<br />
to understand where your data will<br />
be located and who has access to<br />
it. Some providers store data outside<br />
the United States, which, as an<br />
agency, you may be prohibited from<br />
doing by statute. In addition, cloud<br />
providers may allow their subcontractors<br />
to access a customer’s data.<br />
Make sure to ask the prospective<br />
cloud provider who is permitted<br />
to access your data, what kinds of<br />
background checks the service provider<br />
has completed on any personnel<br />
who may access data, and how<br />
access to the data is monitored, as<br />
well as what types of logs are maintained.<br />
• Requisite standards. It is important<br />
to understand whether the<br />
cloud service provider can meet or<br />
satisfy relevant data protection legislation<br />
or industry standards that<br />
may be applicable for your agency,<br />
such as the Payment Card Industry’s<br />
Data Security Standards or the<br />
Health Insurance Portability & Accountability<br />
Act criteria. An agency<br />
should request evidence that the
cloud provider has the appropriate<br />
security measures in place to satisfy<br />
those requirements.<br />
• Liability and damages. also,<br />
be on the lookout for broad exclusions<br />
of liability in cloud provider<br />
agreements. Understand who assumes<br />
liability if data loss occurs<br />
and whether that liability extends<br />
to costs the agency may incur in the<br />
event of an outage.<br />
• Indemnification. in the contract<br />
negotiating process, consider<br />
seeking indemnification for iP infringement,<br />
applicable law, data<br />
protection legislation, regulatory<br />
breaches and losses suffered as a result<br />
of data being removed. While it<br />
may be unlikely to secure this level<br />
of protection, it is recommended<br />
that you request it.<br />
• Warranties. cloud provider<br />
agreements should include performance<br />
warranties for service, reliability<br />
and accuracy. it’s easy to<br />
assume that these warranties are implied,<br />
but if they are not included in<br />
the agreement, it may mean the provider<br />
doesn’t intend to honor them.<br />
request that the contract specify the<br />
relevant warranties.<br />
• Updates and patches. typically,<br />
the cloud provider is contractually<br />
responsible for regularly updating<br />
More on page 26<br />
13
UN Report Highlights Worsening Refugee<br />
Crisis in the Americas<br />
by Walter ewing<br />
The Northern triangle of central<br />
america—comprising el Salvador,<br />
guatemala, and Honduras—is now<br />
one of the most dangerous places<br />
on the planet. The United Nations<br />
estimates that Honduras has the<br />
highest homicide rate in the world,<br />
while el Salvador comes in fifth and<br />
guatemala sixth. it is for this reason<br />
that so many central american<br />
families have made the very difficult<br />
decision to send their children<br />
out of their home countries, bound<br />
primarily to the United States, in<br />
the care of often violent and abusive<br />
smugglers. However, the refugee<br />
crisis currently gripping the<br />
Northern triangle encompasses not<br />
only unaccompanied children, but<br />
mothers with children, as well as entire<br />
families. and it shows no signs<br />
of ending anytime soon.<br />
Related Content: Unaccompanied<br />
Children: A Resource Page<br />
The scope of this crisis, as well as<br />
its level of brutality, are vividly described<br />
in a report from the United<br />
Nations High commissioner for<br />
refugees (UNHcr), titled Women<br />
on the Run. as the report explains,<br />
the women and children who are<br />
arriving at the U.S.-mexico border,<br />
as well as the borders of other<br />
countries in the region, are leaving<br />
places in which government institutions<br />
have effectively lost control<br />
of territory that has come under the<br />
control of armed gangs which kill<br />
with impunity, extort money from<br />
anyone they want, and rape women<br />
as they please.<br />
Consider the story of Norma<br />
in El Salvador:<br />
in late 2014, four gang members abducted<br />
her and took her to a nearby<br />
cemetery. Three of the four proceeded<br />
to rape her; she believes they targeted<br />
her because she was married<br />
14<br />
to a police officer. “They took their<br />
turns…they tied me by the hands.<br />
They stuffed my mouth so i would<br />
not scream.” When it was over, she<br />
said, “They threw me in the trash.”<br />
She contracted a sexually transmitted<br />
disease as a result of the rape.<br />
Not surprisingly, the report found<br />
that, among the thousands of women<br />
and girls from the Northern triangle<br />
who journeyed to the U.S. and<br />
“expressed a fear of being returned<br />
to their home country and were<br />
subject to the credible fear screening<br />
process, U.S. authorities have<br />
found that a large percentage have<br />
a significant possibility of establishing<br />
eligibility for asylum or protec-
tion under the convention against<br />
torture.” However, it is important to<br />
keep in mind that women and children<br />
are not only seeking asylum<br />
in the U.S.—they are also going to<br />
mexico, belize, costa rica, Nicaragua,<br />
and Panama.<br />
mexico’s place in the refugee crisis<br />
is complicated. On the one hand,<br />
there are central american refugees<br />
who are seeking asylum within<br />
mexico. but, on the other hand,<br />
mexico is witnessing its own flow of<br />
refugees from parts of the country<br />
in which conditions have deteriorated<br />
nearly as much as in Honduras or<br />
el Salvador. So, at the same time as<br />
mexican authorities consider offering<br />
safe haven to refugees from the<br />
Northern triangle, they must also<br />
regain control of those stretches of<br />
territory that are now being ruled<br />
and terrorized by gangs and thereby<br />
producing refugee flows.<br />
The report also described the results<br />
of interviews with 160 women<br />
from the Northern triangle and<br />
mexico. Those interviews paint a<br />
grim picture of life in the communities<br />
from which the women fled:<br />
• 85% described living in neighborhoods<br />
controlled by gangs.<br />
• 100% of women who reported<br />
attacks or threats to the police received<br />
no protection or ineffective<br />
protection.<br />
• 64% described direct threats and<br />
attacks by gangs as reasons for fleeing.<br />
• 10% described persecution by<br />
the police.<br />
• 58% of women from Northern<br />
triangle countries described sexual<br />
assault and abuse.<br />
UNHcr recommends that the governments<br />
of the nations to which<br />
these refugees are fleeing respect<br />
the right to asylum, abide by refugee<br />
law, not detain asylum seekers as a<br />
deterrent against the arrival of more<br />
asylum seekers, and seek to address<br />
the root economic, political, and<br />
social causes of the violence that is<br />
forcing so many people from their<br />
homes. and UNHcr emphasizes<br />
that dealing with the refugee crisis<br />
effectively “requires a comprehensive<br />
regional response.” conditions<br />
in the Northern triangle countries<br />
and parts of mexico have spun out<br />
of control. it will require the concerted<br />
effort of more than one nation<br />
to regain control over a very<br />
volatile situation.<br />
Photo Courtesy of UNHCR. See<br />
more at: http://immigrationimpact.<br />
com/<strong>2015</strong>/10/29/un-report-highlights-worsening-refugee-crisis-inthe-americas/#sthash.YYYfCR5M.<br />
dpuf<br />
SAVE MONEY<br />
BY SAVING TIME<br />
Secrets Revealed<br />
7 Solutions to better surveillance<br />
www.SmartMotionVideo.com<br />
15
NICE Systems now Qognify as Battery Ventures<br />
completes acquisition of physical security unit<br />
bOStON, ma – (marketwired -<br />
Sep 21, <strong>2015</strong>) - battery ventures, a<br />
global technology investment firm,<br />
announced today that it has successfully<br />
completed the acquisition<br />
of Physical Security business Unit<br />
(PSbU), formerly part of the security<br />
division of publicly listed Nice<br />
Systems. Through the acquisition,<br />
which was originally announced in<br />
august, battery ventures has established<br />
an independently operating<br />
business named Qognify.<br />
Qognify will build on its leadership<br />
in the physical-security and<br />
mission-critical operations markets<br />
to further help clients capture,<br />
analyze and leverage big data to<br />
anticipate, manage and mitigate security<br />
and safety risks, as well as to<br />
maintain business continuity and<br />
optimize operations. The company’s<br />
customers include banks, utility<br />
companies, airports, seaports, city<br />
centers and transportation systems,<br />
as well as venues hosting<br />
sporting events and major<br />
tourist attractions.<br />
as previously announced,<br />
moti Shabtai, formerly the<br />
general manager of the<br />
PSbU at Nice Systems, has<br />
become president of Qognify.<br />
He is joined by adam<br />
markin, an experienced industry<br />
operator and former<br />
battery ventures executive in residence,<br />
who is the new chairman of<br />
Qognify.<br />
Qognify is headquartered in New<br />
Jersey with additional offices in<br />
london and Singapore, and an r&D<br />
center in israel. as Nice Systems,<br />
the company has been a frequent<br />
gSN awards winner in recent years,<br />
particularly in the airport, Seaport<br />
markets where its video analytics<br />
technologies, integrated security<br />
programs, Situator PSims are now<br />
in use at los angeles airport, Ports<br />
of corpus christi, miami and the<br />
virginia Port authority and other<br />
critical facilities.<br />
more information about Qognify<br />
is available at: www.qognify.com<br />
About Battery Ventures<br />
battery strives to invest in categorydefining<br />
businesses in markets including<br />
software and services, Web<br />
infrastructure, e-commerce, digital<br />
media and industrial technologies.<br />
Founded in 1983, the firm backs<br />
companies at stages ranging from<br />
seed to private equity and invests<br />
globally from offices in boston, the<br />
San Francisco bay area and israel.<br />
Follow the firm on Twitter @BatteryVentures,<br />
visit our website at<br />
http://www.battery.com and find a<br />
full list of Battery’s portfolio companies<br />
here.<br />
16
Oslo Airport selects Qognify,<br />
formerly NICE security, for major<br />
airport expansion project<br />
by using Nicevision, the airport<br />
will be able to respond quickly and<br />
effectively to unfolding incidents to<br />
ensure passenger safety and operational<br />
continuity<br />
ParamUS, <strong>October</strong> 15 - as part<br />
of a major expansion project at<br />
Oslo airport’s terminal 2, slated<br />
for completion in 2017, Qognify,<br />
formerly Nice Security, has been<br />
selected to help ensure operational<br />
efficiency, business continuity and<br />
passenger safety and security, Qognify<br />
announced today.<br />
Oslo airport is already one of the<br />
largest airports in the Nordic region,<br />
and expects to grow its passenger<br />
volume from 24 million to<br />
28 million in the next few years. The<br />
Qognify solution will enable the airport<br />
to effectively manage all types<br />
of incidents, including operational<br />
bottlenecks, safety hazards, and se-<br />
curity threats.<br />
Qognify is working with system<br />
integrator racom to implement a<br />
scalable iP surveillance solution at<br />
the new terminal. by using Nicevision,<br />
the airport will be well-positioned<br />
to:<br />
• Comply with airport regulations<br />
• Quickly gain awareness of unfolding<br />
incidents and their severity,<br />
as well as operational issues<br />
• Ensure consistency of security<br />
and operations across the airport<br />
Arne Grave, CEO, Racom – “Our<br />
partnership with Qognify on this<br />
project has enabled us to design a<br />
solution that fully meets the needs<br />
and expectations of Oslo airport.<br />
This includes an adaptation to modern<br />
video formats, ample storage,<br />
and a robust structure that ensures<br />
access to video in all circumstances<br />
and eventualities.”<br />
Moti Shabtai, President of Qognify<br />
– “The implementation of our<br />
security solutions at one of europe’s<br />
largest airports is a testament to our<br />
leadership in this sector. The pillars<br />
of our security portfolio, Nicevision<br />
can help major transit operations<br />
like Oslo airport streamline<br />
all aspects of incident-handling and<br />
response throughout the entire incident<br />
lifecycle.”<br />
Qognify is an independent company<br />
set off from Nice Systems<br />
Physical Security business Unit<br />
following its acquisition by battery<br />
ventures, a global technology investment<br />
firm.<br />
About Qognify<br />
Qognify solutions help organizations<br />
capture, analyze, and leverage<br />
big data to anticipate, manage, and<br />
mitigate security and safety risks,<br />
maintain business continuity, and<br />
streamline operations. The Qognify<br />
offerings provide valuable insights<br />
that enable enterprises and security-conscious<br />
organizations to take<br />
the best action at the right time by<br />
correlating structured and unstructured<br />
data from multiple sensors<br />
and channels, detecting irregular<br />
patterns, and recognizing trends.<br />
The solutions have been deployed to<br />
help secure a broad range of organizations<br />
and events, such as banks,<br />
utility companies, airports, seaports,<br />
city centers, transportation systems,<br />
major tourist attractions, sporting<br />
events, and diplomatic meetings.<br />
http://www.Qognify.com.<br />
17
Police officers receive life-saving training<br />
from the University of Louisville to help<br />
accident and crime victims<br />
by Steve bittenbender<br />
in a first-of-its-kind event, 16 members<br />
of the louisville metro Police<br />
Department received training to<br />
help them become better first responders<br />
to victims they must tend<br />
to at accidents and crime scenes.<br />
The training on handling arterial<br />
bleeds came from the University of<br />
louisville’s Willed body Program.<br />
in the fresh tissue laboratory in the<br />
school’s Department of anatomical<br />
Sciences and Neurobiology, the<br />
lmPD officers participated in a<br />
day-long session earlier this month<br />
to learn how to properly apply a<br />
tourniquet and other techniques designed<br />
to keep people from bleeding<br />
to death.<br />
The officers worked on cadavers<br />
provided by the school. lmPD officer<br />
Joe Heitzman, who helped organize<br />
the class, said it was the first<br />
time many of his fellow officers got<br />
to work with a cadaver as part of<br />
their training.<br />
“The officers who were in the class<br />
had a great learning experience and<br />
a lot of them told me that the training<br />
was the first time they actually<br />
got to see how trauma affects our<br />
bodies and how to use a tourniquet<br />
correctly to save a life,” Heitzman<br />
said in a press release. “This was an<br />
opportunity that not many officers<br />
will ever get a chance at and they<br />
were excited about the lab.”<br />
law enforcement officers often<br />
arrive on the scene of an accident or<br />
a crime before emergency medical<br />
personnel. Depending on the location<br />
and the severity of a victim’s arterial<br />
bleed, the victim could die in<br />
just a few minutes unless the loss of<br />
blood is staunched.<br />
getting this kind of training is<br />
unique for law enforcement officers,<br />
and those who provided the training<br />
hope it proves its value.<br />
“We are teaching police officers to<br />
save lives. No other form of training<br />
allows for the realism that is provided<br />
by utilizing a tissue lab,” said<br />
brandon Heming, an emergency<br />
medical technician.<br />
in the past, the university has<br />
provided cadavers to military personnel<br />
stationed at Fort Knox<br />
as part of their<br />
20<br />
training, but this was the first time<br />
Uofl had partnered with louisville<br />
police, according to spokeswoman<br />
betty coffman.<br />
Providing such training fits with<br />
the mission of the Willed body Program,<br />
said Nicole Herring, Ph. D.,<br />
the program’s director.<br />
“One of our primary goals for the<br />
Willed body Program is not only<br />
to provide a resource for education<br />
for our medical and dental students,<br />
but for health-care professionals in<br />
our community as well,” Herring<br />
said.<br />
With 1,211 officers, the louisville<br />
metro Police Department is the nation’s<br />
34th largest force, according to<br />
information provided by governing<br />
magazine. The department, which<br />
formed in 2003 after the merger<br />
of louisville and Jefferson county<br />
governments is responsible for patrolling<br />
nearly 400 square miles of<br />
the Kentucky’s largest city.<br />
While this was the first time Uofl<br />
has provided training to lmPD officers,<br />
coffman said the school hopes<br />
it can continue to do so.<br />
However, there<br />
has not been a date<br />
set up for a second session.
NTSB confirms wreckage discovered<br />
to be El Faro<br />
by Steve bittenbender<br />
The National transportation Safety<br />
board on monday confirmed that<br />
wreckage uncovered over the weekend<br />
was that of a vessel lost last<br />
month during Hurricane Joaquin.<br />
On Saturday afternoon, searchers<br />
on board a U.S. Navy vessel used<br />
sonar equipment to detect a vessel<br />
roughly at 15,000 feet below in the<br />
waters near the bahamas, where the<br />
american cargo ship el Faro was<br />
last spotted. Sonar images showed<br />
a nearly 800-foot long ship that appeared<br />
to be intact.<br />
Searchers then used an unmanned<br />
submarine to identify the vessel and<br />
survey for its condition.<br />
eric Weiss, a spokesman for the<br />
NtSb, confirmed the identity of the<br />
ship and said in a one-line statement<br />
that a survey of the ship is continuing.<br />
Now work will begin to find the<br />
voyage data recorder and find out<br />
more information about the final<br />
moments aboard the ship, which<br />
was manned by a crew of 33 americans<br />
and Poles. rescue efforts to<br />
find crew members were suspended<br />
a week after the ship was last seen<br />
afloat, on Oct. 1.<br />
as part of the recovery operation,<br />
which started after rescue mission<br />
ended, the NtSb worked with<br />
the Navy to secure the use of the<br />
U.S.N.S. apache. The tugboat has<br />
been used to assist in the recover<br />
other downed ships and airplanes.<br />
after leaving port in virginia, the<br />
ship arrived at the el Faro’s last location<br />
on Oct. 23.<br />
Searchers aboard the apache<br />
first tried using detection equipment<br />
in an attempt to pick up the<br />
pinger from the el Faro’s recorder.<br />
However, officials stopped that after<br />
three days of unsuccessful attempts<br />
and began using sonar. The wreckage<br />
was discovered during the fifth<br />
round of 13 planned searches.<br />
The wreckage was found using the<br />
Navy’s Orion sonar system, which<br />
can detect vessel in depths of up to<br />
20,000 feet. Naval officials say the<br />
sonar system has a maximum swath<br />
of 3,000 meters to detect for ships<br />
21<br />
and other large objects.<br />
NtSb officials expect the survey<br />
to take about two weeks, but they<br />
warned it could take longer if ideal<br />
conditions are not present.<br />
Owned and operated by tOte<br />
maritime, the 790-foot long el Faro,<br />
built in 1974, received its last coast<br />
guard inspection in march. The<br />
company also conducted an internal<br />
safety audit just prior to that<br />
inspection. The ship departed from<br />
Jacksonville, Fla., on Sept. 29 with<br />
San Juan, P.r., as its scheduled destination.<br />
according to the NtSb, the el<br />
Faro left about three hours after a<br />
hurricane warning has been issued<br />
by the National Hurricane center.<br />
On the day before it sank, the el Faro’s<br />
captain e-mailed a tOte safety<br />
officer to confirm he planned to<br />
take a route to the south of Joaquin’s<br />
predicted path.<br />
The el Faro was last heard from<br />
on the morning of Oct. 1 as it had<br />
taken on water due to the rough<br />
seas created by Hurricane Joaquin.<br />
at that time, Joaquin pounded the<br />
caribbean nation with winds of up<br />
to 130 miles an hour, making it a<br />
powerful category 4 hurricane.
America’s Flagship, The SS United States, may<br />
only have weeks left afloat<br />
NeW YOrK, NY…<strong>October</strong> 07,<br />
<strong>2015</strong>— The board of Directors of<br />
the SS United States conservancy<br />
released the following statement<br />
today announcing that despite<br />
considerable progress toward finding<br />
a permanent home and viable<br />
redevelopment plan for america’s<br />
Flagship, the organization will be<br />
forced to sell the historic vessel to<br />
a responsible metals recycler by the<br />
end of <strong>October</strong> unless new donors<br />
or investors come forward.<br />
Th e SS United States is the largest<br />
and most advanced ocean liner<br />
ever built in her namesake nation.<br />
launched in 1952, the United States<br />
was developed as part of a top Secret<br />
cold War project to build the<br />
fastest ship in the world. She still<br />
holds the transatlantic speed record.<br />
The ship is an iconic symbol<br />
of america’s post-war power, pride<br />
and innovation. The statement appears<br />
below:<br />
“after much deliberation and<br />
consultation, the SS United States<br />
conservancy’s board of Directors<br />
has decided to retain a broker to explore<br />
the potential sale of america’s<br />
Flagship, the SS United States to a<br />
responsible, U.S.-based metals recycler.<br />
“We have achieved an extraordinary<br />
amount of progress in support<br />
of the SS United States’ potential<br />
redevelopment in recent months,<br />
including detailed plans, financial<br />
models, renderings, and engineering<br />
approaches with support from a<br />
number of major firms. in so many<br />
ways, we’ve never been closer to saving<br />
america’s Flagship, but we have<br />
Photo: Courtesy of Nick Landiak<br />
also never been closer to losing this<br />
irreplaceable piece of our history.<br />
“The conservancy has been very<br />
clear in its communications to its<br />
supporters and the media that the<br />
carrying costs for the vessel total<br />
more than $60,000 per month.<br />
While our fundraising efforts have<br />
enabled us to meet those continuing<br />
obligations to date, thanks to<br />
the steadfast support of donors<br />
from across the nation and around<br />
22<br />
the world, the financial burdens imposed<br />
by the ship’s ongoing expenses<br />
have become unsustainable.<br />
“The conservancy continues to<br />
do everything within its power to<br />
advance an outcome that protects<br />
the vessel, preserves her historical<br />
legacy, and secures a viable redevelopment<br />
program. as we have announced<br />
previously, redevelopment<br />
negotiations are ongoing. We have<br />
identified two potential locations<br />
that can accommodate the ship, and<br />
we are continuing complex talks<br />
with various entities regarding these<br />
sites. These ongoing discussions<br />
remain subject to confidentiality<br />
agreements signed by both parties.<br />
“Despite this progress in our redevelopment<br />
negotiations, the tim-
ing of additional financial support<br />
from our partners may come too<br />
late, in the absence of another party<br />
willing to support the conservancy<br />
or assume responsibility for the vessel<br />
at this time.<br />
“if donors or investors step forward<br />
by the end of the month who<br />
are ready, willing, and able to help<br />
the conservancy, america’s Flagship<br />
could still be saved. However,<br />
if progress toward a new sales option<br />
or an infusion of funds does<br />
not occur by <strong>October</strong><br />
31, <strong>2015</strong>, we will<br />
have no choice but<br />
to negotiate the sale<br />
of the ship to a responsible<br />
U.S.-based<br />
recycler.<br />
“given the lead<br />
time required to<br />
broker the vessel’s<br />
potential sale, we believe<br />
it would be irresponsible<br />
to delay<br />
the start of this contingency<br />
planning.<br />
“choosing to explore these options<br />
was a gut-wrenching decision<br />
for the board, but the conservancy<br />
simply cannot exhaust all of its<br />
funds, leaving the organization in<br />
debt or with no resources to support<br />
its curatorial and education<br />
mission.<br />
“We remain deeply committed to<br />
honoring the legacy of the SS United<br />
States through our curatorial and<br />
educational programs, and we will<br />
continue to prioritize this important<br />
work.<br />
“We take our responsibility to our<br />
supporters and to the conservancy’s<br />
mission very seriously, which is<br />
why we believe that despite recent<br />
progress and potentially positive<br />
scenarios, this course of action is<br />
necessary.<br />
“The sale of the vessel to a recycler<br />
is by no means inevitable. We<br />
remain hopeful that our developers<br />
can continue to advance their efforts<br />
or that additional financial support<br />
will be found in time.<br />
“ Th eSS United States is a unique<br />
and endangered historic landmark<br />
that has captivated the imagination<br />
of millions. We are determined to<br />
do everything possible during these<br />
final weeks to try to save her.<br />
“ Th eSS United States’ supporters<br />
from across the country and around<br />
the world have become like family.<br />
We have worked together against<br />
the odds to keep the nation’s last<br />
remaining and greatest ocean liner<br />
safely afloat. The ship has faced previous<br />
dangers and has withstood<br />
them, and we hope she can beat the<br />
23<br />
Photo: Courtesy of Charles Anderson<br />
odds again. anything less would<br />
be, as Walter cronkite once said, “a<br />
crime against history.”<br />
Those interested in making a taxdeductible<br />
contribution to the SS<br />
United States conservancy can do<br />
so at www.SSUSc.org.<br />
About the SS United States<br />
Conservancy<br />
a national nonprofit organization,<br />
the SS United States conservancy<br />
leads the global effort to save and<br />
repurpose america’s Flagship, the<br />
SS United States. The conservancy<br />
raises public awareness and financial<br />
resources for the maintenance,<br />
restoration and ultimate reuse of<br />
this iconic vessel and works to ensure<br />
that the fastest ocean liner ever<br />
to cross the atlantic remains an inspiration<br />
for generations to come.<br />
For more information about the SS<br />
United States visit www.ssusc.org.<br />
MEDIA CONTACT: Tom Basile –<br />
Tbasile@EmpireStrategy.com<br />
917-579-2216
Campbell on Crypto<br />
What comes after perimeter protection?<br />
An intro to why cryptography is important<br />
By Shaun Campbell<br />
According to the <strong>2015</strong> 1H Breach<br />
Level Index Report from Gemalto,<br />
888 security breaches were reported<br />
in the first half of <strong>2015</strong>. Those<br />
breaches resulted in the unauthorized<br />
access of 245,191,393 records.<br />
Advances in technology used by<br />
hackers means that protecting the<br />
perimeter is not enough to ensure<br />
that your sensitive data is not compromised.<br />
Identity theft was the leading<br />
type of breach, the report indicates.<br />
There was also a shift<br />
in attack targets, with<br />
a dramatic rise in data<br />
records stolen from<br />
state-sponsored attacks.<br />
Healthcare and<br />
government overtook<br />
retail as the major affected<br />
sectors, and<br />
outside attacks have begun to overtake<br />
those from within.<br />
All this means that perimeter security<br />
isn’t effective for protecting<br />
your organization from breaches.<br />
For real protection of sensitve data,<br />
you have to focus on protecting<br />
your data, not your network. That’s<br />
why cryptography (or “crypto”) is<br />
becoming increasingly important.<br />
Securing the network<br />
is yesterday’s news<br />
Today’s enterprises (commercial<br />
and public sector) are not making<br />
appropriate investments in security.<br />
Most are using an outdated view of<br />
the realities of security breaches.<br />
Because data breaches have continually<br />
increased in frequency and<br />
size, breach prevention is becoming<br />
irrelevant as protection from cyber<br />
Simple breach prevention just doesn’t cut it<br />
any more. Hackers can be criminals, rogue<br />
nations, or disgruntled insiders, and they<br />
all pose a real threat to data.<br />
attacks.<br />
That kind of strategy is yesterday’s<br />
news. Gone are the days when<br />
hackers were more interested in<br />
just proving they could break in. In<br />
those days, sensitive data was centralized,<br />
and a desktop PC was the<br />
edge of the enterprise network.<br />
It was enough at the time to con-<br />
24<br />
sider network<br />
perimeter<br />
“breach-prevention”<br />
technology,<br />
such<br />
as firewalls, as<br />
the go-to security<br />
method. These days, however,<br />
data is distributed, not centralized,<br />
so simple breach prevention just<br />
doesn’t cut it any more. Hackers can<br />
be criminals, rogue nations, or disgruntled<br />
insiders, and they all pose<br />
a real threat to data.<br />
The insider threat<br />
can’t be discounted.<br />
Every organization,<br />
including government<br />
agencies, can<br />
fall victim to someone<br />
already inside<br />
the protected perimeter.<br />
Focusing on perimeter protection<br />
does nothing to protect against<br />
misuse or just plain carelessness.<br />
Let’s not overlook carelessness.<br />
Using personal email accounts to<br />
bring work home, losing devices,<br />
storing important information on<br />
thumb drives, or sharing network<br />
credentials and passwords can lead
to the accidental leaking of sensitive<br />
data.<br />
In fact, it’s best these days to just<br />
accept the fact that you can’t fully<br />
prevent breaches of network security.<br />
Instead of securing the network,<br />
you need to focus on securing the<br />
data.<br />
How to protect your data –<br />
a quick overview<br />
The world of cyber security becomes<br />
a simpler place when you accept<br />
that breaches will happen. Extending<br />
your focus from just securing<br />
the perimeter to also securing the<br />
data should be Job One.<br />
Most of the threat today is what’s<br />
in the information, not how you access<br />
an entity. It has become very<br />
easy for hackers to insert attacks<br />
into content that allow them to<br />
open channels through the boundary<br />
that no one knows about. As we<br />
mentioned earlier about carelessness,<br />
people already use open channels<br />
in firewalls to send content via<br />
email. Information is not blocked at<br />
the firewall. Malware or other malicious<br />
content may have already<br />
compromised the network. Once<br />
the affected content has gotten in<br />
past the boundary, that’s when the<br />
real problems begin.<br />
It can be a challenge to secure<br />
data. These days, the cloud, virtualization,<br />
and an increasingly mobile<br />
workforce have made the potential<br />
inroads to attack much broader. It’s<br />
understandable that some agencies<br />
might choose to use “containment”<br />
strategy to control where data can<br />
go, and to limit access to a small<br />
group of authorized users.<br />
The problem with basing your<br />
security plans on restricting data<br />
access is that it flies in the face of<br />
what most agencies are trying to<br />
do – namely, to using big data and<br />
analysis to improve efficiency and<br />
productivity, and to help fulfill mission<br />
objectives.<br />
Rather than saying “no,” agencies<br />
should be looking for more ways to<br />
say “yes” – to build security plans<br />
based on the mandate to move and<br />
share data. Here are three quick<br />
things to keep in mind:<br />
• Know your data: You need to<br />
know what you need to protect.<br />
Then you have to control access and<br />
authentication of users.<br />
• Protect your data: The best way<br />
to protect your data is to lock it. Encrypt<br />
all sensitive data at rest and<br />
in motion. Make sure that if data is<br />
taken out of your network it can’t<br />
be used for malicious purposes because<br />
of the strength of the encryption.<br />
• Manage your protection: Encryption<br />
seals your data so it can’t be<br />
used by anyone but you. Then you<br />
have to manage it, because if you<br />
lose your encryption key, you can’t<br />
use the data, either. Securely store<br />
25<br />
and manage all of your encryption<br />
keys.<br />
There is no “one size fits all” approach<br />
for securing data in case<br />
your network security is breached,<br />
and of course you still have to reprotect<br />
your network if the perimeter<br />
is violated. These three steps<br />
are just a skeleton to make sure you<br />
don’t suffer the expense and other<br />
consequences that come in the aftermath<br />
of a security incident.<br />
In future installments of this column,<br />
we will take a closer look at<br />
different aspects of cryptography<br />
and discuss how it can be utilized as<br />
the most effective form of data protection.<br />
GSN is pleased to add “Campbell on<br />
Crypto” as an ongoing new column.<br />
Shaun Campbell, a nationally-recognized<br />
cryptography expert, is VP of<br />
Product Management For SafeNet<br />
Asssured Technologies. Prior to his<br />
12-year service at SafeNet, he held<br />
high-level security positions at The<br />
Windermere Group, A.T. Kearney,<br />
Booze Allen Hamilton and CSC. He<br />
spent eight years in the U.S. Air Force<br />
developing his expertise in cryptography<br />
and cyber security.
Cloud security trending as for<br />
government agencies<br />
Continued from page 13<br />
its system and completing necessary<br />
patches. This may depend upon the<br />
specific service level selected, so it<br />
is important to understand who has<br />
responsibility for this. If the provider<br />
is responsible, the agreement<br />
should confirm that updates and<br />
patches will be implemented in a<br />
timely fashion.<br />
• Breach notification procedures.<br />
The agreement also should<br />
detail notification procedures, as<br />
well as how and when data can be<br />
accessed in the event of a security<br />
breach, in addition to any log file<br />
access that would be necessary to<br />
help determine what happened. The<br />
agreement also should be specific<br />
about whether or not your agency<br />
can bring in an independent forensic<br />
team to review how the attack<br />
occurred and what remediation<br />
steps must be taken.<br />
• Disaster recovery. The cloud<br />
provider should offer, at a minimum,<br />
disaster recovery policies that<br />
meet industry standards. Review<br />
the provider’s general protections,<br />
type of backup services provided<br />
and business continuity practices.<br />
• The long-term outlook. Once<br />
you have made the move to the<br />
cloud, it can be hard to transition<br />
back out. Accordingly, the agreement<br />
should delineate very clearly<br />
how long it will take and what steps<br />
will be required to retrieve your<br />
data if you decide at some point to<br />
move out of the cloud.<br />
In addition to the points noted<br />
above, having a cloud strategy and<br />
performing due diligence is essential<br />
for an agency considering a<br />
move to the cloud. Such due diligence<br />
should include a thorough<br />
evaluation of the provider’s years of<br />
experience, how much content the<br />
provider has under contract and the<br />
company’s track record protecting<br />
data.<br />
The cloud can present several benefits,<br />
as well as a number of risks.<br />
Determining what is best for any<br />
government agency involves a careful<br />
review of the terms and conditions<br />
contained the agreement, plus<br />
a calculated, upfront risk/benefit examination,<br />
free of any assumptions,<br />
to reveal whether the time is right to<br />
make a move to the cloud.<br />
About the author: Jayne Friedland<br />
Holland is Chief Security Officer at<br />
NIC Inc. (NASDAQ: EGOV), the<br />
country’s dominant provider of egovernment<br />
services and secure payment<br />
processing. Contact her at jayne@<br />
egov.com.<br />
Post Your Video on<br />
the Busiest Website<br />
in Homeland Security!<br />
To Place Your Order or Get Further Information, Contact:<br />
Mike Madsen, Publisher, at 732-233-8119, or mmadsen@gsnmagazine.com<br />
26
Intelligent Video Surveillance<br />
NSF-supported engineer and vision scientist Al Bovic<br />
awarded Emmy for tool that predicts perceived video quality<br />
27<br />
September 30, <strong>2015</strong> – Sometimes it’s<br />
not so much what you see as what<br />
you don’t see that matters.<br />
alan bovik led a team of researchers<br />
that, in the early 2000s, invented<br />
a tool to predict how the average<br />
person will perceive the quality of<br />
an image or a video. The tool allows<br />
broadcasters and streaming video<br />
sites to compress and distribute video<br />
with minimal distortion.<br />
So, every time you don’t see jagged<br />
images, blurring, glitches or the<br />
dreaded spinning wheel of death<br />
on tv or the internet, that’s likely<br />
thanks in part to the Structural<br />
Similarity index that bovik and his<br />
research team created.<br />
For his efforts, bovik and three<br />
of his colleagues will each receive<br />
television’s highest honor, an individual<br />
Primetime emmy award for<br />
Outstanding achievement in engineering<br />
Development from the<br />
television academy (formerly the<br />
academy of television arts and Sciences).<br />
bovik--the ernest J. cockrell<br />
endowed chair in engineering at<br />
The University of texas at austin-<br />
-will receive his emmy statuette at<br />
the Primetime emmy engineering<br />
awards ceremony at loew’s Hollywood<br />
Hotel on Oct. 28,<br />
<strong>2015</strong>. two of bovik’s former<br />
PhD students, Zhou<br />
Wang (now at the University<br />
of Waterloo, canada)<br />
and Hamid Sheikh (now at<br />
Samsung, Dallas) will also<br />
receive individual emmy<br />
statuettes for this work,<br />
along with eero Simoncelli,<br />
their collaborator at NYU.<br />
“an engineering emmy award is<br />
bestowed upon an individual, company<br />
or organization for developments<br />
in engineering that are either<br />
so extensive an improvement on<br />
existing methods, or so innovative<br />
in nature, that they materially affect<br />
the transmission, recording or reception<br />
of television,” the television<br />
academy wrote.<br />
bovik was initially surprised<br />
about the emmy--in fact, he found<br />
out about the award while reading<br />
his email in the morning, on his way<br />
to brush his teeth. eventually, his<br />
surprise gave way to appreciation.<br />
“i’m very happy and grateful that<br />
people are recognizing our work,”<br />
bovik said. “i so appreciate NSF<br />
support of our research and our students,<br />
who are so much of the inspiration<br />
and perspiration behind research<br />
success. if you have<br />
good ideas, this kind of<br />
support can change your<br />
life.”<br />
Compression issues<br />
Due to limits in bandwidth<br />
and the ever-expanding<br />
Al Bovic number of streaming videos,<br />
broadcasters need to<br />
compress their video before sending<br />
it over the airwaves or the internet.<br />
This compression can cause a range<br />
of problems, from blurring to blackouts,<br />
which make watching a broadcast<br />
unpleasant or distracting.<br />
“What you would like to be able<br />
to do is have a reliable way of determine<br />
acceptable levels of perceived<br />
quality--as a human viewer would<br />
report it,” bovik said. “This is particularly<br />
important to cable and<br />
satellite video content carriers in<br />
regards to how much they compress<br />
the television signal.”<br />
“it’s not like a certain compression<br />
level will give the same quality for<br />
every video. You actually have to do<br />
something content dependent, and<br />
being able to predict the perceived<br />
quality of a compressed video while<br />
accounting for content makes a big<br />
More on page 28
Intelligent Video Surveillance<br />
NSF support: tool that predicts<br />
perceived video quality<br />
Continued from page 27<br />
difference.”<br />
The Structural SIMilarity (SSIM)<br />
index is a method for measuring the<br />
similarity between a compressed image<br />
or video and the uncompressed<br />
original, in terms of human<br />
perception. Today,<br />
SSIM is part of the technological<br />
toolkit used by<br />
most major broadcasters<br />
and cable and satellite<br />
companies around the<br />
world, including AT&T,<br />
Comcast, NBC, FOX and<br />
PBS.<br />
Technology manufacturers<br />
such as Cisco, Motorola<br />
(Arris), Intel and<br />
Texas Instruments rely<br />
on SSIM to ensure the<br />
broadcast, networking<br />
and TV equipment they produce<br />
maintains the best possible video<br />
quality.<br />
When Bovik and his team started<br />
working on the issue of predicting<br />
how people would perceive video<br />
quality, they faced some difficult<br />
challenges. At the time, state-ofthe-art<br />
prediction algorithms either<br />
did not account for how humans<br />
perceive distorted images, or were<br />
too computationally intensive to<br />
be practical. Drawing from neuroscience<br />
models of low-level vision,<br />
the SSIM model disruptively solved<br />
both problems by providing the<br />
world’s best solution to the video<br />
quality prediction problem at at a<br />
low computational cost.<br />
“The first breakthrough was a<br />
very simple model developed by an<br />
advanced graduate student, Zhou<br />
Wang and myself called Universal<br />
Quality Index. We later developed<br />
the final SSIM model with another<br />
grad student (Hamid Sheikh) and<br />
our NYU collaborator, Professor<br />
Eero Simoncelli,” Bovik said.<br />
The students’ efforts were critical,<br />
Bovik said, particularly Wang’s<br />
development of the efficient SSIM<br />
model and Sheikh’s NSF-supported<br />
large-scale human study of picture<br />
quality.<br />
“NSF support of graduate students<br />
28<br />
is a major reason for the success of<br />
many research projects,” Bovik said.<br />
Early in Bovik’s academic career-<br />
-back in the mid-1980s--he began<br />
collaborating with visual psychologists<br />
and neuroscientists to better<br />
understand perception. In the process,<br />
he became an accomplished vision<br />
scientist.<br />
With support from<br />
NSF, he applied discipline-crossing<br />
theories<br />
about how humans see<br />
and perceive objects and<br />
motion, and used them<br />
to accurately assess how<br />
naturalistic or distorted<br />
an image or video would<br />
appear to a human viewer.<br />
Among the insights<br />
from visual perception<br />
theory that the SSIM<br />
model incorporates are:<br />
Contrast masking, where the<br />
texture or “busyness” causes image<br />
distortions to become less perceptible.<br />
Luminance masking, whereby<br />
distortion is less visible in brighter<br />
regions.<br />
And structural similarity, the<br />
idea that visually important structures,<br />
such as edges and details, are<br />
modified or destroyed by compression,<br />
which can also give rise to new<br />
“false” structures that are perceived
as distortion. Humans perceive visual<br />
distortions, such as compression,<br />
blur or noise, remarkably consistently<br />
with each other.<br />
When Bovik’s team tested their<br />
SSIM index on the world’s largest<br />
databases, including as many as<br />
25,000 human judgments of quality,<br />
they found it successfully predicted<br />
human quality assessments to a<br />
larger degree than any previous algorithms.<br />
This was later confirmed<br />
on even larger datasets containing<br />
more than 250,000 human judgments<br />
of picture distortion.<br />
“When distortions such as blur,<br />
noise, compression artifacts and<br />
channel errors appear, it’s something<br />
that your brain responds to very<br />
quickly,” Bovik said. “It’s instantly<br />
annoying to some degree and that<br />
degree of annoyance is amazingly<br />
consistent among humans.”<br />
The SSIM model has proved indispensable<br />
to broadcasters and has become<br />
a de facto industry standard,<br />
widely commercialized around the<br />
globe in a variety of products.<br />
Beyond its adoption as a standard<br />
tool in broadcast and postproduction<br />
houses throughout the<br />
television industry, the SSIM index<br />
is part of the global ITU standard<br />
H.264 video coding reference software--one<br />
of the most commonly<br />
used formats for the recording,<br />
compression and distribution of<br />
video content. This allows developers<br />
everywhere to “SSIM-optimize”<br />
their encoder implementations and<br />
rate-control protocols.<br />
“This research is an excellent example<br />
of how a deep understanding<br />
of basic science can lead to technological<br />
advances that have positive<br />
benefits across the globe,” said<br />
Lynne Parker, division director for<br />
Information and Intelligent Systems<br />
at NSF. “Dr. Bovik’s research team<br />
has translated a scientific understanding<br />
of human perception into<br />
vast improvements in our global,<br />
video-based communications technologies.<br />
Breakthrough advances<br />
such as the SSIM index illustrate the<br />
broad impact that is possible as a result<br />
of investment in fundamental,<br />
interdisciplinary research.”<br />
Other applications<br />
Bovik and his students did not stop<br />
with SSIM. He has gone on to create<br />
many newer technologies for<br />
image processing and video quality<br />
assessment with NSF funding. These<br />
include MOVIE (the MOtion-based<br />
Video Integrity Evaluation) index<br />
for video quality assessment, the<br />
DIIVINE, BRISQUE, BLIINDS and<br />
NIQE no-reference image and video<br />
quality models and the LIVE Image<br />
and Video Quality Databases.<br />
Recently, again with funding from<br />
NSF, he created algorithms that can<br />
assess the quality of images without<br />
an original reference image--an<br />
29<br />
even trickier task. This research was<br />
inspired in part by work by a famous<br />
result in visual neuroscience<br />
that suggests that images of the real<br />
world, if they are of good quality,<br />
obey certain statistical laws.<br />
“These laws can be used to explain<br />
the success of the SSIM model and<br />
of other algorithms that we’ve created,<br />
and we have also used them<br />
to design the new breed of ‘blind’<br />
models that do not need a reference<br />
signal,” Bovik said. “The human visual<br />
system has evolved in response<br />
to those statistics. By observing<br />
those statistics, we can predict how<br />
neurons will respond to the early<br />
vision system and vice-versa: by<br />
examining the brain, we can get insights<br />
into natural scene statistics. If<br />
you have a photograph or video and<br />
it doesn’t obey those scene statistics,<br />
then it’s likely been distorted.”<br />
Bovik and his team are applying<br />
this idea to a range of digital image<br />
quality issues. Their solutions range<br />
from algorithms can give digital<br />
cameras the ability to determine<br />
whether photographs are objectively<br />
“good,” to systems that can significantly<br />
improve the accuracy of<br />
facial recognition, to advanced image<br />
capture methods using infrared<br />
and other wavelengths.
Intelligent Video Surveillance<br />
OnSSI and Galaxy Control deliver seamlessly integrated<br />
VMS and access control solution Provides Heightened<br />
Situational Awareness and Streamlined Investigations<br />
Pearl River, NY, <strong>October</strong> 29 - In<br />
continuing to deliver higher performance<br />
and added value to customers,<br />
OnSSI announces that the System<br />
Galaxy access control solution<br />
from Galaxy Control Systems fully<br />
integrates and supports the Company’s<br />
Ocularis 5 Video Management<br />
Software (VMS). The integration<br />
of these industry- leading VMS<br />
and access control solutions provides<br />
users with greatly enhanced<br />
real-time situational awareness and<br />
significantly streamlines the postevent<br />
investigation process.<br />
“The correlation of video and access<br />
control provides users with an<br />
effective, efficient and intelligent<br />
solution that is proven to improve<br />
overall security and heighten situational<br />
awareness,” said Ken La-<br />
Marca, VP of Sales and Marketing,<br />
OnSSI. “The integration with Galaxy<br />
Control Systems was facilitated<br />
by Ocularis’ open architecture,<br />
which enables the ability to process<br />
comprehensive intelligence across<br />
multiple platforms.”<br />
Working in concert with System<br />
Galaxy, OnSSI’s Ocularis 5 provides<br />
critical information that lets operators<br />
quickly assess situations as<br />
they unfold, and use the information<br />
gathered to determine the best<br />
course of action.<br />
“The combination of Ocularis 5<br />
30<br />
and System Galaxy creates a unique<br />
and powerful VMS-Access Control<br />
solution that capitalizes on the combined<br />
strengths of these respective<br />
platforms to improve overall safety<br />
and security,” said Robert Laughlin,<br />
President, Galaxy Control Systems.<br />
“The latest version of System Galaxy<br />
includes enhancements that further<br />
enhance the user experience and<br />
streamline installation, while providing<br />
a comprehensive access and<br />
surveillance management platform<br />
by integrating OnSSI’s Ocularis 5.”<br />
The seamless integration between<br />
Ocularis 5 and System Galaxy enables<br />
real-time access control activity<br />
and user-defined, real-time<br />
on-screen event annotation. Each<br />
door can be assigned a preset NVR/<br />
DVR and camera, with alerts triggered<br />
by valid or invalid access attempts,<br />
which are tied to pre- and<br />
post-event video. Upon receiving an<br />
alert, operators can engage the full<br />
power of both Ocularis and System<br />
Galaxy to quickly and easily retrieve<br />
live video, control cameras, lock/<br />
unlock doors and much more. In<br />
addition to delivering unprecedented<br />
real-time situational awareness<br />
the combined solution provides
faster and more accurate retrieval of<br />
correlated video and data for more<br />
effective and efficient post-event investigations.<br />
Ocularis 5 is based on a new recorder<br />
that accommodates a significantly<br />
higher density of cameras<br />
per recorder while maximizing<br />
HDD storage without the need for<br />
user configuration. It features automatic<br />
load balancing for managing<br />
recordings across system servers.<br />
Ocularis 5 also allows for multiple<br />
different recorders to be combined<br />
under the same Base (including<br />
legacy Ocularis 4.X recorders) with<br />
centralized user and event management.<br />
System Galaxy is a scalable, enterprise-class<br />
access control and<br />
management solution, seamlessly<br />
integrates security and building<br />
management functions. Additional<br />
features include active directory<br />
support to enable real-time identity<br />
management, individualized identity-based<br />
door access, and the ability<br />
to generate specific reports for each<br />
screen view or credential holder.<br />
Data can be shared with other systems<br />
such as time and attendance,<br />
visitor management, time clocks,<br />
parking garages and personal messaging.<br />
System Galaxy accommodates<br />
unlimited users and is also<br />
accessible from mobile web browsers<br />
and designed for backward compatibility<br />
with all legacy Galaxy systems.<br />
For more information on OnSSI visit<br />
www.onssi.com.<br />
About OnSSI<br />
On-Net Surveillance Systems, Inc.<br />
(OnSSI) was founded in 2002 with<br />
the goal of developing comprehensive<br />
and intelligent IP video surveillance<br />
management software. OnSSI’s<br />
Ocularis IP security and surveillance<br />
VMS platform increases security,<br />
reduces operational costs, and<br />
helps organizations move closer to<br />
prevention. Ocularis delivers open<br />
architecture, flexibility, and scalability<br />
for a range of applications including<br />
education, gaming, government,<br />
healthcare, manufacturing,<br />
public safety, transportation, and<br />
utilities. OnSSI is headquartered in<br />
Pearl River, New York and has representation<br />
in over 100 countries.<br />
With its acquisition of Germanybased<br />
VMS company, SeeTec AG<br />
and the launch of Ocularis 5, OnSSI<br />
continues to drive global expansion<br />
and technological innovations.<br />
31<br />
About Galaxy Control Systems<br />
Galaxy Control Systems, a privately<br />
held company headquartered in<br />
Walkersville, MD, is a leader in the<br />
integrated access control industry.<br />
The company’s hardware and software<br />
solutions, all manufactured<br />
in the USA, provide access control,<br />
video surveillance, alarms, photoimaging,<br />
badging, elevator control,<br />
building management and time and<br />
attendance for small applications,<br />
fully integrated security management<br />
systems and enterprise-class<br />
control systems. All Galaxy Control<br />
Systems products are scalable and<br />
backwards compatible, designed<br />
and engineered to deliver lower Total<br />
Cost of Ownership and a higher<br />
Return on Investment than competitive<br />
products. With unsurpassed<br />
technical support, Galaxy supports<br />
their reseller partners with free ongoing<br />
training while providing the<br />
highest levels of system implementation<br />
and maintenance.<br />
For more information on Galaxy<br />
Control Systems’ extensive line of<br />
products, visit www.galaxysys.com.
Intelligent Video Surveillance<br />
PureTech Systems supports upgrade of<br />
Remote Video Surveillance System for Customs<br />
and Border Protection<br />
PHOeNiX, aZ. -- Puretech Systems<br />
inc., a leading manufacturer<br />
of geospatial video analytic software,<br />
today announced that it recently<br />
completed the initial field<br />
deployment and test of the remote<br />
video Surveillance System (rvSS)<br />
Upgrade for the U.S. customs and<br />
border Protection (cbP). This test<br />
successfully demonstrated the technical<br />
capabilities of the system and<br />
was a key program milestone in its<br />
deployment schedule, which includes<br />
installation at additional border<br />
patrol stations this year.<br />
USbP agents are now operating<br />
the rvSS in Nogales, ariz.<br />
Puretech Systems, a member of the<br />
general Dynamics OneSource team<br />
(gDOS), which was awarded the<br />
rvSS Upgrade contract, provides<br />
the software for full motion video,<br />
target detection, sensor control and<br />
the geospatial user interface.<br />
located on elevated fixed towers<br />
and building structures, the rvSS<br />
Upgrade wide-area electro-optical<br />
and infrared multi-sensor camera<br />
system provides border Patrol<br />
agents with persistent ground- surveillance<br />
and real-time video analyt-<br />
ics to effectively<br />
detect, track,<br />
identify, classify<br />
and respond to<br />
missions along<br />
U.S. borders. to<br />
date, Puretech<br />
Systems has<br />
participated<br />
in the deployment<br />
of a new<br />
command-andcontrol<br />
system<br />
and upgraded<br />
rvSS camera<br />
suites on new<br />
and existing tower sites supporting<br />
the Nogales border Patrol Station.<br />
During the test, the system assisted<br />
field agents in real- world missions.<br />
“The remote video Surveillance<br />
System is a critical element of our<br />
overall plan to secure the border,<br />
increase our mission effectiveness,<br />
and protect our agents,” said mark<br />
borkowski, assistant commissioner<br />
and chief acquisition executive<br />
from cbP’s Office of technology<br />
innovation and acquisition. “The<br />
gDOS team has done a great job<br />
honoring its commitments and we<br />
32<br />
The RVSS border protection upgrade, featuring video analytics and<br />
geospatial command and control developed by PureTech Systems,<br />
achieves system acceptance by Customs and Border Protection.<br />
are excited to have achieved an initial<br />
operating capability in our first<br />
area of responsibility. We look forward<br />
to continuing this strong relationship,<br />
and to completing the rest<br />
of our arizona deployments over<br />
the next year.”<br />
“The rvSS Upgrade program deployment<br />
is an important milestone<br />
for Puretech Systems, for our Pureactiv<br />
software suite, and for the entire<br />
general Dynamics rvSS team,”<br />
explained larry bowe, president of<br />
Puretech Systems. “Our solution is<br />
targeted at ground-based defense
and homeland security applications<br />
which require long range, accurate<br />
performance in various terrain and<br />
weather conditions. The system acceptance<br />
of PureTech’s solution<br />
for use at the U.S. border confirms<br />
that we are correctly addressing the<br />
needs of this market.”<br />
The RVSS Upgrade program has<br />
a potential 10-year performance<br />
period, during which the General<br />
Dynamics OneSource team, which<br />
includes PureTech Systems, will<br />
manage the operation and maintenance<br />
at all sites.<br />
PureTech Systems Inc. is a manufacturer<br />
of wide-area perimeter surveillance<br />
software solutions including<br />
internally developed outdoor video<br />
analytics, multi-sensor integration<br />
and a map-based (real object size)<br />
command and control. It is offered to<br />
fortune 1000 firms, petro-chemical,<br />
water and electric utilities, seaports,<br />
airports and federal, state and local<br />
governments. With headquarters in<br />
Phoenix Arizona, PureTech Systems<br />
serves national and international<br />
markets. To find out more about<br />
PureTech Systems Inc. visit our website<br />
at www.puretechsystems.com or<br />
contact Eric Olson at 602-424-9842<br />
or Eric.Olson@PureTechSystems.com.<br />
ThreatConnect & DGI uncover<br />
extensive South Chinese espionage<br />
Continued from page 9<br />
cal analysis, as well as data visualization<br />
to clearly connect the points<br />
between the adversary, their capabilities,<br />
the infrastructure they used<br />
and the victims being targeted.<br />
To create this report, ThreatConnect<br />
used a unique methodology<br />
built into their Threat Intelligence<br />
Platform called The Diamond Model<br />
of Intrusion Analysis. Using that<br />
repeatable process, any ThreatConnect<br />
user can derive a multidimensional<br />
picture of the underlying relationships<br />
between threat actors,<br />
their tools, techniques and processes.<br />
The full Project CAMERASHY<br />
report is available at http://www.<br />
threatconnect.com/camerashy.<br />
About ThreatConnect, Inc.<br />
ThreatConnect, Inc. provides industry-leading<br />
advanced threat<br />
intelligence software and services<br />
including ThreatConnect®, the<br />
most comprehensive Threat Intelligence<br />
Platform (TIP) on the market.<br />
ThreatConnect delivers a single<br />
platform in the cloud and on-premises<br />
to effectively aggregate, analyze,<br />
and act to counter sophisticated<br />
cyber-attacks. Leveraging advanced<br />
analytics capabilities, ThreatConnect<br />
offers a superior understanding<br />
of relevant cyber threats to business<br />
operations. To register for a free<br />
ThreatConnect account, or to learn<br />
more about our products and services,<br />
visit: www.threatconnect.com.<br />
33
Intelligent Video Surveillance<br />
Milestone goes wide with new device pack<br />
COPENHAGEN – <strong>October</strong> 29,<br />
<strong>2015</strong>. Milestone Systems, the open<br />
platform company in networked<br />
video management software (VMS),<br />
has released Device Pack 8.2 for<br />
partners and customers using Milestone<br />
XProtect monitoring solutions.<br />
A highlight of this release is support<br />
for perspective correction of<br />
video from 180, 270 or 360 degree<br />
panoramic cameras from Pelco by<br />
Schneider Electric. The support is<br />
achieved by a plugin to the Milestone<br />
XProtect Smart Client. Global<br />
unit shipments of 180/360 degree<br />
panoramic network camera is forecast<br />
to increase by more than 60<br />
percent year-on-year according to<br />
research analysts IHS. Panoramic<br />
cameras are predicted to gain market<br />
share in verticals such as retail,<br />
airports, and casinos, where<br />
monitoring wide indoor areas is a<br />
key requirement of the video security<br />
solution. In these scenarios, the<br />
cameras can reduce capital expenditure<br />
as fewer cameras are required<br />
to cover the same area compared to<br />
fixed or PTZ cameras.<br />
The challenge using fisheye panoramic<br />
cameras is that the picture<br />
from the camera needs perspective<br />
correction, which can be adjusted in<br />
the camera or in the software. This<br />
process called dewarping has several<br />
benefits when done in the software<br />
as it allows retrospective viewing.<br />
This gives the user the ability<br />
to go back in time to view the total<br />
scene in its original form and then<br />
pan, tilt, and/or zoom with corrected<br />
perspective within the 360-degree<br />
image.<br />
In addition to the support for Pelco<br />
panoramic cameras, nearly 200<br />
devices have been added to Milestone<br />
Device Pack 8.2. This list of<br />
new model support includes cameras<br />
from Axis Communications,<br />
Bosch and Samsung Techwin. The<br />
number of ONVIF-supported devices<br />
has increased by 64 now totaling<br />
1271 devices.<br />
ONVIF Testing Ensures Quality<br />
The XProtect Device Packs include<br />
tested drivers that are optimized<br />
to enable the capabilities of a camera<br />
or other hardware device to be<br />
managed by XProtect software.<br />
Testing the drivers ensures the highest<br />
functionality for a video surveillance<br />
solution, which is important<br />
for total system operability, efficiency<br />
and stability. Milestone works<br />
closely with the device manufacturers<br />
in the Camera Partner Program<br />
34<br />
(CaPP) to achieve the optimal interaction<br />
between their devices and<br />
the XProtect VMS.<br />
Milestone has always promoted<br />
driver standards like ONVIF and<br />
remains dedicated to supporting<br />
the broadest range of cameras and<br />
devices on the market. In the case<br />
of ONVIF supported devices, it is<br />
often assumed that a device that<br />
has passed the ONVIF test tool will<br />
work fully in a given infrastructure.<br />
This is not always the case as there<br />
are marked idiosyncrasies that need<br />
to be taken into account to insure<br />
proper interoperability and to leverage<br />
full feature use of a device with<br />
a VMS. Before ONVIF supported<br />
devices are listed on the Milestone<br />
supported hardware list on milestonesys.com,<br />
they have been tested<br />
to ensure that the functionality with<br />
XProtect is compliant with the ON-<br />
VIF specifications.<br />
In the Milestone CaPP, this ON-<br />
VIF functionality test can be done<br />
by Milestone or the vendors can do<br />
the testing in their facility after they<br />
have completed a 4-day Milestone<br />
training class. The ability to do the<br />
complete Milestone certification<br />
test can save time and costs for camera<br />
manufacturers in their go-tomarket<br />
strategy.
Coming Attractions:<br />
“We are constantly working with<br />
our camera partners to provide the<br />
highest quality solutions for the<br />
benefit of our partners and mutual<br />
customers,” says Henrik Sydbo<br />
Hansen, Head of the camera Partner<br />
Program at milestone Systems.<br />
“This ensures the highest possible<br />
quality for a video surveillance solution.”<br />
The milestone XProtect Device<br />
Pack 8.2 is available now for download<br />
from:<br />
www.milestonesys.com/support/<br />
download-software<br />
About Milestone Systems<br />
milestone Systems is a global industry<br />
leader in open platform iP<br />
video management software, founded<br />
in 1998 and now operating as a<br />
stand-alone company in the canon<br />
group. milestone technology is<br />
easy to manage, reliable and proven<br />
in thousands of customer installations,<br />
providing flexible choices in<br />
network hardware and integrations<br />
with other systems. Sold through<br />
partners in more than 100 countries,<br />
milestone solutions help organizations<br />
to manage risks, protect<br />
people and assets, optimize processes<br />
and reduce costs.<br />
Use of trademarks<br />
milestone Systems and the milestone<br />
logo are trademarks or registered<br />
trademarks of milestone<br />
Systems in the U.S. and other countries.<br />
a listing of the milestone<br />
trademarks can be found at news.<br />
milestonesys.com/trademark-information.<br />
all other trademarks and<br />
registrations are property of their<br />
respective owners.<br />
35<br />
<strong>November</strong> Print <strong>Edition</strong><br />
Technology Focus:<br />
Intrusion Detection/<br />
Perimeter Protection<br />
Market Focus:<br />
Airport/Aviation Security<br />
December <strong>Digital</strong> <strong>Edition</strong><br />
Technology Focus:<br />
Access Control/ID &<br />
Insider Threats<br />
Special Year-End<br />
Focus:<br />
DIGITAL YEARBOOK of<br />
<strong>2015</strong> Airport/Seaport/<br />
Rail/Border Security<br />
Awards Winners<br />
And<br />
<strong>2015</strong> Homeland<br />
Security IT, Physical<br />
Security, Government<br />
Awards Winners
Intelligent Video Surveillance<br />
Using video intelligence to protect<br />
critical public infrastructure<br />
By Kimbry McClure<br />
Law enforcement and other entities<br />
charged with protecting national security<br />
are spending more time than<br />
ever planning and implementing<br />
security measures that ensure national<br />
security and improve public<br />
safety. This is for good reason: from<br />
the energy grid to sporting events to<br />
airports, security personnel know<br />
these venues are enticing targets<br />
for terrorist attacks due to the large<br />
amount of people and resources<br />
clustered together in one place.<br />
In a world of heightened extremism,<br />
lone wolf attacks, and general<br />
global instability, it is not beyond<br />
imagination to foresee a scenario<br />
where a small team of terrorists<br />
seizes a U.S. airport. With the prospect<br />
of hostage taking and hijackings<br />
looming large, the response<br />
time for emergency personnel and<br />
law enforcement becomes critical.<br />
First responders must locate the terrorists<br />
and their hostages quickly<br />
to coordinate an effective response.<br />
This requires enhanced detection<br />
capabilities that can seamlessly<br />
distribute information to decision<br />
makers and emergency personnel<br />
to identify and respond to threats in<br />
real time.<br />
To stay a step ahead of attackers,<br />
security and emergency personnel<br />
need a common operational picture<br />
to communicate with civil and federal<br />
agency authorities. This picture<br />
is not only essential in coordinating<br />
a rescue, but also in securing additional<br />
areas of the airport facility<br />
that the terrorists have yet to seize<br />
as well as collect evidence for both<br />
investigative and legal purposes.<br />
With many entities tasked with<br />
restoring airport security, organizations<br />
need the right technology<br />
to assist them. An important tool<br />
emerging in security today is a video<br />
intelligence system that assists<br />
emergency responders and officials<br />
in reaching their security objectives.<br />
Not Your Old-School<br />
CC-TV Cameras<br />
Many people imagine video surveillance<br />
cameras to be a single camera<br />
mounted on a wall pointing in a<br />
particular direction and transmitting<br />
video to a single television. In<br />
this scenario, multiple cameras in<br />
different locations within the same<br />
building work in isolation and only<br />
36<br />
detect motion and images.<br />
Most people do not realize that<br />
video intelligence has evolved tremendously<br />
in recent years. Today’s<br />
video intelligence system consists<br />
of a wide range of disparate sensor<br />
data combined into a single portal.<br />
The integration of sensor data into<br />
one place is a critical development<br />
for law enforcement working in
time sensitive situations.<br />
Back in our besieged airport, authorities<br />
do not have time to monitor<br />
separate video camera, alarm<br />
systems, GPS, and other audio, visual,<br />
and social media monitoring<br />
systems separately. Officials need<br />
data from these sensors to be organized<br />
in such a way that patterns<br />
can be quickly detected to ensure<br />
rapid decision-making.<br />
As law enforcement officials analyze<br />
the data received from multiple<br />
sensors, a video intelligence system<br />
triages the data received. During<br />
the airport terrorist attack, law enforcement<br />
is able to discern that the<br />
screaming coming from an airport<br />
personnel-only hallway is more important<br />
to respond to than the traveling<br />
high school band playing their<br />
instruments in the airport concourse.<br />
First responders have the<br />
ability to triage behaviors because<br />
the video intelligence system has<br />
automated the monitoring process<br />
on a scale much larger than manpower<br />
can provide.<br />
Automating data collection, organization<br />
and storage gives law enforcement<br />
attempting to prevent or<br />
respond to a terrorist attack a more<br />
speedy, meticulous and effective<br />
overall security strategy. Authorities<br />
no longer have to allocate manpower<br />
to spending time searching<br />
and investigating each person who<br />
is in a facility. Since different people<br />
present various behaviors, some that<br />
indicate a higher security risk than<br />
others, video intelligence systems<br />
flag these behaviors for law enforcement<br />
and give them the knowledge<br />
needed to make critical decisions.<br />
Overcoming the Unknown<br />
Adding automation to data collection<br />
and analysis provides other<br />
benefits. Criminals and terrorists<br />
are constantly changing their tactics.<br />
As a result, law enforcement<br />
does not always know the behavior<br />
profile to match the changing<br />
tactics. The integration of a video<br />
intelligence system provides law enforcement<br />
flexibility to quickly and<br />
easily input into the system new behaviors<br />
for the sensors to monitor.<br />
Without unified data management,<br />
authorities would need to take more<br />
time and manpower to update the<br />
sensors on what new behaviors to<br />
track.<br />
Authorities may also face uncertainty<br />
over which agencies, groups<br />
and decision makers need access to<br />
which data points. Today’s homeland<br />
security and emergency response<br />
strategies involve multiple<br />
agencies, organizations and decision<br />
makers. These groups require<br />
that data be shared in real-time to<br />
establish a common operating picture.<br />
The video intelligence system<br />
37<br />
overcomes data sharing challenges<br />
by creating a single portal to store<br />
and view information. As a result,<br />
information can be shared with ease<br />
between various coordinating entities.<br />
How to Implement a Modern<br />
Video Intelligence System<br />
Many in government are concerned<br />
about how much value they will receive<br />
when implementing new technology<br />
systems. The good news is<br />
a modern video intelligence system<br />
is not only effective, but also simple<br />
to implement. The system’s design<br />
focuses on an interface that is integrated<br />
into an organization’s current<br />
IT systems, including legacy<br />
IT. Therefore, the video intelligence<br />
system is built based on customization<br />
and flexibility. Additionally, the<br />
video intelligence system includes<br />
sensors, compute power and onboard<br />
storage that can be installed<br />
and implemented rapidly.<br />
Deploying a video intelligence<br />
platform gives law enforcement a<br />
technological asset that keeps pace<br />
with terrorists and criminals today<br />
and in the future. By placing these<br />
tools under a single management<br />
layer, law enforcement can devote<br />
more resources to what truly matters:<br />
ensuring public safety.
Intelligent Video Surveillance<br />
Louroe CEO discusses emerging surveillance<br />
technologies: Audio Analytics<br />
by richard brent, ceO<br />
louroe electronics<br />
crime never sleeps. law enforcement<br />
officers know this<br />
all too well as they are constantly<br />
reacting to theft, vandalism<br />
and assault incidents. Over<br />
the years, surveillance technology<br />
has grown to play an increasingly<br />
important role in delivering critical<br />
details to investigators and first responders.<br />
many security personnel rely<br />
on cctv and video analytics<br />
to learn important information<br />
about a suspect and crime<br />
scene. cameras can even detect<br />
a range of bad behaviors.<br />
However, video analytics alone<br />
does not yield a high success<br />
rate of incident detection. cameras<br />
are mainly used to review interactions<br />
after the event has occurred.<br />
This is where audio analytics must<br />
come into the picture. video surveillance<br />
is primarily reactive, but<br />
audio can be used to proactively deter<br />
altercations. but what exactly is<br />
audio analytics?<br />
audio analytics is the ability to<br />
analyze and identify a<br />
sound. Similar to how<br />
the human ear processes<br />
audio, the analytic software<br />
analyzes sounds<br />
through advanced algorithms<br />
and classifies it<br />
into a predetermined category such<br />
as aggression or breaking glass.<br />
The other advantage that audio<br />
analytics provide is confidentiality.<br />
language content is not analyzed<br />
during sound detection. The software<br />
does not listen to words, but<br />
distortion and physiological changes<br />
in the voice. in other words, the<br />
technology is language agnostic and<br />
upholds privacy.<br />
recently, there have been great<br />
innovations in the audio analytics<br />
market. in <strong>2015</strong>, louroe electronics,<br />
industry leader in audio monitoring<br />
in the security industry, and Sound<br />
38<br />
intelligence, a premier audio classification<br />
software developer in the<br />
Netherlands, partnered to launch<br />
a suite of audio analytic solutions,<br />
most notably the aggression Detector<br />
and gunshot Detector. The<br />
analytic products integrate louroe’s<br />
microphones, select iP cameras and<br />
leading video management software<br />
(vmS).<br />
The aggression Detector is a valuable<br />
deterrence tool because it distinguishes<br />
the sounds commonly<br />
associated with verbal aggression,<br />
such as screaming,<br />
shouting and yelling.<br />
Sound intelligence’s detection<br />
software automatically<br />
filters out background noises–<br />
such as traffic, weather,<br />
slamming doors and ventilation<br />
systems– while objectively<br />
detecting (rising) human aggression,<br />
anger or fear. The system then<br />
warns staff immediately (by a visual<br />
alert or by triggering an alarm) so<br />
that physical aggression can be prevented.<br />
analytics make the problem<br />
of aggression measurable. it also<br />
ensures that no incident goes unnoticed,<br />
and by the same token, that all
incidents are analyzed to avoid false<br />
alarms.<br />
Reports state that 90 percent of<br />
physical aggression is preceded by<br />
verbal aggression so this software<br />
truly is a game changer. By using the<br />
technology, more incidents are deterred<br />
as well as their costly consequences.<br />
Installing audio analytics<br />
software is far less expensive than<br />
assault investigation or lawsuit fees,<br />
creating a high return on investment.<br />
The Gunshot Detector recognizes<br />
gun discharge up to 3,000 feet away<br />
in quiet environments, and accurately<br />
analyzes gunshots from a<br />
variety of weapons including handguns,<br />
shotguns, rifles and automatic<br />
rifles. The key benefit that this solution<br />
offers end users is shortened<br />
response time as the detector sends<br />
an immediate notification to police<br />
and first responders upon identifying<br />
a gunshot.<br />
Over the next several years, the<br />
security industry will likely see an<br />
increase of sound detectors in cities,<br />
education centers, commercial<br />
buildings and correctional facilities.<br />
It’s only a matter of time before<br />
audio analytics becomes as commonplace<br />
as video analytics as law<br />
enforcement continues to partner<br />
with companies and their security<br />
departments to decrease crime.<br />
39
Coming Attractions – 2016<br />
January Print<br />
Technology Focus:<br />
Access Control/Govt<br />
& Biometric ID<br />
Market Focus:<br />
Airport/Aviation<br />
Aviation Security<br />
Plus<br />
Guest Cyber Expert<br />
February <strong>Digital</strong><br />
Technology Focus:<br />
Perimeter Protection<br />
Intrusion Detection<br />
Market Focus:<br />
Oil/Gas/Utility<br />
Monitoring<br />
Plus<br />
Education Profile<br />
April <strong>Digital</strong><br />
Technology Focus:<br />
Video Surveillance<br />
Market Focus:<br />
Maritime/Coastal<br />
Port Security<br />
Plus<br />
Guest Cyber Expert<br />
May Print<br />
Technology Focus:<br />
Satellite Communications<br />
Market Focus:<br />
Law Enforcement/<br />
Public Safety<br />
Plus Education Profile<br />
June <strong>Digital</strong><br />
Technology Focus:<br />
Disaster Preparation<br />
And Response<br />
Market Focus:<br />
City/State/County/<br />
Municipal Security<br />
Plus<br />
Guest Cyber Expert<br />
July Print <strong>Edition</strong><br />
Technology Focus:<br />
Perimeter Protection/<br />
Intrusion Detection<br />
Market Focus:<br />
Airport/Aviation<br />
Security<br />
Plus<br />
Facility Security Expert<br />
March Print<br />
Technology Focus:<br />
CBRNE/Detection<br />
Market Focus:<br />
Border Security/<br />
Immigration<br />
Plus<br />
Video Surveillance<br />
Guest Expert<br />
For GSN Media Kit or Advertising Rates,<br />
contact Publisher Mike Madsen<br />
at 732-233-8119<br />
or by email at<br />
mmadsen@gsnmagazine.com<br />
40
The News Leader in Physical, IT and Homeland Security<br />
CEO/Editorial Director:<br />
Adrian Courtenay<br />
(O) 212-344-0759, X3<br />
(C) 917-696-5782<br />
acourtenay@gsnmagazine.com<br />
Publisher:<br />
Michael Madsen<br />
(O) 212-344-0759, X1<br />
(C) 732-233-8119<br />
mmadsen@gsnmagazine.com<br />
Senior Writer:<br />
Steve Bittenbender<br />
(C) 502-552-1450<br />
sbittenbender@gsnmagazine.com<br />
Senior Writer:<br />
Karen Ferrick-Roman<br />
(C) 412-671-1456<br />
karenferrickroman@gmail.com<br />
Columnist:<br />
John Convy<br />
Convy on Netcentric Security<br />
john@convyassociates.com<br />
Columnist:<br />
Shaun Campbell<br />
shauncampbell@safenetat.com<br />
Guest Expert Contributor:<br />
Denise Rucker Krepp<br />
(C) 202-546-2533<br />
kdrkrepp@hotmail.com<br />
Art Director:<br />
Gerry O’Hara<br />
OHDesign3<br />
(C) 203-249-0626<br />
gerry@ohd3.com<br />
Production Director:<br />
Tammy Waitt<br />
(O) 732-233-0245<br />
twaitt@gsnmagazine.com<br />
Mailing Address:<br />
Government Security News<br />
P.O. Box 7608<br />
Greenwich, CT 06836<br />
Government Security News (ISSN 1548-940X and UPS 022-845) is published in six print editions (Jan, Mar, May, Jul, Sep, Nov) and<br />
six digital editions (Feb, Apr, Jun, Aug, Oct, Dec) per year by World Business Media, LLC, P.O. Box 7608, Greenwich, CT 06836.<br />
Telephone (212) 344-0759. Periodicals postage paid at New York, NY and additional mailing offices. POSTMASTER: Send address<br />
changes to GSN: Government Security News, Subscription Department, P.O. Box 316, Congers, NY 10920-0316. For Government<br />
decision makers and business executives involved with security products, systems and series. Qualified U.S. subscribers received<br />
GSN: Government Security News at no charge. Non-qualified subscribers in the U.S. are charged $75.00 per year. Canadian and<br />
foreign subscribers are charged $140 International Airmail. Copyright <strong>2015</strong> by GSN: Government Security News. All rights reserved.<br />
Printed in the U.S.A. GSN: Government Security News assumes resonsibility for validity of claims in items reported.<br />
41
Secure access<br />
to cloud, data<br />
and door<br />
Go beyond simple passwords. Protect your<br />
organisation with cost-effective, risk appropriate<br />
Identity Assurance Solutions from HID Global.<br />
With the ever increasing risk from advanced IT security threats, organisations are looking to take authentication<br />
beyond passwords, while lowering cost at the same time. HID Global’s authentication solution provides you<br />
with the convenience, flexibility and comprehensive control you need to deliver secure access, without<br />
compromising on security. HID Global can empower your employee’s, partners and customers with anytime,<br />
anywhere access to enterprise cloud applications, data and the door.<br />
Experience authentication beyond passwords. hidglobal.com<br />
© <strong>2015</strong> HID Global Corporation/ASSA ABLOY AB. All rights reserved. HID, HID Global, the HID Blue Brick logo, and the Chain Design are trademarks or registered trademarks of HID Global or its<br />
licensor(s)/supplier(s) in the US and other countries and may not be used without permission.