GSN Dec 2015/Jan 2016 Digital Edition
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
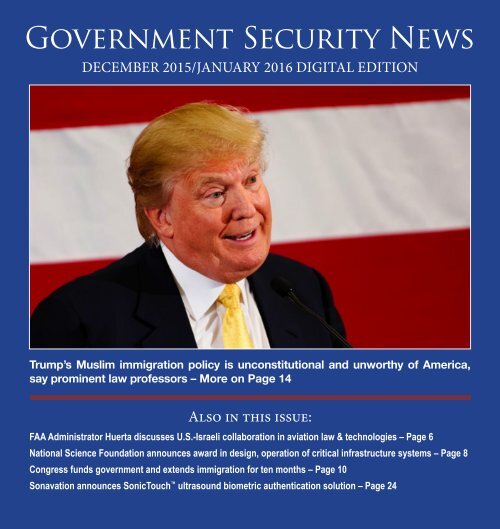
Government Security News<br />
DECEMBER <strong>2015</strong>/JANUARY <strong>2016</strong> DIGITAL EDITION<br />
Trump’s Muslim immigration policy is unconstitutional and unworthy of America,<br />
say prominent law professors – More on Page 14<br />
Also in this issue:<br />
FAA Administrator Huerta discusses U.S.-Israeli collaboration in aviation law & technologies – Page 6<br />
National Science Foundation announces award in design, operation of critical infrastructure systems – Page 8<br />
Congress funds government and extends immigration for ten months – Page 10<br />
Sonavation announces SonicTouch ultrasound biometric authentication solution – Page 24
<strong>GSN</strong> <strong>Dec</strong>ember <strong>2015</strong>/<strong>Jan</strong>uary <strong>2016</strong> <strong>Digital</strong> <strong>Edition</strong><br />
Table of Contents<br />
<strong>GSN</strong> TECHNOLOGY SPOTLIGHT<br />
Battelle plans demonstration of active shooter alarm system.<br />
Former Central Intelligence Agency analyst Ed Jopek discusses<br />
Battelle’s recently tested SiteGuard Active Shooter Response system,<br />
which will be demonstrated to police at a school near Columbus, Ohio<br />
later this month. “In ten or eleven years building systems like SiteGuard<br />
ASR will be as common as smoke detection and fire systems are<br />
today,” Jopek predicts.<br />
Read more on Page 4.<br />
Insider Threats: <strong>GSN</strong> Columnist Shawn Campbell explains why<br />
passwords are not enough.<br />
<strong>GSN</strong>’s new Columnist Shawn Campbell, nationally recognized cryptology<br />
expert and Safenet Assured Technologies VP, discusses insider<br />
threats and explains why passwords aren’t enough. “Unauthorized<br />
access to local networks by employees Is now part of almost every<br />
discussion on cybersecurity,” he points out. “A multifactor approach is<br />
the only way to minimize the danger of insider threats.”<br />
Read more on Page 22.<br />
2
NEWS AND FEATURES<br />
Battelle plans demonstration of active shooter<br />
alarm system Page 4<br />
FAA Administrator speaks at Israeli Aerospace<br />
Dinner Page 6<br />
National Science Foundation announces<br />
interdisciplinary awards program on critical infrastructure<br />
studies Page 8<br />
Congress funds government and extends<br />
immigration for ten months Page 10<br />
CenturyLink VP commends House of<br />
Representatives’ passage of Internet Tax Freedom<br />
Page 12<br />
Investigation by Texas Observer finds systemic<br />
corruption at Customs & Border Protection Page 15<br />
Coalition’s legal brief urges Supreme Court to<br />
reverse Texas v. U.S. immigration decision Page 16<br />
Airport police support legislative efforts to tighten<br />
internal airport security Page 18<br />
Access Control, ID, Insider Threats<br />
____________________________________<br />
Campbell on Crypto – Insider Threats:<br />
Why passwords aren’t enough Page 22<br />
Sonavation announces SonicTouch ultrasound<br />
biometric authentication solution Page 24<br />
Smart Card strong authentication protects<br />
workstations, mobile devices and networks Page 25<br />
New Entrust cloud capabilities simplify SSL<br />
certificate management Page 26<br />
Viscount unveils Freedom Channel Partner<br />
Program with enhanced technical support Page 27<br />
United Arab Emirates goes eBorder<br />
with Morpho Page 28<br />
SecuGen to showcase new unity biometric<br />
development platform Page 29<br />
Coming Attractions/<strong>GSN</strong> Mast Head Page 38<br />
U.S. Congress of Mayors President applauds<br />
unprecedented agreement at COP21 Page 19<br />
FAA announces user-friendly aircraft registration<br />
for small unmanned aircraft Page 20<br />
FAA updates airspace obstructions standards<br />
to make airspace safe and navigable Page 21<br />
3
Battelle plans demonstration of active<br />
shooter alarm system<br />
By Steve Bittenbender<br />
The future of building safety has<br />
been installed at an Ohio high<br />
school.<br />
Battelle, the largest independent<br />
research and development organization<br />
in the world, recently tested its<br />
SiteGuard Active Shooter Response<br />
system at a school near Columbus,<br />
in central Ohio. Officials will showcase<br />
the system to police, security<br />
and other officials later this month.<br />
SiteGuard brings together gunshot<br />
detectors with existing security<br />
systems, with those sensors giving<br />
essential information about the location<br />
of gunfire to first responders<br />
and people inside the building. The<br />
system works similar to smoke detectors<br />
and other fire safety devices<br />
in that SiteGuard can expedite automated<br />
calls to 9-1-1 dispatchers and<br />
mass notification subscribers.<br />
“While we may not be able to prevent<br />
these tragic shootings, we can<br />
give law enforcement technology<br />
that helps them respond more safely<br />
and effectively,” said Ed Jopeck, a senior<br />
program manager for Battelle.<br />
“In 10 or 15 years building systems<br />
like SiteGuard ASR will be as common<br />
as smoke detection and fire<br />
safety systems are today. They can<br />
help authorities to locate, detect and<br />
respond to gunfire more effectively,<br />
which can help save lives.”<br />
Jopeck is a former analyst with<br />
the Central Intelligence<br />
Agency. After leaving<br />
the CIA, he worked as a<br />
consultant and for such<br />
companies as General<br />
Dynamics, SRA International<br />
and ShotSpotter<br />
before joining Battelle<br />
in 2012.<br />
Once gunfire has been<br />
detected, SiteGuard will<br />
pinpoint the location of<br />
each shooter and follow their movements<br />
throughout a facility. This<br />
information will be relayed to police<br />
and building officials, allowing<br />
them to know precisely the number<br />
of intruders as well as the types of<br />
weapons they’re using. When used<br />
in coordination with a building’s<br />
video surveillance system, SiteGuard<br />
will help officials advise occupants<br />
whether they can evacuate<br />
or whether they need to seek shelter<br />
immediately.<br />
Battelle’s already working on fu-<br />
Ed Jopeck<br />
ture enhancements. For example,<br />
SiteGuard is working on a two-way<br />
communications system that would<br />
enable law enforcement officials<br />
to communicate with occupants<br />
or even the shooters. This feature<br />
would allow first responders<br />
the ability to<br />
triage any injured occupants<br />
and give greater<br />
details to law enforcement<br />
site commanders<br />
for their site assessments.<br />
Other developments<br />
in the works include the<br />
ability to automatically<br />
lock doors once a shot<br />
has been detected, reducing the<br />
chances shooters can harm other<br />
occupants.<br />
Battelle joins a number of other<br />
providers of shooter detection sensors<br />
to showcase their products to<br />
government officials. In Reynoldsburg,<br />
a suburban community just<br />
east of Columbus, police officers see<br />
the technology as helping them reduce<br />
delays and chances for human<br />
error.<br />
“If you have a pretty good idea<br />
More on page 12<br />
4
Security<br />
Career Option<br />
#47:<br />
Critical<br />
Infrastructure<br />
Protection<br />
A degree in security can open up a wide, wide world<br />
of career possibilities for you.<br />
In today’s world, security is more important than ever. Which means there is<br />
an immense range of opportunities in the security profession. With a degree in<br />
Security Management from University of Phoenix, you can reach new heights<br />
in this growing field. We offer a Bachelor of Science in Security Management,<br />
an Associate of Arts in Security Management and certificate programs that are<br />
aligned to the Security Competency Model, written by University of Phoenix and<br />
recently validated and published by the U.S. Department of Labor.<br />
To learn more, visit phoenix.edu/security.<br />
For more information about each of these programs, including on-time completion rates, the median debt incurred by students who completed the program and other important information,<br />
please visit phoenix.edu/programs/gainful-employment.<br />
While widely available, not all programs are available in all locations or in both online and on-campus formats.Please check with a University Enrollment Representative. The University’s Central<br />
Administration is located at 1625 W. Fountainhead Pkwy., Tempe, AZ 85282. Online Campus: 3157 E. Elwood St., Phoenix, AZ 85034. © <strong>2015</strong> University of Phoenix, Inc. All rights reserved. | CJS-4156
“Working Together to Foster Safety” Speech<br />
by FAA Administrator Michael Huerta<br />
Editor’s Note: This Speech was delivered<br />
by FAA Administrator Michael<br />
Huerta at the Israel Aerospace Dinner<br />
in Jaffa, Israel on <strong>Dec</strong>ember 16, <strong>2015</strong><br />
I am honored to be here<br />
with you tonight, and I<br />
appreciate the hospitality<br />
and spirit of partnership<br />
you have extended<br />
to me during my visit to<br />
your beautiful country.<br />
I am especially in awe of<br />
this wonderful—and appropriate—venue<br />
for tonight’s<br />
gathering.<br />
I want to thank Civil Aviation<br />
Authority of Israel (CAAI) Director<br />
General Joel Feldschuh and his<br />
team for hosting us here tonight<br />
and for being such great partners,<br />
which I plan to speak more about.<br />
The Peres Center for Peace is truly<br />
inspiring. And I could look out at<br />
this view of the Mediterranean Sea<br />
for hours.<br />
For those of us in this room, aviation<br />
is not just a profession; it is a<br />
passion. We are fortunate to live in<br />
a time when we can do what mankind<br />
has imagined since the days<br />
when this part of the world was<br />
FAA Administrator<br />
Michael Huerta<br />
young. We don’t have to wonder;<br />
we know what it is like to mount up<br />
on wings as eagles.<br />
For us, the world is a much wider<br />
place. Yet, at the same time, it has<br />
never been smaller.<br />
We think nothing of<br />
boarding a modern airliner<br />
and safely disembarking<br />
a few hours later,<br />
an ocean or more away.<br />
Aviation has become the<br />
international language of<br />
commerce, and runways<br />
have enabled inland cities<br />
to become vibrant ports.<br />
It has helped foster an intellectual<br />
and economic prosperity that’s unparalleled<br />
in human history.<br />
As stewards of this industry, we<br />
share an enormous responsibility<br />
to protect this mode of travel and<br />
to nurture its future. Every day, we<br />
ask ourselves, how can we make flying<br />
safer? How can we be more efficient?<br />
What else lies over the horizon?<br />
Since the beginning of manned<br />
flight, aviation has been the catalyst<br />
for international relationships.<br />
I can’t think of anywhere this has<br />
been truer than the deep, unbreakable<br />
bonds that have grown between<br />
Israel and the United States.<br />
In <strong>Jan</strong>uary of this year, Nancy<br />
Spielberg and Roberta Grossman<br />
released a documentary, “Above and<br />
Beyond.” It tells the story of a group<br />
of American fighter pilots who volunteered<br />
to fly in combat for the<br />
State of Israel during the War of Independence<br />
in 1948. It’s a historical<br />
account that isn’t so well known in<br />
my country, even though many of<br />
these men were heroes here in Israel.<br />
They were acting on their own<br />
at the time, but these intrepid Jewish<br />
aviators heralded the beginning<br />
of what today is one of the United<br />
States’ strongest common bonds<br />
with Israel.<br />
We are tied together culturally.<br />
We are tied together economically.<br />
We are tied together by aviation.<br />
More on page 32<br />
6
Is proud to introduce two<br />
exciting new products!<br />
SENTRY<br />
Mobile Workstation<br />
Our heavy duty, steel workstation is excellent<br />
for use as a portable Sentry Mobile Workstation<br />
where a checkpoint is needed at a moment's<br />
notice. Can also be used in:<br />
Classrooms • Conference rooms • Training rooms<br />
Manufacturing /warehouse environments<br />
36-41"<br />
Adjustable<br />
Height<br />
PROMARINE<br />
Megaphone<br />
WATERPROOF PROTECTION - MADE IN THE USA<br />
Rugged And Waterproof, This Military-tough<br />
Megaphone Is An Excellent Option For:<br />
Industrial use • Fire and rescue • Law enforcement • Public safety<br />
Military • Boating & water sports • Outdoor athletics & recreation<br />
www.ampli.com | info@ampli.com | (800) 267-5486<br />
5
National Science Foundation announces<br />
“CRISP”awards program to enhance interdisciplinary<br />
understanding, design and operation of interdependent<br />
critical infrastructure systems<br />
The National Science Foundation<br />
has released the details of a “Critical<br />
Resilient Interdependent Infrastructure<br />
Systems and Processes<br />
(CRISP)” awards program, which<br />
has been designed to foster collaboration<br />
among interdependent stakeholders<br />
and to enhance the understanding,<br />
design and operation of<br />
interdependent critical infrastructure<br />
systems and processes that provide<br />
essential goods and services<br />
despite disruptions and failures<br />
from any cause, natural, technological<br />
or malicious, and to provide<br />
opportunities to innovate in ICIs to<br />
enrich society with new goods and<br />
services. There are currently 18 critical<br />
infrastructures defined by the<br />
U.S.<br />
According to the NSA announcement,<br />
proposals may only be submitted<br />
by two-year and four-year<br />
colleges, including community<br />
colleges that are accredited in, and<br />
have a campus in the U.S, acting on<br />
behalf of their faculty members. Solicitation<br />
in the program are being<br />
sought in the following disciplines,<br />
with a deadline of March 09, <strong>2016</strong>:<br />
Directorate for Engineering<br />
Division of Civil, Mechanical and<br />
Manufacturing Innovation<br />
Division of Electrical, Communications<br />
and Cyber Systems<br />
Division of Chemical, Bioengineering,<br />
Environmental, and Transport<br />
Systems<br />
Emerging Frontiers and Multidisciplinary<br />
Activities<br />
Directorate for Social, Behavioral<br />
& Economic Sciences<br />
Division of Behavioral and Cognitive<br />
Sciences<br />
Division of Social and Economic<br />
Sciences<br />
Directorate for Computer & Information<br />
Science & Engineering<br />
Division of Computer and Network<br />
Systems<br />
Division of Advanced Cyberinfrastructure<br />
Who May Serve as PI:<br />
Because this program is meant to<br />
support interdisciplinary research,<br />
8<br />
a minimum of three investigators is<br />
required per project, including the<br />
Principal Investigator (PI) and two<br />
or more co-Investigators from the<br />
lead or participating institutions.<br />
Persons named as PI or co-PI must<br />
be eligible to serve as such on NSF<br />
proposals submitted through their<br />
respective institutions. In order<br />
to ensure an interdisciplinary approach<br />
to studying ICIs, proposals<br />
should include and clearly identify<br />
at least one PI or co-PI who is an<br />
engineer, at least one who is a computer,<br />
information or computational<br />
scientist, and at least one who is a<br />
social, economic or behavioral scientist.<br />
Additional co-PIs or senior<br />
personnel may be added to cover
other interdisciplinary needs of the<br />
project. The appropriateness of the<br />
research team’s disciplinary composition<br />
and expertise should be justified<br />
and will be a factor in the merit<br />
review of the proposal.<br />
There are currently 18 critical infrastructures<br />
defined by the U.S. Department<br />
of Homeland Security and<br />
some of these are highly aggregated<br />
classifications, for example energy,<br />
of different essential infrastructures,<br />
such as power generation and distribution,<br />
and natural gas production<br />
and pipeline distribution. The National<br />
Science Foundation describes<br />
the program as follows:<br />
Synopsis of Program:<br />
“Critical infrastructures are the<br />
mainstay of our nation’s economy,<br />
security and health. These infrastructures<br />
are interdependent. They<br />
are linked to individual preferences<br />
and community needs. For example,<br />
the electrical power system<br />
depends on the delivery of fuels to<br />
power generating stations through<br />
transportation services, the production<br />
of those fuels depends in turn<br />
on the use of electrical power, and<br />
those fuels are needed by the trans-<br />
More on page 35<br />
DATA CENTER<br />
SECURITY SOLUTIONS<br />
AMERISTARSECURITY.COM | 866-467-2773<br />
9
Congress funds government<br />
and extends immigration for<br />
ten months<br />
By Joshua Breisblatt<br />
This week, the House and Senate<br />
overwhelmingly passed a $1.15<br />
trillion omnibus spending bill that<br />
funds the federal government for the<br />
rest of the Fiscal Year (FY), through<br />
September 30, <strong>2016</strong>, as well as a package<br />
of tax breaks worth around $620<br />
billion. The spending bill, which was<br />
seen as the first significant test for<br />
the new Speaker of the House Paul<br />
Ryan (R-WI), not only funded the<br />
federal government but contained a<br />
variety of major provisions, some of<br />
which effect immigration policy.<br />
The Department of Homeland<br />
Security funding featured many of<br />
the same provisions from previous<br />
years including the following requirements:<br />
that Immigration and<br />
Customs Enforcement (ICE) maintain<br />
34,000 detention beds, that Border<br />
Patrol maintain 21,370 border<br />
agents, and that U.S. Citizenship<br />
and Immigration Services (USCIS)<br />
fund the Citizenship and Integration<br />
Grant Program with $10 million<br />
from its fee account.<br />
The omnibus also funded the nation’s<br />
immigration courts, giving the<br />
chronically-underfunded Executive<br />
Office of Immigration Review<br />
(EOIR) enough funding for 55 new<br />
immigration judges teams, which<br />
will allow EOIR to hire new judges<br />
and necessary support staff. There is<br />
some hope that these new judges will<br />
help to reduce the record backlogs in<br />
the immigration court system.<br />
One of the major policy provisions<br />
included in the omnibus is the<br />
Visa Waiver Improvement and Terrorist<br />
Travel Prevention Act of <strong>2015</strong><br />
which previously passed the House<br />
of Representatives by 407-19. The<br />
bill terminates Visa Waiver Program<br />
(VWP) travel privileges for all citizens<br />
of VWP countries who are also<br />
nationals of Iraq, Syria, Iran, or Sudan,<br />
singling out and discriminating<br />
based on nationality. It also excludes<br />
all individuals who have traveled<br />
since March 1, 2011 to certain countries–<br />
including Syria, Iraq, and other<br />
designated countries. Many organizations<br />
expressed serious concern<br />
over the language, saying it is overbroad<br />
and will have unintended consequences,<br />
with one example being<br />
making it potentially more difficult<br />
for journalists and humanitarian aid<br />
workers to travel.<br />
10<br />
Photo: William Beem<br />
The omnibus also contains controversial<br />
changes to the H-2B program.<br />
The H-2B program allows U.S.<br />
employers to recruit foreign workers<br />
to fill job vacancies for temporary<br />
and seasonal positions. There is an<br />
annual cap of 66,000 H-2B workers<br />
per year. The omnibus contains a<br />
provision, commonly called the “returning<br />
work” exemption, which allows<br />
an H-2B worker that has been<br />
counted against the 66,000 cap in one<br />
of the three previous years to return<br />
to work in the H-2B program in the<br />
current year without being counted<br />
against the cap. Some Republican<br />
and Democratic members strongly<br />
objected to the provision.<br />
The omnibus reauthorized three<br />
visa programs and the E-Verify Program<br />
for the rest of the fiscal year,<br />
without making any changes to the<br />
programs. These programs are:<br />
• The EB-5 program: The immigrant<br />
investor program, known as<br />
EB-5, was created in 1990 to stimulate<br />
job growth and capital investment.<br />
It is the only visa program for<br />
investors that leads to permanent<br />
residence, and it requires that applicants<br />
invest $1 million (or $500,000<br />
if the investment is in a rural or<br />
high-unemployment area) and create<br />
at least 10 jobs. There are 10,000<br />
visas allocated per fiscal year for the<br />
program.<br />
• Conrad 30 Program: This program,<br />
created in 1994, allows certain<br />
physicians who trained in the<br />
United States on J-1 visas to obtain<br />
a waiver of the two-year home residence<br />
requirement. In exchange for<br />
the waiver, the physician must work<br />
for at least three years treating medi-
cally underserved populations in the<br />
United States.<br />
• Special Immigrant Non-Minister<br />
Religious Worker Program: This<br />
program, created in 1990, allows<br />
non-ministers or other lay religious<br />
workers to come to the United States<br />
as lawful permanent residents.<br />
Lastly, in the tax break portion<br />
of the bill, expansions of the Child<br />
Care Tax Credit (CTC) and Earned<br />
Income Tax Credit (EITC) that were<br />
passed in 2009 were made permanent.<br />
According to National Council<br />
of La Raza (NCLR), who applauded<br />
Congress for making these provisions<br />
permanent, the EITC expansion<br />
amounts to as much as $6,143<br />
per family, while the CTC can add up<br />
to $1,000 per child. However NCLR<br />
and others noted that Congress also<br />
erected additional barriers for immigrants<br />
who wish to file taxes using an<br />
individual tax identification number<br />
(or “ITIN”), as well as barring newly<br />
legalized domestic violence survivors,<br />
DACA recipients, and others<br />
from accessing these vital tax credits,<br />
creating a two-tiered tax system<br />
based on immigration status.<br />
Like all massive pieces of legislation,<br />
there is something for everyone<br />
to love and hate. With Congress now<br />
adjourned for the year, hopefully<br />
<strong>2016</strong> brings a renewed effort towards<br />
regular order, transparency, and accountability<br />
in lawmaking.<br />
POWER UTILITY<br />
SECURITY SOLUTIONS<br />
AMERISTARSECURITY.COM | 866-467-2773<br />
11
CenturyLink VP commends<br />
House of Representatives<br />
for passage of Internet Tax<br />
Freedom Act<br />
Editor’s Note: John Jones, Senior VP<br />
for Public Policy and Government<br />
Relations of Century Link, a global<br />
communications, hosting, cloud company<br />
that offers network and data<br />
systems management, has released<br />
the following statement regarding the<br />
legislation recently passed by the U.S.<br />
House of Representatives permanently<br />
banning federal, state and local<br />
governments from taxing consumers<br />
and small businesses on their Internet<br />
access.<br />
“CenturyLink commends the leaders<br />
of the U.S. House of Representatives<br />
for passing legislation that<br />
permanently bans federal, state and<br />
local governments from taxing consumers<br />
and small businesses on their<br />
Internet access. Making the Internet<br />
tax moratorium permanent is sound<br />
economic policy that brings certainty<br />
to the market and encourages<br />
broadband adoption and network<br />
investment.”<br />
Legislation that permanently extends<br />
ITFA was introduced by U.S.<br />
Reps. Bob Goodlatte (R-Va.) and<br />
Anna Eshoo (D-Calif.) and U.S.<br />
Sens. John Thune (R-S.D.) and Ron<br />
Wyden (D-Ore.) earlier this year. A<br />
temporary extension of the Internet<br />
tax moratorium has been enacted<br />
many times since it was first signed<br />
into law in 1998.<br />
About CenturyLink<br />
CenturyLink (NYSE: CTL) is a global<br />
communications, hosting, cloud and<br />
IT services company enabling millions<br />
of customers to transform their<br />
businesses and their lives through<br />
innovative technology solutions.<br />
CenturyLink offers network and data<br />
systems management, big data analytics<br />
and IT consulting, and operates<br />
more than 55 data centers in North<br />
America, Europe and Asia. The company<br />
provides broadband, voice, video,<br />
data and managed services over a<br />
robust 250,000-route-mile U.S. fiber<br />
network and a 300,000-route-mile<br />
international transport network.<br />
Battelle plans demonstration of<br />
active shooter alarm system<br />
Continued from page 4<br />
where the active shooter is located,<br />
you can concentrate the resources<br />
and get them inside as fast as possible,”<br />
he said, adding the extra<br />
knowledge of the shooter’s location<br />
and actions also would make responding<br />
safer for the police. “Every<br />
little bit helps to provide the quickest<br />
and most efficient response.”<br />
With its headquarters in the Ohio<br />
capital, Battelle conducts critical<br />
research and development work in<br />
technology centers and laboratories<br />
worldwide. Since its creation nearly<br />
87 years ago, the company, which<br />
is a 501(c)3 charitable trust, has<br />
worked in national security, human<br />
health, energy and environmental<br />
industries.<br />
Visit CenturyLink for more information.<br />
12
Trump’s Muslim immigration policy is<br />
unconstitutional and unworthy of America,<br />
say prominent law professors<br />
By Wendy Feliz<br />
The latest outrageous proposal out<br />
of the Trump for President campaign<br />
came via a “Statement on<br />
Preventing Muslim Immigration”<br />
where the candidate calls “for a total<br />
and complete shutdown of Muslims<br />
entering the United States until<br />
our country’s representatives can<br />
figure out what is going on.”<br />
According to Vox, “His campaign<br />
has clarified that this would<br />
apply to ‘everybody,’ mentioning<br />
in particular Muslims entering the<br />
U.S. as immigrants or tourists… It<br />
also, as his campaign later clarified,<br />
means that Muslim-American<br />
citizens who are currently<br />
traveling abroad would be prevented<br />
from reentering the US.”<br />
This proposal was immediately<br />
met with criticism from fellow presidential<br />
candidates, political and<br />
religious leaders, and legal experts.<br />
Yet, how realistic is such a policy?<br />
Has the U.S. ever done something<br />
comparable and would this kind of<br />
immigration policy stand up to legal<br />
and public scrutiny?<br />
According to a Washington Post<br />
report, the last time the U.S. barred<br />
an entire group from entering the<br />
U.S. was the Chinese Exclusion Act<br />
of 1882, “which “effectively halted<br />
Chinese immigration for ten years.”<br />
The Act was “induced by blind racism<br />
and eagerness to deflect blame<br />
onto other groups,” noted one analysis<br />
of the Act.<br />
However, Trump’s proposal would<br />
go further than the Chinese Exclusion<br />
Act by banning an entire religion—a<br />
religion observed by the<br />
populations of multiple nations and<br />
individuals of various races and ethnicities.<br />
Such a ban would likely violate<br />
a range of international agreements<br />
to which the U.S. has entered.<br />
And similar to the Chinese Exclusion<br />
Act, which “severely damaged<br />
transnational relations,” there is little<br />
doubt such a policy would have<br />
14<br />
Photo: Michael Vadon<br />
far-reaching, damaging impacts on<br />
U.S. interests abroad.<br />
Experts also weighed in on whether<br />
the anti-Muslim proposal would<br />
hold up to legal scrutiny and international<br />
standards.<br />
An exasperated Jonathan Turley,<br />
a constitutional law expert, told the<br />
Washington Post:<br />
“Oh, for the love of God,” said<br />
the George Washington University<br />
professor of law.“ This would<br />
not only violate international law,<br />
but do so by embracing open discrimination<br />
against one religion.<br />
It would make the United States a<br />
virtual pariah among nations.’’<br />
And Stephen Yale-Loehr, an immigration<br />
law expert and professor<br />
of law at Cornell, told the New<br />
York Times that the Supreme Court<br />
would likely strike down this type of<br />
overly-restrictive immigration policy<br />
under the equal protection clause<br />
of the 14th Amendment:<br />
“Putting the policy into practice<br />
would require an unlikely act of<br />
Congress…It would certainly be<br />
challenged as unconstitutional…<br />
And I predict the Supreme Court<br />
would strike it down.”<br />
More on page 36
Investigation by Texas Observer finds systemic<br />
corruption, insufficient oversight at CBP<br />
By Walter Ewing<br />
In 2002, in the wake of 9/11, Congress<br />
and the White House embarked<br />
upon an unprecedented<br />
bureaucratic experiment: grafting<br />
together 22 federal agencies into a<br />
single entity that was supposed to<br />
protect the nation from terrorist attack<br />
or any other potential threat.<br />
The result was a multi-headed monstrosity<br />
known as<br />
the Department of<br />
Homeland Security<br />
(DHS). Nearly<br />
a decade and a half<br />
after its creation,<br />
DHS remains<br />
deeply fragmented—its<br />
various<br />
components rarely,<br />
if ever, functioning<br />
in unison.<br />
One symptom of<br />
this dysfunction is<br />
corruption. And a<br />
prime example of<br />
this corruption is<br />
U.S. Customs and<br />
Border Protection<br />
(CBP)—the agency<br />
tasked with securing<br />
the nation’s<br />
Photo: Courtesy of Maryland National Guard<br />
15<br />
borders.<br />
As an investigation by the Texas<br />
Observer makes clear, the corruption<br />
within CBP (which includes<br />
the U.S. Border Patrol) is systemic.<br />
Congress keeps adding to the ranks<br />
of Border Patrol agents under the<br />
border-security mantra of “more<br />
boots on the ground,” but “pays little<br />
attention to the men and women<br />
tasked with keeping border agents<br />
accountable. As a result, say the Observer:<br />
“…accounts of corruption have<br />
multiplied: In<br />
Arizona, a Border<br />
Patrol agent<br />
was caught on<br />
police video<br />
loading a bale<br />
of marijuana<br />
into his patrol<br />
vehicle; another<br />
agent in Texas<br />
was caught<br />
waving loads of<br />
drugs through<br />
the international<br />
port of entry<br />
for a cartel; and<br />
in California, a<br />
Border Patrol<br />
agent smuggled<br />
immigrants<br />
across the bor-<br />
More on page 36
Coalition’s Legal Brief urges Supreme Court<br />
to reverse Texas v. U.S. decision blocking<br />
President’s executive actions on immigration<br />
WASHINGTON, D.C. — A coalition<br />
of 224 immigration, civil rights,<br />
labor, and social service groups<br />
has filed an amicus (“friend of the<br />
court”) brief, urging the Supreme<br />
Court to review the case, Texas v.<br />
U.S., that has blocked some of President<br />
Obama’s executive actions on<br />
immigration. The filing comes less<br />
than a month after the U.S. Court<br />
of Appeals for the Fifth Circuit upheld<br />
a preliminary injunction put<br />
in place by a Texas federal district<br />
court that blocked implementation<br />
of protections for millions of immigrants<br />
across the country.<br />
The filing from the American Immigration<br />
Council, National Immigration<br />
Law Center, Service Employees<br />
International Union, American<br />
Federation of Labor and Congress<br />
of Industrial Organizations, Advancement<br />
Project, LatinoJustice<br />
PRLDEF, and the Leadership Conference<br />
on Civil and Human Rights,<br />
among others, comes only ten days<br />
after the formal request, known as a<br />
petition for writ of certiorari, from<br />
the Department of Justice to the<br />
Supreme Court to review the case.<br />
Amicus briefs in support of a cert<br />
petition are usually due 30 days after<br />
the petition is filed. The amici<br />
coalition acted swiftly given that the<br />
Department of Justice has requested<br />
a briefing schedule that would allow<br />
the Supreme Court ample time<br />
to hear the case during the current<br />
term and issue a decision by June<br />
<strong>2016</strong>.<br />
“The breadth and depth of support<br />
for the President’s executive<br />
actions is clear,”<br />
said Marielena<br />
Hincapié, Executive<br />
Director of<br />
the National Immigration<br />
Law<br />
Center. “It’s now<br />
up to the Supreme<br />
Court to take the<br />
case up this term<br />
16<br />
and put the legal questions to rest so<br />
that the over 5 million U.S. citizen<br />
children whose parents are eligible<br />
for DAPA, can finally have stability<br />
and be free from the fear that they<br />
will one day be separated from their<br />
parents.<br />
“With more than 200 organizations<br />
joining this amicus, including<br />
labor groups that represent millions<br />
of immigrant workers, there’s<br />
no question that the president’s immigration<br />
initiatives are necessary<br />
and backed by the majority of the<br />
American public,” said Rocio Saenz,<br />
executive vice president of SEIU<br />
International. “The Supreme Court<br />
has a responsibility to take this case,<br />
just as we have a duty to mobilize<br />
our communities to continue to<br />
defend the immigration action and<br />
push lasting immigration reform to<br />
the forefront of the agenda with our<br />
vote.”<br />
The brief provides personal stories<br />
and testimonials about potential<br />
beneficiaries of expanded DACA<br />
and DAPA and explains how these<br />
deferred action initiatives would<br />
positively impact millions of U.S.<br />
More on page 34
New generation.<br />
New possibilities.<br />
Secure your site with the new F3 Series Fence<br />
Controllers, the latest in perimeter protection.<br />
Find out more at security.gallagher.com/latest-releases<br />
security.gallagher.com<br />
security.gallagher.com
Airport police support legislative efforts<br />
to tighten internal security, with complete<br />
employee screening<br />
LOS ANGELES, CA, <strong>Dec</strong>ember 9<br />
- The American Alliance of Airport<br />
Police Officers (AAAPO) supports<br />
legislation introduced by Senator<br />
Bill Nelson (D- FL), Ranking Member<br />
of the Senate Commerce, Science,<br />
& Transportation Committee,<br />
to strengthen internal security at our<br />
nation’s airports.<br />
The Senator’s Airport Security Enhancement<br />
and Oversight Act calls<br />
for increased screening of aviation<br />
employees and increased oversight<br />
of employees’ secure access badges.<br />
While these proposals are important<br />
to enhancing airport safety, the most<br />
comprehensive solution to fortifying<br />
security at major airports is to immediately<br />
begin performing 100%<br />
screening of all airport employees,<br />
including TSA, and their belongings.<br />
As the AAAPO noted in its 2012 letter<br />
to then TSA Administrator John<br />
Pistole, the most effective way to keep<br />
the public safe is by conducting total<br />
screening of every employee and their<br />
backpacks, purses, bags, etc. Given<br />
that passengers are already subject to<br />
these screening procedures, it is within<br />
reason to expect the same security<br />
standards for airport employees and<br />
TSA.<br />
The Russian Metrojet bombing incident,<br />
which is suspected<br />
to have been<br />
carried out by an<br />
airport employee,<br />
exemplifies the dangers<br />
of the “insider”<br />
threat. Here at<br />
home, in <strong>Dec</strong>ember<br />
of last year, a gun<br />
smuggling scheme<br />
at Hartsfield-Jackson Atlanta International<br />
Airport allowed an airline employee<br />
to bring guns into secure parts<br />
of the airport, while a former airline<br />
employee transported the guns on<br />
flights made between Atlanta and<br />
New York, again highlighting the ongoing<br />
internal security vulnerabilities<br />
at our nation’s airports.<br />
Incidents like the Atlanta gun<br />
smuggling ring are possible because<br />
at many major airports employees are<br />
permitted to enter the airport property<br />
via a rudimentary metal turnstile<br />
that is located immediately off<br />
the aeronautical side of the airport<br />
with easy access to waiting airplanes.<br />
For example, at JFK, the turnstile entrance<br />
point only requires the employee<br />
to swipe their badge and enter<br />
a code-no biometrics are used and<br />
there is no physical screening of the<br />
employee or the bags, purses, etc., the<br />
18<br />
employee brings into<br />
the airport. Without<br />
a nationwide standard<br />
regarding the<br />
screening of airport<br />
employees at major<br />
airports, such security<br />
gaps will continue<br />
to pose dangers to<br />
the traveling public.<br />
In this regard, the AAAPO supports<br />
Senator Nelson’s efforts to improve<br />
security at our country’s airports and<br />
calls on Congress to immediately<br />
implement public policy that requires<br />
the screening of all airport employees,<br />
including TSA.<br />
The Los Angeles Airport Peace Officers<br />
Association (LAAPOA) represents<br />
the sworn police officers and<br />
firefighters of the Los Angeles Airport<br />
Police Department assigned to<br />
protect and serve Los Angeles International<br />
Airport (LAX), LA/Ontario<br />
International Airport (ONT) and<br />
Van Nuys Airport (VNY). For more<br />
information on LAAPOA, please visit<br />
laapoa.com.<br />
The American Alliance of Airport<br />
Police Officers (AAAPO) is comprised<br />
of rank-and-file airport police
officers (including many dual police/<br />
aircraft rescue firefighters) who stand<br />
as the first line of defense against terrorist<br />
attacks, hijackings and other<br />
criminal activity at our nation’s airports.<br />
We seek to promote security<br />
and safety for the traveling public, visitors<br />
and airport employees by highlighting<br />
best practices and identifying<br />
areas for improvement and proposed<br />
solutions for our nation’s airport security<br />
deployment. AAAPO focuses<br />
on regulatory issues that promote our<br />
efforts to provide the most advanced<br />
and cutting-edge service innovations<br />
and security processes in our nation<br />
and the world. Our organization represents<br />
thousands of sworn law enforcement<br />
officers across the United<br />
States beholden only to this mission.<br />
We are unencumbered by neither political<br />
nor managerial constraints that<br />
would prevent us from promoting<br />
sound public safety policy.<br />
The founding members of the American<br />
Alliance of Airport Police Officers<br />
are comprised of numerous rank-andfile<br />
airport police officers from John F.<br />
Kennedy International Airport; La-<br />
Guardia Airport; Los Angeles International<br />
Airport; Dallas/Fort Worth<br />
International Airport; LA/Ontario<br />
International Airport; Newark Liberty<br />
International Airport; Van Nuys Airport;<br />
Stewart International Airport;<br />
and Teterboro Airport.<br />
U.S. Conference of Mayors President,<br />
Baltimore Mayor Stephanie Rawlings-Blake,<br />
applauds unprecedented agreement at COP21<br />
WASHINGTON, <strong>Dec</strong>. 14, <strong>2015</strong> /<br />
PRNewswire-USNewswire/ -- The<br />
United States Conference of Mayors<br />
President Baltimore Mayor<br />
Stephanie Rawlings-Blake issued<br />
the following statement regarding<br />
the agreement reached at COP 21 in<br />
Paris:<br />
“I applaud our national<br />
governments for<br />
reaching consensus<br />
on climate<br />
change at COP<br />
21. Finally, our<br />
leaders have<br />
come together<br />
to acknowledge<br />
the threat<br />
that climate<br />
change presents<br />
to our safety<br />
and security, regardless<br />
of where we live. 195<br />
nations, large and small, rich and<br />
poor, have now committed to take<br />
substantive action that will lower<br />
greenhouse emissions.<br />
“America’s mayors have called on<br />
the nations of the world to act on<br />
climate change for over a decade.<br />
Earlier this month, I led a Conference<br />
of Mayors mission to COP 21,<br />
where we joined with 1,000 mayors<br />
19<br />
to urge international agreement. I<br />
am proud of what we accomplished<br />
in Paris and am honored to have<br />
taken part in this watershed moment<br />
for our planet.<br />
“As national governments move<br />
toward implementation of this historic<br />
accord, America’s mayors<br />
stand ready to do our<br />
part. In 2005, we<br />
began committing,<br />
city by city,<br />
to the Mayors<br />
Climate Protection<br />
Agreement.<br />
In Paris,<br />
we celebrated<br />
the 10th anniversary<br />
of that<br />
agreement, and<br />
over 1,000 U.S. cities<br />
have joined our efforts.”<br />
The U.S. Conference of Mayors<br />
is the official nonpartisan organization<br />
of cities with populations of<br />
30,000 or more. There are nearly<br />
1,400 such cities in the country today,<br />
and each city is represented in<br />
the Conference by its chief elected<br />
official, the mayor.
FAA announces user-friendly aircraft registration<br />
for process for small unmanned aircraft owners<br />
WASHINGTON, DC, <strong>Dec</strong>ember<br />
14 – The U.S. Department of Transportation’s<br />
Federal Aviation Administration<br />
(FAA) today announced a<br />
streamlined and user-friendly webbased<br />
aircraft registration process<br />
for owners of small unmanned aircraft<br />
(UAS) weighing more than<br />
0.55 pounds (250 grams) and less<br />
than 55 pounds (approx. 25 kilograms)<br />
including payloads such as<br />
on-board cameras.<br />
The Registration Task Force delivered<br />
recommendations to FAA<br />
Administrator Michael Huerta and<br />
Transportation Secretary Anthony<br />
Foxx on November 21. The rule incorporates<br />
many of the task force<br />
recommendations.<br />
“Make no mistake: unmanned<br />
aircraft enthusiast are aviators, and<br />
with that title comes a great deal of<br />
responsibility,” said U.S. Transportation<br />
Secretary Anthony Foxx. “Registration<br />
gives us an opportunity to<br />
work with these users to operate<br />
their unmanned aircraft safely. I’m<br />
excited to welcome these new aviators<br />
into the culture of safety and responsibility<br />
that defines American<br />
innovation.”<br />
Registration is a statutory requirement<br />
that applies to all aircraft. Under<br />
this rule, any owner of a small<br />
UAS who has previously operated<br />
an unmanned aircraft exclusively<br />
as a model aircraft prior to <strong>Dec</strong>ember<br />
21, <strong>2015</strong>, must register no later<br />
than February 19, <strong>2016</strong>. Owners of<br />
any other UAS purchased for use as<br />
a model aircraft after <strong>Dec</strong>ember 21,<br />
<strong>2015</strong> must register before the first<br />
flight outdoors. Owners may use either<br />
the paper-based process or the<br />
new streamlined, web-based system.<br />
Owners using the new streamlined<br />
web-based system must be at<br />
least 13 years old to register.<br />
Owners may register through a<br />
web-based system at: www.faa.gov/<br />
uas/registration<br />
Registrants will need to provide<br />
their name, home address and e-<br />
mail address. Upon completion of<br />
the registration process, the web<br />
application will generate a Certificate<br />
of Aircraft Registration/Proof<br />
of Ownership that will include a<br />
unique identification number for<br />
the UAS owner, which must be<br />
marked on the aircraft.<br />
Owners using the model aircraft<br />
for hobby or recreation will only<br />
have to register once and may use<br />
the same identification number for<br />
all of their model UAS. The registration<br />
is valid for three years.<br />
The normal registration fee is<br />
20<br />
$5, but in an effort to encourage as<br />
many people as possible to register<br />
quickly, the FAA is waiving this fee<br />
for the first 30 days (from <strong>Dec</strong>. 21,<br />
<strong>2015</strong> to <strong>Jan</strong> 20, <strong>2016</strong>).<br />
“We expect hundreds of thousands<br />
of model unmanned aircraft will<br />
be purchased this holiday<br />
season,” said FAA Administrator<br />
Huerta.<br />
“Registration gives<br />
us the opportunity<br />
to educate these<br />
new airspace users<br />
before they fly<br />
so they know the<br />
airspace rules and<br />
understand they<br />
are accountable to<br />
the public for flying<br />
responsibly.”<br />
The online registration<br />
system does not yet support registration<br />
of small UAS used for any<br />
purpose other than hobby or recreation<br />
– for example, using an unmanned<br />
aircraft in connection with<br />
a business. The FAA is developing<br />
enhancements that will allow such<br />
online registrations by spring of<br />
<strong>2016</strong>.<br />
The full rule can be viewed here:<br />
www.faa.gov/news/updates/media/<strong>2015</strong>1213_IFR.pdf
FAA updates airspace obstructions standards to<br />
make sure that airspace is safe and navigable<br />
Among the Federal Aviation Administration’s<br />
(FAA) main priorities<br />
is to keep all users of our national<br />
airspace safe. To maintain the safest<br />
aerospace system in the world, the<br />
FAA must make sure the national<br />
airspace is navigable and free of<br />
obstructions.<br />
When anyone proposes<br />
new construction<br />
or proposes<br />
to alter<br />
existing structures<br />
near airports<br />
or navigational<br />
aids,<br />
the FAA determines<br />
how the<br />
proposal would<br />
affect the airspace.<br />
These FAA determinations<br />
about the appropriate<br />
height of buildings, wind<br />
turbines and meteorological towers<br />
near airports, and how they are<br />
lighted and marked, contribute to<br />
the safe navigation of our skies.<br />
The agency has updated its guidelines<br />
for the proper way to light and<br />
mark obstructions affecting navigable<br />
airspace. Advisory Circular<br />
70/7460-1L for Obstruction Lighting<br />
and Marking is effective immediately.<br />
It cancels Advisory Circular<br />
70/7460-1K, dated February 1,<br />
2007.<br />
The main changes to the updated<br />
advisory circular are as follows:<br />
• Federal law requires that the<br />
FAA determine whether a structure<br />
that is proposed to be built or<br />
altered, 200 feet above ground level<br />
(AGL) or higher, or near an airport,<br />
does not pose a hazard to the airspace.<br />
To remain consistent with<br />
changes to the Code of Federal Regulation<br />
(CFR) Part 77, the height of<br />
a structure identified as an obstruction<br />
has been lowered from 500 feet<br />
(AGL) to 499 feet (AGL). All structures<br />
above 499 feet are considered<br />
obstructions and the FAA will continue<br />
to conduct an aeronautical<br />
study on these types of structures to<br />
determine their effect on the navigable<br />
airspace and ensure they do<br />
not create a hazard.<br />
• New lighting is specified for<br />
wind turbines at various heights.<br />
These recommendations will provide<br />
needed guidance for the rapidly<br />
developing wind industry that<br />
takes into account the unique characteristics<br />
of wind turbine farms.<br />
• The FAA implemented standards<br />
for voluntary marking of meteorological<br />
evaluation towers lower than<br />
200 feet. This is an effort to make<br />
21<br />
meteorological evaluation towers<br />
more noticeable and to add an extra<br />
layer of protection for low-level<br />
agricultural flight operations. These<br />
standards include those for lighting<br />
and marking of the tower and associated<br />
guy wires.<br />
• New lighting and marking standards<br />
are provided to reduce the impact<br />
on migratory bird populations.<br />
This change will reduce the confusion<br />
and disruption to migratory<br />
bird patterns that has been attributed<br />
to certain obstruction marking<br />
schemes.<br />
• A chapter on Aircraft Detection<br />
Lighting Systems (Chapter 14) was<br />
added to provide performance standards<br />
for these types of systems. This<br />
change is in response to community<br />
groups, industry, and the aviation<br />
community. New standards will enable<br />
lighting systems that operate<br />
based on aircraft proximity, increasing<br />
safety while reducing other impacts<br />
of the lighting schemes.<br />
For more information on this Advisory<br />
Circular and others go to: http://<br />
www.faa.gov/regulations_policies/<br />
advisory_circulars/
Campbell on Crypto<br />
Insider Threats:<br />
Why passwords aren’t enough<br />
By Shawn Campbell<br />
The rise in hacking from hostile<br />
agents or rogue nations is of growing<br />
concern to IT professionals. But<br />
the threat is not just from the outside.<br />
Unauthorized access to local<br />
corporate networks by employees or<br />
contractors has created the notion<br />
of “insider threat” – which is now<br />
part of almost every discussion on<br />
cyber security.<br />
The definition of<br />
“insider threat” is<br />
broad. It can refer to<br />
everything from malicious,<br />
covert actions<br />
of individuals within<br />
or connected to an organization,<br />
to the accidental<br />
compromising<br />
of data when an<br />
end-user device is lost.<br />
How pervasive is the damage<br />
caused by unauthorized access? The<br />
Gemalto Breach Level Index reports<br />
that nearly 44,000,000 records have<br />
been breached by a malicious insider<br />
as of November <strong>2015</strong>, with the<br />
majority the result of identity theft.<br />
Targets have included organizations<br />
in US, South Korea, Mexico and the<br />
UK, to name a few.<br />
Although general end-users can<br />
pose a threat to an organization, the<br />
most significant data breaches often<br />
can be traced back to users with administrative<br />
privileges.<br />
When it comes to controlling insider<br />
threats, it is not effective to<br />
rely on simple passwords to access<br />
data. A multi-factor approach to authentication<br />
and access is the only<br />
The Gemalto Breach Level Index reports that<br />
nearly 44,000,000 records have been breached<br />
by a malicious insider as of November <strong>2015</strong>,<br />
with the majority the result of identity theft.<br />
real way to minimize the danger of<br />
insider threats.<br />
The ineffective password<br />
22<br />
Many administrative users in an organization<br />
have elevated privileges,<br />
because they need access to a wide<br />
range of applications, networks and<br />
systems. To keep it simple to access<br />
the infrastructure, administrators<br />
often fall back on a one-factor authentication<br />
method, such as a password.<br />
Unfortunately, passwords are not<br />
enough to protect your organization<br />
from insider hack and malware.<br />
They will not adequately protect<br />
employee computers and privileged<br />
workstations.<br />
Because each system and application<br />
requires its own password,<br />
administrators have<br />
to track and manage<br />
numerous passwords<br />
just to do<br />
their job on a daily<br />
basis. That’s a significant<br />
administrative<br />
burden, and often<br />
passwords are stored<br />
in unsecure locations<br />
where they easily can be lost,<br />
stolen or compromised.<br />
Furthermore, it is challenging to<br />
match a password to a user’s identity.<br />
Anyone with access to a password<br />
can pose as the password’s<br />
owner/user – and access any system<br />
for which the user has privileges.<br />
So, one-factor authentication is<br />
ineffective at securing access to an<br />
organization’s networks. To improve
Access Control, ID, Insider Threats<br />
security dramatically, organizations<br />
should utilize two or even three<br />
forms of authentication.<br />
Beyond the password:<br />
Multi-factor authentication<br />
Multi-factor authentication is vital<br />
to both securing access to networks<br />
and protecting users’ identities.<br />
After all, the more factors used to<br />
determine a person’s identity, the<br />
greater the trust of authenticity.<br />
With multi-factor authentication,<br />
an organization can be sure that users<br />
are who they claim to be.<br />
Because multi-factor authentication<br />
security requires multiple<br />
means of identification at login, it<br />
is widely recognized as the most secure<br />
method for authenticating access<br />
to data and applications.<br />
The best way to achieve multifactor<br />
authentication is by using a<br />
combination of the following factors:<br />
• Something You Know – password<br />
or PIN<br />
• Something You Have – token or<br />
smart card (two-factor authentication)<br />
• Something You Are – biometrics,<br />
such as a fingerprint (threefactor<br />
authentication)<br />
A strong authentication solution<br />
that validates the identities of users<br />
and computing devices that access<br />
the non-public areas of an organization’s<br />
network is the first step in<br />
building a secure and robust information<br />
protection system.<br />
How to put strong<br />
authentication to work<br />
Practically speaking, there are two<br />
aspects to follow when putting<br />
strong authentication to work:<br />
• Consider all access points<br />
• Ensure the solution reduces IT<br />
administrative and management<br />
overhead<br />
Consider all access points. Organizations<br />
need to be sure that they<br />
authenticate access to all sensitive<br />
information, whether that information<br />
is on premise or in the cloud.<br />
When it comes to the cloud, the<br />
same security mechanisms should<br />
be in place as in remote network access.<br />
Additionally, organizations should<br />
deploy security mechanisms to make<br />
sure that users are securely authenticated<br />
when accessing network resources<br />
from their mobile consumer<br />
devices (such as tablets and smart<br />
phones).<br />
Ensure the solution reduces<br />
IT administrative and<br />
management overhead.<br />
Authentication environments have<br />
to offer convenience and transparency<br />
for end users and administrators<br />
alike.<br />
23<br />
Administrators need to be able<br />
to manage all users across all devices<br />
and resources. That requires<br />
automation, central management,<br />
and visibility into user access across<br />
multiple resources. To ensure users<br />
have an optimal experience, administrators<br />
need to be equipped with<br />
granular controls and comprehensive<br />
reporting capabilities.<br />
On the end-user side of things,<br />
organizations should be able to offer<br />
users the type of authentication<br />
device that most suits their role and<br />
security profile. Organizations can<br />
offer users several authentication<br />
methods, ranging from contextbased<br />
authentication, through SMS,<br />
phone tokens or hardware tokens.<br />
This improves user acceptance and<br />
compliance with security requirements.<br />
Multi-factor authentication is not<br />
particularly complicated, but it surpasses<br />
passwords by a considerable<br />
margin when protecting your infrastructure<br />
and information from being<br />
compromised – especially from<br />
insider threats.<br />
Shawn Campbell, a nationally recognized<br />
cryptology expert, is VP of Product<br />
Management, SafeNet Assured<br />
Technologies. He can be reached at<br />
Shawn.Campbell@safenetat.com
Access Control, ID, Insider Threats<br />
Sonavation announces SonicTouch <br />
Ultrasound Biometric Authentication Solution<br />
PALM BEACH GARDENS, FL –<br />
Sonavation, a pioneer in ultrasound<br />
biometric technology and first to<br />
develop and successfully bond an<br />
ultrasound biometric sensor to device<br />
protective glass, has announced<br />
another major industry innovation<br />
with SonicTouch, the most advanced<br />
authentication solution for<br />
digital and device security. It is a<br />
FIDO-ready ultrasound biometric<br />
authenticator system-in-package<br />
module that is uniquely designed to<br />
deliver the next generation of identity<br />
security and ease of integration<br />
into mobile and IoT devices.<br />
Sonavation is currently finalizing<br />
design-in specifications and launch<br />
schedules with three global tier one<br />
mobile device manufacturers.<br />
By 2020, biometric technology is<br />
expected to secure $5.6T in mobile<br />
payment transactions and it is estimated<br />
that there will be more than<br />
25B internet connected devices.<br />
Consumers and companies demand<br />
the highest level of assurance<br />
in protecting their identity, personal<br />
data and digital transactions.<br />
SonicTouch was engineered for an<br />
unrivaled experience that empowers<br />
trust and delivers peace of mind<br />
with one touch.<br />
With its Match-In-Sensor architecturally<br />
flexible design, Sonic-<br />
Touch is a dramatic advancement<br />
in trustworthy authentication. Incorporating<br />
the Sonavation 3D ultrasound<br />
sensor, Sonic-<br />
Touch is the industry’s first<br />
full-stack solution with the<br />
highest level end-to-end<br />
encryption architecture<br />
that provides a fully encapsulated<br />
locked-down<br />
module. Combined with<br />
upgradable anti-spoofing<br />
Karl F. Weintz, CEO<br />
and Level 3+ matching<br />
systems, secure transaction platforms<br />
can be deployed by mobile<br />
and IoT device manufacturers, mobile<br />
network operators and application<br />
developers.<br />
With SonicTouch, a user’s singularly<br />
unique acoustic fingerprint<br />
signature is captured, encrypted and<br />
never leaves the device. SonicTouch<br />
demonstrates the highest accuracy<br />
extract and match and allows authentication<br />
despite moisture, dirt<br />
or lotion that might be present on a<br />
user’s finger. Because device protective<br />
glass integrity is of utmost importance,<br />
SonicTouch was purpose-<br />
24<br />
fully designed to eliminate the need<br />
to etch out or cut into the protective<br />
display glass, thus keeping the<br />
full strength of the glass intact. For<br />
device manufacturers, this is a critical<br />
element to reducing device costs<br />
while providing a positive<br />
end-user experience.<br />
According to Karl<br />
Weintz, Sonavation chief<br />
executive offier, “The digital<br />
and connected world is<br />
at our doorstep and is already<br />
beginning to touch<br />
every aspect of life. This<br />
makes biometric security a<br />
critical component and evolving authority<br />
that demands our attention.<br />
The ultra-thin SonicTouch is the<br />
comprehensive advancement that<br />
will enable the most secure authentication<br />
solution for manufacturers.<br />
Those looking to deliver secure solutions<br />
with a protected touch sensor<br />
or touch-under-cover sensor<br />
can now guarantee biometrics are<br />
easily integrated and convenient to<br />
provide a great user experience with<br />
cutting-edge authentication options.”<br />
Dr Rainer Schmitt, Sonavation’s<br />
chief technology officer, added that
Smart Card strong authentication protects<br />
workstations, mobile devices and networks<br />
HID Global’s ActivClient® software<br />
allows organizations to move beyond<br />
simple passwords and deploy<br />
the best strong authentication solution<br />
for their environment.<br />
This strong authentication<br />
solution is available for all major<br />
mobile platforms, enabling<br />
organizations to protect their<br />
resources whether accessed<br />
from a desktop, laptop, tablet or<br />
smartphone.<br />
ActivClient software has been deployed<br />
in over four million desktop<br />
installations and is interoperable<br />
with leading smart cards, readers,<br />
operating systems, certificate authorities,<br />
network environments<br />
and enterprise applications.<br />
With ActivClient, organizations<br />
can confidently:<br />
• Increase security: ActivClient<br />
is proven technology that is widely<br />
adopted, and offers a user-friendly<br />
strong authentication experience.<br />
• Improve compliance: Complies<br />
with all major government and industry<br />
regulations.<br />
• Optimize productivity: Single,<br />
navation aims to broaden the proliferation<br />
of biometric technology,<br />
ultimately increasing the security<br />
on mobile and IoT devices.<br />
About Sonavation<br />
The Sonavation product line is<br />
designed to provide secure authentication<br />
and protection for digital<br />
and physical environments for consumers<br />
and businesses. Solutions<br />
include both embedded and standalone<br />
device offerings designed to<br />
protect access to online systems<br />
including: e-Commerce, financial<br />
services, health data and other sen-<br />
25<br />
versatile strong authentication tool<br />
for both Windows Login and Remote<br />
Access.<br />
• Reduce costs: Integrates easily<br />
into existing infrastructure.<br />
Enable users to easily perform<br />
their daily work without compromising<br />
network security. HID<br />
Global has a wide range of strong<br />
authentication options to secure<br />
access and easily manage<br />
corporate authentication policies.<br />
Download our white paper<br />
“Establishing Trust in User<br />
Identities with Strong Authentication<br />
Technologies” to learn how to<br />
achieve the level of identity assurance<br />
you need, in a way that’s both<br />
convenient and affordable.<br />
“The high frequency ultrasound<br />
technology deployed in SonicTouch<br />
provides high resolution imaging<br />
utilizing acoustic impediography.<br />
The difference of acoustic properties<br />
in the fingerprint structure of ridges<br />
and valleys is at least two orders of<br />
magnitude higher than those of optical<br />
and capacitive fingerprint imaging<br />
methods. This makes acoustic<br />
impediography simple and robust,<br />
while providing the means for<br />
through glass fingerprinting.”<br />
By empowering OEMs with this<br />
easily deployable technology, So-<br />
sitive applications.<br />
Sonavation designs and manufactures<br />
the industry’s leading biometric<br />
fingerprint sensors, utilizing<br />
ultrasound. Its 3D surface scan and<br />
sub-surface technology is protected<br />
by 42 awarded patents and an additional<br />
47 patents filed, making it<br />
the world’s smallest low-power ultrasound<br />
sensor. Headquartered in<br />
Palm Beach Gardens, Fla., Sonavation<br />
is committed to “Empowering<br />
Trust, Delivering Peace of Mind.”
Access Control, ID, Insider Threats<br />
New Entrust cloud capabilities simplify SSL<br />
certificate management, prevent costly mishaps<br />
MINNEAPOLIS—(DEC. 1, <strong>2015</strong>)—<br />
Entrust Datacard today announced<br />
that it has introduced several key<br />
enhancements to its cloud-based<br />
SSL certificate management platform,<br />
Entrust Cloud. The new capabilities<br />
will bring increased simplicity<br />
and control to every step of<br />
the digital certificate management<br />
process, from acquisition, configuration<br />
and installation of certificates<br />
to server analysis, compliance monitoring<br />
and security scans.<br />
The features, which make it easy<br />
for customers to purchase, configure,<br />
install, track and renew SSL<br />
certificates, make Entrust Cloud the<br />
most streamlined platform in industry.<br />
“We greatly expanded the capabilities<br />
of Entrust Cloud to make<br />
life easier for our customers and<br />
to protect them from the financial<br />
impact of expired, rogue or improperly<br />
installed certificates,” said<br />
Russell St. John, senior vice president<br />
of global marketing for Entrust<br />
Datacard. “Certificate-related problems<br />
can cost businesses hundreds<br />
of thousands of dollars a year due to<br />
breaches and other types of fraud,<br />
as well as lost revenue from potential<br />
customers simply abandoning<br />
sites they felt were not secure.”<br />
Highlights of the<br />
new capabilities include:<br />
Entrust® Turbo Auto-Install Client.<br />
A simplified method for installing<br />
SSL certificates and configuring<br />
servers on Microsoft Windows<br />
platforms. Automatically installing<br />
certificates directly to servers<br />
speeds deployment and greatly<br />
minimizes opportunities for configuration<br />
errors.<br />
Automated SSL Server Test. Periodic<br />
testing of servers for configu-<br />
26<br />
ration compliance protects against<br />
Heartbleed, Poodle and other similar<br />
threats. A new automated testing<br />
feature provides deep analysis<br />
of web servers, identifies potential<br />
vulnerabilities and checks compliance<br />
levels. Email notifications and<br />
screen prompts provide automatic<br />
notification of potential problems.<br />
Reporting Engine. Consolidated<br />
data for both Entrust-issued and<br />
discovered certificates is delivered<br />
via standard or customized reports<br />
— or displayed on a management<br />
dashboard. New widgets allow users<br />
to configure the dashboard for customized<br />
views and drill-downs.<br />
Automated Alerts. Customers can<br />
choose to receive email alerts or<br />
dashboard prompts when the management<br />
platform automatically<br />
detects potential problems with certificate<br />
policy, best practices, compliance<br />
or other key considerations.<br />
Site Analysis and Reporting. Customers<br />
can continually scan all of<br />
the websites associated with their<br />
SSL certificates and determine security<br />
levels for each one. This new<br />
feature also provides reports on
certificate locations, certificate and<br />
server configurations, number and<br />
types of certificates for each site,<br />
malware configurations and more.<br />
Certificate Pickup Wizard. An<br />
intuitive new process speeds certificate<br />
installation by delivering<br />
server-specific instructions and file<br />
bundles. Certificate information,<br />
tracking numbers, server types and<br />
associated certificate chains are all<br />
displayed.<br />
“Our customers realize true network<br />
security requires more than<br />
just the simple installation of SSL<br />
certificates,” St. John said. “They<br />
have asked for new capabilities that<br />
allow them to better configure, scan,<br />
track and renew SSL certificates.<br />
These new Entrust Cloud features<br />
offer all of those capabilities and<br />
more.”<br />
To learn more about Entrust Cloud,<br />
visit: https://www.entrust.com/products/cloud/.<br />
About Entrust Datacard<br />
Consumers, citizens and employees<br />
increasingly expect anywhereanytime<br />
experiences — whether<br />
they are making purchases, crossing<br />
borders, accessing e-gov services or<br />
logging onto corporate networks.<br />
Entrust Datacard offers the trusted<br />
identity and secure transaction<br />
technologies that make those experiences<br />
reliable and secure. Solutions<br />
range from the physical world<br />
Viscount unveils Freedom Channel Partner<br />
Program with enhanced technical support<br />
of financial cards, passports and<br />
ID cards to the digital realm of authentication,<br />
certificates and secure<br />
communications. With more than<br />
2,000 Entrust Datacard colleagues<br />
around the world, and a network of<br />
strong global partners, the company<br />
serves customers in 150 countries<br />
worldwide. For more information,<br />
visit www.entrustdatacard.com.<br />
27<br />
VANCOUVER, British Columbia,<br />
<strong>Dec</strong>ember 16, <strong>2015</strong> – Viscount Systems,<br />
Inc. (OTCQB:VSYS) (“Viscount”),<br />
a software company specializing<br />
in physical and logical security<br />
solutions, today announced its Viscount<br />
Systems Certified Channel<br />
Partner Program. The initiative is<br />
designed to help system integrators<br />
expand business opportunities and<br />
revenue growth through the delivery<br />
of Viscount access control and<br />
security management solutions.<br />
Viscount’s Freedom access control<br />
application enables partners to capitalize<br />
on unique differentiators that<br />
drive today’s convergence of physical<br />
and logical access control solutions.<br />
There are measurable benefits<br />
to adopting a unified physical and<br />
logical security program, and customers<br />
in a host of vertical markets<br />
are looking for trusted partners to<br />
help implement technologies to<br />
support this approach.<br />
Partnering with Viscount enables<br />
integrators to deliver unique and<br />
innovative access control, and integrated<br />
security management solutions<br />
to a new generation of security<br />
managers who take a more<br />
holistic approach to securing their<br />
company’s assets. Partnering with<br />
Viscount empowers systems integrators<br />
through the delivery of technologically<br />
advanced solutions that<br />
cost less to install while delivering<br />
an unparalleled level of security at a<br />
lower cost of ownership.<br />
Freedom Certified Channel Partners<br />
gain access to sales and marketing<br />
resources, enhanced technical<br />
support and training, and the<br />
opportunity to maximize margins<br />
and tap into new business opportunities.<br />
The Certified Channel Partner<br />
Program is an exclusive network<br />
of preferred partners that meet high<br />
standards of technical and IT security<br />
expertise and maintain a reputa-<br />
More on page 30
Access Control, ID, Insider Threats<br />
United Arab Emirates goes<br />
eBorder with Morpho<br />
<strong>2015</strong>, UNITED ARAB EMIRATES:<br />
Morpho, in partnership with eI-<br />
MASS, is implementing the prestigious<br />
eBorder management system<br />
in five major airports in the UAE.<br />
The project is setting the standards<br />
for the future of border control in<br />
the world, combining<br />
the very latest in<br />
biometric technologies,<br />
automation<br />
and system integration.<br />
Expanding<br />
upon the eBorder<br />
pilot implemented<br />
in 2012 in Abu Dhabi,<br />
the success story<br />
goes on.<br />
Full Entry and<br />
Exit passenger processing using 96<br />
e-Gates, 94 e-Counters, contactless<br />
and at-a-distance biometric<br />
capture, seamless integration into<br />
existing infrastructure in all project<br />
locations, those are some of the<br />
key features of eBorder in <strong>2015</strong>. No<br />
magic here, but a thorough understanding<br />
of the UAE’s context and a<br />
close partnership with the Ministry<br />
of Interior to design the most fitted<br />
system, leading to golden opportunities<br />
for multiple stakeholders.<br />
The border control challenge<br />
in the UAE<br />
Being centrally located in the Gulf<br />
region, the UAE are at the crossroads<br />
between Europe, Africa and<br />
Asia. UAE airports are among the<br />
busiest in the world, with more than<br />
100 million passengers handled in<br />
2014. The United Arab Emirates are<br />
also a highly attractive country, for<br />
both business people and tourists.<br />
85% of the UAE population are foreigners.<br />
This unique UAE context exacerbates<br />
the challenge of improving<br />
both security and passenger facilitation<br />
that is becoming familiar to<br />
border management authorities<br />
around the world.<br />
Multi-biometrics as the key<br />
to eBorder system<br />
Only the use of biometrics can actually<br />
meet this challenge. Indeed,<br />
biometrics is today’s most secure<br />
way to irrevocably identify an individual.<br />
And Morpho’s latest biometric<br />
technology is now fast, nonintrusive,<br />
even fun, dramatically<br />
improving user experience and particularly<br />
adapted to fit in an airport<br />
environment.<br />
In 2011, Abu Dhabi Police decided<br />
to test the multi-biometric border<br />
management concept and selected<br />
Morpho and eIMASS to implement<br />
a pilot system, connected to<br />
the UAE IRIS system, which is the<br />
key biometric of eBorder system.<br />
The IRIS system is also provided by<br />
Morpho and eIMASS.<br />
The current expansion of the pilot<br />
across the UAE features Morpho’s<br />
Finger On-the-Fly technology,<br />
which is a very rapid, touchless way<br />
of capturing fingerprint, and Iris<br />
At-a-Distance, the world’s fastest<br />
operational capture time (less than<br />
1 second for simultaneous capture<br />
of iris and face).<br />
Sharing the benefits of the system<br />
eBorder system is shaped for everybody’s<br />
benefit, which makes it so<br />
valuable:<br />
• The travelling public benefit<br />
28
SecuGen to showcase new unity<br />
biometric development platform<br />
at CES <strong>2016</strong><br />
from both the efficiency and the visual<br />
appeal of eCounters and eGates,<br />
with the assurance to make their<br />
journey safely and comfortably;<br />
• Those who run the systems enjoy<br />
a more productive, more satisfying<br />
working environment. To airports,<br />
passengers’ satisfaction goes<br />
together with airlines’ satisfaction,<br />
to increase airport’s profitability.<br />
• The Authorities that depend on<br />
the performance and reliability of<br />
the systems value the security guaranteed<br />
by this fully integrated, nationwide<br />
approach to border control.<br />
See more at: http://www.morpho.<br />
com/en/aviation-border-security/<br />
helping-airports-make-passengertravel-safer-and-hassle-free#sthash.<br />
qaBesOmD.dpuf<br />
29<br />
SANTA CLARA, Calif. (<strong>Dec</strong>ember<br />
14, <strong>2015</strong>) – SecuGen, a world leading<br />
optical fingerprint device and<br />
technology vendor, will be showcasing<br />
at CES <strong>2016</strong> its new product,<br />
Unity BDP, a platform for the development<br />
of a wide array of fingerprint<br />
enabled biometric products.<br />
Developers are invited to come by<br />
SecuGen’s booth, number 21733 in<br />
South Hall 1 of the Las Vegas Convention<br />
Center to see a demonstration<br />
of this revolutionary new OEM<br />
fingerprint sensor.<br />
More than ever before, hardware<br />
device manufacturers must consider<br />
whether biometric security<br />
is appropriate for their products.<br />
SecuGen has now made it very easy<br />
to embed sophisticated fingerprint<br />
technology into a wide variety of<br />
hardware products with its new<br />
Unity Biometric Development Platform.<br />
The Unity BDP offers device manufacturers<br />
a flexible, expandable,<br />
and easy to use environment that<br />
provides a simplified way to embed<br />
fingerprint capability into a very<br />
wide range of products such as access<br />
control devices, time & attendance<br />
machines, civil ID handheld<br />
devices, ATMs, industrial equipment,<br />
point of sale equipment, and<br />
much, much more.<br />
With an integrated Linux development<br />
environment and embedded<br />
biometric fingerprint registration<br />
and matching functions, Unity BDP<br />
delivers efficiency of development<br />
in one small but powerful package.<br />
The Unity BDP includes a FAP<br />
20 certified optical fingerprint sensor,<br />
an open Linux system running<br />
on a 1 GHz CPU, and a modular<br />
design that easily accommodates a<br />
wide array of expansion boards. Future<br />
expansion boards may include<br />
Ethernet, Bluetooth capability, and<br />
battery logic for mobile devices. The<br />
boards may also provide a wide array<br />
of interfaces such as LED displays,<br />
keypads, RS-232, and USB. In<br />
More on page 30
Access Control, ID, Insider Threats<br />
SecuGen to showcase new unity<br />
biometric development platform<br />
Continued from page 29<br />
addition, Unity BDP includes an API<br />
that gives developers access to Secu-<br />
Gen’s NIST certified template extraction<br />
and matching algorithms.<br />
Using Unity BDP, many developers<br />
will find that there is no longer a<br />
need for a separate controller board<br />
since Unity BDP comes with a fast<br />
processor, open Linux, and the ability<br />
to add various interfaces and logic<br />
via expansion boards. This makes<br />
Unity BDP an ultra-compact, enormously<br />
capable, and affordable biometric<br />
platform that features Secu-<br />
Gen’s renowned high quality optical<br />
fingerprint sensor.<br />
“Unity BDP is the world’s first biometric<br />
development platform as far<br />
as we can tell,” stated Jeff Brown, VP<br />
of Sales and Marketing for SecuGen.<br />
“Our team has been able to go far beyond<br />
delivering a simple fingerprint<br />
sensor. Unity BDP includes a comprehensive<br />
set of tools that allow developers<br />
to create fingerprint enabled<br />
products quickly and efficiently. This<br />
product is revolutionary.”<br />
VP of Engineering Dan Riley added,<br />
“The SecuGen engineering team<br />
has come up with a new approach to<br />
delivering world class OEM sensors.<br />
Unity BDP is not just a sensor, it is<br />
an entire development platform that<br />
is both software and hardware expandable.<br />
The uses for this product<br />
are nearly limitless, and it represents<br />
a quantum leap in OEM fingerprint<br />
technology.”<br />
Won Lee, CEO of SecuGen, said,<br />
“For many years we have focused exclusively<br />
on delivering to our OEM<br />
partners the tools they need to compete<br />
successfully in this highly competitive<br />
industry. Unity BDP is the<br />
culmination of a decade of effort. We<br />
are very proud to be able to deliver<br />
the first product of its kind, a complete<br />
biometric development platform<br />
that is compact and amazingly<br />
affordable.”<br />
About SecuGen<br />
SecuGen Corporation (www.secugen.com)<br />
is the world’s leading provider<br />
of advanced, optical fingerprint<br />
recognition technology, products,<br />
tools and platforms for physical and<br />
information security. SecuGen designs<br />
and develops FBI-certified fingerprint<br />
readers and OEM components,<br />
developer kits and software,<br />
including NIST/MINEX-compliant<br />
algorithms. Known for high quality,<br />
ruggedness, and performance in<br />
a wide variety of applications and<br />
environmental conditions, SecuGen<br />
products are used by world-leading<br />
financial, medical, government, educational<br />
and corporate institutions<br />
and are sold through an extensive<br />
partner network of reseller partners<br />
including original equipment manufacturers,<br />
independent software vendors<br />
and system integrators around<br />
the world.<br />
SecuGen is a registered trademark<br />
of SecuGen Corp. in the United<br />
States and other countries.<br />
30<br />
Viscount unveils Freedom<br />
Channel Partner Program<br />
Continued from page 27<br />
tion for superior customer service.<br />
“The Viscount Certified Channel<br />
Partner Program is a strategic initiative<br />
that more closely connects our<br />
business with a select network of systems<br />
integrators,” said Scott Sieracki,<br />
CEO of Viscount. “We are committed<br />
to providing our channel partners<br />
with unsurpassed opportunity<br />
and support as they are a critical part<br />
of our growth strategy. Viscount’s<br />
investment in technical support resources<br />
and infrastructure combined<br />
with the delivery of technologically<br />
advanced, secure access control solutions<br />
enable integrators to tap into<br />
new revenue streams, lower support<br />
costs, and improve their profit margins..”<br />
About Viscount<br />
Viscount is the leading provider of<br />
next-generation, IT-centric access<br />
control and identity management<br />
applications. Viscount’s Freedom application<br />
platform allows seamless<br />
unification of the physical and digital<br />
security worlds by replacing discrete,<br />
self-contained systems with an<br />
integrated security system that is sophisticated<br />
enough to protect today’s<br />
critical business assets, and flexible<br />
enough to keep up with the evolving<br />
IT infrastructures of government<br />
and private organizations.<br />
For more information please visit:<br />
www.viscount.com
Los Angeles chosen to welcome largest<br />
container ship ever to call in North America<br />
SAN PEDRO, Calif. — <strong>Dec</strong>. 14, <strong>2015</strong><br />
— The largest container ship ever<br />
to call at a North American port is<br />
scheduled to arrive at the Port of Los<br />
Angeles on <strong>Dec</strong>.26th. French shipping<br />
line CMA-CGM launched the<br />
CMA CGM Benjamin Franklin on<br />
<strong>Dec</strong>. 10. The vessel is scheduled to<br />
make her maiden call at APM Terminals-Pier<br />
400 at the Port of Los<br />
Angeles. The ship has a capacity of<br />
nearly 18,000 Twenty Foot Equivalent<br />
Units (TEUs), which is about<br />
a third larger than the biggest container<br />
ships that currently call at<br />
the San Pedro Bay port complex.<br />
“It’s fitting that the largest container<br />
ship to ever traverse North American<br />
waters would make its first call<br />
right here at the Port of Los Angeles,”<br />
said Mayor Eric Garcetti, who recently<br />
met with Founder and Chairman<br />
Jacques Saadé and other top<br />
CMA CGM executives. “The arrival<br />
of the CMA CGM Benjamin Franklin<br />
sends a powerful message that our<br />
port stands among the world’s greatest,<br />
and that we are prepared to continue<br />
growing and adapting to the<br />
demands of our global economy.”<br />
“As we were reminded nearly a<br />
year ago when activity at the ports<br />
along the West Coast came to a near<br />
standstill, our ports are a critical economic<br />
engine at the local, regional<br />
and national levels,” said Secretary of<br />
Labor Thomas E. Perez. “Their effective,<br />
efficient operation is necessary<br />
for 21st century global commerce,<br />
and today’s news demonstrates that<br />
the Port of LA is prepared for the<br />
next phase of modern trade. Working<br />
together, the shipping companies<br />
and port workers have enabled the<br />
port to bounce back from last year’s<br />
slowdown and show the world its capabilities.”<br />
“Together with the Board of Harbor<br />
Commissioners, we appreciate<br />
the confidence CMA-CGM has instilled<br />
in the Port of Los Angeles and<br />
the opportunities this vessel call will<br />
provide to APM Terminals, longshore<br />
labor and supply chain partners,”<br />
said Port of Los Angeles Executive<br />
Director Gene Seroka. “Earlier<br />
this year APM Terminals, longshore,<br />
and land-side logistics partners efficiently<br />
processed three 13,000 TEUs<br />
ships concurrently producing more<br />
than 38,000 container moves over<br />
an 8-day period. The arrival of the<br />
CMA-CGM Benjamin Franklin signals<br />
a new chapter in Pacific Rim<br />
trade flow and supply chain optimization.”<br />
With its world class infrastructure,<br />
skilled longshore labor, and superior<br />
conveyance network all set to<br />
efficiently handle the largest-class<br />
ships on a routine basis, the Port of<br />
31<br />
Los Angeles is uniquely capable to<br />
accommodate ULCV-class ships. It<br />
is anticipated that the CMA CGM<br />
Benjamin Franklin will return to San<br />
Pedro Bay in the first quarter of <strong>2016</strong><br />
for a call at the Port of Long Beach.<br />
CMA CGM, founded and led by<br />
Jacques R. Saadé is the world’s third<br />
largest and France’s top container<br />
shipping company. Its 470 vessels<br />
call more than 400 ports in<br />
the world, on all 5 continents.<br />
In 2014, over 12.2 million TEUs<br />
(twenty-foot equivalent units)<br />
were carried.<br />
CMA CGM has grown continuously,<br />
and has been constantly innovating<br />
to offer its clients new sea,<br />
land and logistics solutions. Present<br />
in 160 countries, with a network of<br />
655 agencies, the Group employs<br />
20,000 people worldwide, including<br />
2,400 in its headquarters in Marseilles.<br />
As North America’s leading seaport<br />
by container volume and cargo<br />
value, the Port of Los Angeles facilitated<br />
$290 billion in trade during<br />
2014. Port operations and commerce<br />
facilitate more than 148,000<br />
jobs (about one in 12) in the City<br />
of Los Angeles and 531,000 jobs (or<br />
one in 16) in the five-county Southern<br />
California region. The San Pedro<br />
Bay Ports support more than 1 million<br />
California jobs and 3.1 million<br />
nationwide.
“Working Together to Foster<br />
Safety” Speech by FAA<br />
Administrator Michael Huerta<br />
Continued from page 6<br />
FAA Administrator<br />
Michael Huerta<br />
32<br />
Up to this<br />
point, we have<br />
focused mainly<br />
on coordinating<br />
From the earliest days of flight, aviation<br />
has presented us with an everchanging<br />
slate of opportunities and<br />
challenges.<br />
For example, we are able to fly longer<br />
distances in greater safety and<br />
comfort than ever before, making<br />
almost any two points on the planet<br />
reachable in a single flight.<br />
At the same time, the worldwide<br />
security environment and ongoing<br />
regional conflicts have added new<br />
concerns that extend far beyond<br />
questions about aerodynamics and<br />
fuel calculations.<br />
As you all know, we experienced<br />
this first-hand on July 22, 2014,<br />
when a rocket from Gaza landed approximately<br />
a mile from Ben-Gurion<br />
Airport, prompting FAA to issue a<br />
Notice to Airmen that prohibited<br />
U.S. carriers from using BGA for a<br />
period of time. We viewed the suspension<br />
of flights as a temporary but<br />
necessary pause while we assured<br />
ourselves of the safety postures of<br />
both the United States and the Government<br />
of Israel.<br />
As a result of this incident, the FAA<br />
and the Civil Aviation Authority of<br />
Israel (CAAI) began an in-depth<br />
exchange that allowed the FAA and<br />
CAAI to establish new mechanisms<br />
to improve coordination. These are<br />
greatly assisting our communication<br />
and interaction on a number<br />
of fronts, and are helping us remain<br />
prepared for a range of contingencies.<br />
internal processes<br />
between<br />
the FAA and the<br />
CAAI. I hope<br />
in the future we<br />
can expand this<br />
cooperation to<br />
entail working together with U.S.<br />
and Israeli companies to find new,<br />
innovative technologies for the aviation<br />
sector.<br />
The FAA’s primary concern is the<br />
safety of civil aviation anywhere<br />
American passengers travel around<br />
the world. We constantly monitor<br />
world events and work with our international<br />
partners to take the appropriate<br />
actions with the best interests<br />
of travelers foremost in our<br />
minds. This is another common<br />
bond we share with you.<br />
When you think about it, as a sovereign<br />
nation, Israel has been around<br />
for only about 60 percent of the history<br />
of manned flight. Yet, during<br />
that time, this country has emerged<br />
on many fronts as a leader on the<br />
world aviation stage.<br />
Just in October, your flag carrier,<br />
El Al Israel Airlines, announced the<br />
largest fleet-renewal program in the<br />
airline’s history.<br />
El Al placed orders for nine new<br />
Boeing 737s and 787 Dreamliners.<br />
The airline also said it planned to<br />
lease an additional six Dreamliners<br />
and was taking options for the purchase<br />
of another 13. All told, the<br />
deal is valued at roughly $3.4 billion.<br />
Today, almost five years to the day<br />
since the U.S.–Israel Open Skies<br />
Agreement went into force, El Al is<br />
unquestionably a top-notch competitor<br />
in a region that continues to set<br />
new standards for passenger comfort<br />
and aircraft amenities.<br />
International carriers such as United<br />
Airlines have benefited from the<br />
growing demand from the tech industry.<br />
United is scheduled to begin<br />
direct service from Tel Aviv to San<br />
Francisco this coming March and<br />
Delta will also expand its direct service<br />
to New York in <strong>2016</strong>.<br />
The recent discovery of vast fields<br />
of natural gas under the Mediterranean<br />
promises even more future demand<br />
for air travel in this region.<br />
In the manufacturing arena, Israel<br />
has become an important supplier<br />
to many of the world’s leading aerospace<br />
companies. Components made<br />
in your factories are incorporated<br />
into the newest generation of modern<br />
jetliners and fighter jets. Indeed,<br />
one of the premier business jets in its<br />
class, the Gulfstream G280, was certified<br />
by the FAA in 2012 and is built<br />
by Israel Aerospace Industries, not<br />
far from where we are tonight.<br />
The Civil Aviation Authority is a<br />
valuable partner to the FAA, and we<br />
were pleased to work with the Government<br />
of Israel during its efforts in<br />
2011 to update its aviation law. Today,<br />
Israel enjoys a Category 1 safety<br />
rating – the highest possible under<br />
the FAA’s rating system. We continue<br />
to work with the CAA, both directly<br />
and through international safety<br />
committees, to address the pressing<br />
issues that face this industry.<br />
This afternoon, I visited Israel<br />
Aerospace Industries, where we engaged<br />
in constructive conversations<br />
about the strides the company has
also made in the growing field of unmanned<br />
aircraft.<br />
As you have probably seen, the<br />
subject of small, unmanned aircraft<br />
has consumed a great deal of the<br />
FAA’s time in recent months. We are<br />
working to implement regulations<br />
that will enable us to safely integrate<br />
this promising segment of aviation<br />
into the world’s busiest and most<br />
complicated airspace system.<br />
Meanwhile, the industry itself is<br />
growing at a pace unlike anything<br />
we’ve seen since the dawn of the Jet<br />
Age.<br />
We learn every day about new<br />
and creative uses for these aircraft,<br />
whether it’s to deliver packages or<br />
enable companies to accomplish<br />
tasks such as remotely monitoring<br />
miles of railroad or pipeline.<br />
At the same time, these small aircraft—we<br />
call them Unmanned<br />
Aircraft Systems, you call them Remotely<br />
Piloted Aircraft Systems, but<br />
the rest of the world knows them<br />
as drones – are becoming the latest<br />
craze among tech-savvy consumers.<br />
Retailers estimate that as many as<br />
400,000 small unmanned aircraft<br />
will be sold during the holiday season<br />
in the U.S. Most will be piloted<br />
by operators who have little or no experience<br />
in aviation.<br />
We have already had several hundred<br />
instances in the U.S. in which<br />
pilots have reported these small aircraft<br />
have come into close proximity<br />
to manned flights. Many of them<br />
have been in airspace near airports,<br />
while a number have been at altitudes<br />
ranging from 1,500 feet to as<br />
high as 10,000 feet.<br />
As you might imagine, we are<br />
working to eliminate the likelihood<br />
of an unfortunate incident or accident.<br />
We are using every method<br />
at our disposal to engage these new<br />
aviators – and they are aviators. As<br />
we do so, we value the advice and<br />
experience of our international partners<br />
here in Israel and elsewhere.<br />
We recognize that we are all embarking<br />
together into yet another new age<br />
in the constantly changing world of<br />
aviation.<br />
As regulators, airline operators and<br />
business leaders and aviators, we are<br />
constantly called upon to make flying<br />
even safer. We have achieved an<br />
amazing track record together.<br />
One of the most important factors<br />
in the worldwide aviation safety record<br />
is the free exchange of information.<br />
We realized in the late 1980s<br />
and early 1990s that the industry<br />
would need to focus on intense data<br />
analysis to detect risk and prevent<br />
accidents or incidents from occurring.<br />
The industry adopted a wide array<br />
of programs that encouraged<br />
aviation professionals–be they pilots,<br />
flight attendants, mechanics or air<br />
traffic controllers–to voluntarily report<br />
safety events without jeopardizing<br />
their careers.<br />
Airlines and government safety<br />
authorities around the world used<br />
that information to jointly develop<br />
new safety protocols. We improved<br />
not only training, but the technologies<br />
we rely on to keep us safe as we<br />
jet from place to place at almost the<br />
speed of sound.<br />
As a result, we have all but eliminated<br />
the most common causes of commercial<br />
accidents – controlled flight<br />
into terrain, weather, wind shear and<br />
failure to complete checklists. All<br />
33<br />
told, our Commercial<br />
Aviation Safety<br />
Team reduced the<br />
risk of fatalities in<br />
U.S. commercial<br />
aviation by 83 percent<br />
over 10 years.<br />
We continue to work through the<br />
world’s international safety organizations<br />
to make flying safer, no matter<br />
where the wheels touch down. The<br />
path to success depends upon the<br />
free exchange of safety information<br />
and the willingness to always look<br />
for the next improvement. We are<br />
pleased to join you on this journey.<br />
Many people outside our industry<br />
probably aren’t aware of it, but some<br />
of the most valuable lessons about<br />
flying were learned in this part of<br />
the world. Antoine de St. Exupery,<br />
known to many as the author of the<br />
children’s book, “The Little Prince,”<br />
was actually a pioneering aviator<br />
who spent much of his time flying<br />
the airmail throughout the Middle<br />
East.<br />
He wrote an award-winning book,<br />
“Wind, Sand and Stars” in 1939, inspired<br />
by a plane crash that almost<br />
claimed the lives of St. Exupery and<br />
his navigator.<br />
St. Exupery offered several observations<br />
about flying under trying<br />
conditions. Back then, he was in<br />
open-cockpit biplanes. Most often,<br />
those flights occurred at night. Navigation<br />
was best accomplished by following<br />
the stars. As anyone who has<br />
spent any time in the desert knows,<br />
a sand dune in a sea of sand dunes<br />
makes a poor reference point.<br />
He writes about the loneliness of<br />
the desert and the importance of<br />
More on page 34
“Working Together to Foster Safety”<br />
Continued from page 33<br />
friendship and of gaining new perspectives.<br />
One of the more inspirational<br />
passages of the book includes<br />
this line: “The airplane has unveiled<br />
for us the true face of the earth.”<br />
I think that’s something on which<br />
we can all agree. These machines in<br />
which we fly from place to place to<br />
make money, to visit relatives or to<br />
see the wonders of the world, truly<br />
do force us to look beyond ourselves<br />
and our immediate surroundings.<br />
As we have seen in recent weeks,<br />
no place in the world is immune<br />
from acts of terrorism. Whether it’s<br />
Paris, Baghdad, Nigeria, Colorado<br />
Springs, San Bernardino, Jerusalem<br />
or Tel Aviv, hardly a day goes by<br />
without some sort of senseless violence.<br />
It is up to the people in this room –<br />
and across the international aviation<br />
industry –to take steps to guarantee<br />
our air transportation system is robust<br />
and reliable, no matter what lies<br />
over the horizon.<br />
As I close, it occurs to me that<br />
the mission statement of the Peres<br />
Center for Peace—to “promote lasting<br />
peace and advancement in the<br />
Middle East by fostering tolerance,<br />
economic and technological development,<br />
innovation, cooperation<br />
and well-being”—is one that could<br />
apply across all borders and cultures.<br />
I mentioned earlier that the U.S.<br />
and Israel are tied together by aviation.<br />
The world is tied together by<br />
aviation. Because of this, we are all<br />
neighbors, separated only by time<br />
and distance.<br />
Coalition urges Supreme Court to<br />
reverse Texas v. U.S.<br />
Continued from page 16<br />
citizen and lawful permanent resident<br />
children, family members,<br />
employers, employees and other<br />
community members. The groups<br />
explain that the sweeping injunction<br />
upheld in the lower court directly<br />
harms individuals who have<br />
either been in the U.S. since they<br />
were children or are the parents of<br />
U.S. citizens or lawful permanent<br />
residents.<br />
“The individuals profiled in the<br />
brief illustrate the havoc this case<br />
has wreaked on the lives of millions<br />
of immigrants who remain in legal<br />
limbo,” added Benjamin Johnson,<br />
Executive Director of the American<br />
Immigration Council. “We urge the<br />
U.S. Supreme Court to take up this<br />
case and give hard working immigrant<br />
families the chance to live and<br />
work without fear of deportation.”<br />
The immigration programs, which<br />
were announced by the President last<br />
November, would expand eligibility<br />
for the existing Deferred Action for<br />
Childhood Arrivals (DACA) program<br />
and expand protections for<br />
parents of U.S. citizens and lawful<br />
permanent residents through a program<br />
known as Deferred Action for<br />
Parents of Americans (DAPA). Together,<br />
the programs would allow<br />
34<br />
millions of undocumented individuals<br />
to remain in the United States<br />
without fear of deportation and apply<br />
for work authorization permits<br />
for a period of three years, with the<br />
possibility of renewal.<br />
“The DAPA and expanded DACA<br />
policies will help ensure that families<br />
are not needlessly separated and<br />
that immigrant workers can speak<br />
up for basic safety and fairness on<br />
the job without facing retaliation,”<br />
said Tefere Gebre, Executive Vice<br />
President of the AFL-CIO. “We<br />
urge the Supreme Court to take up<br />
this case right away.”<br />
• Click here to see the full legal<br />
brief.<br />
• Click here for more background<br />
on the legal challenges to executive<br />
action on immigration.<br />
• Click here to see an interactive<br />
timeline outlining the process for<br />
review of the case by the Supreme<br />
Court.
National Science Foundation announces<br />
“CRISP” awards program<br />
Continued from page 9<br />
portation services. Social networks,<br />
interactions, and policies can enable<br />
or hinder the successful creation of<br />
resilient complex adaptive systems.<br />
The goals of the Critical Resilient<br />
Interdependent Infrastructure<br />
Systems and Processes<br />
(CRISP) solicitation<br />
are to: (1) foster<br />
an interdisciplinary<br />
research community<br />
of engineers, computer<br />
and computational<br />
scientists and social and<br />
behavioral scientists, that<br />
creates new approaches and engineering<br />
solutions for the design<br />
and operation of infrastructures as<br />
processes and services; (2) enhance<br />
the understanding and design of<br />
interdependent critical infrastructure<br />
systems (ICIs) and processes<br />
that provide essential goods and<br />
services despite disruptions and<br />
failures from any cause, natural,<br />
technological, or malicious; (3) create<br />
the knowledge for innovation<br />
in ICIs so that they safely, securely,<br />
and effectively expand the range of<br />
goods and services they enable; and<br />
(4) improve the effectiveness and<br />
efficiency with which they deliver<br />
existing goods and services. These<br />
goals lead to the following specific<br />
objectives for this solicitation:<br />
• To create new knowledge, approaches,<br />
and engineering solutions<br />
to increase resilience, performance,<br />
and readiness in ICIs.<br />
• To create theoretical frameworks<br />
and multidisciplinary models<br />
of ICIs, processes and services,<br />
capable of analytical prediction of<br />
complex behaviors, in response to<br />
system and policy changes.<br />
• To develop frameworks<br />
to understand interdependencies<br />
created<br />
by the interactions<br />
between the physical,<br />
the cyber (computing,<br />
information, computational,<br />
sensing and communication),<br />
and social,<br />
behavioral and economic elements<br />
of ICIs. These could include, but<br />
are not limited to, software frameworks<br />
for modeling and simulation<br />
using advanced cyber infrastructures,<br />
management, monitoring and<br />
real-time control of interdependent<br />
ICIs and novel software engineering<br />
methodologies.<br />
• To study socioeconomic, political,<br />
legal and psychological obstacles<br />
to improving ICIs and identifying<br />
strategies for overcoming those<br />
obstacles.<br />
The CRISP solicitation seeks to<br />
fund projects likely to produce new<br />
knowledge that can contribute to<br />
making ICI services more effective,<br />
efficient, dependable, adaptable,<br />
35<br />
resilient, safe, and secure, taking<br />
into account the human systems in<br />
which they are embedded. Successful<br />
proposals are expected to study<br />
multiple infrastructures focusing<br />
on them as interdependent systems<br />
that deliver services, enabling a new<br />
interdisciplinary paradigm in infrastructure<br />
research. To meet the<br />
interdisciplinary criterion, proposals<br />
must broadly integrate across<br />
engineering, computer, information<br />
and computational science, and the<br />
social, behavioral and economic sciences.<br />
Proposals that do not meet<br />
this criterion will be returned<br />
without review. Projects supported<br />
under this solicitation may undertake<br />
the collection of new data or<br />
use existing curated data depending<br />
on the category of award, and must<br />
recognize that a primary objective<br />
is integrative, predictive modeling<br />
that can use the data to validate the<br />
models and that can be integrated<br />
into decision making.”<br />
INFORMATION WEBCAST:<br />
The NSF will hold an informational<br />
webcast on Friday, <strong>Jan</strong>uary<br />
22, <strong>2015</strong> at 1:30pm to discuss the<br />
CRISP program and answer questions<br />
about this solicitation. More<br />
details about the webcast will be<br />
posted on the CMMI website, http://<br />
www.nsf.gov/eng/cmmi, as they become<br />
available.
Texas Observer: corruption,<br />
insufficient oversight at CBP<br />
Continued from page 15<br />
36<br />
Trump’s Muslim immigration<br />
policy<br />
Continued from page 14<br />
Finally, putting the history lesson<br />
and legal questions aside, is this truly<br />
the path the U.S. public would want<br />
to see the country take? A public that,<br />
by and large, prides itself on being a<br />
nation of immigrants, built on diversity,<br />
religious tolerance, and equality?<br />
Rabbi Jack Moline, executive director<br />
of Interfaith Alliance, articulated<br />
what is most likely on the minds of<br />
millions of Americans as they consider<br />
Trump’s latest proposal, “Rooting<br />
our nation’s immigration policy in<br />
religious bigotry and discrimination<br />
will not make America great again.”<br />
Trump’s latest immigration policy<br />
proposal is nothing more than political<br />
showmanship that harkens back<br />
to some of the darker days in our nation’s<br />
history and feeds the fear mongers<br />
among us. How can anyone believe<br />
this is the way to move a country<br />
forward?<br />
See more at: http://immigrationimpact.com/<strong>2015</strong>/12/08/<br />
trumps-muslim-immigration-policy-unconstitutional-and-unworthyof-america/#sthash.VuPsV3r1.dpuf<br />
der for money.”<br />
But, while such anecdotes of corruption<br />
abound, “Homeland Security<br />
officials have no way to gauge<br />
how extensive the problem is within<br />
its ranks.” In a 2014 report, a Homeland<br />
Security advisory panel of lawenforcement<br />
officials concluded that<br />
“the true levels of corruption within<br />
CBP are not known.” According to<br />
the Texas Observer, this state of affairs<br />
has existed since the creation of<br />
DHS, which “gave rise to a complex<br />
web of internal affairs bodies, with<br />
overlapping jurisdictions, conflicting<br />
interests and chronic funding shortages.”<br />
In fact, within DHS:<br />
“Each agency has its own protocols,<br />
case numbers and filing systems, its<br />
own sense of institutional pride, and<br />
its own acronyms. The FBI, DHS OIG<br />
[DHS Office of the Inspector General],<br />
ICE OPR (Immigration and Customs<br />
Enforcement Office of Public<br />
Responsibility) and CBP IA [CBP Internal<br />
Affairs] all run their own competing<br />
investigations—even though,<br />
with the exception of the FBI, they’re<br />
all part of the Department of Homeland<br />
Security.”<br />
Yet, somehow, CBP “was left without<br />
its own internal affairs investigators,”<br />
despite being the largest lawenforcement<br />
agency in the country.<br />
Rather, CBP is supposed to be policed<br />
by DHS OIG, which has around 200<br />
investigators who are supposed to<br />
monitor more than 220,000 people.<br />
In comparison, “the FBI has 250 internal<br />
affairs investigators for its<br />
13,000 agents.” With so few investigators<br />
keeping track of so many CBP<br />
personnel, it is no wonder that corruption<br />
appears to be flourishing on<br />
the border.<br />
It’s important to remember that<br />
the lack of accountability which fosters<br />
corruption also creates an atmosphere<br />
of impunity surrounding the<br />
use—and abuse—of power, including<br />
the use of deadly force. According<br />
to an October <strong>2015</strong> Los Angeles<br />
Times investigation, from 2010 to<br />
2013, Border Patrol agents fired their<br />
Tasers 70 times “at people who were<br />
running away, even though there was<br />
no struggle or clear indication that<br />
agents were in danger.” In six instances,<br />
agents used Tasers against “people<br />
who were trying to climb over the<br />
border fence back into Mexico.” Three<br />
people died after being hit by Taser<br />
fire. Two people were shocked while<br />
handcuffed.<br />
Not surprisingly given the lack of<br />
oversight and accountability, Border<br />
Patrol agents are rarely called to account<br />
for their actions. According to<br />
the American Immigration Council,<br />
among the 485 abuse complaints<br />
made against the agency between <strong>Jan</strong>uary<br />
2009 and <strong>Jan</strong>uary 2012 in which<br />
a formal decision was made, “No Action<br />
Taken” represented 97 percent<br />
of all outcomes. Whether or not this<br />
degree of lax oversight also applies<br />
to instances of corruption is not yet<br />
known.<br />
Ultimately, weeding out corruption<br />
(and abuse) from DHS as a whole and<br />
CBP in particular is a responsibility<br />
that rests with Congress. Unfortunately,<br />
jurisdiction of DHS has been<br />
divvied up among “at least 120 congressional<br />
committees, subcommittees<br />
and task forces.” With Congressional<br />
oversight as disjointed as DHS<br />
itself, it is a safe bet that reform will<br />
not come easy.<br />
See more at: http://immigrationimpact.<br />
com/<strong>2015</strong>/12/10/corruption-flourishes-within-cbp/#sthash.6sf0UcZ8.dpuf
<strong>GSN</strong> <strong>2016</strong> Editorial Calendar<br />
MONTH TECHNOLOGY FOCUS MARKET SECTOR FOCUS GUEST CONTRIBUTOR BONUS DISTRIBUTION<br />
<strong>Jan</strong>uary Print<br />
Orders <strong>Dec</strong> 17<br />
Materials <strong>Dec</strong> 21<br />
Access Control/Govt/<br />
Biometric ID<br />
Airport/Aviation<br />
Security<br />
Cybersecurity<br />
Guest Expert<br />
Fencetech<br />
February <strong>Digital</strong><br />
Orders <strong>Jan</strong> 18<br />
Materials - <strong>Jan</strong> 22<br />
Perimeter Protection/<br />
Intrusion Detection<br />
Oil/Gas/Electric Grid<br />
Monitoring<br />
Educational<br />
Opportunities<br />
RSA February<br />
March Print<br />
Orders Feb 18<br />
Materials Feb 22<br />
CBRNE/Detection<br />
Border Security/<br />
Immigration<br />
Video Surveillance<br />
Guest Expert<br />
ISC West/<br />
Border Security Expo<br />
April <strong>Digital</strong><br />
Orders Mar 18<br />
Materials Mar 21<br />
Video Surveilance/<br />
Management<br />
Maritime/Coastal/<br />
Port Security<br />
Cybersecurity<br />
Guest Expert<br />
May Print<br />
Orders Apr 19<br />
Materials Mar 21<br />
Satellite<br />
Communications<br />
Law Enforcement/<br />
Public Safety<br />
Educational<br />
Opportunities<br />
June <strong>Digital</strong><br />
Orders May 17<br />
Materials May 21<br />
Disaster Prep and<br />
Response<br />
City/State/County<br />
Municipal Security<br />
Cybersecurity<br />
Guest Expert<br />
July Print<br />
Orders Jun 17<br />
Materials June 20<br />
Perimeter Protection/<br />
Intrusion Detection<br />
Airport/Aviation<br />
Security<br />
Facility Security<br />
Guest Expert<br />
Transportation Security<br />
Expert<br />
August <strong>Digital</strong><br />
Orders Jul 18<br />
Materials Jul 22<br />
Access Control/Govt/<br />
Biometric ID<br />
Border Security/<br />
Immigration<br />
Educational<br />
Opportunities<br />
U.S. Canada Border<br />
Security Expo<br />
September Print<br />
Orders Aug 16<br />
Materials Aug 22<br />
School Safety Mobile<br />
and Surveillance<br />
Solutions<br />
Maritime/Coastal/<br />
Port Security<br />
Cybersecurity<br />
Guest Expert<br />
ASIS Conference<br />
October <strong>Digital</strong><br />
Orders Sep 16<br />
Materials Sep 19<br />
International Threat/<br />
Cyber Intelligence<br />
Oil/Gas/Electric Grid<br />
Security<br />
Expert on Govt Data<br />
Security<br />
November Print<br />
Orders Oct 17<br />
Materials Oct 21<br />
Perimeter Protection/<br />
Intrusion Detection<br />
Mass Notification/<br />
Disaster Response<br />
Educational<br />
Opportunities<br />
<strong>Dec</strong>ember <strong>Digital</strong><br />
Orders Nov 18<br />
Materials Nov 21<br />
Year End Roundup of<br />
New Technologies<br />
<strong>2016</strong> Yearbook of H.S.<br />
Awards Winners<br />
37<br />
Guest Cyber Expert<br />
The News Leader in Physical, IT and Homeland Security • www.gsnmagazine.com
Coming Attractions – <strong>2016</strong><br />
<strong>Jan</strong>uary Print<br />
Technology Focus:<br />
Access Control/Govt<br />
& Biometric ID<br />
Market Focus:<br />
Airport/Aviation<br />
Aviation Security<br />
Plus<br />
Guest Cyber Expert<br />
February <strong>Digital</strong><br />
Technology Focus:<br />
Perimeter Protection<br />
Intrusion Detection<br />
Market Focus:<br />
Oil/Gas/Utility<br />
Monitoring<br />
Plus<br />
Education Profile<br />
April <strong>Digital</strong><br />
Technology Focus:<br />
Video Surveillance<br />
Market Focus:<br />
Maritime/Coastal<br />
Port Security<br />
Plus<br />
Guest Cyber Expert<br />
May Print<br />
Technology Focus:<br />
Satellite Communications<br />
Market Focus:<br />
Law Enforcement/<br />
Public Safety<br />
Plus Education Profile<br />
June <strong>Digital</strong><br />
Technology Focus:<br />
Disaster Preparation<br />
And Response<br />
Market Focus:<br />
City/State/County/<br />
Municipal Security<br />
Plus<br />
Guest Cyber Expert<br />
July Print <strong>Edition</strong><br />
Technology Focus:<br />
Perimeter Protection/<br />
Intrusion Detection<br />
Market Focus:<br />
Airport/Aviation<br />
Security<br />
Plus<br />
Facility Security Expert<br />
March Print<br />
Technology Focus:<br />
CBRNE/Detection<br />
Market Focus:<br />
Border Security/<br />
Immigration<br />
Plus<br />
Video Surveillance<br />
Guest Expert<br />
For <strong>GSN</strong> Media Kit or Advertising Rates,<br />
contact Publisher Mike Madsen<br />
at 732-233-8119<br />
or by email at<br />
mmadsen@gsnmagazine.com<br />
38
The News Leader in Physical, IT and Homeland Security<br />
CEO/Editorial Director:<br />
Adrian Courtenay<br />
(O) 212-344-0759, X3<br />
(C) 917-696-5782<br />
acourtenay@gsnmagazine.com<br />
Publisher:<br />
Michael Madsen<br />
(O) 212-344-0759, X1<br />
(C) 732-233-8119<br />
mmadsen@gsnmagazine.com<br />
Senior Writer:<br />
Steve Bittenbender<br />
(C) 502-552-1450<br />
sbittenbender@gsnmagazine.com<br />
Senior Writer:<br />
Karen Ferrick-Roman<br />
(C) 412-671-1456<br />
karenferrickroman@gmail.com<br />
Columnist:<br />
John Convy<br />
Convy on Netcentric Security<br />
john@convyassociates.com<br />
Columnist:<br />
Shawn Campbell<br />
shawncampbell@safenetat.com<br />
Guest Expert Contributor:<br />
Denise Rucker Krepp<br />
(C) 202-546-2533<br />
kdrkrepp@hotmail.com<br />
Art Director:<br />
Gerry O’Hara<br />
OHDesign3<br />
(C) 203-249-0626<br />
gerry@ohd3.com<br />
Production Director:<br />
Tammy Waitt<br />
(O) 732-233-0245<br />
twaitt@gsnmagazine.com<br />
Mailing Address:<br />
Government Security News<br />
P.O. Box 7608<br />
Greenwich, CT 06836<br />
Government Security News (ISSN 1548-940X and UPS 022-845) is published in six print editions (<strong>Jan</strong>, Mar, May, Jul, Sep, Nov) and<br />
six digital editions (Feb, Apr, Jun, Aug, Oct, <strong>Dec</strong>) per year by World Business Media, LLC, P.O. Box 7608, Greenwich, CT 06836.<br />
Telephone (212) 344-0759. Periodicals postage paid at New York, NY and additional mailing offices. POSTMASTER: Send address<br />
changes to <strong>GSN</strong>: Government Security News, Subscription Department, P.O. Box 316, Congers, NY 10920-0316. For Government<br />
decision makers and business executives involved with security products, systems and series. Qualified U.S. subscribers received<br />
<strong>GSN</strong>: Government Security News at no charge. Non-qualified subscribers in the U.S. are charged $75.00 per year. Canadian and<br />
foreign subscribers are charged $140 International Airmail. Copyright <strong>2015</strong> by <strong>GSN</strong>: Government Security News. All rights reserved.<br />
Printed in the U.S.A. <strong>GSN</strong>: Government Security News assumes resonsibility for validity of claims in items reported.<br />
39
Secure access<br />
to cloud, data<br />
and door<br />
Go beyond simple passwords. Protect your<br />
organisation with cost-effective, risk appropriate<br />
Identity Assurance Solutions from HID Global.<br />
With the ever increasing risk from advanced IT security threats, organisations are looking to take authentication<br />
beyond passwords, while lowering cost at the same time. HID Global’s authentication solution provides you<br />
with the convenience, flexibility and comprehensive control you need to deliver secure access, without<br />
compromising on security. HID Global can empower your employee’s, partners and customers with anytime,<br />
anywhere access to enterprise cloud applications, data and the door.<br />
Experience authentication beyond passwords. hidglobal.com<br />
© <strong>2015</strong> HID Global Corporation/ASSA ABLOY AB. All rights reserved. HID, HID Global, the HID Blue Brick logo, and the Chain Design are trademarks or registered trademarks of HID Global or its<br />
licensor(s)/supplier(s) in the US and other countries and may not be used without permission.<br />
ActivID-Enterprise-<strong>GSN</strong>.indd 1<br />
1/6/15 4:32 PM