dissection of a Cyber- Espionage attack
cct-w08_evolving-threats-dissection-of-a-cyber-espionage-attack
cct-w08_evolving-threats-dissection-of-a-cyber-espionage-attack
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
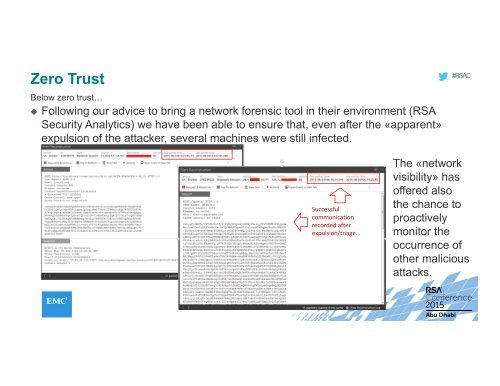
Zero Trust<br />
Below zero trust…<br />
Following our advice to bring a network forensic tool in their environment (RSA<br />
Security Analytics) we have been able to ensure that, even after the «apparent»<br />
expulsion <strong>of</strong> the <strong>attack</strong>er, several machines were still infected.<br />
#RSAC<br />
Successful<br />
communication<br />
recorded after<br />
expulsion/triage…<br />
The «network<br />
visibility» has<br />
<strong>of</strong>fered also<br />
the chance to<br />
proactively<br />
monitor the<br />
occurrence <strong>of</strong><br />
other malicious<br />
<strong>attack</strong>s.