dissection of a Cyber- Espionage attack
cct-w08_evolving-threats-dissection-of-a-cyber-espionage-attack
cct-w08_evolving-threats-dissection-of-a-cyber-espionage-attack
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
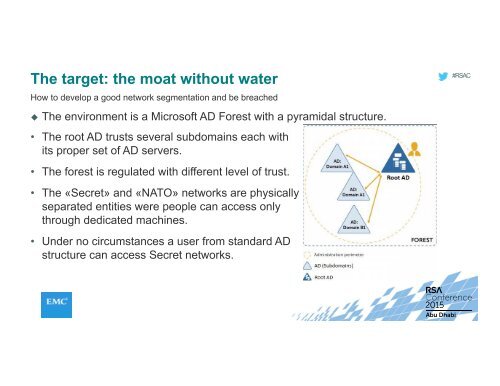
The target: the moat without water<br />
How to develop a good network segmentation and be breached<br />
The environment is a Micros<strong>of</strong>t AD Forest with a pyramidal structure.<br />
#RSAC<br />
• The root AD trusts several subdomains each with<br />
its proper set <strong>of</strong> AD servers.<br />
• The forest is regulated with different level <strong>of</strong> trust.<br />
• The «Secret» and «NATO» networks are physically<br />
separated entities were people can access only<br />
through dedicated machines.<br />
• Under no circumstances a user from standard AD<br />
structure can access Secret networks.