GSN February Digital Edition
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
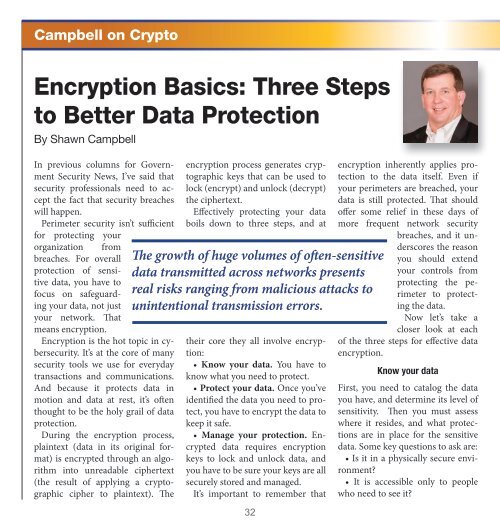
Campbell on Crypto<br />
Encryption Basics: Three Steps<br />
to Better Data Protection<br />
By Shawn Campbell<br />
In previous columns for Government<br />
Security News, I’ve said that<br />
security professionals need to accept<br />
the fact that security breaches<br />
will happen.<br />
Perimeter security isn’t sufficient<br />
for protecting your<br />
organization from<br />
breaches. For overall<br />
protection of sensitive<br />
data, you have to<br />
focus on safeguarding<br />
your data, not just<br />
your network. That<br />
means encryption.<br />
Encryption is the hot topic in cybersecurity.<br />
It’s at the core of many<br />
security tools we use for everyday<br />
transactions and communications.<br />
And because it protects data in<br />
motion and data at rest, it’s often<br />
thought to be the holy grail of data<br />
protection.<br />
During the encryption process,<br />
plaintext (data in its original format)<br />
is encrypted through an algorithm<br />
into unreadable ciphertext<br />
(the result of applying a cryptographic<br />
cipher to plaintext). The<br />
encryption process generates cryptographic<br />
keys that can be used to<br />
lock (encrypt) and unlock (decrypt)<br />
the ciphertext.<br />
Effectively protecting your data<br />
boils down to three steps, and at<br />
The growth of huge volumes of often-sensitive<br />
data transmitted across networks presents<br />
real risks ranging from malicious attacks to<br />
unintentional transmission errors.<br />
their core they all involve encryption:<br />
• Know your data. You have to<br />
know what you need to protect.<br />
• Protect your data. Once you’ve<br />
identified the data you need to protect,<br />
you have to encrypt the data to<br />
keep it safe.<br />
• Manage your protection. Encrypted<br />
data requires encryption<br />
keys to lock and unlock data, and<br />
you have to be sure your keys are all<br />
securely stored and managed.<br />
It’s important to remember that<br />
32<br />
encryption inherently applies protection<br />
to the data itself. Even if<br />
your perimeters are breached, your<br />
data is still protected. That should<br />
offer some relief in these days of<br />
more frequent network security<br />
breaches, and it underscores<br />
the reason<br />
you should extend<br />
your controls from<br />
protecting the perimeter<br />
to protecting<br />
the data.<br />
Now let’s take a<br />
closer look at each<br />
of the three steps for effective data<br />
encryption.<br />
Know your data<br />
First, you need to catalog the data<br />
you have, and determine its level of<br />
sensitivity. Then you must assess<br />
where it resides, and what protections<br />
are in place for the sensitive<br />
data. Some key questions to ask are:<br />
• Is it in a physically secure environment?<br />
• It is accessible only to people<br />
who need to see it?