You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
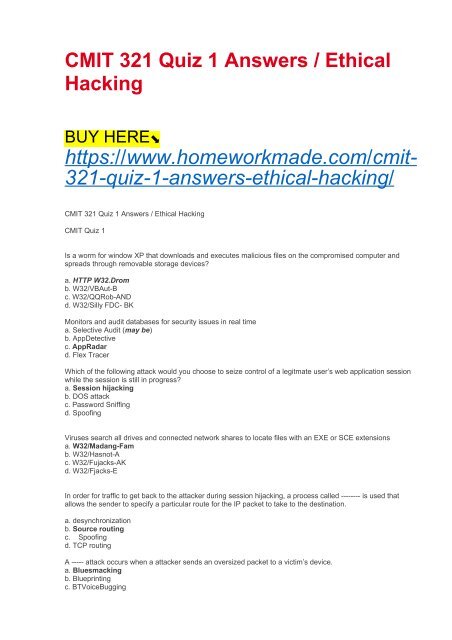
<strong>CMIT</strong> <strong>321</strong> <strong>Quiz</strong> 1 <strong>Answers</strong> / <strong>Ethical</strong><br />
<strong>Hacking</strong><br />
BUY HERE⬊<br />
https://www.homeworkmade.com/cmit-<br />
<strong>321</strong>-quiz-1-answers-ethical-hacking/<br />
<strong>CMIT</strong> <strong>321</strong> <strong>Quiz</strong> 1 <strong>Answers</strong> / <strong>Ethical</strong> <strong>Hacking</strong><br />
<strong>CMIT</strong> <strong>Quiz</strong> 1<br />
Is a worm for window XP that downloads and executes malicious files on the compromised computer and<br />
spreads through removable storage devices?<br />
a. HTTP W32.Drom<br />
b. W32/VBAut-B<br />
c. W32/QQRob-AND<br />
d. W32/Silly FDC- BK<br />
Monitors and audit databases for security issues in real time<br />
a. Selective Audit (may be)<br />
b. AppDetective<br />
c. AppRadar<br />
d. Flex Tracer<br />
Which of the following attack would you choose to seize control of a legitmate user’s web application session<br />
while the session is still in progress?<br />
a. Session hijacking<br />
b. DOS attack<br />
c. Password Sniffing<br />
d. Spoofing<br />
Viruses search all drives and connected network shares to locate files with an EXE or SCE extensions<br />
a. W32/Madang-Fam<br />
b. W32/Hasnot-A<br />
c. W32/Fujacks-AK<br />
d. W32/Fjacks-E<br />
In order for traffic to get back to the attacker during session hijacking, a process called -------- is used that<br />
allows the sender to specify a particular route for the IP packet to take to the destination.<br />
a. desynchronization<br />
b. Source routing<br />
c. Spoofing<br />
d. TCP routing<br />
A ----- attack occurs when a attacker sends an oversized packet to a victim’s device.<br />
a. Bluesmacking<br />
b. Blueprinting<br />
c. BTVoiceBugging
d. Bluesnarfing<br />
---- can monitor a simple mail transfer protocol (SMTP) server regularly after connecting to it.<br />
a. CheckOk<br />
b. SMTPCheck<br />
c. SMTPmom<br />
d. SLCheck<br />
Which of the following definitions best describes a wrapper?<br />
a. A wrapper is a packet-crafting techniques used to perform stealthy port scans.<br />
b. A wrapper is an encryption tool used to hide messages inside image files<br />
c. A wrapper is a method of hiding a virus inside an executable file<br />
d. A wrapper is a tool used to bind a Trojan to a legitimate file.<br />
------ hijacking is a hacking technique that uses spoofed packets to take over a connection between a victim<br />
and a target machine.<br />
a. ACK<br />
b. Blind<br />
c. TCP/IP<br />
d. Network-level<br />
Which of the following is not a Microsoft Internet information services vulnerability<br />
a. ::$Data vulmerability<br />
b. UFS integer overflow vulnerability<br />
c. Showcode.asp vulnerability<br />
d. WebDAV/R PC exploits<br />
The ----- scripts allows a remote user to view the code of server-side scripts.<br />
a. Showlogin.asp<br />
b. Showcode.asp<br />
c. RemoteAccess.asp<br />
d. Remotelogin.asp<br />
----- is acomand-line tool that is bundled with both windows and UNIX operating systems and is used to<br />
querying DNS information<br />
a. Whois<br />
b. Traceroute<br />
c. Netstat<br />
d. NsLookup<br />
Which type of information cannot be found ina resource record (RR)?<br />
a. MX<br />
b. ARP<br />
c. PTR<br />
d. SOA<br />
---- is a network scanning technique used to discover which range of IP address map to live computers<br />
a. Port scanning<br />
b. Ping Sweep<br />
c. Probe scanning<br />
d. Fingerprinting<br />
An attacker is interested in dscovering ports that might be open on a target system. The attacker decides to<br />
port scan the IP address of the system but also wants to make the scan as stealthy as possible. Which of the<br />
following techniques would be the best choice in this scenario?<br />
a. TCP connect scan<br />
b. SYN scan<br />
c. ICMP echo scan<br />
d. List scan<br />
During the reconnaissance phase of an attack, the attacker may resort to looking though an organization;s<br />
trash for discarded sensitive information. This technique is known as<br />
a. social engineering
. breaking and entering<br />
c. dumpster diving<br />
d. passive reconnaissance<br />
Which of the following are objectives of scanning (select all that apply)<br />
All<br />
The simple service discovery protocol will (choose 3)<br />
a. Not work behind a firewall<br />
b. Can be vulnerable to denial of service<br />
c. Uses multicast addresses<br />
d. Controls communication for the universal plug and play service<br />
Which port scanning method is considered the most reliable in terms of accurately reporting port status on a<br />
target system?<br />
a. TCP connect () scan<br />
b. SYN Scan<br />
c. ACK scan<br />
d. Xma Scan<br />
The following tools are used for foot printing (choose 3)<br />
a. Recong-ng<br />
b. Aircrack-ng<br />
c. Maltego<br />
d. FOCA<br />
---- is a spoofing technique that allows an attacker to choose the path a packet will take through the internet<br />
a. SYN Scanning<br />
b. Source Routing<br />
c. Tracerouting<br />
d. Http tunneling<br />
If you want to mask (or spoof your IP address, use this tyoe if scan)<br />
a. IDLE, IPID scan<br />
b. UDP Scan<br />
c. ACK Flag Probe Scan<br />
d. Stealth Scan