HIPAA Guard Herald - Your Monthly Newsletter on Surviving HIPAA
HIPAA Guard Newsletter Issue 07 June 2018
HIPAA Guard Newsletter Issue 07 June 2018
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
<str<strong>on</strong>g>HIPAA</str<strong>on</strong>g> <str<strong>on</strong>g>Guard</str<strong>on</strong>g> HERALD<br />
YOUR MONTHLY NEWSLETTER ON SURVIVING <str<strong>on</strong>g>HIPAA</str<strong>on</strong>g><br />
ISSUE 07 June 2018<br />
LATEST ON <str<strong>on</strong>g>HIPAA</str<strong>on</strong>g><br />
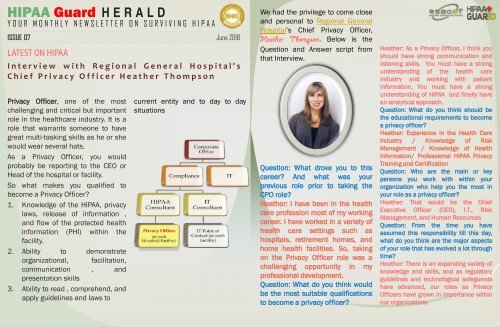
Interview with Regi<strong>on</strong>al General Hospital's<br />
Chief Privacy Officer Heather Thomps<strong>on</strong><br />
Privacy Officer, <strong>on</strong>e of the most<br />
challenging and critical but important<br />
role in the healthcare industry. It is a<br />
role that warrants some<strong>on</strong>e to have<br />
great multi-tasking skills as he or she<br />
would wear several hats.<br />
As a Privacy Officer, you would<br />
probably be reporting to the CEO or<br />
Head of the hospital or facility.<br />
So what makes you qualified to<br />
become a Privacy Officer?<br />
1. Knowledge of the <str<strong>on</strong>g>HIPAA</str<strong>on</strong>g>, privacy<br />
laws, release of informati<strong>on</strong> ,<br />
and flow of the protected health<br />
informati<strong>on</strong> (PHI) within the<br />
facility.<br />
2. Ability to dem<strong>on</strong>strate<br />
organizati<strong>on</strong>al, facilitati<strong>on</strong>,<br />
communicati<strong>on</strong> , and<br />
presentati<strong>on</strong> skills<br />
3. Ability to read , comprehend, and<br />
apply guidelines and laws to<br />
current entity and to day to day<br />
situati<strong>on</strong>s<br />
We had the privilege to come close<br />
and pers<strong>on</strong>al to Regi<strong>on</strong>al General<br />
Hospital’s Chief Privacy Officer,<br />
Heather Thomps<strong>on</strong>. Below is the<br />
Questi<strong>on</strong> and Answer script from<br />
that Interview.<br />
Questi<strong>on</strong>: What drove you to this<br />
career? And what was your<br />
previous role prior to taking the<br />
CPO role?<br />
Heather: I have been in the health<br />
care professi<strong>on</strong> most of my working<br />
career. I have worked in a variety of<br />
health care settings such as<br />
hospitals, retirement homes, and<br />
home health facilities. So, taking<br />
<strong>on</strong> the Privacy Officer role was a<br />
challenging opportunity in my<br />
professi<strong>on</strong>al development.<br />
Questi<strong>on</strong>: What do you think would<br />
be the most suitable qualificati<strong>on</strong>s<br />
to become a privacy officer?<br />
Heather: As a Privacy Officer, I think you<br />
should have str<strong>on</strong>g communicati<strong>on</strong> and<br />
listening skills. You must have a str<strong>on</strong>g<br />
understanding of the health care<br />
industry and working with patient<br />
informati<strong>on</strong>. You must have a str<strong>on</strong>g<br />
understanding of <str<strong>on</strong>g>HIPAA</str<strong>on</strong>g> and finally have<br />
an analytical approach.<br />
Questi<strong>on</strong>: What do you think should be<br />
the educati<strong>on</strong>al requirements to become<br />
a privacy officer?<br />
Heather: Experience in the Health Care<br />
Industry / Knowledge of Risk<br />
Management / Knowledge of Health<br />
Informati<strong>on</strong>/ Professi<strong>on</strong>al <str<strong>on</strong>g>HIPAA</str<strong>on</strong>g> Privacy<br />
Training and Certificati<strong>on</strong><br />
Questi<strong>on</strong>: Who are the main or key<br />
pers<strong>on</strong>s you work with within your<br />
organizati<strong>on</strong> who help you the most in<br />
your role as a privacy officer?<br />
Heather: That would be the Chief<br />
Executive Officer (CEO), I.T., Risk<br />
Management, and Human Resources<br />
Questi<strong>on</strong>: From the time you have<br />
assumed this resp<strong>on</strong>sibility till this day,<br />
what do you think are the major aspects<br />
of your role that has evolved a lot through<br />
time?<br />
Heather: There is an expanding variety of<br />
knowledge and skills, and as regulatory<br />
guidelines and technological safeguards<br />
have advanced, our roles as Privacy<br />
Officers have grown in importance within<br />
our organizati<strong>on</strong>s.
MORE ON <str<strong>on</strong>g>HIPAA</str<strong>on</strong>g> <str<strong>on</strong>g>Guard</str<strong>on</strong>g> H E R A L D<br />
Interview with<br />
Regi<strong>on</strong>al General Hospital's<br />
Chief Privacy Officer<br />
Heather Thomps<strong>on</strong><br />
Questi<strong>on</strong>: What do you think is<br />
the most difficult part of your<br />
role? How are you able to<br />
overcome this difficulty and be<br />
successful in performing it?<br />
Heather: Adapting to the<br />
changing of laws and of course<br />
the ever-changing advance in<br />
technology. I adapt by c<strong>on</strong>tinuing<br />
to educate myself and having the<br />
willingness to adapt to all the<br />
changes that may come. Also, by<br />
accepting and learning from all<br />
the challenges that come my<br />
way.<br />
Questi<strong>on</strong>: For the future Privacy<br />
officers out there or those who<br />
wish to traverse this career path,<br />
what is your advice for them to<br />
succeed in this role?<br />
Heather: To have good<br />
organizati<strong>on</strong> skills, judgement,<br />
problem-solving<br />
skills,<br />
communicati<strong>on</strong> skills, listening<br />
skills, and compassi<strong>on</strong> for<br />
others. Also, to have a desire to<br />
c<strong>on</strong>tinue to educate yourself and<br />
have the willingness to learn.<br />
Questi<strong>on</strong>: What do you think are<br />
some of the compliance issues<br />
facing your company?<br />
Heather: The technology in health<br />
care and our organizati<strong>on</strong> is<br />
c<strong>on</strong>tinually changing and advancing.<br />
I believe that a lot of employees are<br />
used to the way things were, and<br />
have a hard time adapting to<br />
change. Technology can be very<br />
intimidating to those especially who<br />
have been working in their careers<br />
al<strong>on</strong>g time.<br />
Questi<strong>on</strong>: What are some of the<br />
weaknesses in your company’s<br />
compliance program?<br />
Heather: We have a new EMR<br />
System that our employees are still<br />
adapting to<br />
Questi<strong>on</strong>: And how are you now<br />
addressing these weaknesses?<br />
Heather: By c<strong>on</strong>tinuing to educate<br />
the staff and by c<strong>on</strong>ducting<br />
surveillance and auditing of user<br />
access. Then, reporting these issues<br />
in our hospital m<strong>on</strong>thly QA meetings<br />
so that all Department Managers<br />
are aware of our progress.<br />
ISSUE 07<br />
June 2018<br />
Questi<strong>on</strong>: Describe a project you<br />
had to finish with limited resources.<br />
How were you able to accomplish it?<br />
Heather: I have <strong>on</strong>ly been in The<br />
Privacy Officer role for a few m<strong>on</strong>ths<br />
and although I have g<strong>on</strong>e through<br />
some challenges with some <str<strong>on</strong>g>HIPAA</str<strong>on</strong>g><br />
Breach investigati<strong>on</strong>s, I have not<br />
really had the opportunity to start a<br />
new project. If I had to start a<br />
project with limited resources, I<br />
would maintain a positive outlook<br />
and utilize my organizati<strong>on</strong>al skills<br />
to develop a plan. I would start by<br />
organizing my tasks from most<br />
important to least. If I saw that I<br />
could not complete a certain task <strong>on</strong><br />
my own, I would ask for assistance<br />
from my peers at work and at <str<strong>on</strong>g>HIPAA</str<strong>on</strong>g><br />
<str<strong>on</strong>g>Guard</str<strong>on</strong>g>.<br />
Questi<strong>on</strong>: Can you give us your top 3<br />
reas<strong>on</strong>s if you were asked why<br />
should a company or organizati<strong>on</strong><br />
particularly in the Healthcare<br />
industry, have a privacy officer?<br />
Heather: First and most importantly,<br />
to protect and ensure patients’<br />
rights and informati<strong>on</strong>. Sec<strong>on</strong>d, to<br />
help maintain administrative and<br />
compliance requirements. Third, to<br />
keep your organizati<strong>on</strong>s employees<br />
educated <strong>on</strong> patient privacy and<br />
educati<strong>on</strong> of the advancement of<br />
security and other safeguards.<br />
Questi<strong>on</strong>: Can a healthcare<br />
organizati<strong>on</strong> afford not to have a<br />
privacy officer like in the case of<br />
rural hospitals? Can they opt not to<br />
have <strong>on</strong>e for their organizati<strong>on</strong>? If<br />
yes, why and if no, why not?<br />
Heather: I believe an organizati<strong>on</strong><br />
can’t afford to not have a Privacy<br />
Officer. Privacy is about respecting<br />
people, and people having trust. If a<br />
pers<strong>on</strong> does not trust some<strong>on</strong>e, you<br />
may lose their relati<strong>on</strong>ship. In turn,<br />
a business such a small Rural<br />
Hospital, will loose patients due to<br />
lack of trust and respect. It can then<br />
lead to a bad reputati<strong>on</strong> and moral<br />
of the organizati<strong>on</strong>.<br />
Questi<strong>on</strong>: How do you help create a<br />
culture of compliance for privacy<br />
and security of PHI and ePHI within<br />
your organizati<strong>on</strong>?<br />
Heather: I think a good way to create<br />
a good culture, is to give employees<br />
all the tools and resources of<br />
keeping up with knowledge and<br />
educati<strong>on</strong>. If we c<strong>on</strong>tinue create a<br />
positive and creative way to educate<br />
employees… they will have a good<br />
understanding and feel comfortable<br />
with compliance. It becomes a<br />
natural habit of their work day, and<br />
not something they feel is a<br />
stressful challenge.
Interview with Regi<strong>on</strong>al General<br />
Hospital's Chief Privacy Officer<br />
Heather Thomps<strong>on</strong><br />
Questi<strong>on</strong>: We have been hearing about GDPR and how it will so<strong>on</strong><br />
become a big player in the overall privacy and security of an individual’s<br />
pers<strong>on</strong>al data, how are you preparing for this upcoming change? How are<br />
you preparing your organizati<strong>on</strong> for this upcoming change?<br />
Heather: I have just recently been introduced to GDPR. I know it is the<br />
most recent change to data protecti<strong>on</strong> and its going to be a dramatic<br />
change in the way privacy is regulated. As for now, I am going to<br />
strengthen my knowledge with the resources I have…. which primarily<br />
c<strong>on</strong>sists of my associati<strong>on</strong> with <str<strong>on</strong>g>HIPAA</str<strong>on</strong>g> guard for my educati<strong>on</strong>al<br />
resources and support.<br />
We would like to thank Heather for giving us these informative insights<br />
about her role as Chief Privacy Officer. <str<strong>on</strong>g>HIPAA</str<strong>on</strong>g> <str<strong>on</strong>g>Guard</str<strong>on</strong>g> initiatives are and<br />
will always be focused <strong>on</strong> supporting the core team like Heather’s team<br />
in attaining full <str<strong>on</strong>g>HIPAA</str<strong>on</strong>g> and HITECH compliance. We will c<strong>on</strong>tinuously<br />
strive to ensure every<strong>on</strong>e involved in operating your hospital and health<br />
system be fully committed to compliance. Our job becomes much easier<br />
if we have people like Heather who are dedicated to work with us as we<br />
work towards the same goals.<br />
Our Top 4 <str<strong>on</strong>g>HIPAA</str<strong>on</strong>g> Initiatives for this m<strong>on</strong>th of June all relates to the FIRST<br />
Technical Safeguard Standard of the <str<strong>on</strong>g>HIPAA</str<strong>on</strong>g> Administrative Simplificati<strong>on</strong><br />
Security Rule i.e. ACCESS CONTROL. It has four implementati<strong>on</strong><br />
specificati<strong>on</strong>s:<br />
Encrypti<strong>on</strong>/Decrypti<strong>on</strong><br />
<br />
Unique User Identificati<strong>on</strong><br />
<br />
Emergency Access<br />
<br />
Automatic Log-Off<br />
<br />
ISSUE 07<br />
June 2018
Access C<strong>on</strong>trol: What This <str<strong>on</strong>g>HIPAA</str<strong>on</strong>g> Security<br />
Rule Technical Safeguard Standard Is All<br />
About<br />
In your facility, does every member of the workforce have the same<br />
access rights or access levels to those electr<strong>on</strong>ic protected health<br />
informati<strong>on</strong> or ePHI? The access level of say a Fr<strong>on</strong>t Desk staff is similar<br />
to the access of a Laboratory technician? The rightful answer is NO.<br />
<str<strong>on</strong>g>HIPAA</str<strong>on</strong>g> law has mandated that policies and procedures be placed to<br />
provide appropriate access to the ePHI to every workforce of the facility<br />
and this is covered by the “Informati<strong>on</strong> Access Management Standard”.<br />
But not all access will be the same. As menti<strong>on</strong>ed earlier, there must be<br />
some form of c<strong>on</strong>trol <strong>on</strong> who accesses what ePHI, when and how. This is<br />
covered by the ACCESS CONTROL STANDARD.<br />
There are four comm<strong>on</strong>ly used approaches to c<strong>on</strong>trolling who will have<br />
access to informati<strong>on</strong> and when access to this informati<strong>on</strong> is available. It<br />
depends <strong>on</strong> the outcome of the facility’s risk assessments as to which<br />
approach is most suitable to use. More informati<strong>on</strong> about these<br />
approaches provided in NIST 7316 Assessment of Access C<strong>on</strong>trol<br />
Systems.<br />
Access C<strong>on</strong>trol List (ACL)<br />
User Based Access C<strong>on</strong>trol (UBAC)<br />
Role Based Access C<strong>on</strong>trol (RBAC)<br />
C<strong>on</strong>text Based Access C<strong>on</strong>trol (CBAC)<br />
Source: <str<strong>on</strong>g>HIPAA</str<strong>on</strong>g>.com, NIST & hhs.gov<br />
Access C<strong>on</strong>trol:<br />
UNIQUE USER IDENTIFICATION<br />
Technical Standard § 164.312(a)(2)(i)<br />
Covered entity must<br />
“Assign a unique name and/or number<br />
for identifying and tracking user<br />
identity.”<br />
Unique User Identificati<strong>on</strong> is a required implementati<strong>on</strong> specificati<strong>on</strong><br />
and it is a way a covered entity could track :<br />
1. Who accessed the informati<strong>on</strong> system<br />
2. When and How often was the ePHI accessed<br />
3. What ePHI or data in the informati<strong>on</strong> system was accessed<br />
4. Where was the ePHI or data specifically accessed<br />
How this is d<strong>on</strong>e? It depends <strong>on</strong> the structure of the workforce and their<br />
operati<strong>on</strong>s how the format of the unique user identificati<strong>on</strong> will be<br />
designed. It could be <strong>on</strong>e of the following:<br />
1. Employee name or a variati<strong>on</strong> of the name e.g. ebgesmundo<br />
2. Random combinati<strong>on</strong>s of numbers and letters e.g. EB6200014<br />
3. Combinati<strong>on</strong> of the above two e.g. EGesmundo3780<br />
Security Officer must manage and m<strong>on</strong>itor this. IT Manager or Office<br />
Manager must coordinate with the Security Officer the implementati<strong>on</strong><br />
& documentati<strong>on</strong> of this policy and procedure especially when:<br />
1. New employees are hired<br />
2. Existing employees changed job or roles<br />
3. Existing employees change names<br />
4. Employees gets terminated or resigned
Access C<strong>on</strong>trol:<br />
EMERGENCY ACCESS PROCEDURE<br />
Technical Standard § 164.312(a)(2)(ii)<br />
Covered entity must<br />
“Establish (and implement as needed)<br />
procedures for obtaining necessary<br />
electr<strong>on</strong>ic protected health informati<strong>on</strong><br />
during an emergency.”<br />
This is the sec<strong>on</strong>d implementati<strong>on</strong> specificati<strong>on</strong> that is c<strong>on</strong>sidered required.<br />
Emergency situati<strong>on</strong>s like fire, natural disaster, total system shutdown or<br />
failure, and terrorism attacks could result to delay in the access of crucial<br />
informati<strong>on</strong> or data in the informati<strong>on</strong> system of a healthcare provider which<br />
c<strong>on</strong>sequently lead to delay in the provisi<strong>on</strong> of health and medical treatment<br />
of patients and could cause danger in some<strong>on</strong>e’s health. Covered entities<br />
are mandated to prepare for such emergency as such emergency access<br />
procedures and policies be created.<br />
The Security Officer in coordinati<strong>on</strong> with IT Manager, Office Managers and<br />
Informati<strong>on</strong> System as well as software suppliers in coming up with such<br />
Emergency Access Procedures and that these are to be part of the Risk<br />
Analysis that the organizati<strong>on</strong> will c<strong>on</strong>duct.<br />
The following must be c<strong>on</strong>sidered:<br />
1. Determine the type of emergency situati<strong>on</strong>s that would warrant the use<br />
of the Emergency Access Procedures in the informati<strong>on</strong> system or<br />
applicati<strong>on</strong>s that c<strong>on</strong>tain ePHI<br />
2. Coordinate such policies and procedures with the policies and<br />
procedures created for Administrative Safeguards: C<strong>on</strong>tingency Plan<br />
(Standard § 164.308(a)(7))<br />
3. Document these policies and procedures that will be created to address<br />
this implementati<strong>on</strong> specificati<strong>on</strong><br />
Access C<strong>on</strong>trol:<br />
AUTOMATIC LOGOFF<br />
Technical Standard § 164.312(a)(2)(iii)<br />
Covered entity must<br />
“Implement electr<strong>on</strong>ic procedures<br />
that terminate an electr<strong>on</strong>ic sessi<strong>on</strong><br />
after a predetermined time of inactivity.”<br />
This is the third implementati<strong>on</strong> specificati<strong>on</strong> that is c<strong>on</strong>sidered as<br />
addressable i.e. opti<strong>on</strong>al. The covered entity must reas<strong>on</strong>able and<br />
appropriate measures to meet this standard. The main purpose of this<br />
standard is to prevent unauthorized viewing and accessed to electr<strong>on</strong>ic<br />
protected health informati<strong>on</strong> (ePHI) from unattended electr<strong>on</strong>ic<br />
informati<strong>on</strong> system devices such as computers or laptops in<br />
workstati<strong>on</strong>s. After a pre-determined period of inactivity the device<br />
c<strong>on</strong>taining ePHI will automatically log-off. This automatic log-off system<br />
would require the user to enter a unique password to regain access to<br />
the ePHI. All workstati<strong>on</strong>s must be installed with such c<strong>on</strong>figurati<strong>on</strong>s<br />
and the time out or log off period depends areas where the device is<br />
placed and the size of the facility. Example, highly populated areas such<br />
as that of the Fr<strong>on</strong>t Desk must have a automatic log off period of 2 to 3<br />
minutes. But areas that has limited access and c<strong>on</strong>trolled like the<br />
Laboratory or Radiology Offices might have 5 to 10 minutes of time out<br />
period c<strong>on</strong>figurati<strong>on</strong>s.<br />
It is the resp<strong>on</strong>sibility of the Security Officer to document this procedure<br />
and policies as well as manage this implementati<strong>on</strong>. He must also<br />
coordinate with software or applicati<strong>on</strong> vendors <strong>on</strong> how and what<br />
c<strong>on</strong>figurati<strong>on</strong>s are appropriate for each device or workstati<strong>on</strong>. The<br />
Security Officer must also take into account how these devices or<br />
workstati<strong>on</strong>s moved from <strong>on</strong>e place to another.<br />
Source: <str<strong>on</strong>g>HIPAA</str<strong>on</strong>g>.com, NIST & HHS.gov
Access C<strong>on</strong>trol:<br />
ENCRYTION AND DECRYPTION<br />
Technical Standard § 164.312(a)(2)(iv)<br />
Covered entity must<br />
“Implement a mechanism to<br />
encrypt and decrypt<br />
electr<strong>on</strong>ic protected<br />
health informati<strong>on</strong>.”<br />
This is the fourth implementati<strong>on</strong> specificati<strong>on</strong> that is c<strong>on</strong>sidered as<br />
addressable. Similarly, the main goal for this implementati<strong>on</strong> is to ensure<br />
unauthorized viewing and accessing of ePHI is prevented.<br />
As described by Microsoft, “Encrypti<strong>on</strong> is the process of translating plain text<br />
data (plaintext) into something that appears to be random and meaningless<br />
(ciphertext). Decrypti<strong>on</strong> is the process of c<strong>on</strong>verting ciphertext back to<br />
plaintext.”<br />
Needless to say, even if this implementati<strong>on</strong> is an ‘opti<strong>on</strong>al’ <strong>on</strong>e, this is <strong>on</strong>e<br />
str<strong>on</strong>g and relevant key and piece of a security system puzzle. This can help<br />
prevent data breaches and ePHI theft. Also, since HITECH Act required all to<br />
have Electr<strong>on</strong>ic Health Record by 2014, the more reas<strong>on</strong> Encrypti<strong>on</strong> has<br />
become <strong>on</strong>e str<strong>on</strong>g soluti<strong>on</strong> to protect ePHI.<br />
The Nati<strong>on</strong>al Institute of Standards and Technology (NIST) has provided<br />
some guidelines <strong>on</strong> encrypting data at various stages i.e. data at rest, data<br />
in moti<strong>on</strong>, data in use and data disposed.<br />
Want to get a copy of our<br />
previous <str<strong>on</strong>g>Newsletter</str<strong>on</strong>g> issues?<br />
Get updates <strong>on</strong> what is<br />
happening in the<br />
healthcare industry<br />
C<strong>on</strong>nect with other<br />
people working<br />
towards <str<strong>on</strong>g>HIPAA</str<strong>on</strong>g><br />
compliance<br />
C<strong>on</strong>nect, follow,<br />
and have a<br />
c<strong>on</strong>versati<strong>on</strong> with us<br />
ISSUE 07<br />
June 2018