HIPAA Guard Herald - Your Monthly Newsletter on Surviving HIPAA
HIPAA Guard Newsletter Issue 07 June 2018
HIPAA Guard Newsletter Issue 07 June 2018
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
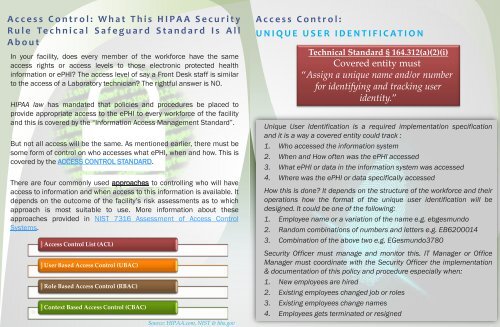
Access C<strong>on</strong>trol: What This <str<strong>on</strong>g>HIPAA</str<strong>on</strong>g> Security<br />
Rule Technical Safeguard Standard Is All<br />
About<br />
In your facility, does every member of the workforce have the same<br />
access rights or access levels to those electr<strong>on</strong>ic protected health<br />
informati<strong>on</strong> or ePHI? The access level of say a Fr<strong>on</strong>t Desk staff is similar<br />
to the access of a Laboratory technician? The rightful answer is NO.<br />
<str<strong>on</strong>g>HIPAA</str<strong>on</strong>g> law has mandated that policies and procedures be placed to<br />
provide appropriate access to the ePHI to every workforce of the facility<br />
and this is covered by the “Informati<strong>on</strong> Access Management Standard”.<br />
But not all access will be the same. As menti<strong>on</strong>ed earlier, there must be<br />
some form of c<strong>on</strong>trol <strong>on</strong> who accesses what ePHI, when and how. This is<br />
covered by the ACCESS CONTROL STANDARD.<br />
There are four comm<strong>on</strong>ly used approaches to c<strong>on</strong>trolling who will have<br />
access to informati<strong>on</strong> and when access to this informati<strong>on</strong> is available. It<br />
depends <strong>on</strong> the outcome of the facility’s risk assessments as to which<br />
approach is most suitable to use. More informati<strong>on</strong> about these<br />
approaches provided in NIST 7316 Assessment of Access C<strong>on</strong>trol<br />
Systems.<br />
Access C<strong>on</strong>trol List (ACL)<br />
User Based Access C<strong>on</strong>trol (UBAC)<br />
Role Based Access C<strong>on</strong>trol (RBAC)<br />
C<strong>on</strong>text Based Access C<strong>on</strong>trol (CBAC)<br />
Source: <str<strong>on</strong>g>HIPAA</str<strong>on</strong>g>.com, NIST & hhs.gov<br />
Access C<strong>on</strong>trol:<br />
UNIQUE USER IDENTIFICATION<br />
Technical Standard § 164.312(a)(2)(i)<br />
Covered entity must<br />
“Assign a unique name and/or number<br />
for identifying and tracking user<br />
identity.”<br />
Unique User Identificati<strong>on</strong> is a required implementati<strong>on</strong> specificati<strong>on</strong><br />
and it is a way a covered entity could track :<br />
1. Who accessed the informati<strong>on</strong> system<br />
2. When and How often was the ePHI accessed<br />
3. What ePHI or data in the informati<strong>on</strong> system was accessed<br />
4. Where was the ePHI or data specifically accessed<br />
How this is d<strong>on</strong>e? It depends <strong>on</strong> the structure of the workforce and their<br />
operati<strong>on</strong>s how the format of the unique user identificati<strong>on</strong> will be<br />
designed. It could be <strong>on</strong>e of the following:<br />
1. Employee name or a variati<strong>on</strong> of the name e.g. ebgesmundo<br />
2. Random combinati<strong>on</strong>s of numbers and letters e.g. EB6200014<br />
3. Combinati<strong>on</strong> of the above two e.g. EGesmundo3780<br />
Security Officer must manage and m<strong>on</strong>itor this. IT Manager or Office<br />
Manager must coordinate with the Security Officer the implementati<strong>on</strong><br />
& documentati<strong>on</strong> of this policy and procedure especially when:<br />
1. New employees are hired<br />
2. Existing employees changed job or roles<br />
3. Existing employees change names<br />
4. Employees gets terminated or resigned