HIPAA Guard Herald - Your Monthly Newsletter on Surviving HIPAA
HIPAA Guard Newsletter Issue 07 June 2018
HIPAA Guard Newsletter Issue 07 June 2018
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
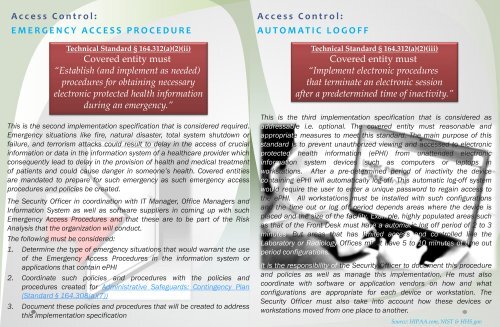
Access C<strong>on</strong>trol:<br />
EMERGENCY ACCESS PROCEDURE<br />
Technical Standard § 164.312(a)(2)(ii)<br />
Covered entity must<br />
“Establish (and implement as needed)<br />
procedures for obtaining necessary<br />
electr<strong>on</strong>ic protected health informati<strong>on</strong><br />
during an emergency.”<br />
This is the sec<strong>on</strong>d implementati<strong>on</strong> specificati<strong>on</strong> that is c<strong>on</strong>sidered required.<br />
Emergency situati<strong>on</strong>s like fire, natural disaster, total system shutdown or<br />
failure, and terrorism attacks could result to delay in the access of crucial<br />
informati<strong>on</strong> or data in the informati<strong>on</strong> system of a healthcare provider which<br />
c<strong>on</strong>sequently lead to delay in the provisi<strong>on</strong> of health and medical treatment<br />
of patients and could cause danger in some<strong>on</strong>e’s health. Covered entities<br />
are mandated to prepare for such emergency as such emergency access<br />
procedures and policies be created.<br />
The Security Officer in coordinati<strong>on</strong> with IT Manager, Office Managers and<br />
Informati<strong>on</strong> System as well as software suppliers in coming up with such<br />
Emergency Access Procedures and that these are to be part of the Risk<br />
Analysis that the organizati<strong>on</strong> will c<strong>on</strong>duct.<br />
The following must be c<strong>on</strong>sidered:<br />
1. Determine the type of emergency situati<strong>on</strong>s that would warrant the use<br />
of the Emergency Access Procedures in the informati<strong>on</strong> system or<br />
applicati<strong>on</strong>s that c<strong>on</strong>tain ePHI<br />
2. Coordinate such policies and procedures with the policies and<br />
procedures created for Administrative Safeguards: C<strong>on</strong>tingency Plan<br />
(Standard § 164.308(a)(7))<br />
3. Document these policies and procedures that will be created to address<br />
this implementati<strong>on</strong> specificati<strong>on</strong><br />
Access C<strong>on</strong>trol:<br />
AUTOMATIC LOGOFF<br />
Technical Standard § 164.312(a)(2)(iii)<br />
Covered entity must<br />
“Implement electr<strong>on</strong>ic procedures<br />
that terminate an electr<strong>on</strong>ic sessi<strong>on</strong><br />
after a predetermined time of inactivity.”<br />
This is the third implementati<strong>on</strong> specificati<strong>on</strong> that is c<strong>on</strong>sidered as<br />
addressable i.e. opti<strong>on</strong>al. The covered entity must reas<strong>on</strong>able and<br />
appropriate measures to meet this standard. The main purpose of this<br />
standard is to prevent unauthorized viewing and accessed to electr<strong>on</strong>ic<br />
protected health informati<strong>on</strong> (ePHI) from unattended electr<strong>on</strong>ic<br />
informati<strong>on</strong> system devices such as computers or laptops in<br />
workstati<strong>on</strong>s. After a pre-determined period of inactivity the device<br />
c<strong>on</strong>taining ePHI will automatically log-off. This automatic log-off system<br />
would require the user to enter a unique password to regain access to<br />
the ePHI. All workstati<strong>on</strong>s must be installed with such c<strong>on</strong>figurati<strong>on</strong>s<br />
and the time out or log off period depends areas where the device is<br />
placed and the size of the facility. Example, highly populated areas such<br />
as that of the Fr<strong>on</strong>t Desk must have a automatic log off period of 2 to 3<br />
minutes. But areas that has limited access and c<strong>on</strong>trolled like the<br />
Laboratory or Radiology Offices might have 5 to 10 minutes of time out<br />
period c<strong>on</strong>figurati<strong>on</strong>s.<br />
It is the resp<strong>on</strong>sibility of the Security Officer to document this procedure<br />
and policies as well as manage this implementati<strong>on</strong>. He must also<br />
coordinate with software or applicati<strong>on</strong> vendors <strong>on</strong> how and what<br />
c<strong>on</strong>figurati<strong>on</strong>s are appropriate for each device or workstati<strong>on</strong>. The<br />
Security Officer must also take into account how these devices or<br />
workstati<strong>on</strong>s moved from <strong>on</strong>e place to another.<br />
Source: <str<strong>on</strong>g>HIPAA</str<strong>on</strong>g>.com, NIST & HHS.gov