Through its unique cyber service delivery construct, CSIOS has been able to: identify more efficient, effective, and time– saving management processes; improve incident response times; and minimize disruptions to cybersecurity services–all while reducing operating costs and continuing to maintain compliance with customer’s legislative and regulatory requirements. Equally important, as an organization, through its demonstrated accomplishment, CSIOS has reached new high levels of confidence when delivering its services. Simply put, CSIOS’ attainment of quadruple ISO certifications has relayed a message of excellence to staff and stakeholders. CSIOS’ culture of top–service– delivery–levels and right–first– time approach has also instilled a higher degree of trust and credibility with and among its U.S. Government customers. CSIOS’ customers have benefited from its improved quality and service, quality assurance, and always– on–time delivery. Overall, CSIOS continual assessment and improvement process has allowed the company to persistently introduce, verify, and validate needed process changes and corrective actions to maintain high–level objectives of availability, integrity, authentication, confidentiality, and non–repudiation. As the only provider of cyber services with quadruple ISO standards, CSIOS has rapidly taken a leadership position in the cyber market becoming one of the preferred U.S. government choices and global leaders in provisioning cybersecurity services to multiple DOD <strong>Cyber</strong>security Service Providers (CSSPs) protecting and defending DOD information systems, networks, warfighters globally in more than 145 countries, 15,000 classified and unclassified networks, and 7 million computers and IT devices worldwide. Year after year, the company has been scaling new heights of cybersecurity services and the unique level of cyber services provisioned by this veteran owned–small business is not going unnoticed—earlier this year, CSIOS was recipient of the Maryland’s 2018 <strong>Cyber</strong>security Defender of the Year Award. CSIOS also landed a spot among the 50 Most Valuable Brands of the Year 2018 by “The Silicon Review” <strong>Magazine</strong>. Further, CSIOS <strong>Cyber</strong>space Operations Team was named winner of a Gold Stevie® Award in the Information Technology Team of Year category in The 16th <strong>Annual</strong> 2018 American Business Awards®. A veteran of the U.S. Marine Corps, Mr. Pie is an established corporate officer with a demonstrated record of success and unyielding commitment to teamwork, honesty, integrity, excellence, and dedication to employees and the U.S. Federal government customers he serves. Mr. Pie was named CSIOS President and Chief Executive Officer in December 2015. Since, he has assumed executive oversight and day–to–day leadership of CSIOS. Mr. Pie holds a Master of Science degree in Computer System Management and Information Assurance from the University of Maryland University College and a myriad of professional certifications to include Certified in the Governance of Enterprise IT (CGEIT), Certified in Risk and Information Systems Control (CRISC), Certified Information Systems Auditor (CISA), Certified Information Systems Security Professional (CISSP), Information Systems Security Engineering Professional (ISSEP), and Project Management Professional (PMP). 32 <strong>Cyber</strong> <strong>Defense</strong> <strong>Magazine</strong> - <strong>Annual</strong> <strong>Print</strong> <strong>Edition</strong> <strong>2019</strong>
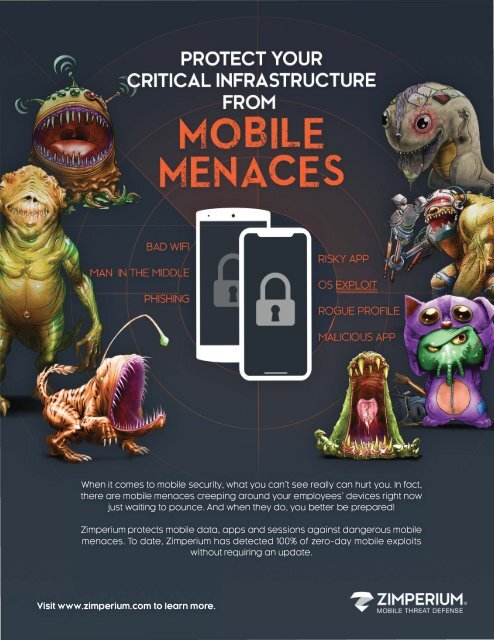
RISKY APP OS EXPLOIT ROGUE PROFILE MLLICIOUS APP ; / When it comes to mobile security, what you can't see really can hurt you. In fact, there are mobile menaces creeping around your employees' devices right now just waiting to pounce. And when they do, you better be prepared! Zimperium protects mobile data, apps and sessions against dangerous mobile menaces. To date, Zimperium has detected 100% of zero-day mobile exploits without requiring an update. Visit www.zimperium.com to learn more.
- Page 2 and 3: WELCOME ABOARD We’re honored to b
- Page 4 and 5: Welcome Letter RSAC 2019 Cyber Defe
- Page 6 and 7: P3 - Nation-state hacking, it’s a
- Page 8 and 9: P7 -AI-based attacks, a nightmare f
- Page 10 and 11: I’ve summarized a sample roadmap
- Page 12 and 13: Does Your Organization Need MFT Sof
- Page 14 and 15: But a fully-connected world is a Ut
- Page 16 and 17: GTB Technologies Data Protection th
- Page 18 and 19: 360 ESG, itself, is endowed with PE
- Page 20 and 21: Winning the Battle for the Inbox by
- Page 22 and 23: 3. Incident Response with Global Re
- Page 24 and 25: HORNETSECURITY • A V ENTER COMPA
- Page 26 and 27: Zero Trust? Not if You’re Surfing
- Page 28 and 29: Remote Browser Isolation is Zero Tr
- Page 30 and 31: INTEZER GENETIC MALWARE ANALYSIS De
- Page 34 and 35: Fraud Protection and AI in the Fina
- Page 36 and 37: Especially in the financial industr
- Page 38 and 39: Thanks to Human Expertise, Companie
- Page 40 and 41: The email told recipients that the
- Page 42 and 43: Why Major Data Breaches Will Contin
- Page 44: The Advanced SQL Behavioral Analysi
- Page 47 and 48: Advanced Safeguards Secure Channels
- Page 49 and 50: www.securechannels.com Protect Your
- Page 51 and 52: To understand how this can work, th
- Page 54 and 55: Attivo Networks and Deception Marke
- Page 56 and 57: Attivo ThreatDefend Solution Differ
- Page 58 and 59: Jumio Ad
- Page 60 and 61: YScanner Web Application Scan YOUNK
- Page 62 and 63: Authentication Methods After the us
- Page 64 and 65: Emerging Use Cases By using your us
- Page 66 and 67: Setting the Standard in Cyber Defen
- Page 68 and 69: For a security culture to take hold
- Page 70 and 71: O2, Ericsson, and Equifax: How Cert
- Page 73 and 74: ‘To Be or Not To Be’: Here’s
- Page 75: On-Premise Model (Hosted by SMEs) M
- Page 78 and 79: How do we as organizations fight ag
- Page 80 and 81: '-. \;Global Learning Systems Globa
- Page 82 and 83:
The time has come to move away from
- Page 84 and 85:
High-Level Strategies for Third-Par
- Page 86 and 87:
Wouldn't you like to see the threat
- Page 88 and 89:
Insight into Your Security Posture
- Page 90 and 91:
Quis custodiet ipsos custodes? (Who
- Page 92 and 93:
ATAR ® SECURITY ORCHESTRATION, AUT
- Page 94 and 95:
Aligning Cybersecurity Effectivenes
- Page 96 and 97:
enterprises do not have the systems
- Page 98 and 99:
DEFENSE BY OFFENSE Purple Team: The
- Page 100 and 101:
◄-► NOZOMI , N E T W O R K S Re
- Page 102 and 103:
It’s latest creation - the 2019 S
- Page 104 and 105:
Filling the Public Relations Void f
- Page 106 and 107:
PR is a relationship business; it m
- Page 108 and 109:
InfoSec Awards for 2019 Access Cont
- Page 110 and 111:
InfoSec Awards for 2019 Digital Foo
- Page 112:
InfoSec Awards for 2019 Security Or
- Page 115 and 116:
DELIVERING THE NEXT EVOLUTION IN MA