High-Level Strategies for Third-Party Risk Mitigation By Phil Won, Product Manager, Owl <strong>Cyber</strong> <strong>Defense</strong> High-Level Strategies for Third-Party Risk Mitigation There are so many technologies and strategies and buzz words around cybersecurity these days that it can be difficult to know where to start. It’s hard enough thinking about the myriad threats that can find their way into your organization without even broaching the subject of third-parties and trusted connections. However, there are a few fundamental, high-level strategies to consider applying in your third-party risk mitigation plan. They can be used individually or in tandem to create a strong cybersecurity framework for your organization. • <strong>Defense</strong> in Depth The primary principle of defense in depth is to build layers of security into your organization’s digital architecture, so that if one layer fails, there will be others to back it up and maintain security. It is essentially a “fail-safe” strategy that assumes threats will most likely eventually find a way through one or two layers of defense (a safe assumption in most cases). There are no limits to the types of security involved, just those that best fit your organization. Role-based access controls, authentication, data encryption/tokenization, firewalls, data diodes, SIEM, and other technologies can all be used together to create a sophisticated, hardened defense. • Risk-Based Security Assuming that threats will eventually breach your network’s defenses (you may be sensing a theme), a riskbased strategy applies more security resources to your most sensitive assets while less resources are applied to the lower risk assets. Risk-based strategies also typically assume that there is not a way to eliminate risk – there will be a need for multiple sophisticated connections to external networks, for a large number of users to access or collaborate on (sometimes sensitive) data, legacy or outdated equipment in use, or other complex issues that complicate traditional security methods. Over time, larger and higher performing companies have evolved the idea of a risk-based strategy into a more comprehensive method of protecting their organizations known as “zero trust.” • Zero Trust A zero-trust strategy assumes that a threat can come from anywhere inside or outside your organization, and therefore a continual assessment of every request or attempt to connect or access networks, devices, or information is required. This can be highly resource intensive, and typically requires sophisticated authentication schemes as well as some sort of SIEM automation in the form of cloud data collection, systems monitoring, etc. User and systems data are monitored continually to develop a baseline of what is considered “normal” activity, which then allows for alerts if any abnormal activity occurs. Reducing the number of your external connections, applying the least privilege principle, and having dedicated resources to monitor and calibrate the results are all key to making this strategy effective, and while it is theoretically a great strategy for complex, highly-connected organizations, in practice it is very difficult to fully achieve today. Phil Won, Product Manager Phil is a product and technology leader, with years of experience in product development enabling the merge of business and technology needs of diverse industries (connected consumer devices, IIOT, automotive, cyber security and telecom). He brings strategic and technical proficiency in new product planning, development, and deployment initiatives. Phil is on the Product Management team at Owl <strong>Cyber</strong> <strong>Defense</strong>. His main product line is OPDS, focusing on growing existing products and innovating future solutions. Phil can be reached at pwon@owlcyberdefense.com or our company website is: www.owlcyberdefense.com – twitter handle: @owlcyberdefense.com 84 <strong>Cyber</strong> <strong>Defense</strong> <strong>Magazine</strong> - <strong>Annual</strong> <strong>Print</strong> <strong>Edition</strong> <strong>2019</strong>
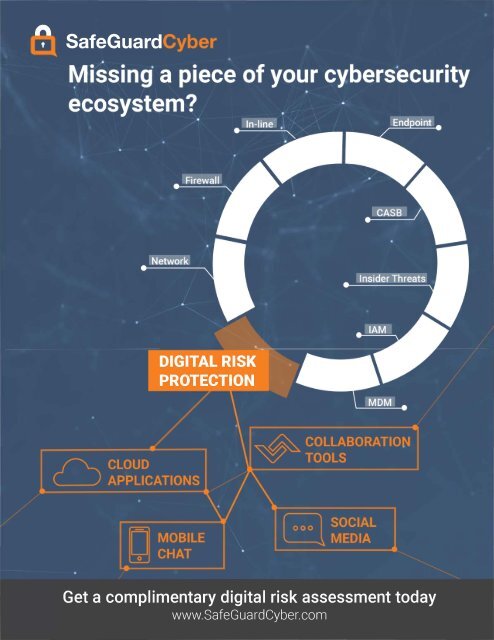
SafeGuard DIGITAL RISK PROTECTION Get a complimentary digital risk assessment today www.SafeGuard<strong>Cyber</strong>.com
- Page 2 and 3:
WELCOME ABOARD We’re honored to b
- Page 4 and 5:
Welcome Letter RSAC 2019 Cyber Defe
- Page 6 and 7:
P3 - Nation-state hacking, it’s a
- Page 8 and 9:
P7 -AI-based attacks, a nightmare f
- Page 10 and 11:
I’ve summarized a sample roadmap
- Page 12 and 13:
Does Your Organization Need MFT Sof
- Page 14 and 15:
But a fully-connected world is a Ut
- Page 16 and 17:
GTB Technologies Data Protection th
- Page 18 and 19:
360 ESG, itself, is endowed with PE
- Page 20 and 21:
Winning the Battle for the Inbox by
- Page 22 and 23:
3. Incident Response with Global Re
- Page 24 and 25:
HORNETSECURITY • A V ENTER COMPA
- Page 26 and 27:
Zero Trust? Not if You’re Surfing
- Page 28 and 29:
Remote Browser Isolation is Zero Tr
- Page 30 and 31:
INTEZER GENETIC MALWARE ANALYSIS De
- Page 32 and 33:
Through its unique cyber service de
- Page 34 and 35: Fraud Protection and AI in the Fina
- Page 36 and 37: Especially in the financial industr
- Page 38 and 39: Thanks to Human Expertise, Companie
- Page 40 and 41: The email told recipients that the
- Page 42 and 43: Why Major Data Breaches Will Contin
- Page 44: The Advanced SQL Behavioral Analysi
- Page 47 and 48: Advanced Safeguards Secure Channels
- Page 49 and 50: www.securechannels.com Protect Your
- Page 51 and 52: To understand how this can work, th
- Page 54 and 55: Attivo Networks and Deception Marke
- Page 56 and 57: Attivo ThreatDefend Solution Differ
- Page 58 and 59: Jumio Ad
- Page 60 and 61: YScanner Web Application Scan YOUNK
- Page 62 and 63: Authentication Methods After the us
- Page 64 and 65: Emerging Use Cases By using your us
- Page 66 and 67: Setting the Standard in Cyber Defen
- Page 68 and 69: For a security culture to take hold
- Page 70 and 71: O2, Ericsson, and Equifax: How Cert
- Page 73 and 74: ‘To Be or Not To Be’: Here’s
- Page 75: On-Premise Model (Hosted by SMEs) M
- Page 78 and 79: How do we as organizations fight ag
- Page 80 and 81: '-. \;Global Learning Systems Globa
- Page 82 and 83: The time has come to move away from
- Page 86 and 87: Wouldn't you like to see the threat
- Page 88 and 89: Insight into Your Security Posture
- Page 90 and 91: Quis custodiet ipsos custodes? (Who
- Page 92 and 93: ATAR ® SECURITY ORCHESTRATION, AUT
- Page 94 and 95: Aligning Cybersecurity Effectivenes
- Page 96 and 97: enterprises do not have the systems
- Page 98 and 99: DEFENSE BY OFFENSE Purple Team: The
- Page 100 and 101: ◄-► NOZOMI , N E T W O R K S Re
- Page 102 and 103: It’s latest creation - the 2019 S
- Page 104 and 105: Filling the Public Relations Void f
- Page 106 and 107: PR is a relationship business; it m
- Page 108 and 109: InfoSec Awards for 2019 Access Cont
- Page 110 and 111: InfoSec Awards for 2019 Digital Foo
- Page 112: InfoSec Awards for 2019 Security Or
- Page 115 and 116: DELIVERING THE NEXT EVOLUTION IN MA