CS Nov-Dec 2020
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
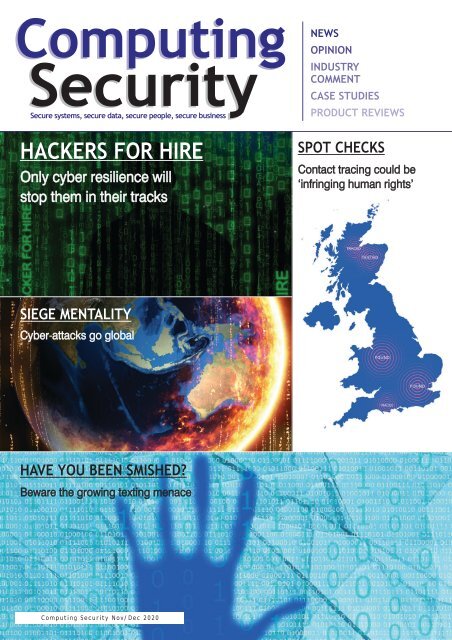
Computing<br />
Security<br />
Secure systems, secure data, secure people, secure business<br />
HACKERS FOR HIRE<br />
Only cyber resilience will<br />
stop them in their tracks<br />
NEWS<br />
OPINION<br />
INDUSTRY<br />
COMMENT<br />
CASE STUDIES<br />
PRODUCT REVIEWS<br />
SPOT CHECKS<br />
Contact tracing could be<br />
‘infringing human rights’<br />
SIEGE MENTALITY<br />
Cyber-attacks go global<br />
HAVE YOU BEEN SMISHED?<br />
Beware the growing texting menace<br />
Computing Security <strong>Nov</strong>/<strong>Dec</strong> <strong>2020</strong>
My peace of<br />
mind starts<br />
with Neustar<br />
Security.<br />
Cloud Security Solutions that are<br />
Always-on, Ultra Secure.<br />
security.neustar
comment<br />
TIME TO TAKE GDPR UP A GEAR<br />
Recent research has revealed that GDPR doesn't go far enough in the eyes of many<br />
IT leaders and employees, who are calling for greater tech regulations around<br />
data protection and cyber security. The research, which comes from Snow<br />
Software, looks at responses from 1,000 IT leaders and 3,000 employees across the<br />
globe. Key findings reveal:<br />
94% of IT leaders and 82% of employees believe more regulations are needed. That's<br />
compared to 74% of employees in 2019 survey. Of those who do want to see more<br />
tech regulations, the two leading areas were data protection (54% of IT leaders/46%<br />
employees) and cybersecurity (54% IT/ 42% employees).<br />
In the UK, 54% of IT would prefer to see regulations that are firmly focused on<br />
cybersecurity first and foremost, followed closely by data protection at 48%. Data<br />
collection and encryption tie for third at 35% each, followed by competition and<br />
universal connectivity at 22% each. British and German IT respondents had the highest<br />
percentage of those who felt the technology industry did not need more regulation,<br />
both reporting 9%. Australians were slightly lower at 6%, while just 2% of American IT<br />
leaders thought additional regulation was not needed.<br />
When asked how the current state of technology regulations made them feel, the<br />
leading sentiment among IT leaders in <strong>2020</strong> was hopeful at 43%. Yet employees<br />
reported being slightly less hopeful - 26% in <strong>2020</strong> down from 29% in 2019.<br />
Unsuprisingly, perhaps, the biggest gap that existed between IT leaders and employees<br />
was around empowerment - in the current year, 32% of IT leaders felt empowered,<br />
versus just 15% of employees.<br />
The biggest year-over-year change related to vulnerability - and this was a positive.<br />
Nearly twice as many employees felt vulnerable in 2019 (24%), compared to <strong>2020</strong><br />
(13% employees and 10% of IT leaders). It suggests organisations are perceived to<br />
be getting a better grip on keeping the workorce safer and more secure. It will be<br />
interesting to see how well such votes of confidence hold up in the wider business<br />
world, as the Covid-19 pandemic continues to exert its impact on us all.<br />
Brian Wall<br />
Editor<br />
Computing Security<br />
brian.wall@btc.co.uk<br />
EDITOR: Brian Wall<br />
(brian.wall@btc.co.uk)<br />
LAYOUT/DESIGN: Ian Collis<br />
(ian.collis@btc.co.uk)<br />
SALES:<br />
Edward O’Connor<br />
(edward.oconnor@btc.co.uk)<br />
+ 44 (0)1689 616 000<br />
Abby Penn<br />
(abby.penn@btc.co.uk)<br />
+ 44 (0)1689 616 000<br />
PUBLISHER: John Jageurs<br />
(john.jageurs@btc.co.uk)<br />
Published by Barrow & Thompkins<br />
Connexions Ltd (BTC)<br />
35 Station Square,<br />
Petts Wood, Kent, BR5 1LZ<br />
Tel: +44 (0)1689 616 000<br />
Fax: +44 (0)1689 82 66 22<br />
SUBSCRIPTIONS:<br />
UK: £35/year, £60/two years,<br />
£80/three years;<br />
Europe: £48/year, £85/two years,<br />
£127/three years<br />
R.O.W:£62/year, £115/two years,<br />
£168/three years<br />
Single copies can be bought for<br />
£8.50 (includes postage & packaging).<br />
Published 6 times a year.<br />
© <strong>2020</strong> Barrow & Thompkins<br />
Connexions Ltd. All rights reserved.<br />
No part of the magazine may be<br />
reproduced without prior consent,<br />
in writing, from the publisher.<br />
www.computingsecurity.co.uk <strong>Nov</strong>/<strong>Dec</strong> <strong>2020</strong> computing security<br />
@<strong>CS</strong>MagAndAwards<br />
3
Secure systems, secure data, secure people, secure business<br />
Computing Security <strong>Nov</strong>/<strong>Dec</strong> <strong>2020</strong><br />
contents<br />
CONTENTS<br />
Computing<br />
Security<br />
NEWS<br />
OPINION<br />
INDUSTRY<br />
COMMENT<br />
CASE STUDIES<br />
PRODUCT REVIEWS<br />
HACKERS FOR HIRE<br />
SPOT CHECKS<br />
Contact tracing could be<br />
Only cyber resilience will<br />
‘infringing human rights’<br />
stop them in their tracks<br />
SIEGE MENTALITY<br />
Cyber-attacks go global<br />
HAVE YOU BEEN SMISHED?<br />
COMMENT 3<br />
Time to take GDPR up a gear<br />
Beware the growing texting menace<br />
EDITOR’S FOCUS 6<br />
Life under siege<br />
OPEN-AND-SHUT CASE 15<br />
Being receptive to ethical disclosure is<br />
vital, states Paul Ritchie, Managing<br />
Security Consultant, Pentest Limited<br />
THE NEW ORDER 16<br />
Is now the perfect time to get your (IT)<br />
house in order? Paul Harris, managing<br />
director, Pentest, offers his thoughts<br />
SHATTERED TRUST 8<br />
Babylon Health suffered a data breach<br />
where users of the GP remote consultation<br />
service were able to access videos of other<br />
patients' appointments with their doctor.<br />
Are such hack attacks, which are soaring,<br />
becoming beyond our control?<br />
HITTING THE SWEET SPOT 18<br />
Digital transformation is forecast to be<br />
the next driver for mergers & acquisitions<br />
SMISH, SMASH, BASH! 12<br />
A relatively new spin on phishing has<br />
DENTED SHIELD 20<br />
entered the lexicon, in the form of<br />
The EU-US Privacy Shield has been ruled<br />
'smishing'. But what is that exactly and<br />
invalid, shaking up how data protection<br />
how dangerous might it be to the<br />
and data privacy are regarded<br />
unsuspecting? And where does ‘vishing’<br />
come to play? Welcome to an ever more<br />
BRAKING BAD! 25<br />
perplexing world!<br />
Car owners could be putting themselves<br />
at great risk by not clearing their personal<br />
data before selling their vehicles<br />
APTS AND COVID-19 30<br />
WE HAVE CONTACT 22<br />
A recent intelligence report reveals how<br />
Effective contact tracing is important when<br />
advanced persistent threats are using the<br />
it comes to successfully limiting the spread<br />
coronavirus as a lure<br />
of pandemics. Yet the data that is gathered<br />
could well lead to human rights abuses, if<br />
THE GOOD... AND THE BAD 31<br />
effective safeguards are not put in place to<br />
Confusion around some new technologies<br />
protect the privacy of individuals<br />
is hitting many companies trying to be<br />
compliant with the GDPR<br />
REBALANCING THE BOOKS 32<br />
Awareness around gender diversity in the<br />
HACKERS FOR HIRE 26<br />
cyber security industry is starting to improve,<br />
‘Hacker for hire’ groups are said to be<br />
but there's still a very long way to go<br />
targeting hundreds of thousands of<br />
institutions around the world, including<br />
PRODUCT REVIEWS<br />
advocacy groups, journalists, elected<br />
• Cybereason Mobile 19<br />
officials, lawyers, hedge funds and<br />
• Hornetsecurity 365 Total Protection 29<br />
companies. Can they be stopped?<br />
computing security <strong>Nov</strong>-<strong>Dec</strong> <strong>2020</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk<br />
4
Pragmatic and experienced<br />
risk management professionals<br />
Xcina Consulting provides high quality business and technology risk assurance and<br />
advisory services, which only comes from years of experience in our clients’ shoes.<br />
We help to ensure an organisation’s key risks are appropriately managed; its processes<br />
and controls are robust and fit for purpose; it remains compliant with legislation<br />
and regulation and wherever feasible it leverages industry standards as part of<br />
good practice.<br />
Accredited by the Payment Card Industry’s Security Standards Council as a Qualified<br />
Security Assessor (QSA) company and a British Standards Institution (BSI) platinum<br />
member for the provision of services related to ISO27001 (Information Security) and<br />
ISO22301 (Business Continuity).<br />
All our consultants have 10+ years minimum experience and have held senior level<br />
positions.<br />
Our services can be customised to your needs.<br />
• Business Continuity and Crisis Management<br />
• Data Protection<br />
• Financial Processes & Procedures<br />
• Information Security / Cyber Security<br />
• IT & OT Security<br />
• Payment Card Industry<br />
• Project & Change<br />
• Risk Management<br />
• Control Assurance (ISAE3402 / SSAE18)<br />
• Due Diligence<br />
• Governance<br />
• Internal Audit<br />
• Operational Processes & Procedures<br />
• Process Management<br />
• Regulatory Compliance (finance services)<br />
• Third Party Management<br />
020 3985 8467<br />
www.xcinaconsulting.com<br />
info@xcinaconsulting.com
editor's focus<br />
UNDER SIEGE<br />
NATION-STATE LED CYBER-ATTACKS ARE BEING UNLEASHED ON GOVERNMENTS AT<br />
AN EVER-GROWING RATE. VIGILANCE IS THE KEY TO HINDERING THEIR IMPACT<br />
It was of great concern to see Australia's<br />
government and institutions being<br />
subjected this year to concerted attacks by<br />
sophisticated, state-based cyber hacks. This is<br />
something that has also plagued the UK for<br />
some time now and is an indication of how<br />
hacking is increasingly used to infiltrate<br />
'enemy states', with a view to disrupting how<br />
they function.<br />
Australia Prime Minister Scott Morrison<br />
has revealed that the cyber-attacks were<br />
widespread, covering "all levels of<br />
government", as well as essential services and<br />
businesses. He has been reluctant to identify<br />
any specific state actor and claims no major<br />
personal data breaches had been made,<br />
although others have been quicker to point<br />
the finger, with China alleged to be the most<br />
likely culprit in the eyes of many observers.<br />
Morrison has said that the attacks spanned<br />
"government, industry, political organisations,<br />
education, health, essential service providers<br />
and operators of other critical infrastructure".<br />
The attacks happened over many months<br />
and are not going away, the government<br />
concedes. It is hoping that raising public<br />
awareness by admitting to these breaches will<br />
help businesses to improve their defences.<br />
But the government has also stressed how<br />
this "malicious" activity is being seen right<br />
across the globe, making it far from a unique<br />
problem to Australia. Previously, defence<br />
manufacturers, government contractors<br />
and accounting firms have been among<br />
those to report data breaches.<br />
300-PLUS ATTACKS<br />
In light of the Australian Government<br />
becoming a victim of a nation-state led cyberattack<br />
affecting all levels of government,<br />
Toni Vitale, head of data protection at JMW<br />
Solicitors LLP, had this to say: "No country is<br />
immune to such attacks and, in the UK,<br />
the National Cyber Security Centre<br />
announced at the end of 2019 that it has<br />
defended British organisations against more<br />
than 300 state-backed cyber-attacks.... As in<br />
Australia, the UK central government was the<br />
main focus of the attacks, but other sectors,<br />
such as academia, IT, managed service<br />
providers and transport and health, were<br />
also attacked. The N<strong>CS</strong>C actively takes down<br />
fraudulent websites, which are used<br />
by nation states to gather intelligence and<br />
finance their craft."<br />
Training staff to be vigilant to cyber-attacks<br />
is key, states Vitale. They should be taught to:<br />
Avoid clicking on links, opening<br />
attachments or emails from people you<br />
don't know or companies you don't do<br />
business with<br />
Be vigilant when opening links or<br />
attachments from people you do know<br />
particularly if they are unexpected<br />
Be aware of email spoofing, where an<br />
email arrives from someone you believe<br />
you know, but has unexpected links or<br />
attachments, as these are the most<br />
common methods used by cyberattackers<br />
to gain entry into systems.<br />
06<br />
computing security <strong>Nov</strong>/<strong>Dec</strong> <strong>2020</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
editor's focus<br />
"Well trained staff become your strongest<br />
defence against cyber-attacks, rather than<br />
your weakest link," he adds.<br />
SAFETY FALLS ON EVERYONE<br />
According to Nick Savvides, director of<br />
Strategic Business at Forcepoint, the attacks<br />
that targeted Australia serve as a timely<br />
reminder that cyber security is a serious<br />
issue and affects every aspect of life.<br />
Everybody has a role to play in keeping us<br />
safe from cyber-security threats, he points<br />
out. "Sophisticated threat actors, statebased<br />
threat actors, have significant<br />
capabilities, and do not rest in their efforts<br />
to gain footholds into our systems,<br />
applications and data. It is important that<br />
governments, businesses and individuals<br />
remain vigilant and continue to improve<br />
their cyber-security practices. We have<br />
entered a new era of business and<br />
government, where cyber-attacks pose<br />
an existential threat to business and can<br />
cripple the machinery of government."<br />
The public revelation of the attacks<br />
also acts as a signal to the threat actors<br />
responsible that the government and some<br />
in the private sector are aware of the<br />
attacks, Savvides comments. "Interestingly,<br />
two specific controls, patching internetfacing<br />
systems [protecting the edge<br />
of networks], enforcing multifactor<br />
authentication for users [protecting the<br />
users], were specifically called out by<br />
the defence minister. This indicates that<br />
attackers likely operated sophisticated<br />
targeted phishing campaigns to capture<br />
usernames and passwords from victims<br />
and were possibly in possession of 0-day<br />
vulnerabilities against systems or used<br />
older vulnerabilities on systems that are<br />
difficult to patch."<br />
While Australia has significant capabilities<br />
in cyber-security and an active cyber-security<br />
community, unfortunately not all<br />
organisations are at the same level, with<br />
many organisations simply not having right<br />
capabilities, he says. "We are also struggling<br />
with a skills shortage, with unfilled cybersecurity<br />
roles in every sector; that means<br />
many of the skills end up in the top end of<br />
town and large departments, leaving small<br />
and medium business, and government<br />
agencies exposed."<br />
GEO-POLITICAL TENSIONS<br />
Meanwhile, Tim Wellsmore, Mandiant<br />
Government Solutions, Asia Pacific, points<br />
to the "considerable geo-political tension<br />
occurring at the moment involving Australia<br />
and, from our experience, we know that<br />
state-sponsored cyber threat activity directly<br />
replicates geo-political tensions, so it would<br />
be plausible to assume this reported activity<br />
and announcement is connected".<br />
FireEye is, he adds, aware of the reported<br />
incidents and the type of exploitation of<br />
systems that are occurring, and have seen<br />
only a few related impacts to its customer<br />
base. "However, we are seeing an increasing<br />
focus by both state-sponsored and criminal<br />
cyber threat actors on exploiting Common<br />
Vulnerabilities and Exposures (CVEs) soon<br />
after they are announced publicly when<br />
victims' systems are not patched quickly<br />
enough, and we deal with state-sponsored<br />
threats against our customers on a daily<br />
basis."<br />
The information provided in the Australian<br />
Government A<strong>CS</strong>C advisory on this issue is<br />
very detailed, he notes, "and provides good<br />
guidance and serves as a timely reminder<br />
to ensure organisations maintain vigilance<br />
in the cyber security programs including<br />
the use of patching and multi-factor<br />
authentication in their networks".<br />
As Wellsmore confirms, such threats will<br />
continue, with an inevitable increase in<br />
cyber threat activity as our world becomes<br />
more and more technologically dependent,<br />
and therefore both attractive to outside<br />
infiltrators and increasingly vulnerable to<br />
their growing arsenal of weaponry.<br />
Nick Savvides, Forcepoint: everybody has<br />
a role to play in keeping us safe from<br />
cyber-security threats.<br />
Toni Vitale, JMW Solicitors: training staff<br />
to be vigilant to cyber-attacks is key.<br />
www.computingsecurity.co.uk @<strong>CS</strong>MagAndAwards <strong>Nov</strong>/<strong>Dec</strong> <strong>2020</strong> computing security<br />
07
health monitoring<br />
SHATTERED TRUST<br />
A USER OF A POPULAR HEALTH APP WAS INADVERTENTLY ABLE TO ACCESS DOZENS OF VIDEO<br />
RECORDINGS OF OTHER PATIENTS' CONSULTATIONS, WHICH HAS BEEN BLAMED ON A 'SOFTWARE ERROR'<br />
The Babylon Health data breach, which<br />
allowed users of the GP remote<br />
consultation service to access videos<br />
of other patients' appointments with their<br />
doctor, will be remembered for a long time.<br />
With Covid-19 driving a more remote way of<br />
patients engaging with medics, news of the<br />
breach sent a chill down many a spine.<br />
The issue first came to light on 9 June when<br />
a user announced on Twitter that he had been<br />
able to view about 50 videos of other patients'<br />
appointments. A follow-up check by the firm<br />
revealed that other UK users could also see<br />
others' sessions.<br />
The company’s own investigations had<br />
shown that "three patients, who had booked<br />
and had appointments, were incorrectly<br />
presented with…recordings of other patients'<br />
consultations through a subsection of the<br />
user's profile within the app, but had not<br />
viewed them". Babylon Health also confirmed<br />
that it had resolved what was a 'software<br />
error', rather than a malicious attack, and<br />
had notified regulators.<br />
Babylon allows its members to speak to<br />
a doctor, therapist or other health specialist<br />
via a smartphone video call and, when<br />
applicable, sends an electronic prescription<br />
to a nearby pharmacy. It has more than two<br />
million registered users in the UK.<br />
Aman Johal, director and lawyer of<br />
YourLawyers, says that since the coronavirus<br />
outbreak, there has been a huge increase in<br />
demand for digital healthcare services. "In<br />
2019, just 1% of NHS appointments took<br />
place over video conference. In March this<br />
year, requests for video consultations on the<br />
healthcare app myGP skyrocketed by 1,451%.<br />
With more patients than ever registering<br />
with digital healthcare providers, it's extremely<br />
alarming to hear that a user of the Babylon<br />
Health app was able to access dozens of<br />
confidential video recordings of other<br />
patients' consultations.<br />
More than 2.3 million registered users across<br />
the UK have trusted Babylon with their<br />
confidential health data. The exposure of<br />
private video consultations to third-party users<br />
is not only a failure of doctor-patient<br />
confidentiality, but also a serious breach of the<br />
GDPR. This revelation may shatter consumer<br />
trust in digital healthcare," Johal warns.<br />
Cybersecurity firm Carbon Black estimates<br />
that personal health information is three<br />
times more valuable to hackers than other<br />
identifying information, adds Johal. "This<br />
makes services like Babylon Health lucrative<br />
targets for hackers and are commonly<br />
attacked: a report released by Clearswift<br />
earlier this year revealed that in 2019 almost<br />
two-thirds of healthcare services suffered a<br />
cyber-security incident. Despite the potential<br />
penalties imposed by the ICO in the post-<br />
GDPR era, lessons have clearly not been<br />
learned."<br />
Athough Babylon blamed the breach on a<br />
software error, rather than a malicious attack,<br />
Johal still points to serious shortcomings.<br />
"Software glitches differ from the targeted<br />
cyberattacks we are used to seeing in the<br />
media, but the fact this error originated from<br />
8<br />
computing security <strong>Nov</strong>/<strong>Dec</strong> <strong>2020</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
health monitoring<br />
within the company itself does not make it<br />
any less harmful. All organisations must<br />
ensure they employ systems and procedures<br />
to identify and prevent potential vulnerabilities<br />
being exposed, including staff training."<br />
LITMUS TEST<br />
"These past few months have been<br />
unprecedented in lots of ways, with many<br />
new working practices thrust upon businesses<br />
that were generally unprepared to such<br />
sudden changes," says Steve Jackson, sales<br />
director at Clinical DPO, one of the largest<br />
outsource data protection officer suppliers in<br />
the healthcare sector. "With a very challenging<br />
economic environment ahead of us, many<br />
are saying this is the litmus test for data<br />
protection."<br />
Will it be viewed as too difficult and too<br />
restrictive in the fluid new normal business<br />
environment, does he think? "Not necessarily.<br />
With many businesses now capturing clinical<br />
data about their staff and their customers, in<br />
order to protect both from COVID-19, CDPO<br />
has received many calls from clients now<br />
seeing the importance of data usage in a firsthand<br />
way and, with that, a new appreciation<br />
to the risk to data posed by many of these<br />
new working practices."<br />
GDPR COMPLEXITIES<br />
So, why has it taken such a dramatic event to<br />
have organisations reassess their own attitude<br />
to data and to their own risk regarding<br />
potential brand and financial exposure?<br />
"The answer lies in a cursory review of the<br />
two years plus since the introduction of<br />
GDPR," states Jackson. "This new legislation<br />
brought a wave of products encouraging<br />
businesses to buy a flat-packed tick-box data<br />
protection compliance solution and today we<br />
are still told by organisations that they have<br />
'completed their GDPR', not appreciating that<br />
GDPR is not a one-time project, but, much<br />
like financial accounting requirements or<br />
HR, data protection must be integrated into<br />
the organisation, so it becomes part of the<br />
company DNA and embedded into 'business<br />
as usual'."<br />
How exactly can this be achieved? "GDPR<br />
introduced a mandated approach to the<br />
appointment of a DPO for organisations<br />
processing large-scale health data," according<br />
to Jackson. "A glance at the ICO's public<br />
register, however, indicates that many<br />
organisations both large and small are still<br />
to appoint a DPO. The single greatest reason<br />
that we see for this lack of appetite for<br />
change is a lack of time that business allocates<br />
to effect this change."<br />
Many data protection issues are not simply<br />
data problems, he adds - they often arise<br />
from an organisation's governance and<br />
culture, as well as operational decisionmaking,<br />
"whether it be understanding the<br />
need, implementing the correct resource<br />
or service, or, as we have seen on many<br />
occasions as an outsourced DPO service,<br />
taking the time to implement the processes<br />
and support being provided by the DPO".<br />
There are no silver bullet solutions, Jackson<br />
concludes. "However, embedding data<br />
protection by design is better in the long<br />
run, but a business must engage to effect<br />
this change. Until this is accepted and<br />
understood, data protection will only<br />
remain on the periphery of a business."<br />
INADEQUATE TESTING?<br />
The root cause of the Babylon Health breach<br />
has never been fully disclosed, but may be<br />
attributed to inadequate testing of the new<br />
feature before moving it into a production<br />
environment, suggests Rob Treacey, MD; cohead<br />
of Xcina Consulting and Shearwater<br />
Group DPO. "Although it seems that Babylon<br />
Health has tried to downplay the significance<br />
of the exposure and remediated it in a timely<br />
manner, such breaches can have an adverse<br />
impact on an organisation."<br />
It remains to be seen whether Babylon<br />
Health will experience any longer-lasting<br />
reputational damage or if it will be able to<br />
fully recover from such a breach, he adds.<br />
"However, one thing is for certain: users will<br />
be more cautious about using the App in<br />
future or may simply refuse to use it<br />
altogether, especially if they have an<br />
alternative."<br />
CONFIDENCE AND TRUST<br />
As Treacey points out, end users need to<br />
have absolute confidence and complete trust<br />
in an organisation's ability to safeguard their<br />
personal data, especially where that involves<br />
sensitive personal data.<br />
"As a risk management consultancy that<br />
performs regular reviews and audits of our<br />
clients, we see such process and control<br />
weaknesses within the software development<br />
lifecycle as not uncommon." These are<br />
normally the result of:<br />
Failure to adequately test and sign off<br />
software updates or upgrades before<br />
release into a production environment<br />
Lack of oversight by organisations that<br />
outsource their software development<br />
to third parties<br />
Lack of awareness by developers and<br />
testers around the latest software security<br />
risks and vulnerabilities, such as injection,<br />
security misconfigurations, sensitive data<br />
exposure and authentication<br />
ssoftware design or architecture that is<br />
inadequate<br />
Cutting corners, due to the pressure to<br />
release software updates or upgrades<br />
against tight deadlines.<br />
"Any organisation that experiences a data<br />
breach, due to a software weakness or any<br />
related software processes and controls,"<br />
he says, "is merely putting itself in the shop<br />
window for a future cyber-attack, not<br />
to mention any subsequent fine from a<br />
supervisory authority. Some organisations<br />
may be able to minimise their reputation<br />
damage or loss of users, but others may be<br />
less fortunate".<br />
www.computingsecurity.co.uk @<strong>CS</strong>MagAndAwards <strong>Nov</strong>/<strong>Dec</strong> <strong>2020</strong> computing security<br />
9
health monitoring<br />
Kelvin Murray, Webroot: the healthcare<br />
industry is at particular risk of cyber-attacks<br />
and data breaches<br />
Steve Jackson, Clinical DPO: there's an<br />
appreciation of the risk to data posed by<br />
many of the new working practices.<br />
KEY QUESTIONS<br />
"Anyone who develops an app that handles<br />
sensitive customer data should ask themselves<br />
two important questions - is it secure and is it<br />
really necessary?" advises Kelvin Murray, senior<br />
threat researcher at Webroot. "We're seeing<br />
that breaches such as these are all too<br />
common and anyone looking to save time<br />
and money by moving to a digital system<br />
should take risks such as these into<br />
consideration.<br />
"Companies that hold private information<br />
should also ensure they have clearly defined<br />
security policies and procedures to avoid the<br />
leak of information. This starts with employee<br />
education, which underscores all effective<br />
cybersecurity and data protection strategies<br />
and comprehensive best practice guides are<br />
critical to protecting information, especially<br />
when holding sensitive data on customers.<br />
"This is especially important in the healthcare<br />
industry, which is at particular risk of cyberattacks<br />
and data breaches, as information<br />
such as health records is very valuable to<br />
criminals. It will always command high<br />
prices on the dark web, as it can be used<br />
for criminal activities such as fraud, extortion<br />
and in the drug trade."<br />
NO ACTION<br />
And the outcome of the breach at Babylon<br />
Health? It will face "no further action", the<br />
ICO) has since confirmed.<br />
"When a data incident occurs, we would<br />
expect an organisation to consider whether it<br />
is appropriate to contact the people affected,<br />
and to consider whether there are steps<br />
that can be taken to protect them from any<br />
potential adverse effects,” a spokesperson<br />
said. “Babylon Health reported an incident to<br />
us. After looking at the details, we provided<br />
Babylon with detailed advice and concluded<br />
no further action was necessary."<br />
The ICO had the power to fine Babylon<br />
Health up to 4% of its worldwide annual<br />
turnover, while the affected patients might<br />
yet be entitled to claim compensation.<br />
RACE TO TRACE<br />
Concerns that digital tracing systems for<br />
COVID-19 could become 'back doors' to<br />
mass surveillance have already mounted,<br />
with academics from 26 countries issuing<br />
a warning that contact-tracing apps could<br />
hamper trust. Confirming you have been<br />
infected with coronavirus requires personal<br />
data to be submitted, recorded, exchanged<br />
and stored, with some apps, like the UK<br />
government's NHSX, indicating that it may be<br />
stored and used for future research purposes.<br />
But with backing as part of the European<br />
Open Science Cloud (EOSC) - a far-reaching<br />
initiative that is changing the way in which<br />
European research is conducted, with<br />
researchers quickly developing instant<br />
diagnoses for major diseases and tackling<br />
climate change - a small research team has<br />
been able to respond rapidly to the pandemic<br />
and develop a contact-tracing app in the<br />
space of a few months.<br />
TIPPING THE BALANCE<br />
This app - called Tracing Ireland's Population<br />
(TIP) - gives users ownership of their data,<br />
places them in full control of any track and<br />
tracing (rather than an automated program<br />
collecting and storing your information to be<br />
used at a later date), and hosts all information<br />
in encrypted form.<br />
"Alexa will invade your privacy more than<br />
our app does," claims co-creator Dr Paul<br />
Byrnes. "Like many contact-tracing systems<br />
hoping to end blanket lockdowns by<br />
providing an accurate, targeted picture of<br />
infections, our new facility looks set to enable<br />
smaller, localised restrictions.<br />
"The success of any contact-tracing app<br />
depends on whether people will engage with<br />
it and, if they don't trust it, they won't use it,"<br />
comments Byrnes. "It's that simple. Once the<br />
pandemic is over, all data will be erased."<br />
10<br />
computing security <strong>Nov</strong>/<strong>Dec</strong> <strong>2020</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
smishing<br />
SMISH, SMASH, BASH!<br />
A RELATIVELY NEW SPIN ON PHISHING HAS ENTERED THE LEXICON, IN THE FORM OF 'SMISHING'.<br />
BUT WHAT IS THAT EXACTLY AND HOW DANGEROUS MIGHT IT BE TO THE UNSUSPECTING?<br />
Phishing scams have become an all<br />
too familiar weapon used against<br />
businesses and individuals, and are<br />
a type of fraud that can come in many<br />
different forms. These scams not only<br />
employ various online techniques, such<br />
as fake emails and pop-up ads, but can<br />
also include phone calls. Often, the<br />
people behind these scams use fear<br />
tactics, in order to get their victims to take<br />
the bait. As Norton points out: "Phishing<br />
is essentially an online con game, and<br />
phishers are nothing more than tech-savvy<br />
con artists and identity thieves. They use<br />
spam, malicious websites, email messages<br />
and instant messages to trick people<br />
into divulging sensitive information."<br />
Banking information, along with credit<br />
card accounts, usernames and passwords,<br />
are just some of the information phishers<br />
seek to exploit.<br />
And now we have 'smishing' to contend<br />
with. For those who are yet to encounter<br />
this form of attack, here are some of its<br />
hallmarks. "Put simply, smishing is any<br />
kind of phishing that involves a text<br />
message. Often times, this form of<br />
phishing involves a text message in an<br />
SMS or a phone number," states Norton.<br />
Smishing is particularly scary, it adds,<br />
because quite often people tend to be<br />
more inclined to trust a text message than<br />
an email. Most people are aware of the<br />
security risks involved with clicking on<br />
links in emails. This is less true when it<br />
comes to text messages.<br />
Smishing uses elements of social<br />
engineering to get people to share their<br />
personal information. "This tactic<br />
leverages your trust, in order to obtain<br />
your information. The information a<br />
smisher is looking for can be anything<br />
from an online password, to your Social<br />
Security Number, to your credit card<br />
information. Once the smisher has that,<br />
they can often start applying for new<br />
credit in your name. That's where you're<br />
really going to start running into<br />
problems."<br />
Another option used by smisher is to say<br />
that, if you don't click a link and enter<br />
your personal information, that you're<br />
going to be charged per day for use of<br />
a service. "If you haven't signed up for the<br />
12<br />
computing security <strong>Nov</strong>/<strong>Dec</strong> <strong>2020</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
smishing<br />
service, ignore the message," advises<br />
Norton. "If you see any unauthorised<br />
charges on your credit card or debit card<br />
statement, take it up with your bank.<br />
They'll be on your side."<br />
HOW TO KNOW IF YOU'RE<br />
BEING SMISHED<br />
In general, don't reply to text messages<br />
from people you don't know. That's the<br />
best way to remain safe. "This is especially<br />
true when the SMS comes from a phone<br />
number that doesn't look like a phone<br />
number, such as a '5000' phone number.<br />
This is a sign that the text message is<br />
actually just an email sent to a phone.<br />
You should also exercise basic precautions<br />
when using your phone. Don't click on<br />
links you get on your phone, unless you<br />
know the person they're coming from.<br />
Even if you get a text message with a link<br />
from a friend, consider verifying they<br />
meant to send the link before clicking<br />
on it. A full-service Internet security suite<br />
isn't just for laptops and desktops. It also<br />
makes sense for your mobile phone.<br />
A VPN such as Norton Secure VPN is<br />
also one advisable option for your mobile<br />
devices. This will secure and encrypt any<br />
communication taking place between<br />
your mobile and the Internet on the<br />
other end. "Never install apps from text<br />
messages. Any apps you install on your<br />
device should come straight from the<br />
official app store. These programs have<br />
vigorous testing procedures to go through<br />
before they're allowed in the marketplace.<br />
Err on the side of caution. If you have any<br />
doubt about the safety of a text message,<br />
don't even open it."<br />
Almost all of the text messages that you<br />
get are going to be totally fine. However,<br />
it only takes single rogue message to<br />
compromise your security. With just a<br />
little bit of common sense and caution,<br />
you can make sure that you don't become<br />
a victim of identity theft.<br />
WHAT SMISHERMEN USE AS BAIT<br />
As Kapsersky Labs points out, texting is<br />
the most common use of smartphones -<br />
and so a rich source of pickings for<br />
smishers. Experian found that adult<br />
mobile users aged 18 to 24 send more<br />
than 2,022 texts per month-on average,<br />
that's 67 per day-and receive 1,831.<br />
"A couple of other factors make this a<br />
particularly insidious security threat,"<br />
warns Kaspersky. "Most people know<br />
something of the risks of email fraud.<br />
You've probably learned to be suspicious<br />
of emails that say 'Hi-check out this cool<br />
link' and don't contain an actual personal<br />
message from the supposed sender.<br />
"When people are on their phones, they<br />
are less wary. Many assume that their<br />
smartphones are more secure than<br />
computers. But smartphone security has<br />
limitations and cannot directly protect<br />
against smishing. As noted by WillisWire,<br />
cybercrime aimed at mobile devices is<br />
rocketing, just as mobile device usage is.<br />
However, while Android devices remain<br />
the prime target for malware-simply<br />
because so many of them are out there;<br />
and the platform offers greater flexibility<br />
for customers (and cybercriminals!)-<br />
smishing, like SMS itself, works crossplatform.<br />
This puts iPhone and iPad users<br />
at particular risk, because they often feel<br />
they are immune to attack."<br />
Although Apple's iOS mobile technology<br />
has a good reputation for security, no<br />
mobile operating system can by itself<br />
protect you from phishing-style attacks,<br />
argues Kaspersky. "Another risk factor is<br />
that you use your smartphone on the go,<br />
often when you're distracted or in a hurry.<br />
This means that you're more likely to get<br />
caught with your guard down and thus<br />
respond without thinking, should you<br />
receive a message asking for bank<br />
information or to redeem a coupon."<br />
The good news is that the potential<br />
ramifications of these attacks are easy to<br />
protect against. In fact, you can keep<br />
yourself safe by doing nothing at all.<br />
"The attack can only do damage if you<br />
take the bait."<br />
No financial institution or merchant<br />
will send you a text message asking you<br />
to update your account information or<br />
confirm your ATM card code, reiterates<br />
Kaspersky. "If you get a message that<br />
seems to be from your bank or a<br />
merchant you do business with, and it<br />
asks you to click on something in the<br />
message, it's a fraud. Call your bank or<br />
merchant directly, if you are in any doubt.<br />
Remember that, like email phishing,<br />
smishing is a crime of trickery - it depends<br />
on fooling the victim into cooperating by<br />
clicking a link or providing information.<br />
Indeed, the simplest protection against<br />
these attacks is to do nothing at all."<br />
As technology has developed and<br />
evolved, the ways in which scammers try<br />
to target people has developed with it,<br />
comments the Financial Ombudsman<br />
Service (FOS). "From fake websites to<br />
text messages that appear to be from<br />
a legitimate source, scammers will<br />
try a variety of ways to get personal<br />
information from you, in order to take<br />
money from your accounts, use the details<br />
you share to pretend to be you, or to sell<br />
on. As well as use of technology, we also<br />
see scammers trying to manipulate or<br />
exploit situations to build trust or create<br />
panic, to try to get people to divulge<br />
information over the phone, and<br />
sometimes even face to face.<br />
MULTIPLE TARGETS<br />
The FOS sees a wide variety of<br />
circumstances in the complaints that<br />
are referred to it and not just related to<br />
banking - "we know that fraudsters also<br />
look to target pensions, investments and<br />
insurances, too". The industry regulator,<br />
the FCA, has information on its website<br />
about avoiding investment and pension<br />
www.computingsecurity.co.uk @<strong>CS</strong>MagAndAwards <strong>Nov</strong>/<strong>Dec</strong> <strong>2020</strong> computing security<br />
13
smishing<br />
scams, while the Association of British<br />
Insurers offers tips on how to avoid<br />
insurance-related scams.<br />
"It's particularly important to be vigilant<br />
at the moment, as a major event like<br />
the Covid-19 (coronavirus) outbreak can<br />
lead to new types of scams emerging,"<br />
cautions the FOS .It cites how Action<br />
Fraud, the UK reporting centre for fraud<br />
and cyber-crime, has recently reported<br />
an increase in Covid-19 related fraud and<br />
scams, especially with so many people<br />
are remotely and from home - and hence<br />
more exposed and vulnerable.<br />
For those whose minds are buckling<br />
from the overload of scamming terms in<br />
circulation, Webroot has tried to simplify<br />
the process. "If you're at all concerned<br />
with the latest techniques cybercriminals<br />
are using to defraud their victims, your<br />
vocabulary may be running over with<br />
terms for the newest tactics," it says.<br />
"Here's a brief refresher to help keep<br />
them straight."<br />
MANY WEAK POINTS<br />
Smishing, as described above, uses text<br />
messages to extract the sought-after<br />
information<br />
Vishing is when a fraudulent actor<br />
calls a victim pretending to be from<br />
a reputable organisation and tries to<br />
extract personal information, such as<br />
banking or credit card information<br />
Phishing is any type of social<br />
engineering attack aimed at getting a<br />
victim to voluntarily turn over valuable<br />
information by pretending to be<br />
a legitimate source. Both smishing and<br />
vishing are variations of this tactic.<br />
Webroot has singled out the following<br />
smishing techniques to watch out for:<br />
Sending a link that then triggers the<br />
downloading of a malicious app. Clicks<br />
can trigger automatic downloads on<br />
smartphones, the same way they can on<br />
desktop internet browsers. In smishing<br />
campaigns, these apps are often<br />
designed to track your keystrokes, steal<br />
your identity, cede control of your phone<br />
to hackers or encrypt the files on your<br />
phone and hold them for ransom<br />
Linking to information-capturing forms.<br />
In the same way many email phishing<br />
campaigns aim to direct their victims to<br />
online forms, where their information<br />
can be stolen, this technique uses text<br />
messages to do the same. Once a user<br />
has clicked on the link and been<br />
redirected, any information entered into<br />
the form can be read and misused by<br />
scammers<br />
Targeting users with personal<br />
information. In a variation of spear<br />
phishing, committed smishers may<br />
research a user's social media activity, in<br />
order to entice their target with highly<br />
personalised bait text messages. The end<br />
goal is the same as any phishing attack,<br />
but it's important to know that these<br />
scammers do sometimes come armed<br />
with your personal information to give<br />
their ruse a real feel.<br />
Referrals to tech support. Again, this is a<br />
variation on the classic tech support scam<br />
or it could be thought of as the 'vish via<br />
smish'. An SMS message will instruct the<br />
recipient to contact a customer support<br />
line via a number that's provided. Once<br />
on the line, the scammer will try to pry<br />
information from the caller by pretending<br />
to be a legitimate customer service<br />
representative.<br />
The ultimate message is to treat more<br />
or less everything as suspect, until it's<br />
proved it isn't. That way, your chances<br />
of staying 'unsmished, unvished and<br />
unphished' will be significantly increased.<br />
14<br />
computing security <strong>Nov</strong>/<strong>Dec</strong> <strong>2020</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
masterclass<br />
OPEN-AND-SHUT CASE<br />
BEING OPEN TO ETHICAL DISCLOSURE IS VITAL, STATES PAUL RITCHIE,<br />
MANAGING SECURITY CONSULTANT, PENTEST LIMITED<br />
As a young and idealistic ethical<br />
hacker, I wanted to help fix the<br />
online world, to make it a better<br />
and more secure place for everyone.<br />
Ethical disclosure was one of the ways<br />
I thought I could make a difference.<br />
After all, having folks willing to<br />
investigate your security for free, and<br />
then tell you about the issues, seemed<br />
like it would be highly beneficial and<br />
warmly welcomed. It wasn't.<br />
Ethical disclose circa 2005-2010 was<br />
an absolute horror show. First, it was<br />
difficult to find someone to talk to<br />
within an organisation. When you<br />
did find someone, you would have to<br />
clarify what the problem was, explain<br />
that you were not attacking them (very<br />
important), that this was a friendly<br />
'head's up' and that you wouldn't be<br />
sharing the secrets with anyone. I do<br />
not miss the sweaty palms while waiting<br />
to see if it was going to be "thanks for<br />
info!" or "here's another lawyer's letter.<br />
Cease & Desist!" It was usually the latter.<br />
At the time, I was baffled by how<br />
communications like this could result<br />
in such action. It seemed hard to justify<br />
when the bad guys were targeting you<br />
and not telling you anything, whilst the<br />
good guys, the ones pointing out your<br />
vulnerabilities, were getting legal<br />
threats.<br />
As I've matured, I can see the layers<br />
of pressure which could generate such<br />
a response, but things are getting better.<br />
Bug bounty programs have helped<br />
a great deal and it's fantastic to see<br />
organisations make better use of the<br />
information security community, but<br />
they aren't for everyone.<br />
Even if bug bounties aren't for you,<br />
there is still an opportunity that you<br />
can benefit from ethical disclosure and<br />
I have seen it done extremely well by<br />
several organisations over the years.<br />
So, what can you learn from these<br />
companies, if you wish to reap the<br />
benefits of ethical disclosure?<br />
First, identify a point of contact<br />
who will be responsible for inbound<br />
disclosures and give them the<br />
information they need to effectively<br />
triage reports. This could include<br />
a risk register (even if it is just on a<br />
spreadsheet) and an up-to-date list of<br />
assets, showing who is responsible for<br />
each asset and how to contact them.<br />
You may even want to estimate the<br />
value of the assets to your business,<br />
thereby allowing the person responsible<br />
for triaging to prioritise their efforts.<br />
Secondly, make disclosure contact<br />
details visible and create a PGP key to<br />
ensure reports can be sent securely.<br />
This will give researchers the confidence<br />
that reports will be taken seriously and<br />
provide them with a direct route by<br />
which to disclose their findings.<br />
Thirdly, don't make legal threats your<br />
default position. Draw up a disclosure<br />
policy and have this on your website.<br />
This will help outline what reporters<br />
Paul Ritchie, Managing Security<br />
Consultant, Pentest Limited.<br />
can expect from you. This can also set<br />
out the ground rules for disclosure,<br />
especially what you can/cannot be<br />
looking in to. If a report is in breach<br />
of this policy, then, yes, legal 'cease<br />
and desist' letters can be used.<br />
Finally, acknowledge reporters where<br />
you can. This doesn't have to be a<br />
monetary reward; it can be as simple<br />
as acknowledging the reporter on your<br />
website.<br />
These steps often require minimal<br />
effort, but they can be extremely<br />
beneficial and it's a great starting point<br />
for improving your cyber maturity.<br />
www.computingsecurity.co.uk @<strong>CS</strong>MagAndAwards <strong>Nov</strong>/<strong>Dec</strong> <strong>2020</strong> computing security<br />
15
industry insights<br />
THE NEW ORDER<br />
IS NOW THE PERFECT TIME TO GET YOUR (I.T.) HOUSE IN ORDER?<br />
PAUL HARRIS, MANAGING DIRECTOR, PENTEST, OFFERS HIS THOUGHTS<br />
There's a lightbulb in the bathroom<br />
at home that's been burnt out for<br />
about eight months. It's always been<br />
on the list of things to fix, but I've either<br />
forgotten about it when at the shops or<br />
had more pressing things to do; after all,<br />
it wasn't really a big deal, especially when<br />
there are plenty of other bulbs working in<br />
the bathroom.<br />
I say 'wasn't' a big deal, as things<br />
changed. Lockdown happened.<br />
Spending all your time at home makes<br />
you more aware of the small, and not so<br />
small, jobs that need to be done around<br />
the house. Previously insignificant home<br />
improvement jobs start to play on your<br />
mind. The clock on the oven is out by<br />
three minutes, the living room door isn't<br />
quite sitting correctly, there's a small<br />
crack in one of the bathroom tiles, one<br />
of the kitchen chairs has been wobbly for<br />
years. Things you could easily dismiss and<br />
ignore before suddenly start to play on<br />
your mind, growing until they become<br />
critical issues. It's no surprise that people<br />
were queuing outside Ikea for over two<br />
hours on the first day after lockdown was<br />
eased. (To clarify, I wasn't one of them!)<br />
I usually go to great lengths to avoid<br />
doing the home improvement jobs,<br />
hence why the lightbulb has been out for<br />
so long, but during lockdown they have<br />
often given me a welcome distraction<br />
from what's going on in the outside<br />
world. I've even got around to tackling<br />
the big jobs, the ones I really hate, like<br />
cleaning out the garage.<br />
Paul Harris, managing director, Pentest.<br />
It's amazing the stuff you find when you<br />
do that: old games consoles you've not<br />
16<br />
computing security <strong>Nov</strong>/<strong>Dec</strong> <strong>2020</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
industry insights<br />
seen in years, records that you never<br />
knew you had, a million and one Allen<br />
keys, an assortment of sports equipment,<br />
the traditional tin of Quality Street from<br />
the 80s, now containing screws and wall<br />
plugs, cables, and lots and lots of<br />
electronic wires and cables. Whilst some<br />
of this stuff is useful, most of it will either<br />
end up at the charity shop or the tip, but<br />
at the end of it all there's a great sense<br />
of satisfaction that you know where<br />
everything is and that everything is in<br />
order (for now at least).<br />
Organisations aren't so different and<br />
it's easy to collect a host of information<br />
technology 'stuff'. It's even easier to lose<br />
track of this technology as time goes on -<br />
especially as the company grows and<br />
people move on, vital knowledge can<br />
easily get lost along the way.<br />
But when it comes to organisations,<br />
the consequences of not knowing what<br />
you have or how it may be connected<br />
to the outside world can be dangerous,<br />
providing malicious threats with a<br />
potential way into your networks.<br />
KNOWING WHAT YOU HAVE<br />
One of the fundamental IT security<br />
challenges within organisations,<br />
especially larger ones, is the shadow IT<br />
'visibility gap' between assumed or known<br />
infrastructure and what actually exists.<br />
Understanding this is a first vital step in<br />
developing a robust security posture for<br />
an organisation. After all, if you don't<br />
know a legitimate device or application<br />
exists on your network, how can you<br />
properly defend it? Similarly, if you are<br />
missing legitimate devices, you may also<br />
be missing unauthorised devices. Could<br />
any of these anonymous devices provide<br />
backdoors into the network, and perhaps<br />
leave your infrastructure exposed and<br />
vulnerable?<br />
"But I know exactly what I have on my<br />
network," I hear you say. Well, you'd be<br />
surprised. There have been plenty of<br />
cases where we have heard this, only<br />
to discover an unknown device or<br />
application on a network during an estate<br />
discovery investigation, whether it be<br />
a legacy server situated at a remote site, a<br />
website that has been put online as a test<br />
by an internal department, an IoT device<br />
plugged into your network by a member<br />
of staff, IT infrastructure inherited as part<br />
of an acquisition or an application that<br />
was meant to be internal, but is available<br />
to the internet. It can be hard to have<br />
a full oversight on what's truly sitting on<br />
your network.<br />
ASSESS THE RISK, PROTECT OR GET RID<br />
Like the stuff from my garage, once you<br />
know what you have, you need to decide<br />
whether it's still needed. If it is useful to<br />
the organisation, then you'll need to take<br />
the necessary steps to conduct an analysis<br />
of the security and data compliance risks,<br />
and to put in place effective measures<br />
that bring it in line with corporate<br />
policies. If it's not useful, then it's best<br />
to remove it from the network and from<br />
external view. But how do you go about<br />
securing a previously unknown device or<br />
application that you wish to keep on the<br />
network? Well, it will all depend on what<br />
you've found and the nature of the data<br />
it stores or processes, but there is one<br />
standard thing you should be checking as<br />
a matter of course. One of the easiest<br />
things you can do to improve security of<br />
a previously unknown device or<br />
application on your network is to make<br />
sure you have up-to-date versions of<br />
software where possible. If a device or<br />
application is running on an old version<br />
of software, then it is highly likely there<br />
will be security flaws present. Attackers<br />
are all too aware of the security<br />
vulnerabilities within unpatched software,<br />
meaning these could be potentially used<br />
to gain entry to a network and to<br />
ultimately exploit your organisation.<br />
STARTING WITH A CLEAN HOUSE<br />
There is no doubting that the coronavirus<br />
situation has been terrible. As businesses<br />
and as a society, we are likely to face<br />
more turbulence as we ease back towards<br />
normality, however that normal may look.<br />
But before the stresses, strains and<br />
busyness of this new 'normal' take over,<br />
I would argue that now is the perfect<br />
opportunity to step back, to take a look<br />
at some of the jobs we've always put off<br />
and to prepare our organisations for<br />
better times ahead.<br />
Gaining a full understanding of your IT<br />
estate should be considered one of these<br />
vital jobs and, as a company, we've seen<br />
first-hand that it's a job that many<br />
organisations have put off over the years.<br />
Yes, you want to be doing something<br />
more exciting, but it's not as painful as<br />
you may think; we do all the leg work for<br />
our clients. And, unless you know what<br />
you have and what the risks are, you<br />
won't be able to gain the peace of mind<br />
that your network is as secure as possible.<br />
www.computingsecurity.co.uk @<strong>CS</strong>MagAndAwards <strong>Nov</strong>/<strong>Dec</strong> <strong>2020</strong> computing security<br />
17
mergers & acquisitions<br />
HITTING THE SWEET SPOT<br />
DIGITAL TRANSFORMATION IN THE CYBER-SECURITY SECTOR IS FORECAST TO BE THE BIG DRIVER<br />
FOR MERGERS & ACQUISITIONS (M&A) AND INVESTMENT FOR THE REST OF <strong>2020</strong><br />
Ben Kolada has been apppointed ICON's<br />
head of US Tech Investment Banking.<br />
Technology-focused investment bank ICON<br />
Corporate Finance believes that digital<br />
transformation across all industry sectors<br />
has accelerated to become the most pressing<br />
priority for organisations in the aftermath of<br />
Covid-19. ICON predicts this will drive future<br />
growth and appetite for acquisition of tech<br />
companies worldwide, particularly in the<br />
cyber-security sector.<br />
Its assessment is underpinned by a recent<br />
ICON survey of some of the most active UK<br />
M&A buyers. This showed that there has been<br />
no drop in appetite for acquisition in the tech<br />
sector in <strong>2020</strong>, which remains high, with key<br />
areas for expansion expected to be in cyber<br />
security, fintech, Cloud, managed services,<br />
healthtech, AI (artificial intelligence) and<br />
enterprise software.<br />
As organisations adapt to new ways of<br />
working, companies in the US tech market will<br />
continue to be amongst the most acquisitive,<br />
as they continue to seek out deep tech and<br />
disruptive young companies that are reshaping<br />
the world. To capitalise on future growth in the<br />
sector and US market appetite, ICON has<br />
extended its footprint into the region with the<br />
opening of an office in San Francisco. It aims to<br />
bring clients in Europe, Africa and Asia direct<br />
access to the epicentre of the world's tech<br />
community, where appetite for investment and<br />
acquisition in disruptive technology persists. For<br />
US clients, it will present new possibilities in<br />
both domestic and international markets.<br />
With the West Coast central to its future<br />
expansion plans, ICON, which led US-based<br />
IQVIA's acquisition of UK-based Optimum<br />
Contact and JP Morgan's funding of UK-based<br />
Mosaic Smart Data, has appointed former<br />
industry analyst at 451 Research and DataTech<br />
expert Ben Kolada as head of US Tech<br />
Investment Banking. He has more than a<br />
decade of experience in the sector and a deep<br />
knowledge of the West Coast and US markets.<br />
According to Pitchbook Data's Emerging<br />
FinTech research*, increasing cybersecurity<br />
threats are forcing organisations to turn to<br />
technology to mitigate against business<br />
interruption, protecting both systems and<br />
remote workers. This is particularly acute for<br />
financial institutions, where new areas of risk<br />
and regulation have been introduced to<br />
address expanding cyberthreats and data<br />
security concerns.<br />
CEO and founder of ICON, Alan Bristow,<br />
adds: "As the world discovers the new<br />
normal, it is the tech sector that will drive<br />
societal changes and enable new ways of<br />
working. The US West Coast's innovative<br />
approach and its dominance in deals<br />
origination is the core driver for our new<br />
presence in San Francisco. We are excited<br />
to be bringing US markets to Europe's<br />
doorstep and vice versa."<br />
* Pitchbook Data Inc Emerging FinTech<br />
Research Q1 <strong>2020</strong><br />
18<br />
computing security <strong>Nov</strong>/<strong>Dec</strong> <strong>2020</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
product review<br />
CYBEREASON MOBILE<br />
The coronavirus pandemic and its<br />
continuing impact have changed the<br />
threat landscape for ever and only<br />
the most agile organisations will survive.<br />
The huge changes in working practices and<br />
unprecedented surge in cyberattacks have<br />
presented enterprises with tough data<br />
security challenges, making endpoint<br />
protection a critical priority.<br />
Clearly, the focus needs to be on mobiles,<br />
as the balance is shifting sharply away<br />
from traditional devices. It's no surprise<br />
that mobiles are being targeted by a large<br />
percentage of malware, as they present<br />
a lucrative target that can easily provide<br />
a back door into the corporate network.<br />
Cybereason is a specialist in endpoint<br />
protection and it offers an enterprise-class<br />
threat prevention, detection and response<br />
solution, with real-time awareness. It has a<br />
sharp focus on keeping remote workforces<br />
safe and its latest Mobile component delivers<br />
these services to Android and iOS devices.<br />
The Defense Platform applies a layered<br />
approach to endpoint security with<br />
signature-based and AI next-generation<br />
antimalware, application controls and<br />
dynamic behavioural analysis to block<br />
ransomware attacks. It goes beyond<br />
most competing products, as it correlates<br />
seemingly isolated incidents to present<br />
a clear picture of an attack.<br />
Cybereason can analyse up to 8 million<br />
events per second and yet has a remarkably<br />
light touch on the network. It uses small<br />
footprint endpoint sensors, which enforce<br />
local antimalware, collect information and<br />
pass it on to detection servers for analysis<br />
and correlation.<br />
The Mobile component is managed in the<br />
cloud for customers making deployment<br />
a swift process. The Cybereason mobile<br />
app is customised to the organisation's<br />
requirements and can be pushed out using<br />
a wide variety of deployment methods.<br />
Once installed, the app enforces<br />
predefined security policies, so protection<br />
starts immediately. Mobile users enjoy<br />
the same multi-layered prevention as<br />
workstation users, but with additional<br />
security measures, such as SMS phishing<br />
attack negation and app behaviour<br />
analysis.<br />
The Cybereason autonomous protection<br />
app is tamper-proof and constantly<br />
monitors mobile devices in real-time for<br />
suspicious behaviour. When a user installs a<br />
new app, its activities and communications<br />
will be blocked until it is certified as safe<br />
and it will not permit known malicious<br />
apps to be installed.<br />
The app blocks attempts to exploit OS<br />
vulnerabilities and monitors all network<br />
activity, looking for suspicious north-south<br />
connections. It requires no training to use<br />
and interaction with end users is kept to<br />
a minimum, as the app doesn't interfere<br />
with user privacy or their experience,<br />
while its lightweight design ensures it<br />
won't compromise device performance<br />
or battery longevity.<br />
The only time they'll see it is when<br />
malicious activity has been detected. The<br />
app pops up with a yellow screen, if risky<br />
activity has been identified or a red one,<br />
if it considers the device to be at risk and<br />
requiring immediate remedial action,<br />
performed by Cybereason.<br />
The app provides detailed notifications<br />
about security events, such as attempts<br />
to access phishing sites or those known<br />
to harbour malicious content. These<br />
are considered secured events, so the<br />
notifications are informational; but those<br />
such as OS vulnerabilities that need an<br />
update to rectify will be listed as requiring<br />
action.<br />
There's much more going on in the<br />
background, as mobile alerts are sent to<br />
the Defense Platform detection servers for<br />
event correlation. Cybereason provides MDR<br />
(managed detection and response) services<br />
for mobiles where its analyst teams review<br />
events, advise the customer of all security<br />
issues and provide remediation services.<br />
The pandemic has created a whole new<br />
world since it struck, forcing organisations<br />
to rapidly reassess their security posture.<br />
Mobile security is now an essential<br />
ingredient for survival, and Cybereason<br />
delivers a sophisticated threat protection<br />
solution that fills the gaps that legacy<br />
endpoint protection solutions leave behind.<br />
Product: Cybereason Mobile<br />
Supplier: Cybereason<br />
Telephone: 0203 036 0974<br />
Web site: www.cybereason.com<br />
www.computingsecurity.co.uk @<strong>CS</strong>MagAndAwards <strong>Nov</strong>/<strong>Dec</strong> <strong>2020</strong> computing security<br />
19
Data privacy<br />
BEYOND THE EU-US PRIVACY SHIELD:<br />
WHAT'S NEXT FOR EUROPEAN ENTERPRISES?<br />
A NEW RULING HAS SHAKEN UP HOW THE EU AND U.S. REGARD DATA PROTECTION AND DATA PRIVACY<br />
comes to processing and using data, namely:<br />
For more effective monitoring and control<br />
of an entire population<br />
For the pursuit of one's own geopolitical<br />
interests<br />
For the benefit of specific economic<br />
interests<br />
With focus on data protection and the<br />
rights of individuals.<br />
Cloud computing and the networking of a<br />
wide variety of systems mean many European<br />
companies send data streams to the United<br />
States, where the international market leaders,<br />
the so-called 'big players', are based. The ECJ's<br />
ruling means there are many enterprises that<br />
are compelled to act now.<br />
The European Court of Justice (ECJ)<br />
judgment invalidating the EU-US Privacy<br />
Shield has caused uncertainty for many<br />
enterprises and presented them with<br />
challenges on how to handle private data. In<br />
the long term, this ruling offers European<br />
enterprises valuable chances for reassessing<br />
data-driven business models and re-imagining<br />
them in a way that is compliant with the<br />
required protections of personal data. Things<br />
may not be so simple for US enterprises<br />
seeking trade in Europe.<br />
As with its predecessor, the Safe Harbour<br />
Privacy Principles, overturned in 2015, the EU-<br />
US Privacy Shield determined that transferred<br />
data in the United States was not sufficiently<br />
protected under the current EU law (GDPR)<br />
demands. Standard Contractual Clauses,<br />
which constitute the foundation on which<br />
many enterprises transfer data to the USA,<br />
continue to be valid. If, however, it turns out<br />
that, despite these clauses, data protection in<br />
the United States (in real and concrete cases)<br />
does not take place, this last remaining legal<br />
basis will undoubtedly be invalidated as well.<br />
Private digital data is increasingly valuable<br />
and is a highly sought-after resource - 'the<br />
new gold'. There are different motives when it<br />
We asked Cryptshare CEO Mark Forrest to<br />
offer his thoughts on what has transpired:<br />
What are the key takeaways from this ruling?<br />
Mark Forrest: This ruling did not take place in<br />
a vacuum. We are looking at 20 years of<br />
legislation: From the Safe Harbour Privacy<br />
Principles to the EU-US Privacy Shield, the<br />
practice of self-certification had enabled<br />
companies to tick a box and say, "Yes, we<br />
comply". They did not have to prove their<br />
compliance, rather their non-compliance had<br />
to be proven. This practice has now been<br />
ruled invalid.<br />
European legislation demands that privacy<br />
requires specific top priority guidelines. In the<br />
United States, other factors are in the<br />
foreground: National security takes<br />
precedence over data protection concerns,<br />
meaning privacy gets put aside, or is<br />
diminished as a consideration. With this<br />
ruling, there are penalties in place that can be<br />
large for companies that breach the EU<br />
requirements and the case against Facebook<br />
20<br />
computing security <strong>Nov</strong>/<strong>Dec</strong> <strong>2020</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
Data privacy<br />
today's legal reality.<br />
has been re-opened.<br />
The US has a strong national agenda; their<br />
economic interests and national security<br />
concerns don't necessarily align with EU data<br />
protection laws. The question now is how the<br />
US will respond. Will US companies be fined<br />
for violations of GDPR or could US intelligence<br />
agencies be restricted in their access to the<br />
personal data of European citizens? We<br />
should expect some debate; with national<br />
security, it is a two-way street. Data-driven<br />
business with high economic value is more<br />
biased to US interests.<br />
What are the implications for European<br />
enterprises?<br />
MF: Many will look at this and think, "There is<br />
nothing we can do". Most use tools provided<br />
by third parties from outside the enterprise<br />
and there is a high dependency on external<br />
contractors. In today's world, there is no going<br />
back from using office tools, databases,<br />
analytics tool, integrations…it is not only<br />
cloud service providers offering these, and the<br />
biggest players are in the US; in Europe, we<br />
have fewer data-driven businesses, and many<br />
promising EU based technologies and startups<br />
have been acquired in their infancy.<br />
If you remove those tools because US<br />
companies don't meet the required standards<br />
of GDPR, many EU companies can't function<br />
well. European enterprises are required to<br />
comply with all data protection laws, so they<br />
must identify any areas where they don't and<br />
take action. If they fail to do so, they risk<br />
getting dragged into a maelstrom of fines.<br />
The potential financial consequences of this<br />
ruling are huge.<br />
What can enterprises do, in concrete terms?<br />
MF: This ECJ ruling was effective immediately.<br />
So, it is important for enterprises to act now<br />
and mitigate the potential risks. European<br />
companies operating mainly in Europe already<br />
have a high standard to meet, namely the<br />
GDPR; they run into trouble when they<br />
employ the services of companies that don't<br />
comply. European enterprises need to divert<br />
the risks that suppliers can cause for them and<br />
require their compliance with any applicable<br />
EU data protection laws. Eventually, there will<br />
be a new agreement increasing the pressure<br />
on the US to change priority, but until then<br />
businesses must ensure their compliance with<br />
How has Cryptshare reacted to this?<br />
MF: Enterprises must comply the way they<br />
needed to before. For European companies<br />
operating in Europe, we already have a high<br />
standard, which we help companies to meet.<br />
Data is one of today's most valuable assets;<br />
entire business models are built on it.<br />
Therefore, it greatly matters where this data<br />
goes and what happens to it, once it is there.<br />
Enterprises need a product like Cryptshare to<br />
protect their data in transit, and make sure it<br />
remains safe between senders and its<br />
intended recipient, not falling victim to<br />
predators that include data-driven businesses,<br />
bad actors and governments both legitimate<br />
and malign. That is the essence of the ECJ<br />
ruling.<br />
Where can transatlantic data privacy<br />
agreements go from here?<br />
MF: Action is required from all parties;<br />
politicians must draft a new agreement<br />
between the EU and the USA that constitutes<br />
a sustainable and resilient basis for all future<br />
data transfers to the USA, and this must be<br />
done quickly. In order to stand up to the<br />
scrutiny of the ECJ, any agreement must<br />
ultimately meet the data protection<br />
requirements that EU standards demand.<br />
In the United States, other factors are clearly<br />
given priority, namely their economic interests<br />
and their intelligence agencies' wide-reaching<br />
powers to access personal data, regardless of<br />
its origin or location. They have so far shown<br />
little willingness to make concessions to<br />
European data protection laws, should they<br />
come at the expense of their national<br />
interests. It currently seems that it will be up<br />
to Europe to make its own demands for data<br />
protection and data privacy a reality, as the US<br />
seems unwilling to concede ground.<br />
To find out how enterprises can exchange<br />
sensitive messages and files in a secure,<br />
traceable and compliant way, go to:<br />
https://bit.ly/3mU8is1<br />
www.computingsecurity.co.uk @<strong>CS</strong>MagAndAwards <strong>Nov</strong>/<strong>Dec</strong> <strong>2020</strong> computing security<br />
21
contact tracing<br />
WE HAVE CONTACT<br />
THERE IS AN INCREASING RELIANCE ON DATA-DRIVEN TECHNOLOGIES TO HELP CONTAIN COVID-19,<br />
ESPECIALLY THROUGH CONTACT TRACING. BUT MIGHT THESE INFRINGE HUMAN RIGHTS?<br />
All contact tracing apps have one thing<br />
in common: they record when you're<br />
close to someone else (usually in a<br />
way that preserves your privacy) and try to<br />
characterise how close and for how long,<br />
states Ian Levy, in a blog published on the<br />
National Cyber Security Centre website.<br />
In all sensible models, he points out, this<br />
information is held privately on the user's<br />
phone. "The differences start when someone<br />
reports they're ill. Then, the different design<br />
choices and cryptographic models dictate<br />
the public health responses your app can<br />
support." In his blog, Levy uses the word<br />
'anonymous' in its security sense. "That's<br />
different to the definition under GDPR and<br />
other law. The proper legal descriptions of<br />
the data we use are in the Data Protection<br />
Impact Assessments, which will be<br />
published," he continues.<br />
In the first model (known as 'the<br />
decentralised model'), you tell the system<br />
you're ill and give it no extra information.<br />
Periodically, it collects a list of everyone who<br />
has said they're ill and sends it out to all users<br />
of the app. "Individual devices look to see if<br />
any of its local contacts are on the list and<br />
tells their user, if this is the case (subject to<br />
some local risk modelling about the sort of<br />
encounters they had). Notifications will lead<br />
to some health interventions, probably selfisolation<br />
to start with."<br />
Those concerned about failures to protect<br />
individual's privacy have argued that this<br />
decentralised model is the one to follow,<br />
as it gives maximum protection. However,<br />
Levy argues that, "while the health authority<br />
would know the anonymous identity of the<br />
22<br />
computing security <strong>Nov</strong>/<strong>Dec</strong> <strong>2020</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
contact tracing<br />
app that's reported symptoms [or sometimes<br />
perhaps just a Bluetooth broadcast value],<br />
it wouldn't know any of the contacts [even<br />
anonymously] and so won't know anything<br />
about how that user may have spread the<br />
disease". In some systems, he adds, "some<br />
users may be able to donate some aggregate<br />
contact data”. In one instance, he had seen<br />
five people who claimed to be infected', but<br />
nothing could be linked to a particular<br />
contact event, or other user.<br />
CENTRALISED APPROACH<br />
The other model is the 'centralised' one<br />
where an ill user reports their symptoms, but<br />
also gives all their anonymous contacts to<br />
the public health authority, along with some<br />
details about the type of contact they've had<br />
(duration and proximity, for example). "The<br />
health authority can use risk modelling to<br />
decide which contacts are most at risk,<br />
and then notify them to take some action -<br />
again probably self-isolation to start with.<br />
Importantly, the public health authority has<br />
anonymous data to help it understand how<br />
the disease appears to be spreading and has<br />
the anonymous contact graphs to carry out<br />
some analysis."<br />
So, the health authority could discover that<br />
a particular anonymous person seems to<br />
infect people really well. While the system<br />
wouldn't know who they are, encounters<br />
with them could be scored as more risky and<br />
adjust the risk of someone being infected<br />
by a particular encounter appropriately. The<br />
NHS app uses this centralised model, but<br />
also protects your security and privacy<br />
strongly," Levy comments.<br />
While some see technological solutions as<br />
a critical tool for contact tracing, quarantine<br />
enforcement, tracking the spread of Covid-<br />
19 and allocating medical resources, these<br />
practices raise significant human rights<br />
concerns. In fact, Norway's Smittestopp<br />
contact tracing app was suspended in mid-<br />
June, following criticism that it was too<br />
invasive of people's privacy. The criticism<br />
came from the national data protection<br />
agency Datatilsynet, which stated that the<br />
benefits of the app were disproportionate<br />
to the privacy infractions it cost their citizens.<br />
Norway's institute of public health also<br />
agreed to delete all data. Significantly,<br />
Smittestopp used a centralised model of data<br />
collection, which was also being utilised in<br />
the UK and France's contact tracing apps.<br />
WAKE-UP CALL<br />
"Norway's decision to suspend its COVID-19<br />
contact tracing app, due to privacy concerns,<br />
was excellent news for Norwegian citizens<br />
and a wake-up call for other countries<br />
currently using or rolling out similar<br />
centralised contact tracing systems," was<br />
the comment at that time from Ray Walsh,<br />
digital privacy expert at ProPrivacy.<br />
"Norway's Smittestopp app uses<br />
a centralised model of data collection - a<br />
troubling and invasive system identical to<br />
that being used in both France and the UK.<br />
Norway's contact tracing app scored just<br />
1 out of 10 in our in-depth study of<br />
Coronavirus contact tracing apps, making<br />
it one of the most invasive and dangerous<br />
apps in the world. Anytime that data is held<br />
in a centralised database, that data is at<br />
risk of data mismanagement, abuse, leaks<br />
or data breaches. Plenty of countries<br />
have demonstrated that it is possible to<br />
implement a contact tracing system that is<br />
completely decentralised and that does not<br />
unnecessarily put citizens' privacy at risk."<br />
Meanwhile, a team at the Technical<br />
University of Munich (TUM) developed an IT<br />
service that simplified the registration and<br />
contact tracing process, while protecting<br />
personal data. The service was therefore seen<br />
as one that could complement the warning<br />
app launched by the German Ministry of<br />
Health and might also be used at locations<br />
where contact lists are not mandatory.<br />
Still, effective contact tracing is important<br />
for successfully limiting the spread of<br />
pandemics, says Georg Carle, professor of<br />
Network Architectures and Services at TUM.<br />
In search of a solution, he worked with his<br />
former doctoral candidate Johann Schlamp<br />
to develop QRONITON. This service, which<br />
uses QR codes that can be scanned with a<br />
mobile phone, will enable organisations to<br />
meet their documentation obligations and<br />
help public health authorities to identify<br />
endangered individuals quickly. Any location<br />
- whether it's at a restaurant table or an seat<br />
in a lecture hall - can be provided with an<br />
individual QR code. When scanned by a<br />
user, the code is captured along with a time<br />
stamp and contact data. What sets this<br />
solution apart from similar approaches is a<br />
sophisticated, multi-stage encryption system<br />
that protects the data.<br />
RESTRICTED ACCESS<br />
"The data are stored centrally on a server,"<br />
says TUM's Carle. "However, they are<br />
encrypted in a form that cannot be read<br />
by the server operator, and which the<br />
authorities can access only in the form of<br />
subsets - and even then, only with the<br />
consent of the concerned parties." If an<br />
infection with the novel coronavirus<br />
SARS-CoV-2 is reported to a public health<br />
authority, it will provide a personal<br />
authorisation code to the infected individual.<br />
The authority can access data on the places<br />
visited and the direct contact persons only<br />
if the infected person enters the code<br />
in QRONITON. "The principle of data<br />
minimisation was very important to us,"<br />
says Schlamp. "The system captures only a<br />
telephone number and a postal code. The<br />
latter is used to determine which authority<br />
can access the data in case of a concrete<br />
infection risk."<br />
QRONITON is a browser-based tool, which<br />
means that the user does not need to install<br />
an app. It also means that users can be<br />
sure that data are not being collected in the<br />
background. They can decide themselves<br />
whether or how often they wish to scan QR<br />
codes. The developers also had users without<br />
www.computingsecurity.co.uk @<strong>CS</strong>MagAndAwards <strong>Nov</strong>/<strong>Dec</strong> <strong>2020</strong> computing security<br />
23
contact tracing<br />
smartphones in mind: These users can print<br />
out a personal QR code to be scanned by<br />
restaurants and other places they visit.<br />
KEEPING WATCH<br />
Human Rights Watch is equally concerned<br />
about proposals for the use of mobile<br />
location data in the Covid-19 response,<br />
because the data usually contains sensitive<br />
and revealing insights about people's<br />
identity, location, behaviour, associations<br />
and activities. Indeed, mobile location data<br />
programs to combat Covid-19 may not<br />
be scientifically necessary and could lead<br />
to human rights abuses, if they are not<br />
equipped with effective safeguards to<br />
protect privacy. The long history of<br />
emergency actions, such as surveillance<br />
measures put in place to counter terrorism,<br />
shows that they often go too far, fail to<br />
have their desired effect and, once approved,<br />
often outlast their justification, according to<br />
the international watchdog body.<br />
Contact tracing’s goal is, of course, to<br />
interrupt transmission by rapidly identifying<br />
individuals who have been in close contact<br />
of someone who is infected, defined by the<br />
United States Centers for Disease Control<br />
and Prevention (CDC) as within six feet of<br />
someone for approximately 10 or more<br />
minutes. The idea is to encourage such<br />
individuals to isolate themselves from others,<br />
and seek testing and treatment.<br />
Because the coronavirus is primarily<br />
transmitted through person-to-person<br />
contact via respiratory droplets when an<br />
infected person coughs, sneezes or talks,<br />
mobile location data has been advocated in<br />
many quarters as an essential method to<br />
identify potentially exposed individuals.<br />
Companies and governments are also<br />
examining location data in aggregate form<br />
to better understand general patterns of<br />
people's movements and behaviours, and<br />
how these have changed over time. Such<br />
analysis aims to forecast how the virus might<br />
be spreading and the effectiveness of public<br />
health interventions, particularly social<br />
distancing measures, and identify ways to<br />
better allocate testing and medical resources.<br />
RIGHTS & FREEDOMS<br />
Even in times of emergency, when States<br />
restrict human rights for public health<br />
reasons, international human rights law says<br />
that measures taken that limit people's rights<br />
and freedoms must be lawful, necessary and<br />
proportionate. States of emergency need to<br />
be limited in duration and any curtailment<br />
of rights needs to take into consideration<br />
the disproportionate impact on specific<br />
populations or marginalised groups.<br />
These rules apply to efforts to track and<br />
manage Covid-19 using mobile location<br />
data. The collection and analysis of<br />
such data could reveal users' identities,<br />
movements, and associations in a manner<br />
that interferes with the right to privacy.<br />
Article 17 of the International Covenant on<br />
Civil and Political Rights (ICCPR), which is<br />
derived from Article 12 of the Universal<br />
<strong>Dec</strong>laration of Human Rights (UDHR),<br />
establishes "the protection of the law"<br />
against "arbitrary or unlawful interference"<br />
with an individual's "privacy, family, home,<br />
or correspondence." The United Nations<br />
Human Rights Committee has found that<br />
restrictions on the right to privacy must take<br />
place only "in cases envisaged by the law."<br />
Restrictions must also be "proportionate to<br />
the end sought, and ... necessary in the<br />
circumstances of any given case".<br />
In the EU, eight major telcos agreed earlier<br />
this year to share anonymised metadata with<br />
the EC for modelling and predicting the<br />
propagation of the coronavirus. An official<br />
from the commission advised that the data<br />
would be aggregated and anonymised, and<br />
that the commission will delete it when the<br />
pandemic is over. However, and worryingly,<br />
the European Data Protection Supervisor<br />
has previously warned about the possibility<br />
of such measures becoming permanent.<br />
24<br />
computing security <strong>Nov</strong>/<strong>Dec</strong> <strong>2020</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
data disasters<br />
BRAKING BAD!<br />
CAR OWNERS COULD BE PUTTING THEIR PERSONAL DATA AT RISK BY NOT CLEARING<br />
THIS BEFORE SELLING THEIR CARS, ACCORDING TO CONSUMER WATCHDOG WHICH?<br />
AWhich? survey has revealed that<br />
car owners could be putting their<br />
personal information seriously at<br />
risk by failing to clear their data before<br />
selling their cars. In a survey of over<br />
14,000 drivers who sold cars in the<br />
last two years, four in five failed to<br />
wipe information transferred from their<br />
phone, such as contact numbers, home<br />
address and even WiFi passwords, to<br />
their cars before they sold them.<br />
Chris Harris, EMEA technical director<br />
at Thales, has been looking at the clear<br />
dangers of this behaviour, and what<br />
drivers and car manufacturers can do<br />
to stop sensitive data falling into the<br />
wrong hands. "When selling a car, we're<br />
usually quick to remove our possessions -<br />
whether that's CDs, a roof rack, or<br />
personalised seat covers. However,<br />
many of us are failing to remove our<br />
more 'invisible' possessions, and with<br />
cars becoming increasingly connected,<br />
they are swiftly becoming a hotbed<br />
for potentially lucrative sensitive data,<br />
including addresses, recent calls and<br />
birthdays.<br />
"The majority of us wouldn't be<br />
comfortable sharing this kind of<br />
information with complete strangers,<br />
so it's concerning to see consumers<br />
unwittingly hand this data across,"<br />
adds Harris. "Whether you're selling<br />
a car, taking a ride with a friend or<br />
even returning a rental car, it's essential<br />
to practice good data hygiene and<br />
protect your personal data. However,<br />
manufacturers need to be doing more<br />
to ensure data hygiene is easy to practice<br />
and drivers know how to remove this<br />
data."<br />
He offers what he describes as "three<br />
quick tips" for keeping such data safe<br />
when selling your car:<br />
1. When you come to sell your car,<br />
consider all the places where your<br />
personal information may be stored and<br />
find out from the car's manual how to<br />
delete or erase it. Most of us wouldn't<br />
be comfortable sharing our address,<br />
contacts and recent messages with a<br />
complete stranger, but that's effectively<br />
what we're doing by not clearing<br />
sensitive data from our cars.<br />
2. Go through any accounts or apps<br />
that you may have connected to the<br />
vehicle, and ensure you've logged out<br />
and removed any saved data. You won't<br />
want the new owner benefiting from<br />
services you've subscribed to - and, just<br />
as importantly, the new owner probably<br />
won't be too grateful when your app<br />
unknowingly starts to control their new<br />
vehicle.<br />
3. Finally, check for old-school methods<br />
of storing data. Did you have a USB stick<br />
or CD in the glovebox with music you<br />
were playing in the car? What else might<br />
that memory stick have had on it? Even<br />
files you thought you had deleted can<br />
often be recovered from hard drives and<br />
USB sticks.<br />
www.computingsecurity.co.uk @<strong>CS</strong>MagAndAwards <strong>Nov</strong>/<strong>Dec</strong> <strong>2020</strong> computing security<br />
25
hacking surge<br />
HACKERS FOR HIRE<br />
HACKER FOR HIRE GROUPS ARE LEAVING A TRAIL OF DESTRUCTION IN THEIR WAKE. THE RIGHT<br />
CYBER RESILIENCE STRATEGIES MUST BE PUT IN PLACE TO COUNTERACT THIS GROWING THREAT<br />
operators used to disguise the phishing links.<br />
We subsequently discovered that this<br />
shortener was part of a larger network of<br />
custom URL shorteners operated by a single<br />
group [Dark Basin]. Because the shorteners<br />
created URLs with sequential shortcodes, we<br />
were able to enumerate them and identify<br />
almost 28,000 additional URLs containing<br />
email addresses of targets. We used open<br />
source intelligence techniques to identify<br />
hundreds of targeted individuals and<br />
organisations. We later contacted a substantial<br />
fraction of them, assembling a global picture<br />
of Dark Basin's targeting."<br />
Citizen Lab's investigation yielded several<br />
clusters of interest, including two clusters of<br />
advocacy organisations in the United States<br />
working on climate change and net neutrality.<br />
"While we initially thought that Dark Basin<br />
might be state-sponsored, the range of<br />
targets soon made it clear that Dark Basin<br />
was likely a hack-for-hire operation. Dark<br />
Basin's targets were often on only one side of<br />
a contested legal proceeding, advocacy issue<br />
or business deal."<br />
According to a report published by<br />
internet-watching Citizen Lab, hacker<br />
for hire groups are targeting hundreds<br />
of thousands of institutions around the world,<br />
including advocacy groups, journalists, elected<br />
officials, lawyers, hedge funds and companies.<br />
"We give the name 'Dark Basin' to a hackfor-hire<br />
organisation that has targeted<br />
thousands of individuals and organisations<br />
on six continents, including senior politicians,<br />
government prosecutors, CEOs, journalists,<br />
and human rights defenders," states Citizen<br />
Lab. "Over the course of our multi-year<br />
investigation, we found that Dark Basin likely<br />
conducted commercial espionage on behalf<br />
of their clients against opponents involved<br />
in high-profile public events, criminal cases,<br />
financial transactions, news stories and<br />
advocacy."<br />
In 2017, Citizen Lab was contacted by<br />
a journalist who had been targeted with<br />
phishing attempts and asked if it would<br />
investigate. "We linked the phishing attempts<br />
to a custom URL shortener, which the<br />
CYBERCRIME EVOLUTION<br />
What this all too clearly demonstrates is that<br />
cybercrime has evolved and cybercrime-as-aservice<br />
(CAAS) is now a commonplace activity.<br />
"Not so long ago, if one wanted to launch<br />
a distributed denial of service [DDoS] attack,<br />
then one would need to develop the required<br />
malware, push the malware out into the<br />
web, infect enough computers to create a<br />
sufficiently large attack force and then launch<br />
the attack against the desired target domain,"<br />
says Kev Brear, director of consulting -<br />
Technology Risk - Xcina Consulting. "This<br />
was a time-consuming and labour-intensive<br />
process, and it required a fair degree of<br />
26<br />
computing security <strong>Nov</strong>/<strong>Dec</strong> <strong>2020</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
hacking surge<br />
technical expertise to develop the malware<br />
and manage the DDoS attack process."<br />
However, the world of technology has<br />
'progressed' and it is entirely possible to<br />
purchase a DDoS attack from the 'Dark web'.<br />
"One simply has to make contact with one of<br />
the numerous vendors of the services and<br />
specify the target, the magnitude and<br />
duration of the attack, pay the required fee<br />
(usually in crypto-currency) and then one sits<br />
back and observes as the crime unfolds," he<br />
adds. "The DDoS attack will have an associated<br />
service level agreement, but quite how the SLA<br />
is enforced in the event of a disagreement is<br />
currently an opaque area!"<br />
This "commoditisation of cybercrime" now<br />
extends beyond DDoS attacks, states Brear,<br />
and it is possible to purchase ransomware<br />
attacks, targeted hacks, bespoke malware,<br />
phishing email templates, industrial espionage<br />
services, and lists of potential targets for<br />
frauds and extortion attempts. "The other<br />
consequence of the commoditisation of<br />
cybercrime is that traditional criminals can<br />
purchase the required technical solutions to<br />
combine with their criminal prowess, and<br />
produce ever more inventive methods to<br />
defraud and attack people and organisations."<br />
Action Fraud, the UK's dedicated resource<br />
for reporting fraud and cyber-crime, estimated<br />
that UK citizens have already lost around<br />
£16 million from online scams and frauds in<br />
the earlier stages of the UK lockdown. "Also,<br />
the illegal takeover, or compromise, of cloudbased<br />
email accounts is approaching epidemic<br />
proportions and shows no signs of abating<br />
anytime soon," Brear warns.<br />
"Despite the focus on disruption to business<br />
operations created by the Covid-19 crisis, the<br />
traditional challenges created by cybercrime<br />
have not diminished and organisations need<br />
to have in place appropriate protective<br />
measures, security response plans and<br />
business continuity arrangements to maintain<br />
their critical services and functions." What is<br />
clear from these findings is that the range of<br />
threats that organisations face is increasing<br />
and now, more than ever, it's essential that<br />
companies have the right cyber resilience<br />
strategies in place to counteract this growing<br />
threat - which has only been amplified by the<br />
coronavirus pandemic and remote working.<br />
This is supported by another report, published<br />
by cyber security specialist firm Mimecast,<br />
titled 'State of Email Security', which has<br />
detailed some of threats facing businesses<br />
today. The report surveyed 1,025 global IT<br />
decision makers. Some of key findings include:<br />
60% of IT professionals surveyed believed<br />
it's inevitable or likely they will suffer from<br />
an email-borne attack in the coming year<br />
72% of respondents reported an increase<br />
in phishing on their organisations and,<br />
due to the global pandemic, threat actors<br />
are broadly using impersonation and<br />
BEC to steal from unsuspecting users.<br />
Mimecast has found that impersonation<br />
fraud attempts jumped by a staggering<br />
30% from January to April <strong>2020</strong><br />
47% of IT professionals surveyed in the UK<br />
say the volume of email-based spoofing of<br />
customers, vendors or business partners,<br />
using their brand to trick an organisation<br />
into giving cybercriminals money, sensitive<br />
intellectual property or login credentials<br />
has increased over the past year<br />
51% of IT professionals surveyed in the UK<br />
say the volume of email-based spoofing<br />
of well-known internet brands (Microsoft,<br />
PayPal etc), asking employees for money,<br />
sensitive intellectual property or login<br />
credentials, has increased in the last year.<br />
TIMES ARE CHANGING<br />
This research comes at a time when<br />
organisations across the globe have been<br />
forced to adopt remote work policies for<br />
employees in response to the coronavirus<br />
pandemic. Threat actors have seized this<br />
opportunity and evolved the ways they are<br />
targeting their victims. Domain-spoofing and<br />
email-spoofing have become mainstream<br />
attack vectors, according to the report. Nearly<br />
half of organisations (49%) surveyed report<br />
anticipating an increase in web or email<br />
spoofing and brand exploitation in the next<br />
12 months, and it is a rising concern. In fact,<br />
84% of respondents felt concerned about<br />
an email domain, web domain, brand<br />
exploitation or site spoofing attack. It is critical<br />
for organisations to look beyond their email<br />
perimeters to determine how cyber threat<br />
actors may be using and damaging their<br />
brands online.<br />
Similar to years past, impersonation attacks,<br />
phishing attempts and ransomware continue<br />
to be a major problem, according to the<br />
research. Seventy-two per cent of report<br />
participants said phishing attacks remained<br />
flat or increased in the previous 12 months<br />
and 74% reported the same of impersonation<br />
attacks. This indicates that phishing is<br />
potentially becoming more difficult to stop<br />
or prevent, due to more advanced tactics such<br />
as spear-phishing.<br />
Ransomware also continues to wreak havoc,<br />
as just over half of respondents (51%) said<br />
that ransomware attacks impacted their<br />
organisation, citing data loss, downtime,<br />
financial loss and loss of reputation or trust<br />
among customers.<br />
The State of Email Security <strong>2020</strong> report also<br />
shines a light on the urgent need for a more<br />
cyber-aware workforce. Encouragingly, 97%<br />
of the respondents' organisations offered<br />
security awareness training at varying<br />
frequencies and formats. However, 60% of<br />
those surveyed reported having been hit by<br />
malicious activity spread from employee to<br />
employee, pointing to the fact that the format<br />
or frequency of these trainings could be the<br />
problem. With frequent, consistent, engaging<br />
content that humanises security, security<br />
awareness training is an effective way to<br />
reduce risk inside the network and<br />
organisation.<br />
While threat actors are visibly gaining in<br />
sophistication and evolving, their tactics in<br />
www.computingsecurity.co.uk @<strong>CS</strong>MagAndAwards <strong>Nov</strong>/<strong>Dec</strong> <strong>2020</strong> computing security<br />
27
hacking surge<br />
Adrian Rowley, Gigamon: a much stricter<br />
privilege regulation policy is needed - a<br />
Zero Trust one.<br />
Joe Hancock, MDR Cyber: "Many of the<br />
targets of sophisticated cyber-attacks are<br />
nameless or their experience is tempered<br />
by being part of an organisation that can<br />
protect them.<br />
many ways remain the same, points out<br />
Chris Goettl, director of security solutions,<br />
Ivanti. "This means businesses can cut<br />
through this sophistication and prioritise<br />
measures to maximise their cybersecurity<br />
strategies. For this reason, they should look<br />
to cybersecurity frameworks, such as the<br />
CIS Critical Security Controls.<br />
THE RIGHT MEASURES<br />
"By following the top five CIS guidelines<br />
and adhering to basic cyber hygiene<br />
measures, it's possible to eliminate 85%<br />
of modern cyber threats. Take vulnerability<br />
management, for example: if IT and<br />
security teams don't treat vulnerability<br />
management as an ongoing process,<br />
business infrastructure will be exposed,<br />
as hackers can find and weaponise<br />
vulnerabilities faster than these teams can<br />
patch. Automating this process can further<br />
protect the organisation by minimising the<br />
gap between the onset of new knowledge<br />
and remediation, reducing the period in<br />
which cybercriminals can strike."<br />
Goettl also recognises how businesses<br />
have faced an entirely new security<br />
challenge over recent months due to<br />
the added risks of a remote workforce.<br />
"For companies that weren't prepared to<br />
support remote workers, this was a drastic<br />
change. It's important that IT and security<br />
teams implement tailored measures to<br />
counter this drastic shift in attack surface,<br />
as remote working looks set to continue in<br />
some capacity for the foreseeable future.<br />
"For example,", he also points out,<br />
"patching a remote or fluid workforce may<br />
require the implementation of a hybrid or<br />
cloud-based patch management solution<br />
that can implement patches to companyowned<br />
devices and BYOD, and that won't<br />
take up valuable VPN bandwidth with<br />
update traffic."<br />
With workers undefended away from their<br />
offices and targeted by malicious actors,<br />
companies must keep security front of<br />
mind as they familiarise themselves with<br />
the 'new normal', says Adrian Rowley,<br />
senior director Sales Engineering EMEA at<br />
Gigamon. "As flexible working becomes the<br />
go-to, employees will be shifting between<br />
on-premise and remote working,<br />
combining user-owned and company<br />
devices (not to mention personal WiFi<br />
connections). This will make network<br />
perimeters even harder to define and<br />
to protect.<br />
"Traffic flows will also be impacted,<br />
with users switching from LAN to WAN<br />
and back - so inspecting encrypted and<br />
unencrypted data will be critical for IT and<br />
security teams to keep abreast of potential<br />
threats. Ultimately, the only way to drive<br />
security in these difficult circumstances is<br />
minimising blind spots and ensuring<br />
unclouded visibility throughout the<br />
network."<br />
To create security resilience in times of<br />
uncertainty, companies must move away<br />
from the idea that any asset or user within<br />
the network perimeter can be trusted, and<br />
a much stricter privilege regulation policy is<br />
needed - in other words, a Zero Trust (ZT)<br />
architecture, he continues. "This security<br />
strategy consists of scrutinising asset<br />
behaviour and only granting access based<br />
on this information, rather than based on<br />
pre-existing credentials. Because it's<br />
impossible to monitor what you can't see,<br />
companies need a clear view of everything<br />
that happens on their network to enable<br />
a ZT approach. "What many businesses<br />
haven't grasped yet is that ZT isn't a<br />
product they can buy, deploy and use to<br />
dispel their security woes," states Rowley.<br />
"It's a mindset which must be applied to<br />
every IT and security decision. Shifting<br />
to a ZT model is no easy feat, but it's<br />
imperative to ensure fool-proof protection<br />
at a time when IT environments are<br />
complicated by a fluid workforce and<br />
cyberattacks are fiercer than ever."<br />
28<br />
computing security <strong>Nov</strong>/<strong>Dec</strong> <strong>2020</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
product review<br />
HORNETSECURITY 365 TOTAL PROTECTION<br />
Microsoft 365 is by far the most<br />
prevalent cloud email service for<br />
businesses, but this popularity<br />
brings inherent risks, as it also makes it the<br />
top target for cybercriminals. Email security<br />
features are provided by Microsoft, but<br />
these are widely used, comparatively basic<br />
and, consequently, easier to circumvent.<br />
To provide greater protection, businesses<br />
must implement a multi-layered defence -<br />
and Hornetsecurity offers a cost-effective<br />
and highly efficient solution. Its 365 Total<br />
Protection cloud service provides a wealth<br />
of email security measures, which includes<br />
AI intelligence-based protection, allowing<br />
it to evolve as new threats emerge.<br />
Two options are available, with the<br />
Business version providing all key threat<br />
defence measures, along with live email<br />
tracking, content control and compliance<br />
filtering. The Enterprise version augments<br />
these with ATP (advanced threat<br />
protection) cloud sandboxing, URL<br />
malware controls, email archiving, e-<br />
discovery and forensics analysis tools.<br />
Onboarding from the cloud panel is<br />
swift, as you change your domain's MX<br />
records, go to the registration link<br />
provided and authenticate with your<br />
account from the standard Microsoft 365<br />
login screen. Using its Azure connector,<br />
365 Total Protection synchronises all your<br />
users, with the entire process taking as<br />
little as 30 seconds.<br />
Protection starts immediately, as the<br />
default settings activate full spam and<br />
malware protection, which blocks<br />
suspicious emails before they reach your<br />
mailbox. The Spam and Malware filter uses<br />
over 15,000 heuristics to reject nuisance<br />
messages, such as newsletters and those<br />
sent from mass marketing campaigns.<br />
The cloud panel opens with an email<br />
live tracking view that shows logs of all<br />
inbound and outbound email activity. This<br />
is vastly superior to Microsoft's logging, as<br />
you can view every detail about individual<br />
emails, including header information, and<br />
each one is colour coded to clearly show<br />
its classification.<br />
Multiple filters can be applied to refine<br />
the list and clicking on the coloured icon<br />
for an email loads a drop-down menu<br />
where you can add the sender to deny or<br />
allow lists, report it as spam or release it.<br />
Enterprise users can also pass suspect<br />
emails to the ATP service for further<br />
examination.<br />
Self-service features lighten the support<br />
burden, as users can review their emails<br />
in the portal and release them, where<br />
permitted. Regular reports for each user<br />
can be generated and show spam activity,<br />
quarantined attachments, plus the reasons<br />
for rejection.<br />
The ATP sandbox recognises emails<br />
with encrypted attachments and, if the<br />
password is in the email message body,<br />
it will use it to scan these files. The URL<br />
rewrite feature deals efficiently with email<br />
web links, as Hornetsecurity opens a web<br />
session to its secure proxy to check where<br />
the link connects to and see if it includes<br />
harmful downloads or other threats.<br />
Fraudulent emails that appear to be<br />
legitimate are handled by a targeted<br />
forensics filter, which uses first and last<br />
name combinations in order to check for<br />
authenticity. The compliance filter provides<br />
more granular control of emails by<br />
applying DLP-like rules to outbound<br />
messages that check for specific keywords<br />
in the body, subject and attachment.<br />
The continuity service will prove<br />
invaluable when the Microsoft 365<br />
services go down, as it keeps copies for<br />
three months back for you to use during<br />
the outage and transfers them back to<br />
your account when the service comes<br />
up again. Rule-based encryption for<br />
outbound messages is just as easy to<br />
implement, as all certificates are centrally<br />
managed for you.<br />
Hornetsecurity's 365 Total Protection lives<br />
up to its name, as it delivers a smart email<br />
security solution that integrates seamlessly<br />
with Microsoft 365. It fills the security<br />
holes Microsoft leaves behind and, with<br />
prices for the Business version starting at<br />
only $2 per user per month, is affordable<br />
for organisations of all sizes.<br />
Product: 365 Total Protection<br />
Supplier: Hornetsecurity<br />
Web site: www.hornetsecurity.com<br />
Contact: info@hornetsecurity.com<br />
Price: From $2 per user per month<br />
www.computingsecurity.co.uk @<strong>CS</strong>MagAndAwards <strong>Nov</strong>/<strong>Dec</strong> <strong>2020</strong> computing security<br />
29
threat intelligence<br />
APTS AND COVID-19<br />
A RECENT INTELLIGENCE REPORT REVEALS HOW ADVANCED<br />
PERSISTENT THREATS ARE USING THE CORONAVIRUS AS A LURE<br />
KHNP (Korea Hydro & Nuclear Power) cyber<br />
terrorism attacks of 2014.<br />
Since it first showed itself, Covid-19<br />
has had a catastrophic impact on our<br />
lives, turning into a global pandemic<br />
that has upended economies, livelihoods<br />
and hospital systems - almost all facets<br />
of everyday life has been touched. Such<br />
uncertainty and fear surrounding the<br />
virus and its impact represents a golden<br />
opportunity for threat actors to exploit the<br />
situation, as Malwarebytes points out in<br />
one of its latest Threat Intelligence Reports.<br />
"By using social engineering tactics such<br />
as spam and spear phishing campaigns,<br />
with Covid-19 as a lure, cybercriminals<br />
and threat actors increase the likelihood<br />
of successful attack. From late January on,<br />
several cybercriminal and state-sponsored<br />
groups have been doing just that, using<br />
coronavirus-themed phishing emails as<br />
their infection vector to gain a foothold<br />
on victim machines." In its white paper,<br />
Malwarebytes provides an overview of<br />
several APT groups using coronavirus as an<br />
enticement, as well as a description of their<br />
varied attack vectors, categorising the APT<br />
groups according to the technique they<br />
used to send spam or phishing emails:<br />
template injection, malicious macros, RTF<br />
exploits and malicious LNK files. Here, we<br />
look at just a few it singles out.<br />
TEMPLATE INJECTION<br />
Template injection refers to a technique in<br />
which threat actors embed a script moniker<br />
in the lure document - usually a Microsoft<br />
Office document - that contains a link to<br />
a malicious Office template via an XML<br />
setting. Upon opening the document, the<br />
remote template is dropped and executed.<br />
Kimsuky and Gamaredon are examples of<br />
APTs using template injection.<br />
Kimsuky (also known as Velvet Chollima)<br />
is a North Korean threat actor group active<br />
since 2013 and is known to be behind the<br />
Gamaredon, a Russian APT, primarily<br />
performs cyber espionage operations<br />
against Ukrainian military forces, as well<br />
as individuals related to the Ukrainian<br />
government. Gamaredon has been active<br />
since 2013 and often uses spear phishing<br />
as its initial infection vector.<br />
MALICIOUS MACROS<br />
Embedding malicious macros is the most<br />
popular method of infection used by APTs,<br />
warns Malwarebytes. In this attack vector,<br />
a macro is embedded in the lure document<br />
that will be activated upon its opening.<br />
APT36 is another threat group that has<br />
employed macro-embedded COVID-19<br />
themes in its recent campaigns. The group,<br />
believed to be Pakistani state-sponsored,<br />
mainly targets the defence, embassies and<br />
government of India. The primary targets<br />
of this APT are organisations related to<br />
diplomatic and government agencies in the<br />
UK, China, Japan, the Middle East, the US,<br />
Bangladesh, Sri Lanka and Pakistan.<br />
Hades is the APT group behind the attack<br />
against the Pyeongchang Winter Olympics.<br />
"Evidence suggests that this group is<br />
connected to the well-known Russian<br />
threat actor APT288," points out<br />
Malwarebytes. In their recent campaign,<br />
called Tricky Mouse, Hades targeted<br />
Ukrainian users using COVID-19 lures."<br />
The Malwarebytes Threat Intelligence<br />
team is "monitoring the threat landscape<br />
and paying particular attention to attacks<br />
trying to abuse the public's fear of the<br />
COVID-19 crisis".<br />
30<br />
computing security <strong>Nov</strong>/<strong>Dec</strong> <strong>2020</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
GDPR<br />
THE GOOD…<br />
AND THE BAD<br />
LACK OF CLARITY AROUND CERTAIN NEW TECHNOLOGIES IS HITTING<br />
MANY LAW-ABIDING COMPANIES TRYING TO BE COMPLIANT WITH THE GDPR<br />
More than two years after the EU<br />
introduced the General Data<br />
Protection Regulation (GDPR),<br />
a report from the European Commission on<br />
the regulation’s progress makes for interesting<br />
reading. In it, the commission speaks of the<br />
many positives delivered. "Citizens are more<br />
empowered and aware of their rights. The<br />
GDPR enhances transparency and gives<br />
individuals enforceable rights, such as the right<br />
of access, rectification, erasure, the right to<br />
object and the right to data portability<br />
Individuals also have the right to lodge a<br />
complaint with a data protection authority<br />
and to seek an effective judicial remedy."<br />
Today, around 69% of the population above<br />
the age of 16 in the EU are said to have heard<br />
about the GDPR and 71% of people about<br />
their national data protection authority,<br />
according to results published in a survey from<br />
the EU Fundamental Rights Agency. "The GDPR<br />
has empowered individuals to play a more<br />
active role in what is happening with their<br />
data in the digital transition."<br />
While GDPR has been widely celebrated -<br />
and even mirrored in some countries, like the<br />
United States with the California Consumer<br />
Privacy Act - it's also clear that the EU needs<br />
to take additional steps to make it a more<br />
effective deterrent, according to Chris Harris,<br />
EMEA technical director at Thales.<br />
"Since its inception, there has been murmurs<br />
about its effectiveness, due to lack of clarity<br />
on compliance and fears around the resources<br />
and power each data protection authority<br />
(DPA) has to track and investigate the number<br />
of breaches that occur in their country. This is<br />
something that should have been sorted from<br />
the start, and not something that we are still<br />
talking about more than two years later - four<br />
plus, if you include the transition period!"<br />
Harris acknowledges that there have been<br />
some hefty fines justifiably dished out, which<br />
have caught the headlines and impressed.<br />
But he also points to how, as organisations<br />
continue to digitally transform, the lack<br />
of clarity around new technologies like<br />
blockchain and AI is actually mostly hitting<br />
law-abiding companies that are just trying<br />
to be compliant. "We need to ensure GDPR<br />
operates as the protective bubble around<br />
personal information that we all want, without<br />
restricting the innovation and development<br />
that the world needs from these disruptive<br />
technologies.<br />
"Smaller companies may have found<br />
compliance harder, not only due to the<br />
complexity and potentially onerous nature<br />
of the requirements, but because many<br />
vendors with GDPR-focused solutions were<br />
understandably scaling their offerings for the<br />
larger organisations. With a continued increase<br />
in the migration to the cloud, this has perhaps<br />
now become simpler with the advent<br />
of solutions such as cloud-agnostic key<br />
management solutions and subscription-based<br />
data-protection-on-demand services."<br />
In order to be truly effective, the EU needs<br />
to give clearer instructions on how to be<br />
compliant that are consistent across each<br />
country, he adds, "while giving local DPAs<br />
more resources to pursue heavy penalties<br />
against companies that are intentionally<br />
putting their customers' data at risk".<br />
Chris Harris, Thales: we need to ensure<br />
GDPR operates as the protective bubble<br />
around personal information.<br />
www.computingsecurity.co.uk @<strong>CS</strong>MagAndAwards <strong>Nov</strong>/<strong>Dec</strong> <strong>2020</strong> computing security<br />
31
gender inequality<br />
TIME TO REBALANCE THE BOOKS<br />
AWARENESS AROUND GENDER DIVERSITY IN THE CYBER SECURITY INDUSTRY<br />
IS GETTING BETTER, BUT THERE'S STILL A VERY LONG WAY TO GO<br />
Areport published by CREST has<br />
highlighted progress made in<br />
gender diversity across the cyber<br />
security industry in the past few years<br />
and points to the next steps needed to<br />
further address the gender gap. CREST -<br />
the not-for-profit body that represents<br />
the technical security industry including<br />
vulnerability assessment, penetration<br />
testing, incident response, threat<br />
intelligence and SOC (Security Operations<br />
Centre) - has found that, while<br />
awareness around gender diversity has<br />
improved, there is still work to be done<br />
to make a significant practical difference.<br />
In polls that were taken at CREST's<br />
gender diversity workshop, only 14% of<br />
attendees argued that not enough work<br />
has been done to lessen the gender gap,<br />
but 86% believed that while progress<br />
has been made, it is not nearly enough.<br />
The study also found that 59% of<br />
participants classified their experience in<br />
the industry as mixed, having received<br />
support and enjoyed roles but pointing<br />
to obstacles and challenges that had to<br />
be overcome as a result of being female.<br />
The workshops had the primary focus<br />
and objective of inspiring change and<br />
concluded that the main priorities for<br />
change are encouraging girls at school<br />
to study computer science; improving<br />
visibility of female role models;<br />
challenging the perception of industry<br />
and perceived gender-specific roles;<br />
and industry-wide female mentoring<br />
and coaching.<br />
32<br />
computing security <strong>Nov</strong>/<strong>Dec</strong> <strong>2020</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
gender inequality<br />
The report suggests the primary reason<br />
for the under-representation of women in<br />
the cyber security industry is down to a lack<br />
of interest in the subject from school age.<br />
When considering ways to make change,<br />
the report recommends that industry<br />
leaders - including directors, CEOs and<br />
accreditation bodies - could and should be<br />
responsible for approaching schools help<br />
educate and encourage students. Schools<br />
could also promote initiatives such as<br />
CyberFirst's online Girls Competition,<br />
which aims to inspire the next generation<br />
of young women to consider computer<br />
science as an option, with a view to<br />
a future career in cyber security.<br />
Findings by CREST also point to issues<br />
with current recruitment practices,<br />
including the way job descriptions are<br />
written, the language used and arguably<br />
even candidate requirements. Female<br />
representatives at the workshops agreed<br />
that the inclusion of training options<br />
on the job advert would encourage<br />
more female applicants, as would flexible<br />
working hours, good maternity policies<br />
and back to work support.<br />
Another key finding is the demand for<br />
an industry-wide female mentoring and<br />
coaching scheme to create a stronger,<br />
closer female community, while enabling<br />
women to grow and develop in their<br />
careers.<br />
MUCH MORE TO BE DONE<br />
"It is encouraging that as an industry we<br />
are making progress, but there is a lot<br />
more to do and improving the visibility<br />
of female role models will allow us to<br />
challenge the perception of the cyber<br />
security industry," says Ian Glover, president<br />
of CREST. "Schools hold the key and we<br />
need to help them to encourage more<br />
girls into the industry. Furthermore, the<br />
mentoring scheme would give a platform<br />
on which role models can help to coach<br />
and guide others, which in turn will help<br />
to challenge the perception of gender as<br />
it relates to the industry," adds Glover.<br />
"The actions are well-thought through,<br />
they are doable, but just need the support<br />
of industry, education and recruiters."<br />
FORTUNES TO BE MADE<br />
Interestingly, increasing the number of<br />
women working in cybersecurity could<br />
boost the UK economy by £12.6 billion<br />
according to a new report from Tessian,<br />
the human layer security company. The<br />
report also reveals that closing the 24%<br />
gender pay gap in the UK cybersecurity<br />
industry, and equalising women's salaries<br />
to men's, could add a further £4.4 billion<br />
to the UK economy, albeit such thoughts<br />
must now be tempered by the on-going<br />
ravages inflicted by the pandemic.<br />
The firm carried out a survey of 200<br />
female cybersecurity professionals in both<br />
the US and UK, and interviewed more than<br />
one dozen practitioners from some of the<br />
world's largest organisations about their<br />
personal experiences. The Tessian report<br />
highlights what it sees as the potential<br />
impact of expanding gender diversity in<br />
cybersecurity, as well as current perceptions<br />
around gender bias in the field.<br />
Key findings:<br />
82% of female cybersecurity<br />
professionals in the US believed that<br />
cybersecurity had a gender bias<br />
problem, compared with 49% of<br />
those in the UK<br />
The cybersecurity gender pay gap in<br />
the US was 17%; in the UK, 19%<br />
US respondents were three times as<br />
likely (68%) to believe that a more<br />
gender-balanced workforce would be<br />
an effective tool for recruiting more<br />
women to work in cybersecurity<br />
than UK respondents (22%)<br />
45% of US respondents said equal<br />
pay would help with recruitment,<br />
compared with just 10% of UK<br />
respondents<br />
61% of US respondents cited lack of<br />
qualified talent as a reason why 4m<br />
cybersecurity jobs would be left<br />
unfulfilled by 2021, while only 33% of<br />
UK women cited lack of qualified talent<br />
as a barrier. Once again, Covid-19 will<br />
have had its impact on all these figures.<br />
Factors discouraging women from joining<br />
the cybersecurity industry:<br />
42% of respondents (US. and UK)<br />
believed a cybersecurity skills gap<br />
existed, as the industry isn't considered<br />
'cool' or 'exciting'. This opinion was<br />
most commonly shared by millennials<br />
(46%), compared with 22% of 45-54-<br />
year-olds<br />
A lack of awareness or knowledge of<br />
the industry was the top challenge<br />
female professionals faced at the start<br />
of their career, with 43% citing this as<br />
a barrier<br />
43% of women said a lack of a clear<br />
development path was another<br />
challenge at the start of their<br />
cybersecurity career, while nearly<br />
a quarter (23%) cited a lack of role<br />
models<br />
Just 53% believed their organisations<br />
were doing enough to recruit women<br />
into security roles.<br />
GREATER VISIBILITY<br />
Sabrina Castiglione, senior executive at<br />
Tessian, comments: "For organisations to<br />
successfully recruit more women into<br />
security roles, they need to understand<br />
what's discouraging them from signing<br />
up, beyond just gender bias. We need to<br />
make women in cybersecurity more visible.<br />
We need to tell their stories and raise<br />
awareness of their roles and experiences.<br />
And, once through the door, managers<br />
need to clearly show women the<br />
opportunities available to them to progress<br />
and develop their careers."<br />
Shamla Naidoo, former CISO at IBM, has<br />
this to say: "To many people, cybersecurity<br />
www.computingsecurity.co.uk @<strong>CS</strong>MagAndAwards <strong>Nov</strong>/<strong>Dec</strong> <strong>2020</strong> computing security<br />
33
gender inequality<br />
equates to - and is limited to - someone in<br />
a hoodie bent over a keyboard in a dark<br />
room. That's not the case at all. If we don't<br />
expand beyond that, then we'll lose out<br />
on even more people in the industry." And<br />
she adds: "The future of cybersecurity needs<br />
diversity. 2019 was the worst year on<br />
record for data breaches, with 61% of<br />
organisations reporting a breach as a result<br />
of human error or malicious activity. With<br />
data breaches rising year on year, and with<br />
cyber threats continually evolving, we need<br />
different ideas and approaches to solving<br />
security problems, if we are going to keep<br />
people and data safe."<br />
WOMEN IN CYBER<br />
For its part, Cisco's commitment to the<br />
gender equality cause can be seen in its<br />
'Women in Cyber' initiative, which aims to<br />
bring diversity of thinking to a team and<br />
to a problem - what the company's Gregory<br />
Neal Akers describes as "unique perspectives<br />
that we would otherwise not have, because<br />
of the biases we bring from our own<br />
backgrounds".<br />
Akers, senior vice president of Advanced<br />
Security Initiatives and chief technology<br />
officer within the Global Governments<br />
Solutions Group at Cisco, says he can<br />
see that the gender gap in security is,<br />
unfortunately, real. "We have the problem<br />
of not having enough females in STEM in<br />
general and that yields a gap in security.<br />
I'm especially concerned about female<br />
undergrads and high school students in<br />
STEM, because they tend to gravitate to<br />
other domains like natural sciences or<br />
biology - rather advanced mathematics<br />
that is important to things like encryption<br />
and quantum computing.<br />
"Even within the research environment,<br />
I see senior-level female colleagues at other<br />
institutions lacking more women on their<br />
research teams - not because of bias, but<br />
because there simply isn't a talent pool of<br />
qualified women to draw from."<br />
He believes this situation is rooted in the<br />
primary and secondary education system,<br />
where we're not sufficiently encouraging<br />
girls and women into the field. "For<br />
example, in cryptography, which is my area<br />
of specialty, the required deep level math is<br />
not being taught to enough women. Yet<br />
these skills will be increasingly important<br />
for the ongoing critical development of<br />
Machine Learning. While some women<br />
will be drawn to this work, others may be<br />
reluctant; we need to actively demonstrate<br />
that cyber talent needs extend well beyond<br />
deep maths to a breadth of roles that<br />
demand all available talent. The imperative<br />
is urgent."<br />
So what can be done about this? "We<br />
must incentivise women to get involved in<br />
the cyber field; it offers satisfying experience<br />
and great intellectual stimulation," says<br />
Akers. "I believe in mentoring; for me, as<br />
a leader, it's very gratifying and I always get<br />
back more than I give. I insist on diversity<br />
in staffing activities: diverse interview teams<br />
to assess job candidates; diverse hiring<br />
professionals in HR; and having people<br />
with diverse perspectives make decisions<br />
on rewards and promotions. This can at<br />
times be difficult to do, given the pool of<br />
incumbents available to engage in the<br />
process. But, if you don't have multiple<br />
perspectives on a decision-making advisory<br />
group, you end up with biases and<br />
limitations in the ways to think about<br />
things. Leaders have to be dogmatic<br />
about this and make sure it's being done."<br />
Of course, the cyber talent shortage<br />
requires skilled women and men to fill<br />
much-needed jobs, he points out. "We need<br />
to balance encouraging and incentivising<br />
women to enter the field with cultivating<br />
skills of their male counterparts.<br />
And he concludes: "I firmly believe that,<br />
if the opportunity is presented, over time<br />
there will be a natural tendency for the<br />
balance to come."<br />
34<br />
computing security <strong>Nov</strong>/<strong>Dec</strong> <strong>2020</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
FULLSTACK VULNERABILITY MANAGEMENT<br />
CONTINUOUS VULNERABILITY<br />
INTELLIGENCE<br />
Accurately identifies vulnerabilities<br />
and exposures across the full stack.<br />
All threats are verified by<br />
cybersecurity experts, providing<br />
exploitable risk and remediation<br />
guidance.<br />
“The expertise and<br />
delivery of this service<br />
has been outstanding...”<br />
SECURITY AND RISK MANAGEMENT,<br />
MEDIA INDUSTRY, 30B+ US<br />
<strong>2020</strong>
NEW Sensitive Data Discovery and Remediation<br />
for Atlassian Confluence<br />
Discover, manage and protect sensitive information across your digital stack<br />
- now including Atlassian Confluence<br />
Ascema Sensitive Data Discovery and Extraction discovers, labels, monitors and restricts<br />
business-critical data across enterprise authorised applications.<br />
Find and protect your enterprise crown jewels easily using<br />
Ascema for Atlassian Confluence<br />
Complete data discovery and extraction across cloud and on premise<br />
True content level detection and restriction to safeguard your sensitive data<br />
Highly automated and flexible remediation capabilities<br />
Granular reporting into data threat patterns, user activity and risk profile<br />
Intelligent machine learning to classify sensitive information in real-time<br />
Elegant and simple to deploy, use and manage; all in a single console<br />
Integrated with popular and approved enterprise connectors, including:<br />
Find us on the Atlassian Marketplace, or click here to arrange a live demonstration or enquire about a FREE trial<br />
info@geolang.com<br />
www.geolang.com<br />
+(44) 02920 647 012