ANALYSIS: CYBERSECURITY MODERN WARFARE DANIEL HOFMANN, CEO OF HORNETSECURITY, EXAMINES THE 'DIGITAL BATTLEFIELD' OF CYBERSECURITY VERSUS MALICIOUS AI In the rapidly evolving world of cybersecurity, there's a relentless race in the use of AI between cybersecurity experts and malicious threat actors. This race is driven by the widespread adoption of Generative AI, presenting a double-edged sword for cybersecurity specialists. Cybersecurity experts use AI within their next-gen solutions to identify and address vulnerabilities in a system's security, detect abnormal activity, alert people to potential threats, and more. On the opposite side, malicious actors are exploiting similar technology to orchestrate increasingly sophisticated cyber-attacks. THE RISE OF DARK WEB AI VARIANTS The emergence of Dark Web variants of large language models (LLMs), such as DarkBERT and WormGPT, enables threat actors to use AI for nefarious purposes. These tools provide even novice attackers with technology that can be used to easily create and automate cyber threats with alarming authenticity. One byproduct of this is the ability to reach new global markets, including regions that are less accustomed to traditional cyber threats, as LLMs can instantly translate and automate large-scale phishing scams. The misuse of AI extends beyond the manipulation of LLMs. The escalating sophistication of deep-fakes poses a significant concern, particularly within the realm of biometric-based Multi-factor Authentication (MFA). This authentication method is gaining traction as businesses intensify their efforts to protect their systems against unauthorised access. Threat actors create spoofing attacks that often involve the replicas or imitations of an individual's biometric details whether it is a fingerprint, 3D facial masks, or voice - which was recently used in a deep-fake attack to scam an undisclosed Hong Kong-based business out of $25 million. PUBLIC AWARENESS It's not just businesses that are facing these attacks; consumers are at risk too. Cybercriminals are increasingly using "MFA bypass kits" to exploit the growing adoption of MFAs. These kits, such as Evilproxy and the W3LL panel (private phishing kit), create deceptive log-in pages that capture a user's credentials and MFA prompts. In its presence, unsuspecting users are then directed to the real login page, signing into the legitimate service while the bypass kit steals the user's session token for the threat actor to use at their leisure. Protecting against these attacks can be challenging, as they are adept at bypassing MFA and are connected to authentic websites. Threat actors often use these bypass kits to impersonate trusted connections and brands. Our research found that some of the top impersonated brands were leading e-commerce and delivery sites, like DHL, Amazon, and FedEx - with DHL (26.1%) and Amazon (7.7%) accounting for some of our top ten recorded brand impersonations. So, consumers likewise need to be aware of these tactics. BEACON OF HOPE Nevertheless, AI is also a formidable ally in the ongoing battle against cyber threats. Security experts and technology vendors integrate AI and machine learning into their defensive toolkits against such attacks, helping keep their solutions one step ahead in the 'cat and mouse' dance with attackers. Additionally, leading AI organisations such as OpenAI have launched initiatives aimed at empowering cybersecurity entities to "AI-enable" their defences. This strategic move is predicted to improve various facets of cybersecurity, ranging from outlier detection and improved log analysis to AI-simulated attacks as underscored in Hornetsecurity's Cyber Security Report 2024, along with threat modelling. All businesses with a digital presence may be at risk, so it's imperative to invest in robust security solutions, as well as ongoing employee education and awareness around cyber risks. A majority of breached businesses were infiltrated due to the absence of robust authentication (preferably MFA with phishresistant hardware), the allowance of simple passwords, and the lack of employee training to instil caution when clicking on links in emails. Coupled with next-gen cybersecurity solutions, taking action to avoid these missteps can go very far in protecting against AIenabled threats. More info: www.hornetsecurity.com 26 STORAGE Mar/Apr 2024 @STMagAndAwards www.storagemagazine.co.uk MAGAZINE
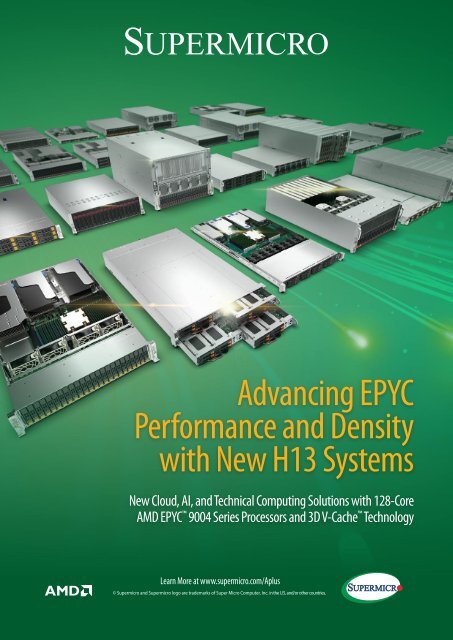
Advancing EPYC Performance and Density with New H13 Systems New Cloud, AI, and Technical Computing Solutions with 128-Core AMD EPYC 9004 Series Processors and 3D V-Cache Technology Learn More at www.supermicro.com/Aplus © Supermicro and Supermicro logo are trademarks of Super Micro Computer, Inc. in the U.S. and/or other countries.