Study & Evaluation Scheme of Bachelor of Science in Forensic ...
Study & Evaluation Scheme of Bachelor of Science in Forensic ...
Study & Evaluation Scheme of Bachelor of Science in Forensic ...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
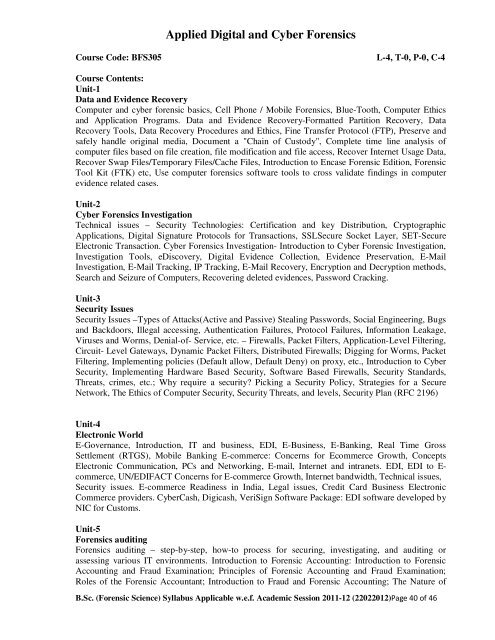
Applied Digital and Cyber <strong>Forensic</strong>s<br />
Course Code: BFS305 L-4, T-0, P-0, C-4<br />
Course Contents:<br />
Unit-1<br />
Data and Evidence Recovery<br />
Computer and cyber forensic basics, Cell Phone / Mobile <strong>Forensic</strong>s, Blue-Tooth, Computer Ethics<br />
and Application Programs. Data and Evidence Recovery-Formatted Partition Recovery, Data<br />
Recovery Tools, Data Recovery Procedures and Ethics, F<strong>in</strong>e Transfer Protocol (FTP), Preserve and<br />
safely handle orig<strong>in</strong>al media, Document a "Cha<strong>in</strong> <strong>of</strong> Custody", Complete time l<strong>in</strong>e analysis <strong>of</strong><br />
computer files based on file creation, file modification and file access, Recover Internet Usage Data,<br />
Recover Swap Files/Temporary Files/Cache Files, Introduction to Encase <strong>Forensic</strong> Edition, <strong>Forensic</strong><br />
Tool Kit (FTK) etc, Use computer forensics s<strong>of</strong>tware tools to cross validate f<strong>in</strong>d<strong>in</strong>gs <strong>in</strong> computer<br />
evidence related cases.<br />
Unit-2<br />
Cyber <strong>Forensic</strong>s Investigation<br />
Technical issues – Security Technologies: Certification and key Distribution, Cryptographic<br />
Applications, Digital Signature Protocols for Transactions, SSLSecure Socket Layer, SET-Secure<br />
Electronic Transaction. Cyber <strong>Forensic</strong>s Investigation- Introduction to Cyber <strong>Forensic</strong> Investigation,<br />
Investigation Tools, eDiscovery, Digital Evidence Collection, Evidence Preservation, E-Mail<br />
Investigation, E-Mail Track<strong>in</strong>g, IP Track<strong>in</strong>g, E-Mail Recovery, Encryption and Decryption methods,<br />
Search and Seizure <strong>of</strong> Computers, Recover<strong>in</strong>g deleted evidences, Password Crack<strong>in</strong>g.<br />
Unit-3<br />
Security Issues<br />
Security Issues –Types <strong>of</strong> Attacks(Active and Passive) Steal<strong>in</strong>g Passwords, Social Eng<strong>in</strong>eer<strong>in</strong>g, Bugs<br />
and Backdoors, Illegal access<strong>in</strong>g, Authentication Failures, Protocol Failures, Information Leakage,<br />
Viruses and Worms, Denial-<strong>of</strong>- Service, etc. – Firewalls, Packet Filters, Application-Level Filter<strong>in</strong>g,<br />
Circuit- Level Gateways, Dynamic Packet Filters, Distributed Firewalls; Digg<strong>in</strong>g for Worms, Packet<br />
Filter<strong>in</strong>g, Implement<strong>in</strong>g policies (Default allow, Default Deny) on proxy, etc., Introduction to Cyber<br />
Security, Implement<strong>in</strong>g Hardware Based Security, S<strong>of</strong>tware Based Firewalls, Security Standards,<br />
Threats, crimes, etc.; Why require a security? Pick<strong>in</strong>g a Security Policy, Strategies for a Secure<br />
Network, The Ethics <strong>of</strong> Computer Security, Security Threats, and levels, Security Plan (RFC 2196)<br />
Unit-4<br />
Electronic World<br />
E-Governance, Introduction, IT and bus<strong>in</strong>ess, EDI, E-Bus<strong>in</strong>ess, E-Bank<strong>in</strong>g, Real Time Gross<br />
Settlement (RTGS), Mobile Bank<strong>in</strong>g E-commerce: Concerns for Ecommerce Growth, Concepts<br />
Electronic Communication, PCs and Network<strong>in</strong>g, E-mail, Internet and <strong>in</strong>tranets. EDI, EDI to Ecommerce,<br />
UN/EDIFACT Concerns for E-commerce Growth, Internet bandwidth, Technical issues,<br />
Security issues. E-commerce Read<strong>in</strong>ess <strong>in</strong> India, Legal issues, Credit Card Bus<strong>in</strong>ess Electronic<br />
Commerce providers. CyberCash, Digicash, VeriSign S<strong>of</strong>tware Package: EDI s<strong>of</strong>tware developed by<br />
NIC for Customs.<br />
Unit-5<br />
<strong>Forensic</strong>s audit<strong>in</strong>g<br />
<strong>Forensic</strong>s audit<strong>in</strong>g – step-by-step, how-to process for secur<strong>in</strong>g, <strong>in</strong>vestigat<strong>in</strong>g, and audit<strong>in</strong>g or<br />
assess<strong>in</strong>g various IT environments. Introduction to <strong>Forensic</strong> Account<strong>in</strong>g: Introduction to <strong>Forensic</strong><br />
Account<strong>in</strong>g and Fraud Exam<strong>in</strong>ation; Pr<strong>in</strong>ciples <strong>of</strong> <strong>Forensic</strong> Account<strong>in</strong>g and Fraud Exam<strong>in</strong>ation;<br />
Roles <strong>of</strong> the <strong>Forensic</strong> Accountant; Introduction to Fraud and <strong>Forensic</strong> Account<strong>in</strong>g; The Nature <strong>of</strong><br />
B.Sc. (<strong>Forensic</strong> <strong>Science</strong>) Syllabus Applicable w.e.f. Academic Session 2011-12 (22022012)Page 40 <strong>of</strong> 46