Nokia Mobile VPN
Nokia Mobile VPN
Nokia Mobile VPN
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
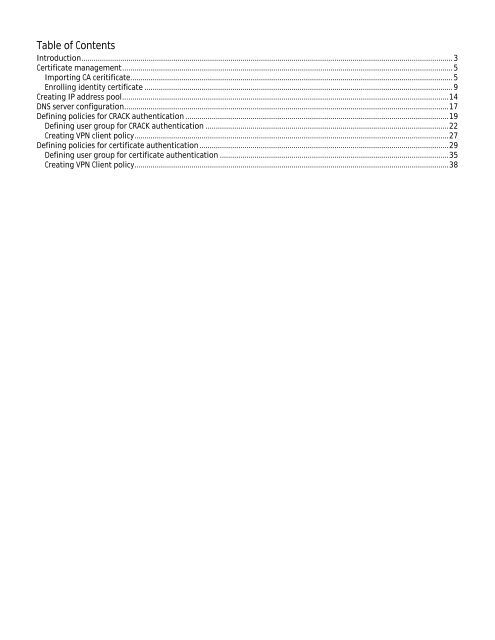
Table of Contents<br />
Introduction...................................................................................................................................................................................... 3<br />
Certificate management.................................................................................................................................................................. 5<br />
Importing CA ceritificate.............................................................................................................................................................. 5<br />
Enrolling identity certificate ....................................................................................................................................................... 9<br />
Creating IP address pool................................................................................................................................................................14<br />
DNS server configuration...............................................................................................................................................................17<br />
Defining policies for CRACK authentication .................................................................................................................................19<br />
Defining user group for CRACK authentication .......................................................................................................................22<br />
Creating <strong>VPN</strong> client policy..........................................................................................................................................................27<br />
Defining policies for certificate authentication ..........................................................................................................................29<br />
Defining user group for certificate authentication ................................................................................................................35<br />
Creating <strong>VPN</strong> Client policy..........................................................................................................................................................38