- Page 1 and 2:
The menace came from below Éric Le
- Page 3 and 4:
Victor Julien a.k.a Inliniac Dutch
- Page 5 and 6:
Suricata Features High performance,
- Page 7 and 8:
1 Introduction Netfilter and the Co
- Page 9 and 10:
Netfilter Definition Packet filteri
- Page 11 and 12:
Application Level Gateway Non-linea
- Page 13 and 14:
The example of FTP FTP client Logge
- Page 15 and 16:
The example of FTP FTP client Logge
- Page 17 and 18:
Details of Netfilter implementation
- Page 19 and 20:
Do I use helpers? What happens if I
- Page 21 and 22:
Do I use helpers? What happens if I
- Page 23 and 24:
Global analysis Sane defaults Dange
- Page 25 and 26:
FTP analysis If we follow RFC (loos
- Page 27 and 28:
IRC analysis The DCC command DCC co
- Page 29 and 30:
Using DCC command Client NATed behi
- Page 31 and 32:
Using DCC command Client NATed behi
- Page 33 and 34:
Demonstration of DCC usage Video Le
- Page 35 and 36:
Objective Determine if it is possib
- Page 37 and 38:
Attack description Existing attacks
- Page 39 and 40:
Attack description Existing attacks
- Page 41 and 42:
Attack description for FTP 1 The at
- Page 43 and 44:
Attack description for FTP 1 The at
- Page 45 and 46:
Attack description for FTP 1 The at
- Page 47 and 48:
Demonstration on Netfilter Video É
- Page 49 and 50:
Policy violation We’ve manage to
- Page 51 and 52:
Policy violation We’ve manage to
- Page 53 and 54:
Counter-measures Anti-spoofing is s
- Page 55 and 56:
Counter-measures Anti-spoofing is s
- Page 57 and 58:
Checkpoint setup Checkpoint absolut
- Page 59 and 60:
Demonstration setup Éric Leblond,
- Page 61 and 62:
Demonstration setup Let’s do a fi
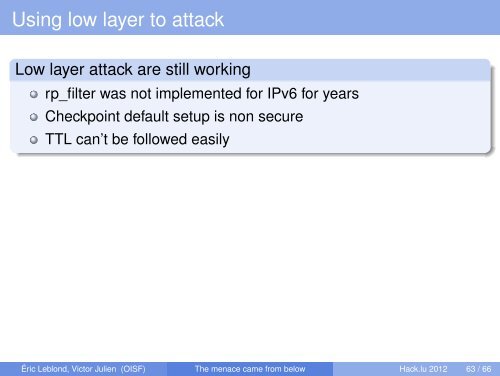
- Page 63 and 64:
Demonstration Video Let’s have a
- Page 65 and 66: Policy violation One managed to ope
- Page 67 and 68: There is no problem Swift reaction
- Page 69 and 70: Others protocols IRC As discussed b
- Page 71 and 72: 1 Introduction Netfilter and the Co
- Page 73 and 74: Protection for Netfilter We only ha
- Page 75 and 76: Protection for Netfilter We only ha
- Page 77 and 78: Protection for Netfilter We only ha
- Page 79 and 80: Protection for Netfilter We only ha
- Page 81 and 82: IPv6 protection for Netfilter Since
- Page 83 and 84: IPv6 protection for Netfilter The b
- Page 85 and 86: Suricata Rules Largely compatible w
- Page 87 and 88: Suricata Rules Largely compatible w
- Page 89 and 90: Counter measures on Suricata FTP in
- Page 91 and 92: Detecting overlapping data Rule Att
- Page 93 and 94: Detect FTP injection - step 1 Rule
- Page 95 and 96: Detect FTP injection - step 3 Rule
- Page 97 and 98: Detect FTP injection - port Rule In
- Page 99 and 100: Luajit script Simplified Script f u
- Page 101 and 102: Protocol analysis: a difficult task
- Page 103 and 104: Example of nDPI History Originally
- Page 105 and 106: Causing recognition mistake Evading
- Page 107 and 108: Don’t mess with the server Issue
- Page 109 and 110: Implementing the attack in opensvp
- Page 111 and 112: Attack on nDPI Test used Injection
- Page 113 and 114: Detecting very low TTL Example TTL
- Page 115: Future changes in Suricata We’re
- Page 119 and 120: SNMP: Security is Not My Problem Ke
- Page 121 and 122: Questions Thanks to Do you have any