Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
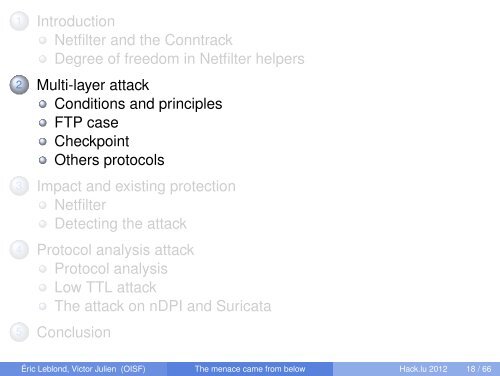
1 Introduction<br />
Netfilter and the Conntrack<br />
Degree of freedom in Netfilter helpers<br />
2 Multi-layer attack<br />
Conditions and principles<br />
FTP case<br />
Checkpoint<br />
Others protocols<br />
3 Impact and existing protection<br />
Netfilter<br />
Detecting the attack<br />
4 Protocol analysis attack<br />
Protocol analysis<br />
Low TTL attack<br />
<strong>The</strong> attack on nDPI and Suricata<br />
5 Conc<strong>lu</strong>sion<br />
Éric Leblond, Victor Julien (OISF) <strong>The</strong> <strong>menace</strong> <strong>came</strong> <strong>from</strong> <strong>below</strong> <strong>Hack</strong>.<strong>lu</strong> 2012 18 / 66