Timed CTL Model Checking in Real-Time Maude⋆ - IfI
Timed CTL Model Checking in Real-Time Maude⋆ - IfI
Timed CTL Model Checking in Real-Time Maude⋆ - IfI
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
<strong><strong>Time</strong>d</strong> <strong>CTL</strong> <strong>Model</strong> <strong>Check<strong>in</strong>g</strong> <strong>in</strong><br />
<strong>Real</strong>-<strong>Time</strong> Maude ⋆<br />
(Extended Version) ⋆⋆<br />
Daniela Lepri 1 , Erika Ábrahám2 , and Peter Csaba Ölveczky1,3<br />
1 University of Oslo, Norway<br />
2 RWTH Aachen University, Germany<br />
3 University of Ill<strong>in</strong>ois at Urbana-Champaign, USA<br />
Abstract. This paper presents a timed <strong>CTL</strong> model checker for <strong>Real</strong>-<br />
<strong>Time</strong> Maude and its semantic foundations. In particular, we give a timed<br />
<strong>CTL</strong> model check<strong>in</strong>g procedure for that is sound and complete for closedbound<br />
formulas under a cont<strong>in</strong>uous semantics for a fairly large class of<br />
systems. An important benefit of our model checker is that it also automatically<br />
provides a timed <strong>CTL</strong> model checker for subsets of model<strong>in</strong>g<br />
languages, like Ptolemy II and (Synchronous) AADL, which have <strong>Real</strong>-<br />
<strong>Time</strong> Maude model check<strong>in</strong>g <strong>in</strong>tegrated <strong>in</strong>to their tool environments.<br />
1 Introduction<br />
<strong>Real</strong>-<strong>Time</strong> Maude [31] extends Maude [15] to support the formal model<strong>in</strong>g and<br />
analysis of real-time systems <strong>in</strong> rewrit<strong>in</strong>g logic. <strong>Real</strong>-<strong>Time</strong> Maude is characterized<br />
by its expressiveness and generality, natural model of object-based distributed<br />
real-time systems, that supports multiple <strong>in</strong>heritance as well as dynamic<br />
creation and deletion of both objects and messages, the possibility to def<strong>in</strong>e any<br />
computable data type, and a range of automated formal analysis such as simulation,<br />
reachability and temporal logic model check<strong>in</strong>g. This has made it possible<br />
to successfully apply the tool to a wide range of real-time systems, <strong>in</strong>clud<strong>in</strong>g<br />
advanced state-of-the-art wireless sensor network algorithms [18, 33], multicast<br />
protocols [32, 21], schedul<strong>in</strong>g algorithms requir<strong>in</strong>g unbounded queues [27], and<br />
rout<strong>in</strong>g protocols [34].<br />
<strong>Real</strong>-<strong>Time</strong> Maude’s expressiveness and generality also make it a suitable<br />
semantic framework and analysis tool for model<strong>in</strong>g languages for real-time systems<br />
[25]. For example, the tool has been used to formalize (subsets of) the<br />
⋆⋆ This paper is the extended version of a work submitted for publication. In particular,<br />
more details about the model checker implementation and optimizations are given<br />
<strong>in</strong> Section 5, and Section 6 conta<strong>in</strong>s two further case studies, about model check<strong>in</strong>g,<br />
respectively, a simple network of embedded medical devices, and the Ptolemy II<br />
railoroad cross<strong>in</strong>g benchmark.<br />
⋆ This work was partially supported by the Research Council of Norway through the<br />
Rhytm project, by the DAADppp HySmart project, and by AFOSR Grant FA8750-<br />
11-2-0084.
2 D. Lepri, E. Ábrahám, and P. Cs. Ölveczky<br />
<strong>in</strong>dustrial avionics model<strong>in</strong>g standard AADL [26], a synchronous version of<br />
AADL [6], Ptolemy II discrete-event (DE) models [7], the web orchestration language<br />
Orc [2], different EMF-based timed model transformation frameworks [35,<br />
10], etc. <strong>Real</strong>-<strong>Time</strong> Maude formal analysis has been <strong>in</strong>tegrated <strong>in</strong>to the tool environment<br />
of some of these languages, enabl<strong>in</strong>g a model eng<strong>in</strong>eer<strong>in</strong>g process that<br />
comb<strong>in</strong>es the convenience of an <strong>in</strong>tuitive model<strong>in</strong>g language with formal analysis.<br />
In <strong>Real</strong>-<strong>Time</strong> Maude, the data types of the system are def<strong>in</strong>ed by an algebraic<br />
equational specification, and the system’s <strong>in</strong>stantaneous transitions are modeled<br />
by (<strong>in</strong>stantaneous) rewrite rules. <strong>Time</strong> advance is modeled explicitly by so-called<br />
tick (rewrite) rules of the form {t} => {t ′ } <strong>in</strong> time u if cond, where {_} is<br />
an operator that encloses the entire global state, and the term u denotes the<br />
duration of the rewrite. <strong>Real</strong>-<strong>Time</strong> Maude is parametric <strong>in</strong> the time doma<strong>in</strong>,<br />
which may be discrete or dense. For dense time (<strong>in</strong> particular), tick rules typically<br />
have the form {t} => {t ′ } <strong>in</strong> time x if x
<strong><strong>Time</strong>d</strong> <strong>CTL</strong> <strong>Model</strong> <strong>Check<strong>in</strong>g</strong> <strong>in</strong> <strong>Real</strong>-<strong>Time</strong> Maude 3<br />
the branch<strong>in</strong>g time logic <strong>CTL</strong> <strong>in</strong> which the temporal operators are annotated<br />
with a time <strong>in</strong>terval, so that, for example, the formula E ϕ1 U [2,4] ϕ2 holds if<br />
there is a path <strong>in</strong> which ϕ2 holds after some time 2 ≤ r ≤ 4 and where ϕ1 holds<br />
<strong>in</strong> all states until then.<br />
Go<strong>in</strong>g from untimed temporal logic to a timed temporal logic presents at<br />
least two significant challenges for <strong>Real</strong>-<strong>Time</strong> Maude:<br />
1. What is the <strong>in</strong>tended semantics of a <strong>Real</strong>-<strong>Time</strong> Maude specification with the<br />
above tick rule w.r.t. timed temporal logic properties? For example, given<br />
a tick rule {f(y)} => {f(y + x)} <strong>in</strong> time x if x
4 D. Lepri, E. Ábrahám, and P. Cs. Ölveczky<br />
studies: a <strong>Real</strong>-<strong>Time</strong> Maude model of a simple network of embedded medical<br />
devices, a Ptolemy II model of a railroad cross<strong>in</strong>g system, and a Ptolemy II<br />
model of a fault-tolerant traffic light system.<br />
An important benefit of our work is that a T<strong>CTL</strong> model checker for <strong>Real</strong>-<br />
<strong>Time</strong> Maude also gives us a T<strong>CTL</strong> model checker for free for Ptolemy II DE<br />
models, synchronous AADL models, and other model<strong>in</strong>g languages for which<br />
<strong>Real</strong>-<strong>Time</strong> Maude models can be generated. As shown <strong>in</strong> Section 6, our model<br />
checker has already been <strong>in</strong>tegrated <strong>in</strong>to the Ptolemy II tool, allow<strong>in</strong>g the user<br />
to model check T<strong>CTL</strong> properties of Ptolemy II models from with<strong>in</strong> Ptolemy II.<br />
Related Work. The tools Kronos [39], Redlib [37], and TSMV [22] implement<br />
T<strong>CTL</strong> model checkers for, respectively, timed automata, l<strong>in</strong>ear hybrid automata,<br />
and timed Kripke structures. The tool Uppaal [9] provides an efficient symbolic<br />
model check<strong>in</strong>g procedure for timed automata for a subset of non-nested T<strong>CTL</strong><br />
properties. The Roméo tool [17, 11], based on a timed extension of Petri nets [1,<br />
23], has an <strong>in</strong>tegrated timed model checker for some non-nested T<strong>CTL</strong> modalities,<br />
with the addition of bounded response properties. These formalisms are<br />
significantly less expressive than real-time rewrite theories [28], which makes<br />
their model check<strong>in</strong>g problems decidable. The first approaches to model check<strong>in</strong>g<br />
timed temporal properties for <strong>Real</strong>-<strong>Time</strong> Maude are described <strong>in</strong> [20, 38]<br />
and analyze important specific classes of timed temporal logic formulas (timebounded<br />
response, time-bounded safety, and m<strong>in</strong>imum separation), but only for<br />
flat object-based specifications. Unlike <strong>in</strong> [20, 38], our new model checker is not<br />
limited to specific classes of temporal logic properties, but offers the full T<strong>CTL</strong>.<br />
The new model checker is also not limited to flat object-oriented systems, but<br />
can also analyze any (sensible) <strong>Real</strong>-<strong>Time</strong> Maude model, <strong>in</strong>clud<strong>in</strong>g hierarchical<br />
object-oriented specifications, which is crucial, s<strong>in</strong>ce both AADL and Ptolemy II<br />
models are hierarchical.<br />
Paper Structure. Section 2 <strong>in</strong>troduces real-time rewrite theories and <strong>Real</strong>-<strong>Time</strong><br />
Maude. Section 3 describes our model checker and its semantics. Section 4<br />
presents our soundness and completeness results. We discuss our model checker<br />
implementation <strong>in</strong> Section 5, and demonstrate its applicability on three case<br />
studies <strong>in</strong> Section 6. F<strong>in</strong>ally, conclud<strong>in</strong>g remarks are given <strong>in</strong> Section 7.<br />
2 <strong>Real</strong>-<strong>Time</strong> Rewrite Theories and <strong>Real</strong>-<strong>Time</strong> Maude<br />
A rewrite theory is a tuple (Σ, E, R), where (Σ, E) is a membership equational<br />
logic theory [15] that def<strong>in</strong>es the state space of a system as an algebraic data<br />
type, with Σ a signature declar<strong>in</strong>g sorts, subsorts, and function symbols, and<br />
E a set of conditional equations and membership axioms, and where R is a set<br />
of labeled conditional rewrite rules of the form [l] : t −→ t ′ if cond, where<br />
l is a label, t, t ′ are Σ-terms, and cond is a conjunction of rewrite conditions<br />
u −→ u ′ , equational conditions v = v ′ , and membership conditions w : s, where<br />
u, u ′ , v, v ′ , w are Σ-terms and s is a sort <strong>in</strong> Σ. A rule is implicitly universally
<strong><strong>Time</strong>d</strong> <strong>CTL</strong> <strong>Model</strong> <strong>Check<strong>in</strong>g</strong> <strong>in</strong> <strong>Real</strong>-<strong>Time</strong> Maude 5<br />
quantified by the variables appear<strong>in</strong>g <strong>in</strong> t, t ′ and cond, and specifies a set of<br />
local one-step transitions <strong>in</strong> the system. Rules are applied modulo the equations<br />
E. The set T Σ/E,s of states of sort s is def<strong>in</strong>ed by the E-equivalence classes of<br />
ground terms of sort s.<br />
<strong>Real</strong>-time rewrite theories [28] are used to specify real-time systems <strong>in</strong> rewrit<strong>in</strong>g<br />
logic. Rules are divided <strong>in</strong>to tick rules, that model time elapse <strong>in</strong> a system,<br />
and <strong>in</strong>stantaneous rules, that model <strong>in</strong>stantaneous change. Formally a real-time<br />
rewrite theory R is a tuple (Σ, E, R, φ, τ) such that<br />
– (Σ, E, R) is a rewrite theory, with a sort System and a sort GlobalSystem<br />
with no subsorts or supersorts and with only one operator {_} : System →<br />
GlobalSystem which satisfies no non-trivial equations; furthermore, for any<br />
f : s1 . . . sn → s <strong>in</strong> Σ, the sort GlobalSystem does not appear <strong>in</strong> s1 . . . sn.<br />
– φ : TIME → (Σ, E) is an equational theory morphism which <strong>in</strong>terprets<br />
TIME <strong>in</strong> R; the theory TIME [28] def<strong>in</strong>es time abstractly as an ordered commutative<br />
monoid (<strong>Time</strong>, 0, +, r with t −→ t ′′ for some<br />
t ′′ r0 r1 r2<br />
. A timed path <strong>in</strong> R is an <strong>in</strong>f<strong>in</strong>ite sequence π = t0 −→ t1 −→ t2 −→ · · · such<br />
that<br />
ri<br />
– for all i ∈ N, ti −→ ti+1 is a one-step rewrite <strong>in</strong> R; or<br />
ri<br />
– there exists a k ∈ N such that ti −→ ti+1 is a one-step rewrite <strong>in</strong> R for all<br />
0 ≤ i < k, there is no one-step rewrite from tk <strong>in</strong> R, and tj = tk and rj = 0<br />
for each j ≥ k.<br />
For paths π of the above form we def<strong>in</strong>e dπ m = m−1 i=0 ri, tπ m = tm and rπ m = rm.<br />
r0 r1 r2<br />
We call the timed path π = t0 −→ t1 −→ t2 −→ · · · a timed fair path if<br />
– for any ground term ∆ of sort <strong>Time</strong>, if there is a k such that for each j > k<br />
r<br />
there is a one-step tick rewrite tj −→ t with ∆ ≤ dπ j + r then there is an l<br />
with ∆ ≤ dπ l , and<br />
– for each k, if for each j > k both a maximal tick step with duration 0 and an<br />
<strong>in</strong>st<br />
<strong>in</strong>stantaneous rule can be applied <strong>in</strong> tj then tl −→ tl+1 is a one-step rewrite<br />
apply<strong>in</strong>g an <strong>in</strong>stantaneous rule for some l > k.<br />
We denote the set of all timed fair paths of R start<strong>in</strong>g <strong>in</strong> t0 by tfPathsR(t0). A<br />
term t is reachable from t0 <strong>in</strong> R <strong>in</strong> time r iff there is a path π ∈ tfPathsR(t0) with tπ k = t and dπ k = r for some k. A path π is time-divergent iff for each time<br />
value r ∈ <strong>Time</strong> there is an i ∈ N such that dπ i > r.<br />
r ′
6 D. Lepri, E. Ábrahám, and P. Cs. Ölveczky<br />
The <strong>Real</strong>-<strong>Time</strong> Maude tool [30] extends the Maude system [15] to support<br />
the specification, simulation, and analysis of real-time rewrite theories. <strong>Real</strong>-<br />
<strong>Time</strong> Maude is parametric <strong>in</strong> the time doma<strong>in</strong>, which may be discrete or dense,<br />
and def<strong>in</strong>es a supersort <strong>Time</strong>Inf of <strong>Time</strong> which adds the <strong>in</strong>f<strong>in</strong>ity element INF.<br />
To cover all time <strong>in</strong>stances <strong>in</strong> a dense time doma<strong>in</strong>, tick rules often have one of<br />
the forms<br />
crl [tick] : {t} => {t ′ } <strong>in</strong> time x if x {t ′ } <strong>in</strong> time x if cond [nonexec] . (∗), or<br />
rl [tick] : {t} => {t ′ } <strong>in</strong> time x [nonexec] . (§).<br />
where x is a new variable of sort <strong>Time</strong> not occurr<strong>in</strong>g <strong>in</strong> {t} and cond. This<br />
ensures that the tick rules can advance time by any amount <strong>in</strong> rules of the form<br />
(∗) or (§) and any amount less than or equal to u <strong>in</strong> rules of the form (†). Rules<br />
of these forms are called time-nondeterm<strong>in</strong>istic and are not directly executable<br />
<strong>in</strong> general, s<strong>in</strong>ce many choices are possible for <strong>in</strong>stantiat<strong>in</strong>g the new variable x.<br />
In contrast to, e.g., timed automata, where the restrictions <strong>in</strong> the formalism<br />
allow the abstraction of the dense time doma<strong>in</strong> by “clock regions” conta<strong>in</strong><strong>in</strong>g<br />
bisimilar states [3], for the more complex systems expressible <strong>in</strong> <strong>Real</strong>-<strong>Time</strong><br />
Maude there is not such a discrete “quotient”. Instead, <strong>Real</strong>-<strong>Time</strong> Maude executes<br />
time-nondeterm<strong>in</strong>istic tick rules by offer<strong>in</strong>g a choice of different time sampl<strong>in</strong>g<br />
strategies [30], so that only some moments <strong>in</strong> the time doma<strong>in</strong> are visited.<br />
For example, the maximal time sampl<strong>in</strong>g strategy advances time by the maximum<br />
possible time elapse u <strong>in</strong> rules of the form (†) (unless u equals INF), and<br />
tries to advance time by a user-given time value r <strong>in</strong> tick rules hav<strong>in</strong>g other<br />
forms. In the default mode each application of a time-nondeterm<strong>in</strong>istic tick rule<br />
will try to advance time by a given time value r.<br />
The paper [30] expla<strong>in</strong>s the semantics of <strong>Real</strong>-<strong>Time</strong> Maude <strong>in</strong> more detail.<br />
In particular, given a real-time rewrite theory R and a time sampl<strong>in</strong>g strategy<br />
σ, there is a real-time rewrite theory R σ that has been obta<strong>in</strong>ed from R<br />
by apply<strong>in</strong>g a theory transformation correspond<strong>in</strong>g to us<strong>in</strong>g the time sampl<strong>in</strong>g<br />
strategy σ when execut<strong>in</strong>g the tick rules. In particular, the real-time rewrite<br />
theory R maxDef (r) denotes the real-time rewrite theory R where the tick rules<br />
are applied accord<strong>in</strong>g to the maximal time sampl<strong>in</strong>g strategy, while R def(r) denotes<br />
R where the tick rules are applied accord<strong>in</strong>g to the default time sampl<strong>in</strong>g<br />
strategy (tick steps which advance time by 0 are not applied).<br />
A real-time rewrite theory R is time-robust if the follow<strong>in</strong>g hold for all ground<br />
terms t, t ′ , t ′′ of sort GlobalSystem and all ground terms r, r ′ , of sort <strong>Time</strong>:<br />
– t = t ′ holds <strong>in</strong> the underly<strong>in</strong>g equational theory for any 0-time tick step<br />
0<br />
t −→ t ′ .<br />
– t r+r′<br />
−→ t ′′ if and only if there is a t ′ r<br />
of sort <strong>Time</strong> such that t −→ t ′ and<br />
−→ t ′′ .<br />
r<br />
– If t −→ t ′ ′ <strong>in</strong>st<br />
is a tick step with r > 0, and t −→ t ′′ is an <strong>in</strong>stantaneous one-step<br />
r<br />
rewrite, then t −→ t ′′ is a maximal tick step.<br />
– for M = {r | ∃t ′ r<br />
. t −→ t ′ } we have that either there is a maximal element <strong>in</strong><br />
M or M is the whole doma<strong>in</strong> of <strong>Time</strong>.<br />
t ′ r ′
<strong><strong>Time</strong>d</strong> <strong>CTL</strong> <strong>Model</strong> <strong>Check<strong>in</strong>g</strong> <strong>in</strong> <strong>Real</strong>-<strong>Time</strong> Maude 7<br />
<strong>Real</strong>-<strong>Time</strong> Maude extends Maude’s l<strong>in</strong>ear temporal logic model checker to<br />
check whether each behavior, possibly up to a certa<strong>in</strong> time bound, satisfies an<br />
(untimed) LTL formula. State propositions are terms of sort Prop. The label<strong>in</strong>g<br />
of states with propositions can be specified by (possibly conditional) equations<br />
of the form<br />
{stateP attern} |= prop = b<br />
for b a term of sort Bool, which def<strong>in</strong>es the state proposition prop to evaluate to b<br />
<strong>in</strong> all states match<strong>in</strong>g the given pattern. We say that a set of atomic propositions<br />
is tick-<strong>in</strong>variant <strong>in</strong> R if tick rules do not change their values.<br />
S<strong>in</strong>ce the model check<strong>in</strong>g commands execute time-nondeterm<strong>in</strong>istic tick rules<br />
accord<strong>in</strong>g to a time sampl<strong>in</strong>g strategy, only a subset of all possible behaviors<br />
is analyzed. Therefore, <strong>Real</strong>-<strong>Time</strong> Maude analysis is <strong>in</strong> general not sound and<br />
complete. However, the reference [29] gives easily checkable sufficient conditions<br />
for soundness and completeness, which are satisfied by many large <strong>Real</strong>-<strong>Time</strong><br />
Maude applications.<br />
3 <strong><strong>Time</strong>d</strong> <strong>CTL</strong> <strong>Model</strong> <strong>Check<strong>in</strong>g</strong> for <strong>Real</strong>-<strong>Time</strong> Maude<br />
In untimed temporal logics it is not possible to reason about the duration<br />
of/between events. There are many timed extensions of temporal logics: both<br />
po<strong>in</strong>t-based and <strong>in</strong>terval-based, l<strong>in</strong>ear-time and branch<strong>in</strong>g-time, with discrete or<br />
dense time, based on po<strong>in</strong>twise or cont<strong>in</strong>uous semantics, etc. (see [4, 36, 12] for<br />
an overview). In this paper we consider T<strong>CTL</strong> [5] with <strong>in</strong>terval time constra<strong>in</strong>ts<br />
on temporal operators.<br />
3.1 <strong><strong>Time</strong>d</strong> <strong>CTL</strong><br />
In computation tree logic (<strong>CTL</strong>) [5], a state formula specifies a property over the<br />
computation tree correspond<strong>in</strong>g to the system behavior rooted <strong>in</strong> a given state.<br />
State formulae are constructed by add<strong>in</strong>g universal (A ) and existential (E )<br />
path quantifiers <strong>in</strong> front of path formulae to specify whether the path formula<br />
must hold, respectively, on each path start<strong>in</strong>g <strong>in</strong> the given state, or just on some<br />
path. Path formulae are built from state formulae us<strong>in</strong>g the temporal operators<br />
X (“next”) and U (“until”). Intuitively, the path formula p U q (“p until q”)<br />
is satisfied by a path if the property q becomes valid with<strong>in</strong> a f<strong>in</strong>ite number of<br />
steps and the property p constantly holds on the path before.<br />
As syntactic sugar we use the common abbreviations: E F ϕ is def<strong>in</strong>ed as<br />
E true U ϕ; A F ϕ is def<strong>in</strong>ed as A true U ϕ; E G ϕ is def<strong>in</strong>ed as ¬A F ¬ϕ and<br />
A G ϕ is def<strong>in</strong>ed as ¬E F ¬ϕ.<br />
<strong><strong>Time</strong>d</strong> <strong>CTL</strong> (T<strong>CTL</strong>) is a quantitative extension of <strong>CTL</strong> [5], where the scope<br />
of the temporal operators can be limited <strong>in</strong> time by subscript<strong>in</strong>g them with time<br />
constra<strong>in</strong>ts. In this paper we consider an <strong>in</strong>terval-bound version of T<strong>CTL</strong> where<br />
the temporal operators are subscripted with a time <strong>in</strong>terval. A time <strong>in</strong>terval I<br />
is an <strong>in</strong>terval of the form [a, b], (a, b], [a, b∞) or (a, b∞), where a and b are values<br />
of sort <strong>Time</strong> and b∞ is a value of sort <strong>Time</strong>Inf.
8 D. Lepri, E. Ábrahám, and P. Cs. Ölveczky<br />
Def<strong>in</strong>ition 1. Given a set Π of atomic propositions, T<strong>CTL</strong> formulae are built<br />
us<strong>in</strong>g the follow<strong>in</strong>g abstract syntax:<br />
ϕ ::= true | p | ¬ϕ | ϕ ∧ ϕ | E ϕ UI ϕ | A ϕ UI ϕ<br />
where p ∈ Π and I is a time <strong>in</strong>terval.<br />
We omit the bound [0, ∞) as subscript and we write ≤ b, < b, ≥ a and > a for<br />
[0, b], [0, b), [a, ∞) and (a, ∞), respectively. We denote by T<strong>CTL</strong>cb the fragment<br />
of T<strong>CTL</strong> where all time bounds are of the form [a, b] with a < b, or [a, ∞).<br />
3.2 <strong><strong>Time</strong>d</strong> Kripke Structures and T<strong>CTL</strong> Semantics<br />
The semantics of T<strong>CTL</strong> formulae is def<strong>in</strong>ed on Kripke structures. A Kripke<br />
structure is a transition system with an associated label<strong>in</strong>g function, which maps<br />
each state <strong>in</strong> the transition system to the set of atomic propositions that hold<br />
<strong>in</strong> that state.<br />
A timed Kripke structure is a Kripke structure where each transition has the<br />
form s r<br />
−→ s ′ , where r denotes the duration of the transition step.<br />
Def<strong>in</strong>ition 2. Given a set of atomic propositions Π and a time doma<strong>in</strong> T , a<br />
timed Kripke structure is a triple T K = (S, T<br />
−→, L) where S is a set of states,<br />
T<br />
−→⊆ S×T ×S is a transition relation with duration, and L is a label<strong>in</strong>g function<br />
L : S → P(Π). The transition relation T<br />
−→ is total, 4 i.e., for each s ∈ S there<br />
exist r ∈ T , s ′ ∈ S such that (s, r, s ′ ) ∈ T<br />
−→. We write s r<br />
−→ s ′ if (s, r, s ′ ) ∈ T<br />
−→.<br />
We use a similar notation for timed paths <strong>in</strong> a timed Kripke structure T K as for<br />
r0 r1<br />
real-time rewrite theories. Thus, a timed path is written π = t0 −→ t1 −→ . . .,<br />
we def<strong>in</strong>e dπ m = m−1 i=0 ri, tπ m = tm and rπ m = rm, and the set of all timed fair<br />
paths orig<strong>in</strong>at<strong>in</strong>g <strong>in</strong> state t is denoted by tfPathsT K(t).<br />
The semantics of T<strong>CTL</strong> formulae is def<strong>in</strong>ed as follows:<br />
Def<strong>in</strong>ition 3. For timed Kripke structures T K = (S, T<br />
−→, L), states t ∈ S, and<br />
T<strong>CTL</strong> formulae ϕ, the po<strong>in</strong>twise satisfaction relation T K, t |=p ϕ is def<strong>in</strong>ed<br />
<strong>in</strong>ductively as follows:<br />
T K, t |=p true always.<br />
T K, t |=p p iff p ∈ L(t).<br />
T K, t |=p ¬ϕ1 iff T K, t |=p ϕ1.<br />
T K, t |=p ϕ1 ∧ ϕ2 iff T K, t |=p ϕ1 and T K, t |=p ϕ2.<br />
T K, t |=p E ϕ1 UI ϕ2 iff there exists π ∈ tfPaths T K(t) and an <strong>in</strong>dex k s.t.<br />
d π k ∈ I, T K, tπ k |=p ϕ2, and<br />
T K, t π l |=p ϕ1 for all 0 ≤ l < k.<br />
T K, t |=p A ϕ1 UI ϕ2 iff for each π ∈ tfPaths T K(t) there is an <strong>in</strong>dex k s.t.<br />
d π k ∈ I, T K, tπ k |=p ϕ2, and<br />
T K, t π l |=p ϕ1 for all 0 ≤ l < k.<br />
4 T<br />
T • T<br />
A transition relation −→ can be made total by def<strong>in</strong><strong>in</strong>g ( −→) = −→ ∪{(s, 0, s) ∈<br />
S × T × S | ¬∃ s ′ ∈ S, r ∈ T s.t. (s, r, s ′ ) ∈ T<br />
−→}.
<strong><strong>Time</strong>d</strong> <strong>CTL</strong> <strong>Model</strong> <strong>Check<strong>in</strong>g</strong> <strong>in</strong> <strong>Real</strong>-<strong>Time</strong> Maude 9<br />
For a timed Kripke structure T K = (S, T<br />
−→, L), a state t ∈ S and paths<br />
π, π ′ ∈ tfPathsT K(t) we say that π ′ is a simple time ref<strong>in</strong>ement of π if either<br />
π = π ′ or π ′ can be obta<strong>in</strong>ed from π by replac<strong>in</strong>g a transition tk<br />
rk<br />
−→ tk+1,<br />
r ′<br />
k k<br />
rk > 0, by a sequence tk −→ t r′′<br />
−→ tk+1 of transitions for some t ∈ S and time<br />
values r ′ k , r′′<br />
k > 0 with r′ k + r′′<br />
k = rk. A path π ′ is a time ref<strong>in</strong>ement of another<br />
path π if π ′ can be obta<strong>in</strong>ed from π by apply<strong>in</strong>g a (possibly <strong>in</strong>f<strong>in</strong>ite) number of<br />
time ref<strong>in</strong>ements. We also say that π is a time abstraction of π ′ .<br />
Def<strong>in</strong>ition 4. The cont<strong>in</strong>uous-time satisfaction relation T K, t |=c ϕ is def<strong>in</strong>ed<br />
<strong>in</strong>ductively as follows:<br />
T K, t |=c true always.<br />
T K, t |=c p iff p ∈ L(t).<br />
T K, t |=c ¬ϕ1 iff T K, t |=c ϕ1.<br />
T K, t |=c ϕ1 ∧ ϕ2 iff T K, t |=c ϕ1 and T K, t |=c ϕ2.<br />
T K, t |=c E ϕ1 UI ϕ2 iff there is a path π ∈ tfPathsT K(t) such that for each<br />
time ref<strong>in</strong>ement π ′ ∈ tfPathsT K(t) of π there is an<br />
<strong>in</strong>dex k s.t. d π′<br />
k<br />
∈ I, T K, tπ′<br />
k |=c ϕ2, and<br />
T K, t π′<br />
l |=c ϕ1 for all 0 ≤ l < k.<br />
T K, t |=c A ϕ1 UI ϕ2 iff for each path π ∈ tfPaths T K(t) there is a time<br />
ref<strong>in</strong>ement π ′ ∈ tfPaths T K(t) of π and an <strong>in</strong>dex k<br />
s.t. d π′<br />
k<br />
∈ I, T K, tπ′<br />
k |=c ϕ2, and<br />
T K, t π′<br />
l |=c ϕ1 for all 0 ≤ l < k.<br />
3.3 Associat<strong>in</strong>g <strong><strong>Time</strong>d</strong> Kripke Structures to <strong>Real</strong>-<strong>Time</strong> Rewrite<br />
Theories<br />
To each real-time rewrite theory we associate a timed Kripke structure as follows:<br />
Def<strong>in</strong>ition 5. Given a real-time rewrite theory R = (Σ, E, R, φ, τ), a set of<br />
atomic propositions Π and a protect<strong>in</strong>g extension (Σ ∪ Π, E ∪ D) ⊇ (Σ, E), we<br />
def<strong>in</strong>e the associated timed Kripke structure<br />
T K(R)Π = (T Σ/E,GlobalSystem, ( T<br />
−→R) • , LΠ),<br />
where ( T<br />
−→R) • ⊆ TΣ/E,GlobalSystem × TΣ/E,φ(<strong>Time</strong>) × TΣ/E,GlobalSystem conta<strong>in</strong>s<br />
r<br />
all transitions of the k<strong>in</strong>d t −→ t ′ which are also one-step rewrites <strong>in</strong> R and<br />
0<br />
all transitions of the k<strong>in</strong>d t −→ t for all those states t that cannot be further<br />
rewritten <strong>in</strong> R, and for LΠ : TΣ/E,GlobalSystem → P(Π) we have that p ∈ LΠ(t)<br />
if and only if E ∪ D ⊢ (t |= p) = true.<br />
We use this transformation to def<strong>in</strong>e R, LΠ, t0 |=c ϕ as T K(R)Π, t0 |=c<br />
ϕ, and similarly for the po<strong>in</strong>twise semantics. The model check<strong>in</strong>g problems<br />
T K(R)Π, t0 |=p ϕ and T K(R)Π, t0 |=c ϕ are decidable if<br />
– the equational specification <strong>in</strong> R is Church-Rosser and term<strong>in</strong>at<strong>in</strong>g,
10 D. Lepri, E. Ábrahám, and P. Cs. Ölveczky<br />
– the set of states reachable from t0 <strong>in</strong> the rewrite theory R is f<strong>in</strong>ite, and<br />
– given a pair of reachable states t and t ′ , the number of one-step rewrites of<br />
r<br />
the k<strong>in</strong>d t −→ t ′ <strong>in</strong> R is f<strong>in</strong>ite.<br />
As mentioned above, real-time rewrite theories generally conta<strong>in</strong> a time-nondeterm<strong>in</strong>istic<br />
tick rule, but s<strong>in</strong>ce <strong>Real</strong>-<strong>Time</strong> Maude executes such theories by<br />
apply<strong>in</strong>g a time sampl<strong>in</strong>g strategy σ, our model checker does not analyze R but<br />
the executable theory Rσ <strong>in</strong> which the time sampl<strong>in</strong>g strategy transformation<br />
has been applied. Thus, we associate a timed Kripke structure not to R, but<br />
to Rσ , and hence the third requirement is satisfied by all but the most esoteric<br />
cases; <strong>in</strong>deed, the tick rules <strong>in</strong> all <strong>Real</strong>-<strong>Time</strong> Maude applications we have seen<br />
are determ<strong>in</strong>istic, <strong>in</strong> the sense that there is at most one one-step tick rewrite<br />
r<br />
t −→ t ′ from any state, when the time sampl<strong>in</strong>g strategy is taken <strong>in</strong>to account.<br />
We denote by T K(R, t0)Π the timed Kripke structure associated to R which<br />
is restricted to states reachable from t0, and for states t reachable from t0 we<br />
write R, LΠ, t |= ϕ for T K(R, t0)Π, t |= ϕ.<br />
4 Sound and Complete T<strong>CTL</strong> <strong>Model</strong> <strong>Check<strong>in</strong>g</strong> for<br />
<strong>Real</strong>-<strong>Time</strong> Maude<br />
As mentioned above, for dense time doma<strong>in</strong>s, <strong>Real</strong>-<strong>Time</strong> Maude only analyzes<br />
those behaviors obta<strong>in</strong>ed by apply<strong>in</strong>g the tick rules accord<strong>in</strong>g to a selected<br />
time sampl<strong>in</strong>g strategy. The paper [29] specifies some conditions on a real-time<br />
rewrite theory R and on the atomic propositions that ensure that model check<strong>in</strong>g<br />
R maxDef (r) , i.e., us<strong>in</strong>g the maximal time sampl<strong>in</strong>g strategy, is a sound and<br />
complete model check<strong>in</strong>g procedure to check whether all behaviors <strong>in</strong> the orig<strong>in</strong>al<br />
model R satisfy an untimed LTL formula without the next operator.<br />
For example, if<br />
– no application of a tick rule changes the valuation of the atomic propositions<br />
<strong>in</strong> a formula (this requirement almost always holds <strong>in</strong> real applications, s<strong>in</strong>ce<br />
the only values changed by ticks are clock and timer values that usually do<br />
not appear <strong>in</strong> the formula);<br />
– <strong>in</strong>stantaneous rewrite rules can only be applied after maximal tick steps or<br />
after apply<strong>in</strong>g an <strong>in</strong>stantaneous rule,<br />
then model check<strong>in</strong>g R maxDef (r) gives a sound and complete model check<strong>in</strong>g<br />
procedure for R. 5 This result yields a feasible sound and complete model check<strong>in</strong>g<br />
procedure for many useful (dense-time) systems, that <strong>in</strong>clude many systems<br />
that cannot be modeled as, e.g., timed automata.<br />
Unfortunately, this completeness result does not carry over to timed temporal<br />
logic properties. Consider for example the T<strong>CTL</strong> formula ϕ = E F≥1 (E p U≥2 q).<br />
5 The requirements <strong>in</strong> [29] are weaker than described here; e.g., the valuation of the<br />
atomic propositions may change once <strong>in</strong> a sequence of maximal tick rewrites.
<strong><strong>Time</strong>d</strong> <strong>CTL</strong> <strong>Model</strong> <strong>Check<strong>in</strong>g</strong> <strong>in</strong> <strong>Real</strong>-<strong>Time</strong> Maude 11<br />
Then, we can have a sequence of only maximal tick steps (where we only show<br />
the atomic properties valid <strong>in</strong> the correspond<strong>in</strong>g states)<br />
p 3<br />
−→ p <strong>in</strong>st<br />
−→ q −→ · · · (¬p ∧ ¬q forever)<br />
that does not satisfy the formula ϕ, whereas if we can “split” up the maximal<br />
tick step <strong>in</strong>to three non-maximal tick steps, where time elapses by one time unit<br />
<strong>in</strong> each tick step, we get a behavior<br />
p 1<br />
−→ p 1<br />
−→ p 1<br />
−→ p <strong>in</strong>st<br />
−→ q −→ · · · (¬p ∧ ¬q forever)<br />
which makes ϕ hold for the system. Notice that the system satisfies the two<br />
strong criteria suggested above. It is also worth mention<strong>in</strong>g that this problem<br />
also applies to timed l<strong>in</strong>ear logics. For the system R <strong>in</strong>dicated <strong>in</strong> the example,<br />
the “timed LTL” formula ¬ (✸≥1 (p U≥2 q)) is satisfied by R maxDef (r) but not<br />
by R.<br />
In the follow<strong>in</strong>g we focus on dense time, s<strong>in</strong>ce we can achieve sound and<br />
complete model check<strong>in</strong>g for discrete time by explor<strong>in</strong>g all possible tick steps <strong>in</strong><br />
the po<strong>in</strong>twise semantics, and by advanc<strong>in</strong>g time by the smallest possible nonzero<br />
duration <strong>in</strong> the cont<strong>in</strong>uous semantics. Furthermore, as already mentioned,<br />
<strong>in</strong> this paper we restrict our treatment to T<strong>CTL</strong>cb formulas under the cont<strong>in</strong>uous<br />
semantics. 6<br />
Our goal is therefore to f<strong>in</strong>d a discrete abstraction of a real-time rewrite<br />
theory R, so that model check<strong>in</strong>g the abstraction (under the po<strong>in</strong>twise semantics)<br />
is equivalent to model check<strong>in</strong>g R under the cont<strong>in</strong>uous semantics. One part of<br />
our solution is to make sure that time progress “stops” at any time po<strong>in</strong>t when a<br />
time bound <strong>in</strong> the formula could be reached. This can be achieved if we split any<br />
tick step by an amount that divides all possible maximal tick durations and all<br />
possible f<strong>in</strong>ite non-zero time bounds <strong>in</strong> the formula. Let ¯r be the greatest common<br />
divisor of the durations of all maximal tick steps <strong>in</strong> R maxDef (r) reachable from the<br />
<strong>in</strong>itial state and each f<strong>in</strong>ite non-zero time bound <strong>in</strong> the formula; then “stopp<strong>in</strong>g”<br />
at each <strong>in</strong>terest<strong>in</strong>g time po<strong>in</strong>t should be acheieved if we divide each maximal<br />
tick step <strong>in</strong>to smaller steps of duration ¯r.<br />
However, the follow<strong>in</strong>g example shows that it is not sufficient to always advance<br />
time by this greatest common divisor ¯r to obta<strong>in</strong> a sound and complete<br />
abstraction under the cont<strong>in</strong>uous semantics. Consider a (dense-time) theory R<br />
that has only one behavior <strong>in</strong> terms of maximal tick steps, which we show here<br />
<strong>in</strong> terms of validity of the atomic proposition p <strong>in</strong> the correspond<strong>in</strong>g states:<br />
π = ¬p 1<br />
−→ ¬p <strong>in</strong>st<br />
−→ p <strong>in</strong>st<br />
−→ ¬p 1<br />
−→ · · · (¬p forever)<br />
That is, a p-state is reachable <strong>in</strong> exactly time 1, and ticks do not change the<br />
valuations of the atomic propositions. In this model all maximal tick steps have<br />
6 We are currently work<strong>in</strong>g on releas<strong>in</strong>g the restriction to closed bounds. However,<br />
our proof for the completeness result cannot be directly extended to T<strong>CTL</strong> formulas<br />
with open bounds.
12 D. Lepri, E. Ábrahám, and P. Cs. Ölveczky<br />
duration 1. Let’s consider the formula ϕ = E ϕ1 U [1,1] true, where ϕ1 is the<br />
formula E F [1,1] p. The formula ϕ says that ϕ1 must hold all the way until we<br />
reach time 1. The greatest common divisor of all maximal time <strong>in</strong>crements and<br />
all time values <strong>in</strong> ϕ is still 1, so the “greatest common divisor” abstraction is<br />
equivalent to R maxDef (r) . In particular, this abstraction (i.e., the above behavior)<br />
satisfies ϕ w.r.t. the <strong>in</strong>itial state π(0). However, R, L {p}, π(0) |=c ϕ does not hold,<br />
s<strong>in</strong>ce ϕ does not hold <strong>in</strong> the timed ref<strong>in</strong>ement (where the first tick has been split<br />
<strong>in</strong>to two smaller ones)<br />
π ′ = ¬p 1/2<br />
−→ ¬p 1/2<br />
−→ ¬p <strong>in</strong>st<br />
−→ p <strong>in</strong>st<br />
−→ ¬p 1<br />
−→ · · · (¬p forever)<br />
because ϕ1 does not hold <strong>in</strong> the second state <strong>in</strong> the ref<strong>in</strong>ement.<br />
Our approach is therefore to capture all these “<strong>in</strong>termediate” states by further<br />
splitt<strong>in</strong>g the “gcd” tick steps <strong>in</strong>to two smaller tick steps. In essence, we advance<br />
time not by ¯r, but by “half” the gcd ¯r <strong>in</strong> each tick step.<br />
To formalize this notion, let us first consider the time doma<strong>in</strong>. <strong>Real</strong>-time<br />
rewrite theories are parametric <strong>in</strong> their time doma<strong>in</strong>; the time doma<strong>in</strong> must only<br />
satisfy some abstract properties given <strong>in</strong> some functional theory def<strong>in</strong>ed <strong>in</strong> [28]<br />
that def<strong>in</strong>es the time doma<strong>in</strong> abstractly as a commutative monoid (0, ≤, T ime)<br />
with some additional operators, such as monus, where x monus y denotes x − y<br />
if y < x, and 0 otherwise. The follow<strong>in</strong>g theory states that there exist functions<br />
gcd and half on the non-zero time values with the expected properties.<br />
fth GCD-TIME-DOMAIN is <strong>in</strong>clud<strong>in</strong>g LTIME-INF .<br />
sort Nz<strong>Time</strong> . subsort Nz<strong>Time</strong> < <strong>Time</strong> .<br />
cmb T:<strong>Time</strong> : Nz<strong>Time</strong> if T:<strong>Time</strong> =/= 0 .<br />
op gcd : Nz<strong>Time</strong> Nz<strong>Time</strong> -> Nz<strong>Time</strong> [assoc comm] .<br />
op _divides_ : Nz<strong>Time</strong> Nz<strong>Time</strong> -> Bool .<br />
op half : Nz<strong>Time</strong> -> Nz<strong>Time</strong> .<br />
vars T1 T2 T3 : Nz<strong>Time</strong> . vars T T’ : <strong>Time</strong> .<br />
eq T1 divides T1 = true .<br />
ceq T1 divides T2 = false if T2 < T1 .<br />
eq T1 divides (T1 + T2) = T1 divides T2 .<br />
eq gcd(T1, T2) divides T1 = true .<br />
ceq gcd(T1, T2) >= T3 if T3 divides T1 /\ T3 divides T2 .<br />
eq half(NZT) + half(NZT) = NZT .<br />
endfth<br />
In the follow<strong>in</strong>g we assume that all considered time doma<strong>in</strong>s satisfy the theory<br />
GCD-TIME-DOMAIN, and write gcd and half for the <strong>in</strong>terpretation of gcd and half,<br />
respectively. Note that the usual dense time doma<strong>in</strong>s, such as the nonnegative<br />
rationals, satisfy this theory with the standard <strong>in</strong>terpretation of division and the<br />
gcd operator.
<strong><strong>Time</strong>d</strong> <strong>CTL</strong> <strong>Model</strong> <strong>Check<strong>in</strong>g</strong> <strong>in</strong> <strong>Real</strong>-<strong>Time</strong> Maude 13<br />
The real-time rewrite theory R gcd(t0,r,ϕ) is obta<strong>in</strong>ed from the tick-robust realtime<br />
rewrite theory R, a state t0 <strong>in</strong> R, and a T<strong>CTL</strong> formula ϕ, by advanc<strong>in</strong>g<br />
time by “half” the greatest common divisor of all the follow<strong>in</strong>g values:<br />
– all tick step durations appear<strong>in</strong>g <strong>in</strong> paths from tfPaths R maxDef (r)(t0) and<br />
– all f<strong>in</strong>ite non-zero lower and upper bounds of all temporal operators <strong>in</strong> ϕ.<br />
Def<strong>in</strong>ition 6. For a real-time rewrite theory R whose time doma<strong>in</strong> satisfies the<br />
theory GCD-TIME-DOMAIN, a non-zero time value r, a T<strong>CTL</strong> formula ϕ and a<br />
state t0 of R we def<strong>in</strong>e<br />
T1(R, t0, r) = {r ′ ∈ Nz<strong>Time</strong> | ∃π ∈ tfPaths R maxDef (r)(t0). ∃i ≥ 0. r ′ = r π i }<br />
T2(ϕ) = {r ∈ Nz<strong>Time</strong> | there exists a subformula E ϕ1 UI ϕ2 or<br />
GCD(R, r, ϕ, t0) = gcd(T1(R, t0, r) ∪ T2(ϕ)).<br />
A ϕ1 UI ϕ2 of ϕ with r a non-zero f<strong>in</strong>ite<br />
lower or upper bound <strong>in</strong> I}<br />
If T1(R, t0, r) and T2(ϕ) are f<strong>in</strong>ite then the GCD value is well-def<strong>in</strong>ed and<br />
we can def<strong>in</strong>e the real-time rewrite theory R gcd(t0,r,ϕ) as follows:<br />
Def<strong>in</strong>ition 7. Given a real-time rewrite theory R whose time doma<strong>in</strong> satisfies<br />
the theory GCD-TIME-DOMAIN, a non-zero time value r, a T<strong>CTL</strong> formula ϕ, a<br />
state t0 of R, and assume that ¯r = GCD(R, t0, r, ϕ) is a def<strong>in</strong>ed non-zero time<br />
value. Then R gcd(t0,r,ϕ) is def<strong>in</strong>ed as R but where each tick rule of the forms (†),<br />
(∗), and (§) is replaced by the respective tick rule:<br />
crl [tick] : {t} => {t ′ } <strong>in</strong> time x if x := half (¯r) /\ cond [nonexec] .<br />
crl [tick] : {t} => {t ′ } <strong>in</strong> time x if x := half (¯r) /\ cond [nonexec] .<br />
crl [tick] : {t} => {t ′ } <strong>in</strong> time x if x := half (¯r) [nonexec] .<br />
The follow<strong>in</strong>g lemma states that the evaluation of the formula ϕ and its<br />
subformulas does not change <strong>in</strong>side tick steps of R gcd(t0,r,ϕ) .<br />
Lemma 1. Assume a time-robust real-time rewrite theory R whose time doma<strong>in</strong><br />
satisfies the theory GCD-TIME-DOMAIN. Let Π be a set of tick-<strong>in</strong>variant atomic<br />
propositions, and assume a protect<strong>in</strong>g extension of R def<strong>in</strong><strong>in</strong>g the atomic propositions<br />
<strong>in</strong> Π and <strong>in</strong>duc<strong>in</strong>g a label<strong>in</strong>g function LΠ. Let t0 be a state of R, r a<br />
non-zero time value of sort <strong>Time</strong>, ϕ a T<strong>CTL</strong>cb formula over Π, and assume that<br />
¯r = GCD(R, t0, r, ϕ) is a def<strong>in</strong>ed non-zero time value.<br />
Then for each subformula ϕ ′ of ϕ, each time-divergent path π ∈ tfPathsR(t0) r π<br />
i<br />
and for all tick step sequences tπ i −→ . . . rπ<br />
j−1<br />
−→ tπ j <strong>in</strong> π satisfy<strong>in</strong>g n· ¯r < dπi < dπj <<br />
(n + 1) · ¯r for some n we have that<br />
R, LΠ, t π i |=c ϕ ′<br />
iff R, LΠ, t π j |=c ϕ ′ .<br />
Proof. In the follow<strong>in</strong>g we use N0 and N for the set of all natural numbers<br />
<strong>in</strong>clud<strong>in</strong>g resp. exclud<strong>in</strong>g 0. The proof is by <strong>in</strong>duction on the structure of ϕ ′ .<br />
Base cases:
14 D. Lepri, E. Ábrahám, and P. Cs. Ölveczky<br />
– ϕ ′ = true: R, t |=c true for all t by the def<strong>in</strong>ition of |=c.<br />
– ϕ ′ = p: S<strong>in</strong>ce all steps between tπ i and tπj are tick steps, the property follows<br />
from the tick-<strong>in</strong>variance of p.<br />
Assume now that the lemma holds for the subformulae ϕ1 and ϕ2.<br />
– ϕ ′ = ¬ϕ1:<br />
– ϕ ′ = ϕ1 ∧ ϕ2:<br />
– ϕ ′ = E ϕ1 UI ϕ2:<br />
R, t π i |=c ¬ϕ1 ⇐⇒ not (R, t π i |=c ϕ1)<br />
<strong>in</strong>duction<br />
⇐⇒ not (R, t π j |=c ϕ1)<br />
⇐⇒ R, t π j |=c ¬ϕ1 .<br />
R, t π i |=c ϕ1 ∧ ϕ2 ⇐⇒ R, t π i |=c ϕ1 and R, t π i |=c ϕ2<br />
<strong>in</strong>duction<br />
⇐⇒ R, t π j |=c ϕ1 and R, t π j |=c ϕ2<br />
⇐⇒ R, t π j |=c ϕ1 ∧ ϕ2 .<br />
We def<strong>in</strong>e d1 = dπ i −n¯r, d2 = dπ j −dπi and d3 = (n+1)¯r−d π j . Let furthermore<br />
πpre denote the prefix of π end<strong>in</strong>g at tπ i and let πpre i denote the tick sequence<br />
tπ ri<br />
i −→ . . . rj−1<br />
−→ tπ j . Let ml¯r be the lower bound of I. The upper bound of I<br />
is either INF or a f<strong>in</strong>ite bound mu¯r.<br />
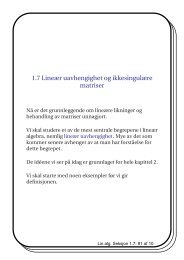
“⇒”: The proof structure is illustrated on Figure 1.<br />
Assume that R, t π i |=c E ϕ1 UI ϕ2 holds. Then by def<strong>in</strong>ition there is a path<br />
πi ∈ tfPaths T K(t π i ) such that for each time ref<strong>in</strong>ement π′ i ∈ tfPaths T K(t π i )<br />
of πi there is an <strong>in</strong>dex k s.t. d π′ i<br />
i<br />
k ∈ I, T K, tπ′<br />
k |=c ϕ2, and T K, t π′ i<br />
l |=c ϕ1 for<br />
all 0 ≤ l < k.<br />
Let πi be such a path. Due to time robustness, πi has a time ref<strong>in</strong>ement<br />
π ′ i ∈ tfPathsT K(tπ i ) which conta<strong>in</strong>s the state tπj at time po<strong>in</strong>t d2, a state t∗ at time po<strong>in</strong>t7 ml¯r − d1/2 <strong>in</strong> case ml > 0, and a state t∗∗ at time po<strong>in</strong>t<br />
ml¯r + d2 (which is tπ j <strong>in</strong> case ml = 0). Note that time robustness assures<br />
that the state <strong>in</strong> π ′ i at time po<strong>in</strong>t d2 is tπ j .<br />
Let π ′ i be such a path. Let πpre′ i and πj be the prefix resp. suffix of π ′ i<br />
end<strong>in</strong>g resp. start<strong>in</strong>g at tπ j at the time po<strong>in</strong>t d2. We show that πj satisfies<br />
the conditions for R, tπ j |=c E ϕ1 UI ϕ2.<br />
Let π ′ j be a time ref<strong>in</strong>ement of πj. Then the concatenation π ′′<br />
i<br />
of πpre′<br />
i<br />
π ′ j is a time ref<strong>in</strong>ement of πi. By assumption there is an <strong>in</strong>dex k s.t. d π′′<br />
i<br />
k<br />
and<br />
∈ I,<br />
T K, t π′′<br />
i<br />
k |=c ϕ2, and T K, t π′′<br />
i<br />
l |=c ϕ1 for all 0 ≤ l < k.<br />
Let k be such an <strong>in</strong>dex and let π ′ be the concatenation of πpre and π ′′<br />
i .<br />
Remember that ml¯r is the lower bound of I. We dist<strong>in</strong>guish between (i)<br />
d π′′<br />
i<br />
k ∈ I1 = [ml¯r, ml¯r + d2 + d3) and (ii) d π′′<br />
i<br />
k ∈ I2 = I\I1.<br />
7 For <strong>in</strong>tuition we sample the middle po<strong>in</strong>t between ml¯r − d1 and ml¯r. However, any<br />
time po<strong>in</strong>t <strong>in</strong> the <strong>in</strong>terval (ml¯r − d1, ml¯r) would fit for our purpose.
π :<br />
πi :<br />
π ′ i :<br />
πj :<br />
π ′ j :<br />
π ′′<br />
i :<br />
π ′ :<br />
<strong><strong>Time</strong>d</strong> <strong>CTL</strong> <strong>Model</strong> <strong>Check<strong>in</strong>g</strong> <strong>in</strong> <strong>Real</strong>-<strong>Time</strong> Maude 15<br />
0 ¯r 2¯r 3¯r 4¯r 5¯r<br />
t π i<br />
t π j<br />
n¯r d1 d2 d3<br />
π pre π pre<br />
i<br />
t π i<br />
t π i<br />
π pre′<br />
i<br />
d2<br />
t π j<br />
ml ¯r− d 1 2<br />
t ∗<br />
t π j t ∗<br />
t π j t ∗<br />
t π i t π j t ∗<br />
π pre′<br />
i<br />
t π i t π j t ∗<br />
π pre π ′′<br />
i<br />
I<br />
ml ¯r+d2<br />
Fig. 1: Lemma 1: Proof structure for the “⇒” direction of existentially quantified<br />
bounded until<br />
I1<br />
πj<br />
I<br />
π ′ j<br />
t ∗∗<br />
t ∗∗<br />
t ∗∗<br />
t ∗∗<br />
t ∗∗<br />
I2<br />
I
16 D. Lepri, E. Ábrahám, and P. Cs. Ölveczky<br />
(i) Assume first that d π′′<br />
i<br />
k ∈ I1 = [ml¯r, ml¯r + d2 + d3). We observe that<br />
π ′′<br />
i conta<strong>in</strong>s the state t∗∗ at time po<strong>in</strong>t ml¯r + d2 (we added this sample<br />
po<strong>in</strong>t when ref<strong>in</strong><strong>in</strong>g πi to π ′ i ), thus t∗∗ appears <strong>in</strong> π ′ at time po<strong>in</strong>t (n +<br />
ml)¯r + d1 + d2. Furthermore, we assumed that d π′′<br />
i<br />
k<br />
d π′′<br />
i<br />
k < ml¯r + d2 + d3, imply<strong>in</strong>g that t π′′<br />
i<br />
∈ I1, i.e., ml¯r ≤<br />
k appears <strong>in</strong> π′ at a time po<strong>in</strong>t <strong>in</strong><br />
[(n + ml)¯r + d1, (n + ml + 1)¯r). Thus both t∗∗ and t π′′ i<br />
k appear <strong>in</strong> π′ <strong>in</strong><br />
the <strong>in</strong>terval ((n + ml)¯r, (n + ml + 1)¯r), and from T K, t π′′ i<br />
k |=c ϕ2 we get<br />
by <strong>in</strong>duction that T K, t∗∗ |=c ϕ2.<br />
Note that t∗∗ also appears <strong>in</strong> π ′ j . We want to show that the <strong>in</strong>dex of t∗∗ <strong>in</strong><br />
π ′ j satisfies the conditions for the satisfaction of the until formula by π′ j .<br />
We already have shown that T K, t∗∗ |=c ϕ2. Additionally, t∗∗ appears <strong>in</strong><br />
at time po<strong>in</strong>t ml¯r,<br />
π ′′<br />
i at time po<strong>in</strong>t ml¯r + d2, therefore it appears <strong>in</strong> π ′ j<br />
which is the left end po<strong>in</strong>t of the <strong>in</strong>terval I.<br />
In case ml = 0 we are done, because tπ j satisfies ϕ2 and there are no<br />
states prior to tπ j <strong>in</strong> π′ j . Otherwise, if ml > 0, it rema<strong>in</strong>s to show that all<br />
states prior to t∗∗ <strong>in</strong> π ′ j satisfy ϕ1. There are two cases.<br />
∗ We know that all states t π′′<br />
i<br />
l<br />
with l < k (especially all states at time<br />
po<strong>in</strong>ts less than ml¯r) satisfy ϕ1. We conclude that the states <strong>in</strong> π ′ j at<br />
time po<strong>in</strong>ts less than ml¯r − d2, build<strong>in</strong>g a subset of the above states,<br />
all satisfy ϕ1.<br />
∗ It rema<strong>in</strong>s to show that all states at time po<strong>in</strong>ts from [ml¯r −d2, ml¯r)<br />
<strong>in</strong> π ′ j also satisfy ϕ1. Notice that π ′ i conta<strong>in</strong>s the state t∗ at time<br />
po<strong>in</strong>t ml¯r − d1/2. S<strong>in</strong>ce this time po<strong>in</strong>t is below the lower bound of<br />
I we have T K, t ∗ |=c ϕ1.<br />
This state t ∗ appears <strong>in</strong> π ′ at time po<strong>in</strong>t<br />
(n¯r + d1) + (ml¯r − d1/2) = (n + ml)¯r + d1/2 .<br />
By <strong>in</strong>duction we get that all states appear<strong>in</strong>g <strong>in</strong> π ′ at time po<strong>in</strong>ts<br />
from the <strong>in</strong>terval ((n + ml)¯r, (n + ml + 1)¯r) satisfy ϕ1. I.e., all states<br />
<strong>in</strong> π ′ j at time po<strong>in</strong>ts from<br />
((n + ml)¯r − (n¯r + d1 + d2), (n + ml + 1)¯r − (n¯r + d1 + d2))<br />
= (ml¯r − d1 − d2, (ml + 1)¯r − d1 − d2)<br />
⊇ [ml¯r − d2, ml¯r)<br />
satisfy ϕ1.<br />
(ii) For the case d π′′ i<br />
k ∈ I2 = I\I1 let v be the number of states <strong>in</strong> π pre′<br />
i . We<br />
show that k − v is a proper <strong>in</strong>dex for the satisfaction of the bounded<br />
until along π ′ j .<br />
We observe that t π′<br />
j<br />
l<br />
T K, t π′<br />
j<br />
i = tπ′′<br />
l+v<br />
i<br />
for all l. Therefore, T K, tπ′′<br />
k |=c ϕ2 implies<br />
k−v |=c ϕ2. S<strong>in</strong>ce d π′′ i<br />
k ∈ I2 we have d π′′ i<br />
k ≥ ml¯r + d2 + d3 and<br />
thus d π′<br />
j<br />
i<br />
k−v = dπ′′<br />
k − d2 ≥ ml¯r + d3, i.e., the duration of π ′ j until the<br />
(k − v)-th state is above the lower bound of I. It is easy to see that this
<strong><strong>Time</strong>d</strong> <strong>CTL</strong> <strong>Model</strong> <strong>Check<strong>in</strong>g</strong> <strong>in</strong> <strong>Real</strong>-<strong>Time</strong> Maude 17<br />
duration is also below the upper bound (d π′′<br />
i<br />
k is below the upper bound<br />
and d π′<br />
j<br />
k−v<br />
i = dπ′′<br />
k − d2 < d π′′<br />
i<br />
k ).<br />
F<strong>in</strong>ally, T K, t π′′ i<br />
l+v |=c ϕ1 implies T K, t π′<br />
j<br />
l |=c ϕ1 for all l < k−v Therefore,<br />
the <strong>in</strong>dex (k − v) is appropriate to show that the path π ′ j satisfies the<br />
bounded until property.<br />
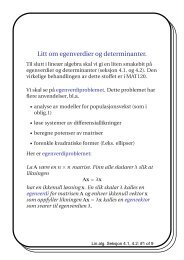
“⇐”: The proof structure is illustrated <strong>in</strong> Figure 2.<br />
Assume that R, t π j |=c E ϕ1 UI ϕ2 holds. Then by def<strong>in</strong>ition there is a path<br />
πj ∈ tfPaths T K(t π j ) such that for each time ref<strong>in</strong>ement π′ j ∈ tfPaths T K(t π j )<br />
of πj there is an <strong>in</strong>dex k s.t. d π′ j<br />
j<br />
k ∈ I, T K, tπ′<br />
k |=c ϕ2, and T K, t π′<br />
j<br />
l |=c ϕ1 for<br />
all 0 ≤ l < k.<br />
Let πj be such a path. Remember that mu¯r denotes the upper bound of I <strong>in</strong><br />
case it is f<strong>in</strong>ite. Let π ′ j be πj if the upper bound of I is INF or 0 and a time<br />
ref<strong>in</strong>ement of πj which conta<strong>in</strong>s the state t∗∗ at the time po<strong>in</strong>t mu¯r − d2<br />
otherwise. Then the above properties hold also for π ′ j .<br />
Let πi be the concatenation of π pre<br />
i (appear<strong>in</strong>g <strong>in</strong> π) and π ′ j . We show that<br />
πi satisfies the requirements for R, tπ i |=c E ϕ1 UI ϕ2.<br />
Let π ′ i be a time ref<strong>in</strong>ement of πi. Then tπ j appears <strong>in</strong> π′ i at time po<strong>in</strong>t d2 at<br />
some position v.<br />
Let π ′′<br />
j be the suffix of π′ i start<strong>in</strong>g at position v. Then π′′ j is a time ref<strong>in</strong>ement<br />
of π ′ j<br />
T K, t π′′<br />
j<br />
l<br />
j<br />
. Therefore there must be an <strong>in</strong>dex k s.t. dπ′′<br />
k<br />
j<br />
∈ I, T K, tπ′′<br />
k |=c ϕ2, and<br />
|=c ϕ1 for all 0 ≤ l < k. We dist<strong>in</strong>guish between k = 0 and k > 0.<br />
k = 0 For the case k = 0 notice that t π′′<br />
j<br />
0 = tπ j and thus T K, tπ j |=c ϕ2. By<br />
<strong>in</strong>duction we get T K, t π i |=c ϕ2. Furthermore, s<strong>in</strong>ce d π′′<br />
j<br />
0<br />
j<br />
= 0 and dπ′′ 0<br />
∈ I,<br />
the lower bound of I must be 0. I.e., the <strong>in</strong>dex 0 satisfies the condition<br />
for the bounded until on the path π ′ i .<br />
k > 0 Otherwise, if k > 0 then, s<strong>in</strong>ce t π′′<br />
j<br />
0 = tπj we get T K, tπj |=c ϕ1 and by<br />
<strong>in</strong>duction T K, t π′<br />
i<br />
l |=c ϕ1 for all l < v (i.e., all states <strong>in</strong> the prefix π pre′<br />
i<br />
of π ′ i end<strong>in</strong>g at tπj at time po<strong>in</strong>t d2 satisfy ϕ1).<br />
(i) If the upper bound of I is INF then we show that k+v is an appropri-<br />
ate <strong>in</strong>dex to satisfy the bounded until along π ′ j<br />
i . From T K, tπ′′<br />
k |=c ϕ2<br />
and t π′′<br />
j i<br />
i<br />
k = tπ′<br />
k+v we conclude that T K, tπ′<br />
k+v |=c ϕ2. Furthermore, d π′′<br />
j<br />
is above the lower bound of I and d π′<br />
i<br />
j<br />
k+v = dπ′′<br />
k + d2, i.e., d π′<br />
i<br />
k+v ∈ I.<br />
F<strong>in</strong>ally, all states with <strong>in</strong>dices from v to (k + v − 1) <strong>in</strong> π ′ i satisfy ϕ1,<br />
s<strong>in</strong>ce they also appear <strong>in</strong> π ′′<br />
j before the <strong>in</strong>dex k. We have already<br />
shown above that the states with <strong>in</strong>dices up to v also satisfy ϕ1,<br />
therefore the bounded until is satisfied along the path π ′ i .<br />
(ii) Assume next that the upper bound mu¯r of I is f<strong>in</strong>ite. Note that<br />
k > 0 implies mu > 0. We first assume d π′′<br />
j<br />
k ∈ I2 = (mu¯r − d2, mu¯r],<br />
and consider d π′′<br />
j<br />
k ∈ I1 = I\I2 <strong>in</strong> case (iii).<br />
k
18 D. Lepri, E. Ábrahám, and P. Cs. Ölveczky<br />
π :<br />
πj :<br />
π ′ j :<br />
πi :<br />
π ′ i :<br />
π ′′<br />
j :<br />
π ′ :<br />
0 ¯r 2¯r 3¯r 4¯r 5¯r<br />
t π i<br />
t π j<br />
n¯r d1 d2 d3<br />
π pre π pre<br />
i<br />
t π i<br />
t π i<br />
π pre<br />
i<br />
π pre′<br />
i<br />
t π j<br />
t π j<br />
t π j<br />
t π j<br />
π ′ j<br />
I<br />
π ′′<br />
j<br />
I<br />
mu ¯r−d2<br />
I1<br />
t ∗∗<br />
t ∗∗<br />
t ∗∗<br />
t π j t ∗∗<br />
t π i t π j t ∗∗<br />
π pre π ′ i<br />
Fig. 2: Lemma 1: Proof structure for the “⇐” direction of existentially quantified<br />
bounded until<br />
I<br />
I2
<strong><strong>Time</strong>d</strong> <strong>CTL</strong> <strong>Model</strong> <strong>Check<strong>in</strong>g</strong> <strong>in</strong> <strong>Real</strong>-<strong>Time</strong> Maude 19<br />
Assume that d π′′<br />
j<br />
k ∈ I2 and let π ′ be the concatenation π pre and π ′ i .<br />
The state t π′′<br />
j<br />
k<br />
appears <strong>in</strong> π′′<br />
j<br />
by assumption at a time po<strong>in</strong>t <strong>in</strong> (mu¯r−<br />
d2, mu¯r], and therefore also <strong>in</strong> π ′ i at a time po<strong>in</strong>t <strong>in</strong> (mu¯r, mu¯r + d2]<br />
and <strong>in</strong> π ′ at a time po<strong>in</strong>t <strong>in</strong> ((n + mu)¯r + d1, (n + mu)¯r + d1 + d2].<br />
By construction π ′ j conta<strong>in</strong>s the state t∗∗ at time po<strong>in</strong>t mu¯r − d2.<br />
Aga<strong>in</strong> by construction, also π ′ i conta<strong>in</strong>s t∗∗ at time po<strong>in</strong>t mu¯r − d2 +<br />
d2 = mu¯r. Therefore, the state t ∗∗ appears also <strong>in</strong> π ′ at time po<strong>in</strong>t<br />
(n + mu)¯r + d1.<br />
We conclude that both t π′′ j<br />
k and t∗∗ appear <strong>in</strong> π ′ with<strong>in</strong> the time<br />
<strong>in</strong>terval ((n + mu)¯r, (n + mu + 1)¯r). From T K, t π′′ j<br />
k |=c ϕ2 we get<br />
therefore by <strong>in</strong>duction T K, t∗∗ |=c ϕ2.<br />
S<strong>in</strong>ce t∗∗ appears <strong>in</strong> π ′ i at time po<strong>in</strong>t mu¯r be<strong>in</strong>g the upper bound of<br />
I, also the time bound of the until is satisfied for t∗∗ on π ′ i .<br />
F<strong>in</strong>ally, we have already shown that all states up to <strong>in</strong>dex v <strong>in</strong> π ′ i<br />
satisfy ϕ1. This holds also for all rema<strong>in</strong><strong>in</strong>g states preceed<strong>in</strong>g t∗∗ <strong>in</strong><br />
, s<strong>in</strong>ce they also appear <strong>in</strong> π′′ before the <strong>in</strong>dex k. Thus the <strong>in</strong>dex<br />
π ′ i j<br />
of t∗∗ <strong>in</strong> π ′ i satisfies the condition of the bounded until on π′ i .<br />
(iii) For the case d π′′<br />
j<br />
k ∈ I1 = I\I2 we observe that t π′ i<br />
l<br />
j<br />
= tπ′′<br />
l−v for all l ≥ v.<br />
Therefore, T K, t π′′ j<br />
k |=c ϕ2 implies T K, t π′<br />
i<br />
k+v |=c ϕ2. S<strong>in</strong>ce d π′′ j<br />
k<br />
∈ I2<br />
we have d π′′<br />
j<br />
k ≤ mu¯r − d2 and thus d π′ i<br />
j<br />
k+v = dπ′′<br />
k + d2 ≤ mu¯r, i.e., the<br />
duration of π ′ i until the (k + v)-th state is below the upper bound of<br />
I. It is easy to see that this duration is also above the lower bound<br />
(d π′′<br />
j<br />
k is above the lower bound and d π′<br />
i<br />
j<br />
k+v = dπ′′<br />
k + d2 > d π′′<br />
j<br />
k ).<br />
We have already shown above that the states with <strong>in</strong>dices up to v<br />
satisfy ϕ1. Furthermore, T K, t π′′<br />
j<br />
l<br />
|=c ϕ1 implies T K, t π′<br />
i<br />
l+v |=c ϕ1 for<br />
all l < k Therefore, the <strong>in</strong>dex (k + v) is appropriate to show that the<br />
path π ′ i satisfies the bounded until property.<br />
– ϕ = A ϕ1 UI ϕ2,<br />
“⇒”: This proof case it quite analogous to the “⇒” direction of the existentially<br />
quantified bounded until case. The proof structure is illustrated <strong>in</strong><br />
Figure 3.<br />
Assume that R, tπ i |=c A ϕ1 UI ϕ2 holds. Then by def<strong>in</strong>ition each path<br />
πi ∈ tfPathsT K(tπ i ) has a time ref<strong>in</strong>ement π′ i ∈ tfPathsT K(tπ i ) such that for<br />
some <strong>in</strong>dex k with d π′<br />
i<br />
0 ≤ l < k.<br />
k<br />
i<br />
∈ I we have T K, tπ′<br />
k |=c ϕ2, and T K, t π′<br />
i<br />
l |=c ϕ1 for all<br />
We show that R, tπ j |=c A ϕ1 UI ϕ2 holds. Let πj ∈ tfPathsT K(tπ j ) be a path.<br />
Due to time robustness, πj has a time ref<strong>in</strong>ement π ′ j ∈ tfPathsT K(tπ j ) which<br />
conta<strong>in</strong>s a state t∗∗ at time po<strong>in</strong>t ml¯r (which is tπ j <strong>in</strong> case ml = 0) and a<br />
state t∗ at time po<strong>in</strong>t ml¯r − d2 − d1/2 <strong>in</strong> case ml > 0.<br />
Let π ′ j be such a time ref<strong>in</strong>ement and let πi be the concatenation of π pre<br />
i<br />
and<br />
π ′ j . From R, tπi |=c A ϕ1 UI ϕ2 we conclude that there is a time ref<strong>in</strong>ement
20 D. Lepri, E. Ábrahám, and P. Cs. Ölveczky<br />
π :<br />
πj :<br />
π ′ j :<br />
πi :<br />
π ′ i :<br />
π ′′<br />
j :<br />
π ′ :<br />
0 ¯r 2¯r 3¯r 4¯r 5¯r<br />
t π i<br />
t π j<br />
n¯r d1 d2 d3<br />
π pre π pre<br />
i<br />
t π j<br />
ml ¯r−d2− d 1 2<br />
t π j t ∗<br />
t π i t π j t ∗<br />
π pre<br />
i<br />
t π i t π j t ∗<br />
π pre′<br />
i<br />
t π j t ∗<br />
t π i t π j t ∗<br />
π pre π ′ i<br />
Fig. 3: Lemma 1: Proof structure for the “⇒” direction of universally quantified<br />
bounded until<br />
I1<br />
π ′ j<br />
π ′′<br />
j<br />
ml ¯r<br />
I<br />
t ∗∗<br />
t ∗∗<br />
t ∗∗<br />
t ∗∗<br />
t ∗∗<br />
I2<br />
I<br />
I
<strong><strong>Time</strong>d</strong> <strong>CTL</strong> <strong>Model</strong> <strong>Check<strong>in</strong>g</strong> <strong>in</strong> <strong>Real</strong>-<strong>Time</strong> Maude 21<br />
π ′ i of πi and an <strong>in</strong>dex k s.t. d π′<br />
i<br />
i<br />
k ∈ I, T K, tπ′<br />
k |=c ϕ2, and T K, t π′ i<br />
l |=c ϕ1 for<br />
all 0 ≤ l < k. Let π ′ i be such a path and k such an <strong>in</strong>dex.<br />
Note that π ′ i conta<strong>in</strong>s the state tπj at time po<strong>in</strong>t d2. Let π pre′<br />
i and π ′′<br />
j be<br />
the prefix resp. suffix of π ′ i end<strong>in</strong>g resp. start<strong>in</strong>g at that state. Let v be the<br />
number of states <strong>in</strong> π pre′<br />
i and let π ′ be the concatenation of πpre and π ′ i . We<br />
show that the bounded until is satisfied along π ′′<br />
j , be<strong>in</strong>g a time ref<strong>in</strong>ement<br />
of πj.<br />
Remember that ml¯r is the lower bound of I. We dist<strong>in</strong>guish between (i)<br />
d π′<br />
i<br />
k ∈ I1 = [ml¯r, ml¯r + d2 + d3) and (ii) d π′<br />
i<br />
k ∈ I2 = I\I1.<br />
(i) Assume first that d π′ i<br />
k ∈ I1 = [ml¯r, ml¯r + d2 + d3). We observe that π ′ i<br />
conta<strong>in</strong>s the state t∗∗ at time po<strong>in</strong>t ml¯r + d2 (we added this sample<br />
po<strong>in</strong>t when ref<strong>in</strong><strong>in</strong>g πj to π ′ j ), thus t∗∗ appears <strong>in</strong> π ′ at time po<strong>in</strong>t (n +<br />
ml)¯r + d1 + d2. Furthermore, we assumed that d π′<br />
i<br />
k ∈ I1, i.e., ml¯r ≤<br />
d π′<br />
i<br />
k < ml¯r + d2 + d3, imply<strong>in</strong>g that t π′ i<br />
[(n + ml)¯r + d1, (n + ml + 1)¯r). Thus both t∗∗ and t π′ i<br />
k appear <strong>in</strong> π′ <strong>in</strong><br />
the <strong>in</strong>terval ((n + ml)¯r, (n + ml + 1)¯r), and from T K, t π′<br />
i<br />
k |=c ϕ2 we get<br />
by <strong>in</strong>duction that T K, t∗∗ |=c ϕ2.<br />
k appears <strong>in</strong> π′ at a time po<strong>in</strong>t <strong>in</strong><br />
Note that t ∗∗ also appears <strong>in</strong> π ′′<br />
j . We want to show that the <strong>in</strong>dex of t∗∗ <strong>in</strong><br />
π ′′<br />
j<br />
satisfies the conditions for the satisfaction of the until formula by π′′<br />
j .<br />
We already have shown that T K, t ∗∗ |=c ϕ2. Additionally, t ∗∗ appears <strong>in</strong><br />
π ′′<br />
j at time po<strong>in</strong>t ml¯r, which is the left end po<strong>in</strong>t of the <strong>in</strong>terval I.<br />
In case ml = 0 we are done, because there are no states prior to t∗∗ <strong>in</strong><br />
π ′′<br />
j . Otherwise, if ml > 0, it rema<strong>in</strong>s to show that all states prior to t∗∗ <strong>in</strong> π ′′<br />
j satisfy ϕ1. There are two cases.<br />
∗ We know that all states t π′<br />
i<br />
l<br />
with l < k (especially all states at time<br />
po<strong>in</strong>ts less than ml¯r) satisfy ϕ1. We conclude that the states <strong>in</strong> π ′′<br />
j at<br />
time po<strong>in</strong>ts less than ml¯r − d2, build<strong>in</strong>g a subset of the above states,<br />
all satisfy ϕ1.<br />
∗ It rema<strong>in</strong>s to show that all states at time po<strong>in</strong>ts from [ml¯r −d2, ml¯r)<br />
<strong>in</strong> π ′′<br />
j also satisfy ϕ1. Notice that π ′ i conta<strong>in</strong>s the state t∗ at time<br />
po<strong>in</strong>t ml¯r − d1/2. S<strong>in</strong>ce this time po<strong>in</strong>t is below the lower bound of<br />
I we have T K, t ∗ |=c ϕ1.<br />
This state t ∗ appears <strong>in</strong> π ′ is at time po<strong>in</strong>t<br />
(n¯r + d1) + (ml¯r − d1/2) = (n + ml)¯r + d1/2 .<br />
By <strong>in</strong>duction we get that all states appear<strong>in</strong>g <strong>in</strong> π ′ at time po<strong>in</strong>ts<br />
from the <strong>in</strong>terval ((n + ml)¯r, (n + ml + 1)¯r) satisfy ϕ1. I.e., all states<br />
<strong>in</strong> π ′′<br />
j at time po<strong>in</strong>ts from<br />
((n + ml)¯r − (n¯r + d1 + d2), (n + ml + 1)¯r − (n¯r + d1 + d2))<br />
= (ml¯r − d1 − d2, (ml + 1)¯r − d1 − d2)<br />
⊇ [ml¯r − d2, ml¯r)<br />
satisfy ϕ1.
22 D. Lepri, E. Ábrahám, and P. Cs. Ölveczky<br />
(ii) For the case d π′<br />
i<br />
k ∈ I2 = I\I1 let v be the number of states <strong>in</strong> π pre′<br />
i . We<br />
show that k − v is a proper <strong>in</strong>dex for the satisfaction of the bounded<br />
until along π ′′<br />
j .<br />
We observe that t π′′<br />
j<br />
l<br />
T K, t π′′<br />
j<br />
i = tπ′<br />
l+v<br />
i<br />
for all l. Therefore, T K, tπ′<br />
k |=c ϕ2 implies<br />
k−v |=c ϕ2. S<strong>in</strong>ce d π′ i<br />
k ∈ I2 we have d π′ i<br />
k ≥ ml¯r + d2 + d3 and<br />
thus d π′′ j<br />
i<br />
k−v = dπ′<br />
k − d2 ≥ ml¯r + d3, i.e., the duration of π ′′<br />
j until the<br />
(k − v)-th state is above the lower bound of I. It is easy to see that this<br />
duration is also below the upper bound (d π′<br />
i<br />
k is below the upper bound<br />
and d π′′ j<br />
i<br />
k−v = dπ′<br />
k − d2 < d π′ i<br />
k ).<br />
F<strong>in</strong>ally, T K, t π′<br />
i<br />
l+v |=c ϕ1 implies T K, t π′′<br />
j<br />
l |=c ϕ1 for all l < k−v Therefore,<br />
the <strong>in</strong>dex (k − v) is appropriate to show that the path π ′′<br />
j satisfies the<br />
bounded until property.<br />
“⇐”: This proof case is quite analogous to the “⇐” case of the existentially<br />
quantified bounded until. The proof structure is illustrated <strong>in</strong> Figure 4.<br />
Assume that R, t π j |=c A ϕ1 UI ϕ2 holds. Then by def<strong>in</strong>ition for all paths<br />
πj ∈ tfPaths T K(t π j ) there is a time ref<strong>in</strong>ement π′ j ∈ tfPaths T K(t π j ) of πj and<br />
an <strong>in</strong>dex k s.t. d π′<br />
j<br />
j<br />
k ∈ I, T K, tπ′<br />
k |=c ϕ2, and T K, t π′<br />
j<br />
l |=c ϕ1 for all 0 ≤ l < k.<br />
We show that R, tπ i |=c A ϕ1 UI ϕ2 holds. Let πi ∈ tfPathsT K(tπ i ) be a path.<br />
Due to time robustness, πi has a time ref<strong>in</strong>ement π ′ i ∈ tfPathsT K(tπ i ) which<br />
conta<strong>in</strong>s the state tπ j at time po<strong>in</strong>t d2, and <strong>in</strong> case the upper bound of I is<br />
f<strong>in</strong>ite also a state t∗∗ at time po<strong>in</strong>t mu¯r. Note that time robustness assures<br />
that the state at time po<strong>in</strong>t d2 is tπ j .<br />
Let π pre′<br />
i and πj be the prefix resp. suffix of π ′ i<br />
end<strong>in</strong>g resp. start<strong>in</strong>g at<br />
time po<strong>in</strong>t d2, i.e., at the state tπ j . From R, tπj |=c A ϕ1 UI ϕ2 we conclude<br />
that there is a time ref<strong>in</strong>ement π ′ j of πj and an <strong>in</strong>dex k such that d π′<br />
j<br />
k<br />
T K, t π′<br />
j<br />
∈ I,<br />
k |=c ϕ2, and T K, t π′<br />
j<br />
l |=c ϕ1 for all 0 ≤ l < k.<br />
Let π ′′<br />
i be the concatenation of πpre′ i and π ′ j . Note that π′′ i is a time ref<strong>in</strong>ement<br />
of πi. We show that the bounded until holds along π ′′<br />
i . We dist<strong>in</strong>guish<br />
between k = 0 and k > 0.<br />
k = 0 For the case k = 0 notice that t π′<br />
j<br />
0 = tπj and thus T K, tπj |=c ϕ2. Us<strong>in</strong>g the<br />
path π, by <strong>in</strong>duction we get T K, tπ i |=c ϕ2. Furthermore, s<strong>in</strong>ce d π′<br />
j<br />
0 = 0<br />
and d π′ j<br />
0 ∈ I, the lower bound of I must be 0. I.e., the <strong>in</strong>dex 0 satisfies<br />
the condition for the bounded until on the path π ′′<br />
i .<br />
k > 0 Otherwise, if k > 0 then T K, tπ j |=c ϕ1 and we get by <strong>in</strong>duction that<br />
T K, t π′′<br />
i<br />
l |=c ϕ1 for all l < v (i.e., all states <strong>in</strong> the prefix π pre′<br />
i<br />
end<strong>in</strong>g at tπ j at time po<strong>in</strong>t d2 satisfy ϕ1).<br />
of π ′′<br />
i<br />
(i) If the upper bound of I is INF then from T K, t π′′<br />
j<br />
k |=c ϕ2 and t π′′<br />
j<br />
k =<br />
t π′<br />
i<br />
k+v<br />
i<br />
we conclude that T K, tπ′<br />
k+v |=c ϕ2. Furthermore, d π′′<br />
j<br />
k is above<br />
the lower bound of I and d π′<br />
i<br />
k+v<br />
j<br />
= dπ′′<br />
k + d2, i.e., d π′<br />
i<br />
k+v<br />
∈ I.
π :<br />
πi :<br />
π ′ i :<br />
πj :<br />
π ′ j :<br />
π ′′<br />
i :<br />
π ′ :<br />
<strong><strong>Time</strong>d</strong> <strong>CTL</strong> <strong>Model</strong> <strong>Check<strong>in</strong>g</strong> <strong>in</strong> <strong>Real</strong>-<strong>Time</strong> Maude 23<br />
0 ¯r 2¯r 3¯r 4¯r 5¯r<br />
t π i<br />
t π j<br />
n¯r d1 d2 d3<br />
π pre π pre<br />
i<br />
t π i<br />
t π i<br />
π pre′<br />
i<br />
d2<br />
t π j<br />
t π j<br />
t π j<br />
I<br />
πj<br />
I1<br />
mu ¯r<br />
t ∗∗<br />
t ∗∗<br />
t ∗∗<br />
t π i t π j t ∗∗<br />
π pre′<br />
i<br />
t π i t π j t ∗∗<br />
π pre π ′′<br />
i<br />
Fig. 4: Lemma 1: Proof structure for the “⇐” direction of universally quantified<br />
bounded until<br />
I<br />
π ′ j<br />
I<br />
I2
24 D. Lepri, E. Ábrahám, and P. Cs. Ölveczky<br />
F<strong>in</strong>ally, all states with <strong>in</strong>dices from v to (k + v − 1) <strong>in</strong> π ′ i satisfy ϕ1,<br />
s<strong>in</strong>ce they also appear <strong>in</strong> π ′′<br />
j before the <strong>in</strong>dex k. We have already<br />
shown above that the states with <strong>in</strong>dices up to v also satisfy ϕ1,<br />
therefore the bounded until is satisfied along the path π ′ i .<br />
(ii) Otherwise mu¯r is the f<strong>in</strong>ite upper bound of I. Note that k > 0<br />
implies mu > 0. We assume first d π′<br />
j<br />
k ∈ I2 = (mu¯r − d2, mu¯r] and<br />
cover d π′<br />
j<br />
k ∈ I1 = I\I2 <strong>in</strong> case (iii).<br />
Let π ′ be the concatenation πpre′ and π ′′<br />
j<br />
j . The state tπ′<br />
k appears <strong>in</strong><br />
π ′ j by assumption at a time po<strong>in</strong>t <strong>in</strong> (mu¯r − d2, mu¯r], and therefore<br />
also <strong>in</strong> π ′′<br />
i at a time po<strong>in</strong>t <strong>in</strong> (mu¯r, mu¯r + d2] and <strong>in</strong> π ′ at time po<strong>in</strong>t<br />
((n + mu)¯r + d1, (n + mu)¯r + d1 + d2].<br />
By construction π ′ j conta<strong>in</strong>s the state t∗∗ at time po<strong>in</strong>t mu¯r − d2.<br />
Aga<strong>in</strong> by construction, also π ′′<br />
i conta<strong>in</strong>s t∗∗ at time po<strong>in</strong>t mu¯r −d2 +<br />
d2 = mu¯r. Therefore, the state t∗∗ appears also <strong>in</strong> π ′ at time po<strong>in</strong>t<br />
(n + mu)¯r + d1.<br />
We conclude that both t π′<br />
j<br />
k and t∗∗ appear <strong>in</strong> π ′ with<strong>in</strong> the time<br />
<strong>in</strong>terval ((n + mu)¯r, (n + mu + 1)¯r). From T K, t π′<br />
j<br />
k |=c ϕ2 we get<br />
therefore by <strong>in</strong>duction T K, t ∗∗ |=c ϕ2 .<br />
S<strong>in</strong>ce t ∗∗ appears <strong>in</strong> π ′′<br />
i at time po<strong>in</strong>t mu¯r be<strong>in</strong>g the upper bound of<br />
I, also the time bound of the until is satisfied for t ∗∗ on π ′′<br />
i .<br />
We have shown above that all states with <strong>in</strong>dices up to v <strong>in</strong> π ′′<br />
i satisfy<br />
ϕ1. The rema<strong>in</strong><strong>in</strong>g states preceed<strong>in</strong>g t ∗∗ <strong>in</strong> π ′′<br />
i also satisfy ϕ1, s<strong>in</strong>ce<br />
they appear <strong>in</strong> π ′ j before the <strong>in</strong>dex k. Thus the <strong>in</strong>dex of t∗∗ <strong>in</strong> π ′′<br />
i<br />
satisfies the condition of the bounded until on π ′ i .<br />
(iii) For the case d π′ j<br />
k ∈ I1 = I\I2 we observe that t π′′<br />
i<br />
l<br />
j<br />
= tπ′<br />
l−v<br />
for all l ≥ v.<br />
Therefore, T K, t π′<br />
j<br />
k |=c ϕ2 implies T K, t π′′ i<br />
k+v |=c ϕ2. S<strong>in</strong>ce d π′<br />
j<br />
k<br />
∈ I2<br />
we have d π′<br />
j<br />
k ≤ mu¯r − d2 and thus d π′′<br />
i<br />
j<br />
k+v = dπ′<br />
k + d2 ≤ mu¯r, i.e., the<br />
duration of π ′′<br />
i until the (k + v)-th state is below the upper bound of<br />
I. It is easy to see that this duration is also above the lower bound<br />
(d π′ j<br />
k<br />
i<br />
j<br />
is above the lower bound and dπ′′<br />
k+v = dπ′<br />
k + d2 > d π′ j<br />
k ).<br />
We have shown above that all states with <strong>in</strong>dices up to v satisfy ϕ1.<br />
Furthermore, T K, t π′ j<br />
l |=c ϕ1 implies T K, t π′′ i<br />
l+v |=c ϕ1 for all l < k.<br />
Therefore, the <strong>in</strong>dex (k + v) is appropriate to show that the path π ′′<br />
i<br />
satisfies the bounded until property.<br />
Based on the above lemma we ga<strong>in</strong> our completeness result:<br />
Theorem 1. Assume a time-robust real-time rewrite theory R whose time doma<strong>in</strong><br />
satisfies the theory GCD-TIME-DOMAIN. Let Π be a set of tick-<strong>in</strong>variant<br />
atomic propositions, and assume a protect<strong>in</strong>g extension of R def<strong>in</strong><strong>in</strong>g the atomic<br />
propositions <strong>in</strong> Π and <strong>in</strong>duc<strong>in</strong>g a label<strong>in</strong>g function LΠ. Let t0 be a state of R, r<br />
a non-zero time value of sort <strong>Time</strong>, ϕ a T<strong>CTL</strong>cb formula over Π, and assume
<strong><strong>Time</strong>d</strong> <strong>CTL</strong> <strong>Model</strong> <strong>Check<strong>in</strong>g</strong> <strong>in</strong> <strong>Real</strong>-<strong>Time</strong> Maude 25<br />
that ¯r = GCD(R, t0, r, ϕ) is a def<strong>in</strong>ed non-zero time value. Then<br />
R, LΠ, t |=c ϕ ⇐⇒ R gcd(t0,r,ϕ) , LΠ, t |=p ϕ<br />
for all states t reachable <strong>in</strong> R gcd(t0,r,ϕ) from t0.<br />
Proof. Notice that t0 is also a state of R gcd(t0,r,ϕ) . Furthermore, all states t<br />
reachable <strong>in</strong> the abstraction R gcd(t0,r,ϕ) from t0 are also states reachable <strong>in</strong> R<br />
from t0.<br />
S<strong>in</strong>ce t is reachable <strong>in</strong> T K gcd , there is a path π pre ∈ tfPaths T K gcd(t0) lead<strong>in</strong>g<br />
from t0 to t. Let π pre be such a path and let n0 be the number of states <strong>in</strong> π pre .<br />
Note that π pre has tick steps of length ¯r/2 and also that π pre ∈ tfPaths T K(t0).<br />
We denote by T K the timed Kripke structure associated to R, by T K gcd the<br />
timed Kripke structure associated to R gcd(t0,r,ϕ) . By def<strong>in</strong>ition<br />
R, LP , t |=c ϕ ⇐⇒ T K, t |=c ϕ,<br />
R gcd(t0,r,ϕ) , LP , t |=p ϕ ⇐⇒ T K gcd , t |=p ϕ.<br />
Thus the theorem is equivalently proved, if we show that<br />
T K, t |=c ϕ ⇐⇒ T K gcd , t |=p ϕ.<br />
Given a T<strong>CTL</strong>cb formula of the k<strong>in</strong>d E ϕ1 UI ϕ2 or A ϕ1 UI ϕ2, we refer to<br />
the path formula ϕ1 UI ϕ2 as “the until path formula”.<br />
The proof is done by <strong>in</strong>duction on the structure of ϕ. Base cases:<br />
– ϕ = true: We have R, LP , t |=c true and R gcd(t0,r,ϕ) , LP , t |=p true for all t<br />
by def<strong>in</strong>ition of, respectively, |=c and |=p.<br />
– ϕ = p: We have R, LP , t |=c p iff p ∈ LP (t) iff R gcd(t0,r,ϕ) , LP , t |=p p, by<br />
def<strong>in</strong>ition of |=c and |=p.<br />
Assume now that the theorem holds by <strong>in</strong>duction hypothesis for ϕ1 and ϕ2 that<br />
is, respectively,<br />
R, LP , t |=c ϕ1 ⇐⇒ R gcd(t0,r,ϕ) , LP , t |=p ϕ1,<br />
R, LP , t |=c ϕ2 ⇐⇒ R gcd(t0,r,ϕ) , LP , t |=p ϕ2,<br />
for all states t reachable <strong>in</strong> the abstraction R gcd(t0,r,ϕ) from t0.<br />
– ϕ = ¬ϕ1:<br />
– ϕ = ϕ1 ∧ ϕ2:<br />
T K, t |=c ¬ϕ1 ⇐⇒ not (T K, t |=c ϕ1) (by def. of |=c)<br />
⇐⇒ not (T K gcd , t |=p ϕ1) (by <strong>in</strong>d. on ϕ1)<br />
⇐⇒ T K gcd , t |=p ¬ϕ1 . (by def. of |=p)<br />
T K, t |=c ϕ1 ∧ ϕ2 ⇐⇒ T K, t |=c ϕ1 and T K, t |=c ϕ2<br />
⇐⇒ T K<br />
(by def. of |=c)<br />
gcd , t |=p ϕ1 and<br />
T K gcd , t |=p ϕ2<br />
(by <strong>in</strong>d. on ϕ1 and ϕ2)<br />
⇐⇒ T K gcd , t |=p ϕ1 ∧ ϕ2 . (by def. of |=p)
26 D. Lepri, E. Ábrahám, and P. Cs. Ölveczky<br />
– ϕ = E ϕ1 UI ϕ2: We need to show both implication directions.<br />
“⇐”: Assume T K gcd , t |=p ϕ. By def<strong>in</strong>ition<br />
T K gcd , t |=p ϕ iff there exists π ∈ tfPathsT Kgcd(t) and an <strong>in</strong>dex j s.t. dπ j ∈ I,<br />
T K gcd , t π j |=p ϕ2, and ∀ 0 ≤ i < j T K gcd , t π i |=p ϕ1.<br />
Let π be such a path and j such an <strong>in</strong>dex. Note that all tick steps <strong>in</strong> π have<br />
duration ¯r/2.<br />
This path π is also <strong>in</strong> tfPaths T K(t). We show that for each time ref<strong>in</strong>ement<br />
π ′ ∈ tfPathsT K(t) of π there is an <strong>in</strong>dex j ′′ s.t. dπ′ j ′′ ∈ I, T K, tπ′ j ′′ |=c ϕ2, and<br />
T K, t π′<br />
i |=c ϕ1 for all 0 ≤ i < j ′′ .<br />
Let π ′ ∈ tfPaths T K(t) be a time ref<strong>in</strong>ement of π. Then t π j<br />
also appears <strong>in</strong><br />
π ′ at the same time po<strong>in</strong>t dπ j at some <strong>in</strong>dex j′ , i.e., dπ′ j ′ ∈ I. By <strong>in</strong>duction<br />
T K, t π j |=c ϕ2 and from t π j<br />
dπ j is a multiple of ¯r/2 we have that dπ′ j ′ = dπj Let π0 be the concatenation of πpre and π ′ . Then tπ′ = tπ′ j ′ we get T K, tπ′ j ′ |=c ϕ2. Furthermore, s<strong>in</strong>ce<br />
is also a multiple of ¯r/2.<br />
j ′ appears <strong>in</strong> π0 at position<br />
n0 + j ′ and time po<strong>in</strong>t d π0<br />
n0+j ′. If dπ0<br />
n0+j ′ is a multiple of ¯r then we def<strong>in</strong>e<br />
j ′′ = j ′ . Otherwise let d π0<br />
n0+j ′ be <strong>in</strong> the time <strong>in</strong>terval (n¯r, (n + 1)¯r) for some<br />
n ∈ N0. Let j ′′ be the smallest <strong>in</strong>dex such that d π0<br />
n0+j ′′ ∈ (n¯r, (n + 1)¯r). Then<br />
by Lemma 1 we conclude from T K, tπ′ j ′ |=c ϕ2 and tπ′ ′ = tπ0 ′ that also<br />
T K, t π0<br />
n0+j ′′ |=c ϕ2, i.e., T K, t π′<br />
j ′′ |=c ϕ2.<br />
j<br />
n0+j<br />
Similarly, by <strong>in</strong>duction we get that T K, t π′<br />
i |=c ϕ1 for all i < j ′′ <strong>in</strong> case d π′<br />
i is<br />
a multiple of ¯r/2, s<strong>in</strong>ce these states also appear <strong>in</strong> π at the same time po<strong>in</strong>ts<br />
and they satisfy ϕ1 <strong>in</strong> the po<strong>in</strong>twise semantics by assumption.<br />
For the other states t π′<br />
i <strong>in</strong> π ′ appear<strong>in</strong>g before the <strong>in</strong>dex j ′′ we use the<br />
concatenation π0 of π pre and π ′ to show that they satisfy ϕ1 us<strong>in</strong>g Lemma 1.<br />
Note that those states t π′<br />
i all appear <strong>in</strong> π0 <strong>in</strong> some time <strong>in</strong>terval (n¯r, (n+1)¯r).<br />
Furthermore, <strong>in</strong> this <strong>in</strong>terval there is also a state tmid at the time po<strong>in</strong>t<br />
n¯r + ¯r/2, for which we have already shown that T K, tmid |=c ϕ1. Thus by<br />
Lemma 1 and us<strong>in</strong>g the path π0, also t π′<br />
i satisfies ϕ1.<br />
“⇒”: Assume T K, t |=c E ϕ1 UI ϕ2. By def<strong>in</strong>ition<br />
T K, t |=c E ϕ1 UI ϕ2 iff there is a path π ∈ tfPaths T K(t) s. t. for each time<br />
ref<strong>in</strong>ement π ′ ∈ tfPaths T K(t) of π there is an <strong>in</strong>dex<br />
j ′ s.t. dπ′ j ′ ∈ I, T K, tπ′ j ′ |=c ϕ2, and ∀ 0 ≤ i < j ′<br />
T K, t π′<br />
i |=c ϕ1.<br />
Let π be such a path. Let π ′ be a time ref<strong>in</strong>ement of π <strong>in</strong> which a state<br />
appears at all time po<strong>in</strong>ts n¯r/2 for n ∈ N0. By the above def<strong>in</strong>ition we<br />
conclude that there is an <strong>in</strong>dex j ′ such that dπ′ j ′ ∈ I, T K, tπ′ j ′ |=c ϕ2, and<br />
T K, t π′<br />
i |=c ϕ1 for all 0 ≤ i < j ′ .<br />
Next we def<strong>in</strong>e an <strong>in</strong>dex j ′′ satisfy<strong>in</strong>g the same conditions as j ′ but addi-<br />
tionally such that d π′<br />
j<br />
′′ is a multiple of ¯r/2. If dπ′ j<br />
then let j ′′ = j ′ . Otherwise let aga<strong>in</strong> π0 be the concatenation of πpre and π ′ .<br />
′′ is already a multiple of ¯r/2
<strong><strong>Time</strong>d</strong> <strong>CTL</strong> <strong>Model</strong> <strong>Check<strong>in</strong>g</strong> <strong>in</strong> <strong>Real</strong>-<strong>Time</strong> Maude 27<br />
Then dπ′ j ′ is <strong>in</strong> π0 <strong>in</strong> an <strong>in</strong>terval (n¯r, (n + 1)¯r) for some n ∈ N0. Furthermore<br />
there is another state tmid at time po<strong>in</strong>t n¯r + ¯r/2 and <strong>in</strong>dex n0 + j ′′ <strong>in</strong> π0.<br />
Aga<strong>in</strong> by Lemma 1 we have T K, tπ′ j ′′ |=c ϕ2.<br />
Now we can build a time abstraction of π ′ which we obta<strong>in</strong> by replac<strong>in</strong>g each<br />
rl<br />
tick step sequence tl −→ . . . rl+i−1<br />
−→ tl+i with dπ′ l = n¯r/2 and dπ′<br />
l+i = (n+1)¯r/2<br />
r<br />
for some n ∈ N0 by tl −→ tl+i with r = l+i−1 ri.<br />
This time abstraction π ′′ is a path of T K gcd , and the states of π ′′ appear<br />
at the same time po<strong>in</strong>ts also <strong>in</strong> π ′ . Furthermore, s<strong>in</strong>ce dπ′ j ′′ is a multiple of<br />
¯r/2, it also appears <strong>in</strong> π ′′ at some position j ′′′ . F<strong>in</strong>ally, s<strong>in</strong>ce all states <strong>in</strong> π ′<br />
with <strong>in</strong>dex less that j ′′ satisfy ϕ1, also all states <strong>in</strong> π ′′ with <strong>in</strong>dex less that<br />
j ′′′ , build<strong>in</strong>g a subset of the previous ones, satisfy ϕ1. Thus π ′′ satisfies the<br />
bounded until path formula, i.e., T K gcd , t |=p E ϕ1 UI ϕ2.<br />
– ϕ = A ϕ1 UI ϕ2: We need to show both implication directions.<br />
“⇐”: Assume that T K gcd , t |=p A ϕ1 UI ϕ2. By def<strong>in</strong>ition<br />
T K gcd , t |=p A ϕ1 UI ϕ2 iff for each π ∈ tfPathsT Kgcd(t) there is an <strong>in</strong>dex j s.t. dπ j ∈ I,<br />
i=l<br />
T K gcd , t π j |=p ϕ2 and ∀ 0 ≤ i < j T K gcd , t π i |=p ϕ1.<br />
In order to prove that T K, t |=c A ϕ1 UI ϕ2, we have to show that for each<br />
path π ∈ tfPathsT K(t) there exists a time ref<strong>in</strong>ement π ′ ∈ tfPathsT K(t) of π<br />
and an <strong>in</strong>dex j s.t. dπ′ j ∈ I, T K, tπ′ j |=c ϕ2, and ∀ 0 ≤ i < j T K, tπ′ i |=c ϕ1.<br />
Let π ∈ tfPathsT K(t) and let π ′ ∈ tfPathsT K(t) be a ref<strong>in</strong>ement of π conta<strong>in</strong><strong>in</strong>g<br />
a state at each time po<strong>in</strong>t n¯r/2, n ∈ N0.<br />
We obta<strong>in</strong> π ′′ from π ′ rl<br />
by replac<strong>in</strong>g each tick step sequence tl −→ . . . rl+i−1<br />
−→<br />
r<br />
−→ tl+i<br />
tl+i with d π′<br />
l<br />
with r = l+i−1<br />
i=l<br />
= n¯r/2 and dπ′<br />
l+i = (n + 1)¯r/2 for some n ∈ N0 by tl<br />
ri.<br />
Note that π ′′ is <strong>in</strong> tfPaths T K gcd(t) and thus by assumption there is an <strong>in</strong>dex<br />
j such that d π j ∈ I, T Kgcd , t π j |=p ϕ2 and T K gcd , t π i |=p ϕ1 for all 0 ≤ i < j.<br />
Let j be such an <strong>in</strong>dex.<br />
Then by construction and <strong>in</strong>duction there exists an <strong>in</strong>dex j ′ such that dπ′ j ′ is<br />
a multiple of ¯r/2, dπ′ j ′ ∈ I, T K, tπ′ j ′ |=c ϕ2 and T K, tπ′ i |=c ϕ1 for all 0 ≤ i < j ′<br />
with d π′<br />
i<br />
be<strong>in</strong>g a multiple of ¯r/2. For the other states prior to the <strong>in</strong>dex j′<br />
we construct π0 as the composition of π pre and π ′ . Note that <strong>in</strong> each <strong>in</strong>terval<br />
(n¯r, (n + 1)¯r) with (n + 1)¯r < tπ′ j ′ there is a po<strong>in</strong>t at n¯r + ¯r/2, for which<br />
we have already shown to satisfy ϕ1. Thus by Lemma 1 also the states that<br />
are prior to the <strong>in</strong>dex j ′′ and are not at multiples of ¯r/2 satisfy ϕ1. Hence<br />
π ′ |=c ϕ.<br />
“⇒”: Assume T K, t |=c A ϕ1 UI ϕ2.<br />
T K, t |=c A ϕ1 UI ϕ2 iff for each path π ∈ tfPathsT K(t) there is a time<br />
ref<strong>in</strong>ement π ′ ∈ tfPathsT K(t) of π<br />
and an <strong>in</strong>dex j s.t. dπ′ j ∈ I,<br />
T K, tπ′ j |=c ϕ2, and ∀ 0 ≤ i < j T K, tπ′ i |=c ϕ1.
28 D. Lepri, E. Ábrahám, and P. Cs. Ölveczky<br />
In order to prove that T K gcd , t |=p A ϕ1 UI ϕ2, we have to show that for<br />
each π ∈ tfPathsT Kgcd(t) there is an <strong>in</strong>dex j s.t. dπ j ∈ I, T Kgcd , tπ j |=p ϕ2,<br />
and ∀ 0 ≤ i < j T K gcd , tπ i |=p ϕ1.<br />
Let π ∈ tfPathsT Kgcd(t). We know that π is also a path <strong>in</strong> T K, thus by<br />
assumption there exist a path ref<strong>in</strong>ement π ′ of π that satisfies the until path<br />
formula <strong>in</strong> the cont<strong>in</strong>uous semantics <strong>in</strong> T K. By def<strong>in</strong>ition, all tick durations<br />
<strong>in</strong> π ′ are ≤ ¯r<br />
2 , thus, we can def<strong>in</strong>e π′′ to be the same time abstraction of π ′<br />
that we def<strong>in</strong>ed <strong>in</strong> the proof for the (“⇒”) of the existential until, where we<br />
removed all states at time po<strong>in</strong>ts non-multiple of ¯r . We have already shown<br />
2<br />
how this path also satisfies the until path formula <strong>in</strong> T K, thanks to Lemma 1.<br />
In particular, we have that π ′′ = π and, by us<strong>in</strong>g the <strong>in</strong>duction hypotesis on<br />
ϕ1 and ϕ2 as we did for the “⇐” proof, we know that π ′′ satisfies the until<br />
path formula <strong>in</strong> the po<strong>in</strong>twise semantics <strong>in</strong> T K gcd , and hence T K gcd |=p ϕ.<br />
4.1 Soundness and completeness for TACLT and TECLT<br />
S<strong>in</strong>ce it is the theory R σ that is model checked, not all behaviors <strong>in</strong> the theory R<br />
are analyzed. Therefore, R σ , LΠ, s |= ϕ does not necessarily imply R, LΠ, s |= ϕ.<br />
However, for the universal fragment TA<strong>CTL</strong> 8 , <strong>in</strong> the po<strong>in</strong>twise semantics, if a<br />
counter-example exists <strong>in</strong> the model check<strong>in</strong>g of R σ , then this is also a counterexample<br />
<strong>in</strong> R; that is, for ϕA a TA<strong>CTL</strong> formula, we have<br />
R σ , LΠ, s |=p ϕA =⇒ R, LΠ, s |=p ϕA.<br />
Thus, R σ is a complete abstraction of R for TA<strong>CTL</strong>.<br />
However, if a counter-example does not exist <strong>in</strong> R σ , then this does not exclude<br />
the existence of a counter-example <strong>in</strong> R.<br />
Conversely, <strong>in</strong> the existential fragment, if the given state satisfies the TE<strong>CTL</strong><br />
formula <strong>in</strong> R σ <strong>in</strong> the po<strong>in</strong>twise semantics, mean<strong>in</strong>g that there exists a path π<br />
satisfy<strong>in</strong>g the given formula, then this holds also for R, s<strong>in</strong>ce π is also a path <strong>in</strong><br />
R; that is, for ϕE a TE<strong>CTL</strong> formula, we have<br />
R σ , LΠ, s |=p ϕE =⇒ R, LΠ, s |=p ϕE.<br />
Thus, R σ is a sound abstraction of R for TE<strong>CTL</strong>.<br />
5 Implementation<br />
Our model checker makes the natural and reasonable assumption that given a<br />
real-time rewrite theory R, and an <strong>in</strong>itial state t0 on which we would like to<br />
check some T<strong>CTL</strong> formula ϕ, all behaviors start<strong>in</strong>g from t0 are time-diverg<strong>in</strong>g<br />
8 The universal and the existential fragments [13] of T<strong>CTL</strong> are def<strong>in</strong>ed by allow<strong>in</strong>g<br />
negation only <strong>in</strong> front of propositions and by restrict<strong>in</strong>g quantification to the universal<br />
quantifier TA<strong>CTL</strong>, and to the existential quantifier <strong>in</strong> TE<strong>CTL</strong>.
<strong><strong>Time</strong>d</strong> <strong>CTL</strong> <strong>Model</strong> <strong>Check<strong>in</strong>g</strong> <strong>in</strong> <strong>Real</strong>-<strong>Time</strong> Maude 29<br />
w.r.t. the selected time sampl<strong>in</strong>g strategy σ. This assumption also implies that<br />
the transition relation T<br />
−→R σ <strong>in</strong> the timed Kripke structure T K(Rσ , t0)Π is total.<br />
The current implementation of the model checker assumes that time values<br />
are either <strong>in</strong> NAT-TIME-DOMAIN-WITH-INF or POSRAT-TIME-DOMAIN-WITH-INF,<br />
and provides the user with two possible model-check<strong>in</strong>g strategies:<br />
(i) The basic strategy, which performs the model check<strong>in</strong>g on the model obta<strong>in</strong>ed<br />
by apply<strong>in</strong>g the user-def<strong>in</strong>ed time sampl<strong>in</strong>g strategy on the orig<strong>in</strong>al model.<br />
As we expla<strong>in</strong>ed <strong>in</strong> section 4.1, this strategy provides a sound analysis for<br />
TETCL and a complete analysis for TATCL.<br />
(ii) The gcd strategy, which extends the maximal time sampl<strong>in</strong>g strategy with<br />
the “gcd” transformation to perform the model check<strong>in</strong>g for the satisfaction<br />
problem R gcd(t0,r,ϕ) , LΠ, t0 |=p ϕ.<br />
Soundness and completeness of the gcd strategy might come at the cost of<br />
a larger state space due to the application of the gcd transformation. When the<br />
gcd strategy is impractical, the user can still perform model check<strong>in</strong>g with the<br />
generally faster basic strategy, which does not <strong>in</strong>crease the system state space<br />
and can still be very useful to discover potential bugs, as illustrated below.<br />
<strong>Real</strong>-<strong>Time</strong> Maude, and hence our model checker, is implemented <strong>in</strong> Maude,<br />
mak<strong>in</strong>g extensive use of Maude’s meta-programm<strong>in</strong>g capabilities. Therefore, our<br />
model checker gets as <strong>in</strong>put the meta-representation R of the <strong>Real</strong>-<strong>Time</strong> Maude<br />
model R to analyze, as well as the meta-representations t0 and ϕ of, respectively,<br />
the <strong>in</strong>itial state t0 and the T<strong>CTL</strong> formula ϕ to check. The algorithm first applies<br />
the user selected time sampl<strong>in</strong>g strategy to R, and then explores the reachable<br />
state space to <strong>in</strong>crementally construct the timed Kripke structure T K(R σ , t0)Π,<br />
which is subsequently model checked (directly as it is <strong>in</strong> the default strategy,<br />
while, <strong>in</strong> the gcd strategy, it is further ref<strong>in</strong>ed by “splitt<strong>in</strong>g” the transitions <strong>in</strong>to<br />
smaller ones of duration equal to the computed greatest common divisor <strong>in</strong> the<br />
gcd strategy and then model checked). This is done by repeatedly us<strong>in</strong>g Maude’s<br />
meta-level descent functions metaSearch, to f<strong>in</strong>d all states reachable from a state<br />
<strong>in</strong> one rewrite step, and metaReduce, to check whether an atomic proposition<br />
holds <strong>in</strong> a state. S<strong>in</strong>ce the meta-representation of the states can be fairly large 9 ,<br />
perform<strong>in</strong>g the rest of the model check<strong>in</strong>g procedure on the generated timed<br />
Kripke structure is fairly <strong>in</strong>efficient. In our current implementation, we assign a<br />
unique natural number to each (meta-represented) state <strong>in</strong> the generated timed<br />
Kripke structure, and construct a more compact timed Kripke structure, where<br />
all the occurrences of these meta-represented states are replaced by their respective<br />
identifiers. We then perform the ma<strong>in</strong> part of the model check<strong>in</strong>g procedure,<br />
namely, the recursive computation of the satisfaction set of ϕ on this compact<br />
representation. This optimization led to a large performance improvement and<br />
made it feasible to apply our model checker to a number of case studies <strong>in</strong> reasonable<br />
time, whereas work<strong>in</strong>g directly on meta-represented terms made model<br />
check<strong>in</strong>g unfeasible even for simple case studies.<br />
9 For example, each state <strong>in</strong> the Maude representation of the Ptolemy II model <strong>in</strong><br />
Section 6 “conta<strong>in</strong>s” the entire Ptolemy II model.
30 D. Lepri, E. Ábrahám, and P. Cs. Ölveczky<br />
Our implementation of the T<strong>CTL</strong> model checker is based on the explicit-state<br />
<strong>CTL</strong> model check<strong>in</strong>g approach [8] that, start<strong>in</strong>g with the atomic propositions,<br />
recursively computes for each subformula of the desired T<strong>CTL</strong> formula the set<br />
of satisfy<strong>in</strong>g reachable states. We implemented specific procedures for a basic set<br />
of temporal modal operators and we expressed other formulas <strong>in</strong>to this canonical<br />
form. The basic set consists of the <strong>CTL</strong> modal operators E ϕ1 U ϕ2, E G ϕ,<br />
the T<strong>CTL</strong>≤≥ 10 modal operators E ϕ1 U∼r ϕ2 with ∼∈ {>, ≥}, E ϕ1 U∼r ϕ2<br />
with ∼∈ {0 ϕ2 and the T<strong>CTL</strong>cb modal operator E ϕ1 U [a,b] ϕ2.<br />
The procedures for <strong>CTL</strong> modalities follow the standard explicit algorithm [8].<br />
For T<strong>CTL</strong>≤≥ modalities, our implementation adapts the T<strong>CTL</strong>≤≥ model check<strong>in</strong>g<br />
procedure def<strong>in</strong>ed <strong>in</strong> [19] for time-<strong>in</strong>terval structures and to timed Kripke<br />
structures with time-diverg<strong>in</strong>g paths.<br />
We briefly expla<strong>in</strong> the model check<strong>in</strong>g procedure for ϕ = E ϕ1 U [a,b] ϕ2. We<br />
first compute the satisfacton set for the <strong>CTL</strong> formula ˆϕ = E ϕ1 U ϕ2, then we<br />
restrict the transition relation (which we here denote by tr) <strong>in</strong> the timed Kripke<br />
structure, to those transitions between states satisfy<strong>in</strong>g ˆϕ except transitions from<br />
¬ϕ1-states, obta<strong>in</strong><strong>in</strong>g ¯tr. We then recursively compute all the time distances from<br />
any state to some ϕ2 state up to b time units. This is computed by the operator<br />
computeDistances. The first two arguments of this operator are set of pairs of<br />
the k<strong>in</strong>d < r, s > with r a time value and s a state (represented by a natural<br />
number <strong>in</strong> the current implementation), where each pair means that it is possible<br />
to reach some ϕ2-state from state s <strong>in</strong> time r ≤ b. The first set of such pairs is<br />
the set of time distances that still have to be “visited”, that is the predecessors<br />
of s still have to be visited with the given time stamp r. The second of such sets<br />
conta<strong>in</strong>s time distances that have already been visited. The third argument is<br />
the time bound b and the fourth argument is the restricted transition relation<br />
¯tr. The operator is <strong>in</strong>itially called with<br />
computeDistances({< 0, ϕ2-state >},emptyRatNatPairSet,b, ¯tr),<br />
s<strong>in</strong>ce each ϕ2-state can obviously be reached <strong>in</strong> zero time.<br />
vars RNPS0 RNPS1 RNPS RNPS’ : RatNatPairSet .<br />
vars TIME0 TIME : Rat .<br />
var TRTKS : TransRelTKS .<br />
var N0 : Nat .<br />
op computeDistances :<br />
RatNatPairSet RatNatPairSet Rat TransRelTKS -> RatNatPairSet .<br />
ceq computeDistances(( < TIME0, N0 > RNPS), RNPS’, TIME, TRTKS) =<br />
computeDistances((RNPS1 RNPS), (< TIME0, N0 > RNPS’), TIME, TRTKS)<br />
if RNPS0 := all<strong><strong>Time</strong>d</strong>Predecessors(TRTKS,N0) /\<br />
RNPS1 := add<strong>Time</strong>AndFilter(RNPS0, TIME0, TIME) .<br />
eq computeDistances(emptyRatNatPairSet, RNPS’, TIME, TRTKS) = RNPS’ .<br />
10 We denote by T<strong>CTL</strong>≤≥ the restricted T<strong>CTL</strong> logic with time constra<strong>in</strong>ts on the<br />
temporal modalities of the form ∼ r, where ∼∈ {},
<strong><strong>Time</strong>d</strong> <strong>CTL</strong> <strong>Model</strong> <strong>Check<strong>in</strong>g</strong> <strong>in</strong> <strong>Real</strong>-<strong>Time</strong> Maude 31<br />
The operator all<strong><strong>Time</strong>d</strong>Predecessors computes the set of < r, s > pairs<br />
where s is a predecessor of N0 that can reach N0 <strong>in</strong> r time <strong>in</strong> the given transition<br />
relation, for each pair of time distances that still have to be visited. Then<br />
add<strong>Time</strong>AndFilter selects all pairs such that TIME0 + r ≤ b, which are then<br />
recursively added to the set of pairs to be “visited”, while < TIME0, N0 > is<br />
moved to the “visited pairs”. The computation term<strong>in</strong>ates by return<strong>in</strong>g all the<br />
visited pairs when all possible pairs have been “visited”.<br />
The satisfaction set of ϕ consists of all states that can reach a ϕ2-state <strong>in</strong><br />
a time with<strong>in</strong> the <strong>in</strong>terval [a, b]. Notice that this procedure works also for open<br />
bounded <strong>in</strong>tervals, and <strong>in</strong>deed our implementation covers also open bounded<br />
<strong>in</strong>tervals, however, the model checked logic is closed under negation only for close<br />
bounded <strong>in</strong>tervals. In particular, for modalities with close bounded <strong>in</strong>tervals, we<br />
transform each formula of the k<strong>in</strong>d A ϕ1 U [a,b] ϕ2, with a = 0, <strong>in</strong>to its equivalent<br />
one A G
32 D. Lepri, E. Ábrahám, and P. Cs. Ölveczky<br />
E tt U[
<strong><strong>Time</strong>d</strong> <strong>CTL</strong> <strong>Model</strong> <strong>Check<strong>in</strong>g</strong> <strong>in</strong> <strong>Real</strong>-<strong>Time</strong> Maude 33<br />
In order to analyze this property, we first def<strong>in</strong>e two state propositions, isPaus<strong>in</strong>g<br />
and isBreath<strong>in</strong>g, <strong>in</strong> the expected way. The bounded response property is model<br />
checked us<strong>in</strong>g the follow<strong>in</strong>g <strong>Real</strong>-<strong>Time</strong> Maude command:<br />
Maude> (mc-tctl <strong>in</strong>itState |=<br />
AG(isPaus<strong>in</strong>g implies AF[ (mc-tctl <strong>in</strong>itState |= AG(isPaus<strong>in</strong>g implies<br />
(AF[
34 D. Lepri, E. Ábrahám, and P. Cs. Ölveczky<br />
Fig. 5: A Ptolemy II DE model of the railroad cross<strong>in</strong>g benchmark.<br />
6.2 Ptolemy II Discrete Event <strong>Model</strong>s<br />
As mentioned, <strong>Real</strong>-<strong>Time</strong> Maude provides a formal analysis tool for a set of model<strong>in</strong>g<br />
languages for embedded systems, <strong>in</strong>clud<strong>in</strong>g Ptolemy II discrete-event (DE)<br />
models. Ptolemy II [16] is a well-established model<strong>in</strong>g and simulation tool used<br />
<strong>in</strong> <strong>in</strong>dustry that provides a powerful yet <strong>in</strong>tuitive graphical model<strong>in</strong>g language.<br />
Our model checker has been <strong>in</strong>tegrated <strong>in</strong>to Ptolemy II by Kyungm<strong>in</strong> Bae, so<br />
that we can now model check T<strong>CTL</strong> properties of Ptolemy II DE models from<br />
with<strong>in</strong> Ptolemy 12 . We show the T<strong>CTL</strong> analysis of the railroad cross<strong>in</strong>g and the<br />
hierarchical traffic light exist<strong>in</strong>g Ptolemy II models. In this second case study,<br />
our model check<strong>in</strong>g has uncovered a previously unknown flaw <strong>in</strong> the model.<br />
Railroad Cross<strong>in</strong>g <strong>Model</strong> Figure 5 shows the Ptolemy II model of the well<br />
known railroad cross<strong>in</strong>g benchmark. In this model, a tra<strong>in</strong> approaches a railroad<br />
cross<strong>in</strong>g, and a gate should be lowered when a tra<strong>in</strong> is <strong>in</strong> the <strong>in</strong>tersection. The<br />
12 <strong>Real</strong>-<strong>Time</strong> Maude verification commands can be entered <strong>in</strong>to the dialog box that<br />
pops up when the button “Double click to generate code” <strong>in</strong> Fig. 6 is clicked.
<strong><strong>Time</strong>d</strong> <strong>CTL</strong> <strong>Model</strong> <strong>Check<strong>in</strong>g</strong> <strong>in</strong> <strong>Real</strong>-<strong>Time</strong> Maude 35<br />
model conta<strong>in</strong>s two f<strong>in</strong>ite state mach<strong>in</strong>es: one for the tra<strong>in</strong> and one for the gate.<br />
One transition is taken <strong>in</strong> each time unit <strong>in</strong> the state mach<strong>in</strong>e Tra<strong>in</strong>. We refer<br />
to [7] for a thorough explanation of the model.<br />
The <strong>Real</strong>-<strong>Time</strong> Maude specification for Ptolemy II DE models provides an <strong>in</strong>tuitive<br />
syntax for specify<strong>in</strong>g state propositions, so that e.g. the state proposition<br />
“the tra<strong>in</strong> is <strong>in</strong> state approach<strong>in</strong>g” is written<br />
’RailroadSystem . ’Tra<strong>in</strong> @ ’approach<strong>in</strong>g<br />
One important property that the system should satisfy is that the gate should<br />
open with<strong>in</strong> a reasonable time (here 11 time units) after be<strong>in</strong>g lowered, which<br />
can be model checked by the follow<strong>in</strong>g <strong>Real</strong>-<strong>Time</strong> Maude command:<br />
Maude> (mc-tctl {<strong>in</strong>it} |=<br />
AG((’RailroadSystem . ’Gate @ ’closed) implies<br />
AF[ (mc-tctl {<strong>in</strong>it} |=<br />
A not (’RailroadSystem . ’Gate)@ ’closed U AG[
36 D. Lepri, E. Ábrahám, and P. Cs. Ölveczky<br />
Decision<br />
HierarchicalTrafficLight<br />
Normal<br />
TrafficLight<br />
TrafficLight<br />
Fig. 6: A hierarchical fault-tolerant traffic light system <strong>in</strong> Ptolemy II.<br />
Error<br />
(a) Pedestrianlight (b) Carlight<br />
Fig. 7: The FSM actors for pedestrian lights and car lights
<strong><strong>Time</strong>d</strong> <strong>CTL</strong> <strong>Model</strong> <strong>Check<strong>in</strong>g</strong> <strong>in</strong> <strong>Real</strong>-<strong>Time</strong> Maude 37<br />
Fig. 8: Dialog w<strong>in</strong>dow for the hierarchical traffic light code generation.<br />
Maude> (mc-tctl {<strong>in</strong>it} |=<br />
AG((’HierarchicalTrafficLight . ’Decision | (port ’Error is present))<br />
implies AF[
38 D. Lepri, E. Ábrahám, and P. Cs. Ölveczky<br />
Us<strong>in</strong>g the gcd strategy we can also determ<strong>in</strong>e a “m<strong>in</strong>imal” time <strong>in</strong>terval such<br />
that the above bounded response is satisfied <strong>in</strong> the system. In particular, we<br />
discovered that this <strong>in</strong>terval is [5, 12] by try<strong>in</strong>g different values for a and b <strong>in</strong> the<br />
<strong>in</strong>terval-bounded command<br />
Maude> (mc-tctl {<strong>in</strong>it} |=<br />
AG((’HierarchicalTrafficLight . ’Decision | (port ’Error is present))<br />
implies AF[c a, b c] (’HierarchicalTrafficLight |<br />
(’Cyel = # 1, ’Cgrn = # 0, ’Cred = # 0)))) .)<br />
Figure 8 shows the dialog w<strong>in</strong>dow for the <strong>Real</strong>-<strong>Time</strong> Maude code generation<br />
of the hierarchical traffic light model: after enter<strong>in</strong>g the error handl<strong>in</strong>g property,<br />
a simple click on the Generate button will display the result of the model<br />
check<strong>in</strong>g command execution <strong>in</strong> the “Code Generator Commands” box.<br />
7 Conclusions and Future Work<br />
We have described the semantic foundations of our T<strong>CTL</strong> model checker for<br />
<strong>Real</strong>-<strong>Time</strong> Maude. Our model<strong>in</strong>g formalism is more expressive than those of<br />
other timed model checkers, allow<strong>in</strong>g us to analyze real-time systems which<br />
are beyond the scope of other verification tools. In particular, we have proved<br />
soundness and completeness of our model checker for a class of dense-time <strong>Real</strong><br />
<strong>Time</strong> Maude specifications that conta<strong>in</strong> many systems outside the scope of other<br />
real-time model checkers. Furthermore, the <strong>in</strong>troduced T<strong>CTL</strong> model checker also<br />
provides for free a timed temporal logic model checker for <strong>in</strong>terest<strong>in</strong>g subsets of<br />
model<strong>in</strong>g languages widely used <strong>in</strong> <strong>in</strong>dustry, such as Ptolemy II and the avionics<br />
standard AADL.<br />
So far, we have only proved soundness and completeness for formulas with<br />
closed <strong>in</strong>tervals under the cont<strong>in</strong>uous semantics. We should also cover formulas<br />
with open time <strong>in</strong>tervals and the po<strong>in</strong>twise semantics. The model checker should<br />
also provide counter-examples <strong>in</strong> a user-friendly way, when possible. We should<br />
also extend our model checker to time-bounded T<strong>CTL</strong> model check<strong>in</strong>g to support<br />
the model check<strong>in</strong>g of systems with <strong>in</strong>f<strong>in</strong>ite reachable state space. F<strong>in</strong>ally, the<br />
current version of the tool is implemented at the Maude meta-level; for efficiency<br />
purposes, it should be implemented <strong>in</strong> C++ <strong>in</strong> the Maude eng<strong>in</strong>e.<br />
References<br />
1. Aalst, W.M.P.v.d.: Interval timed coloured Petri nets and their analysis. In: Application<br />
and Theory of Petri Nets 1993. LNCS, vol. 691, pp. 453–472. Spr<strong>in</strong>ger<br />
(1993)<br />
2. AlTurki, M., Meseguer, J.: <strong>Real</strong>-time rewrit<strong>in</strong>g semantics of Orc. In: Proc.<br />
PPDP’07. ACM (2007)<br />
3. Alur, R., Dill, D.L.: A theory of timed automata. Theoretical Computer Science<br />
126(2), 183–235 (1994)<br />
4. Alur, R., Henz<strong>in</strong>ger, T.: Logics and models of real time: A survey. In: <strong>Real</strong> <strong>Time</strong>:<br />
Theory <strong>in</strong> Practice. LNCS, vol. 600. Spr<strong>in</strong>ger (1992)
<strong><strong>Time</strong>d</strong> <strong>CTL</strong> <strong>Model</strong> <strong>Check<strong>in</strong>g</strong> <strong>in</strong> <strong>Real</strong>-<strong>Time</strong> Maude 39<br />
5. Alur, R., Courcoubetis, C., Dill, D.: <strong>Model</strong>-check<strong>in</strong>g <strong>in</strong> dense real-time. Inf. Comput.<br />
104, 2–34 (May 1993)<br />
6. Bae, K., Ölveczky, P.C., Al-Nayeem, A., Meseguer, J.: Synchronous AADL and its<br />
formal analysis <strong>in</strong> <strong>Real</strong>-<strong>Time</strong> Maude. In: ICFEM’11. LNCS, vol. 6991. Spr<strong>in</strong>ger<br />
(2011)<br />
7. Bae, K., Ölveczky, P.C., Feng, T.H., Lee, E.A., Tripakis, S.: Verify<strong>in</strong>g hierarchical<br />
Ptolemy II discrete-event models us<strong>in</strong>g <strong>Real</strong>-<strong>Time</strong> Maude. Science of Computer<br />
Programm<strong>in</strong>g (2011), to appear, doi:10.1016/j.scico.2010.10.002<br />
8. Baier, C., Katoen, J.P.: Pr<strong>in</strong>ciples of <strong>Model</strong> <strong>Check<strong>in</strong>g</strong>. MIT Press (2008)<br />
9. Behrmann, G., David, A., Larsen, K.G.: A tutorial on uppaal. In: SFM-RT 2004.<br />
LNCS, vol. 3185. Spr<strong>in</strong>ger (2004)<br />
10. Boronat, A., Ölveczky, P.C.: Formal real-time model transformations <strong>in</strong> MO-<br />
MENT2. In: FASE’10. LNCS, vol. 6013. Spr<strong>in</strong>ger (2010)<br />
11. Boucheneb, H., Gardey, G., Roux, O.H.: T<strong>CTL</strong> <strong>Model</strong> <strong>Check<strong>in</strong>g</strong> of <strong>Time</strong> Petri<br />
Nets. J Logic Computation 19(6), 1509–1540 (2009)<br />
12. Bouyer, P.: <strong>Model</strong>-check<strong>in</strong>g timed temporal logics. ENTCS 231, 323–341 (2009)<br />
13. Clarke, E., Grumberg, O., Peled, D.A.: <strong>Model</strong> <strong>Check<strong>in</strong>g</strong>. MIT Press (1999)<br />
14. Clarke, E.M., Grumberg, O., McMillan, K.L., Zhao, X.: Efficient generation of<br />
counterexamples and witnesses <strong>in</strong> symbolic model check<strong>in</strong>g. In: DAC ’95 (1995)<br />
15. Clavel, M., Durán, F., Eker, S., L<strong>in</strong>coln, P., Martí-Oliet, N., Meseguer, J., Talcott,<br />
C.: All About Maude, LNCS, vol. 4350. Spr<strong>in</strong>ger (2007)<br />
16. Eker, J., Janneck, J.W., Lee, E.A., Liu, J., Liu, X., Ludvig, J., Neuendorffer, S.,<br />
Sachs, S., Xiong, Y.: Tam<strong>in</strong>g heterogeneity—the Ptolemy approach. Proceed<strong>in</strong>gs<br />
of the IEEE 91(2), 127–144 (2003)<br />
17. Gardey, G., Lime, D., Magn<strong>in</strong>, M., Roux, O.H.: Roméo: A tool for analyz<strong>in</strong>g time<br />
Petri nets. In: CAV’05. LNCS, vol. 3576. Spr<strong>in</strong>ger, Ed<strong>in</strong>burgh, Scotland, UK (2005)<br />
18. Katelman, M., Meseguer, J., Hou, J.: Redesign of the LMST wireless sensor protocol<br />
through formal model<strong>in</strong>g and statistical model check<strong>in</strong>g. In: Proc. FMOODS’08.<br />
LNCS, vol. 5051. Spr<strong>in</strong>ger (2008)<br />
19. Larouss<strong>in</strong>ie, F., Markey, N., Schnoebelen, P.: Efficient timed model check<strong>in</strong>g for<br />
discrete-time systems. Theor. Comput. Sci. 353, 249–271 (2006)<br />
20. Lepri, D., Ölveczky, P.C., Ábrahám, E.: <strong>Model</strong> check<strong>in</strong>g classes of metric LTL<br />
properties of object-oriented <strong>Real</strong>-<strong>Time</strong> Maude specifications. In: Proc. RTRTS’10.<br />
EPTCS, vol. 36, pp. 117–136 (2010)<br />
21. Lien, E., Ölveczky, P.C.: Formal model<strong>in</strong>g and analysis of an IETF multicast protocol.<br />
In: Proc. SEFM’09. IEEE Computer Society (2009)<br />
22. Markey, N., Schnoebelen, P.: TSMV: A Symbolic <strong>Model</strong> Checker for Quantitative<br />
Analysis of Systems. In: QEST. IEEE Computer Society (2004)<br />
23. Morasca, S., Pezzè, M., Trubian, M.: <strong><strong>Time</strong>d</strong> high-level nets. The Journal of <strong>Real</strong>-<br />
<strong>Time</strong> Systems 3, 165–189 (1991)<br />
24. Ölveczky, P.C.: Towards formal model<strong>in</strong>g and analysis of networks of embedded<br />
medical devices <strong>in</strong> <strong>Real</strong>-<strong>Time</strong> Maude. In: Proc. SNPD’08. IEEE (2008)<br />
25. Ölveczky, P.C.: Semantics, simulation, and formal analysis of model<strong>in</strong>g languages<br />
for embedded systems <strong>in</strong> <strong>Real</strong>-<strong>Time</strong> Maude. In: Formal <strong>Model</strong><strong>in</strong>g: Actors, Open<br />
Systems, Biological Systems. LNCS, vol. 7000. Spr<strong>in</strong>ger (2011)<br />
26. Ölveczky, P.C., Boronat, A., Meseguer, J.: Formal semantics and analysis of behavioral<br />
AADL models <strong>in</strong> <strong>Real</strong>-<strong>Time</strong> Maude. In: Proc. FMOODS/FORTE’10. LNCS,<br />
vol. 6117. Spr<strong>in</strong>ger (2010)<br />
27. Ölveczky, P.C., Caccamo, M.: Formal simulation and analysis of the CASH schedul<strong>in</strong>g<br />
algorithm <strong>in</strong> <strong>Real</strong>-<strong>Time</strong> Maude. In: Proc. FASE’06. LNCS, vol. 3922. Spr<strong>in</strong>ger<br />
(2006)
40 D. Lepri, E. Ábrahám, and P. Cs. Ölveczky<br />
28. Ölveczky, P.C., Meseguer, J.: Specification of real-time and hybrid systems <strong>in</strong><br />
rewrit<strong>in</strong>g logic. Theoretical Computer Science 285, 359–405 (2002)<br />
29. Ölveczky, P.C., Meseguer, J.: Abstraction and completeness for <strong>Real</strong>-<strong>Time</strong> Maude.<br />
Electronic Notes <strong>in</strong> Theoretical Computer Science 176(4), 5–27 (2007)<br />
30. Ölveczky, P.C., Meseguer, J.: Semantics and pragmatics of <strong>Real</strong>-<strong>Time</strong> Maude.<br />
Higher-Order and Symbolic Computation 20(1-2), 161–196 (2007)<br />
31. Ölveczky, P.C., Meseguer, J.: The <strong>Real</strong>-<strong>Time</strong> Maude tool. In: Proc. TACAS’08.<br />
LNCS, vol. 4963. Spr<strong>in</strong>ger (2008)<br />
32. Ölveczky, P.C., Meseguer, J., Talcott, C.L.: Specification and analysis of the<br />
AER/NCA active network protocol suite <strong>in</strong> <strong>Real</strong>-<strong>Time</strong> Maude. Formal Methods<br />
<strong>in</strong> System Design 29(3), 253–293 (2006)<br />
33. Ölveczky, P.C., Thorvaldsen, S.: Formal model<strong>in</strong>g, performance estimation, and<br />
model check<strong>in</strong>g of wireless sensor network algorithms <strong>in</strong> <strong>Real</strong>-<strong>Time</strong> Maude. Theoretical<br />
Computer Science 410(2-3), 254–280 (2009)<br />
34. Riesco, A., Verdejo, A.: Implement<strong>in</strong>g and analyz<strong>in</strong>g <strong>in</strong> Maude the enhanced <strong>in</strong>terior<br />
gateway rout<strong>in</strong>g protocol. Electr. Notes Theor. Comput. Sci. 238(3), 249–266<br />
(2009)<br />
35. Rivera, J.E., Durán, F., Vallecillo, A.: On the behavioral semantics of real-time<br />
doma<strong>in</strong> specific visual languages. In: Proc. WRLA’10. LNCS, vol. 6381. Spr<strong>in</strong>ger<br />
(2010), see also the e-Motions web page http://atenea.lcc.uma.es/<strong>in</strong>dex.php/<br />
Ma<strong>in</strong>_Page/Resources/E-motions<br />
36. Wang, F.: Formal verification of timed systems: A survey and perspective. Proceed<strong>in</strong>gs<br />
of the IEEE 92(8), 1283–1307 (2004)<br />
37. Wang, F.: REDLIB for the formal verification of embedded systems. In: Proc.<br />
ISoLA’06. IEEE (2006)<br />
38. Wirs<strong>in</strong>g, M., Bauer, S.S., Schroeder, A.: <strong>Model</strong><strong>in</strong>g and analyz<strong>in</strong>g adaptive usercentric<br />
systems <strong>in</strong> <strong>Real</strong>-<strong>Time</strong> Maude. In: Proc. RTRTS’10. EPTCS, vol. 36, pp.<br />
1–25 (2010)<br />
39. Yov<strong>in</strong>e, S.: Kronos: A verification tool for real-time systems. Software Tools for<br />
Technology Transfer 1(1–2), 123–133 (1997)