chapter 1 computer forensics and investigations as a profession
chapter 1 computer forensics and investigations as a profession
chapter 1 computer forensics and investigations as a profession
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
CHAPTER 1<br />
COMPUTER FORENSICS AND<br />
INVESTIGATIONS AS A PROFESSION<br />
Modified from the slides accompanying Nelson et al “Computer<br />
Forensics <strong>and</strong> Investigations”. (4ed) Original content © Richard<br />
Austin<br />
Instructor Bio<br />
30+ Year IT Career<br />
Resumed 26+ year HP career <strong>as</strong> a Cyber Security Engineer in Global Cyber Security<br />
MS in IS (concentration in INFOSEC) from KSU (a NCAE/IAE)<br />
CNSS Certificate in Information Security <strong>and</strong> Assurance (IATS 4011, 4012, 4013, 4014)<br />
Senior Member, IEEE<br />
Senior Member, ACM<br />
IEEE Computer Society, CTIN, ISC(2)<br />
Book review editor for IEEE Cipher Postcard<br />
SNIA Security Technical Working Group<br />
INCITS/CS1<br />
Storage <strong>and</strong> Evidence Working Group<br />
Incident Management Working Group<br />
NIST Cloud Forensics Working Group<br />
Cloud Security Alliance<br />
Trusted Cloud Reference Architecture Working Group<br />
Cloud Incident Response <strong>and</strong> Forensics Working Group<br />
Atlanta Chapter of Infragard<br />
Chapter 01 1<br />
Chapter 1<br />
2
Mr. Manners Says<br />
My name is not Dr. Austin (I don’t have a<br />
doctoral degree)<br />
You will treat your fellow students with the<br />
<strong>profession</strong>al courtesy deserving of a<br />
colleague<br />
There are no “dumb” questions – only silly<br />
answers <strong>and</strong> I’ll provide most of those.<br />
Academic Honesty<br />
Trust is the<br />
foundational<br />
requirement for an<br />
information security<br />
<strong>profession</strong>al<br />
Chapter 01 2<br />
Chapter 1<br />
NO!!!<br />
Chapter 1 4<br />
3
What will you learn?<br />
Not a certification prep<br />
Underst<strong>and</strong> the legal <strong>and</strong> policy environment<br />
Similarities <strong>and</strong> differences between digital <strong>forensics</strong> <strong>and</strong> e-discovery<br />
Underst<strong>and</strong> the place of <strong>forensics</strong> in the incident response<br />
process<br />
Processes for identifying, collecting, documenting <strong>and</strong><br />
safeguarding evidence<br />
Analysis of evidence using EnC<strong>as</strong>e Forensic Edition, FTK, The<br />
Sleuth Kit <strong>and</strong> the Volatility framework<br />
Build familiarity with the capabilities <strong>and</strong> use of forensic tools<br />
Documenting <strong>and</strong> reporting the analysis of evidence<br />
In both oral <strong>and</strong> written form<br />
Purpose <strong>and</strong> place of anti-<strong>forensics</strong><br />
Chapter 01 3<br />
Chapter 1<br />
International St<strong>and</strong>ards<br />
ISO 27041CD, p. vi<br />
Chapter 1 6<br />
5
Lecture Outline<br />
Introduce the Course<br />
Chapter 1 Lecture<br />
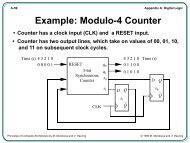
Define <strong>computer</strong> <strong>and</strong> network <strong>forensics</strong><br />
Process for <strong>computer</strong> <strong>investigations</strong><br />
Professional Guidelines <strong>and</strong> Ethics<br />
Cl<strong>as</strong>s Logistics<br />
Chapter 01 4<br />
Chapter 1<br />
Lab/Lecture<br />
Notebook for cl<strong>as</strong>s notes<br />
must be SEWN binding<br />
in your h<strong>and</strong>writing<br />
only thing you’re allowed to use for exams<br />
Laboratory Notebook (or equiv)<br />
Must have by first lab<br />
Chapter 1<br />
7<br />
8
Course Format<br />
We will cover entire text supplemented with<br />
selected outside readings<br />
There will be at le<strong>as</strong>t 8 lab activities<br />
You will perform one complete c<strong>as</strong>e<br />
investigation from the complaint through<br />
evidence collection <strong>and</strong> analysis, reporting <strong>and</strong><br />
presentation to the company CEO <strong>and</strong>/or CFO<br />
with your <strong>as</strong>sessment <strong>and</strong> recommendations for<br />
further action<br />
Chapter 01 5<br />
Chapter 1<br />
Additional Materials<br />
A sewn-bound notebook for your cl<strong>as</strong>s notes<br />
Laboratory notebook – see specific<br />
requirement in the syllabus<br />
Chapter 1<br />
9<br />
10
Labs<br />
Lab <strong>as</strong>signments will be provided on the day<br />
of the lab<br />
There will be an answer/sheet report that<br />
must be turned in at the beginning of the<br />
next cl<strong>as</strong>s meeting<br />
Duplicate record from your laboratory<br />
notebook must accompany answer sheet<br />
Must follow record keeping st<strong>and</strong>ard<br />
Grading<br />
Chapter 01 6<br />
Chapter 1<br />
Labs/Other Assignments 20%<br />
Exam I 20%<br />
Exam 2 20%<br />
Project 40%<br />
Chapter 1 12<br />
11
Late Work<br />
Late work will not be accepted except<br />
If you are absent on the date a deliverable is due,<br />
you may note that on the deliverable with the<br />
re<strong>as</strong>on for your absence <strong>and</strong> turn it in at the next<br />
cl<strong>as</strong>s. At my discretion, I may accept it for credit.<br />
DO NOT:<br />
EMAIL it<br />
Slide it under my office door<br />
Chapter 1 13<br />
Office Hours/Contact Info<br />
See me after cl<strong>as</strong>s<br />
Other arrangements can be made via EMAIL<br />
It is very unlikely that you will reach me at my<br />
office phone <strong>and</strong> I do not use voicemail<br />
EMAIL is the most reliable method for contacting<br />
me <strong>and</strong> I will typically respond within 24 hours<br />
Chapter 1 14<br />
Chapter 01 7
WARNING<br />
Your text does contain errors which I will call<br />
attention to in cl<strong>as</strong>s<br />
The “text book” answer may not be correct<br />
Lecture notes <strong>and</strong> cl<strong>as</strong>sroom presentation<br />
overrule the text<br />
It is the best currently available <strong>forensics</strong> textbook<br />
Forensics is a f<strong>as</strong>t-evolving <strong>profession</strong> <strong>and</strong> a text<br />
is, in some ways, already out-of-date by the time<br />
it is published<br />
What is “<strong>forensics</strong>”<br />
Chapter 01 8<br />
Chapter 1<br />
Webster – from L forensis fr forum. Belonging to,<br />
used in or suitable to courts of judicature or to<br />
public discussion <strong>and</strong> debate<br />
Saferstein – Forensic science in its broadest<br />
definition is the application of science to law<br />
Computer <strong>forensics</strong> – using accepted methods<br />
<strong>and</strong> procedures to properly seize, safeguard <strong>and</strong><br />
analyze data. (Kroll Ontrack)<br />
Chapter 1<br />
15<br />
16
“Evidence”<br />
An item does not become officially a piece of<br />
evidence until a court admits it <strong>as</strong> such<br />
Opposing counsel can (<strong>and</strong> will) challenge this<br />
admission<br />
Incidentally, attorneys do argue with me about which<br />
comes first – the evidence or its admission<br />
Typically where we use the word “evidence,”<br />
we’re using it <strong>as</strong> a shortcut for “item of potential<br />
evidentiary value”<br />
Much of <strong>forensics</strong> practice concerns how to<br />
collect, preserve <strong>and</strong> analyze these items<br />
without compromising their potential to be<br />
admitted <strong>as</strong> evidence in a court of law<br />
Chapter 01 9<br />
Chapter 1<br />
So what is “digital evidence”?<br />
ISO 27037 – “information or data, stored or<br />
transmitted in binary form that may be relied<br />
on <strong>as</strong> evidence”<br />
Eoghan C<strong>as</strong>ey – “any data stored or<br />
transmitted using a <strong>computer</strong> that support or<br />
refute a theory of the offense such <strong>as</strong> intent<br />
or alibi” (Dig. Evid. & Comp. Crime, p. 7)<br />
Brian Carrier – “digital data that support or<br />
refute a hypothesis about digital events or<br />
the state of digital data” (CERIAS TR 2006-6)<br />
Chapter 1 18<br />
17
Evidence<br />
Chapter 1 19<br />
Evidentiary Requirements<br />
(requirements for admissibility)<br />
Relevant<br />
H<strong>as</strong> an important role in deciding a question of<br />
fact<br />
Authentic<br />
The “real” thing<br />
Integrity preserved<br />
Really a component of authenticity but important<br />
enough to mention separately<br />
H<strong>as</strong> not been modified in any way<br />
Chapter 01 10<br />
Chapter 1<br />
20
It Matters In the Private<br />
Sector<br />
The legal<br />
<strong>profession</strong> is<br />
becoming<br />
incre<strong>as</strong>ingly<br />
savvy regarding<br />
digital evidence<br />
including its<br />
recovery<br />
through forensic<br />
processes<br />
Chapter 01 11<br />
Chapter 1<br />
Forensics | e-discovery<br />
The concepts are similar but different<br />
E-discovery formalized in the new FRCP<br />
Focused on indentifying <strong>and</strong> preserving all relevant<br />
digital information not protected by privilege in the<br />
digital corpus of an organization<br />
Forensics<br />
Similar goal but more attuned to indentifying <strong>and</strong><br />
recovering digital artifacts relevant to the matter<br />
Explicitly interface in the “image-<strong>and</strong>-hold”<br />
preservation technique<br />
Chapter 1 22<br />
21
E-discovery<br />
Objectives<br />
Define <strong>computer</strong> <strong>forensics</strong><br />
Chapter 1 23<br />
Describe how to prepare for digital <strong>investigations</strong><br />
<strong>and</strong> explain the difference between law<br />
enforcement agency <strong>and</strong> corporate<br />
<strong>investigations</strong><br />
Explain the importance of maintaining<br />
<strong>profession</strong>al conduct<br />
Chapter 1 24<br />
Chapter 01 12
Underst<strong>and</strong>ing Digital<br />
Forensics<br />
Digital <strong>forensics</strong><br />
Involves obtaining <strong>and</strong> analyzing digital information<br />
<strong>as</strong> well <strong>as</strong> communicating the results of analysis<br />
As evidence in civil, criminal, or administrative c<strong>as</strong>es<br />
Underst<strong>and</strong>ing Digital<br />
Forensics<br />
Chapter 1 25<br />
Fourth Amendment to the U.S. Constitution<br />
Esablishes right to be secure in their person,<br />
residence, <strong>and</strong> property<br />
From search <strong>and</strong> seizure<br />
Search warrants are generally required for most LE<br />
<strong>investigations</strong><br />
Gray area around warrantless searches<br />
Chapter 1 26<br />
Chapter 01 13
Digital Forensics <strong>and</strong> Related<br />
Fields<br />
Computer <strong>forensics</strong><br />
Investigates data that can be retrieved from a <strong>computer</strong>’s<br />
hard disk or other digital devices/media<br />
Network <strong>forensics</strong><br />
Yields information about how a perpetrator or an attacker<br />
gained access to a network <strong>and</strong> how intrusion/extrusion<br />
unfolded over time<br />
Data recovery<br />
Recovering information that w<strong>as</strong> deleted by mistake<br />
Or lost during a power surge or server cr<strong>as</strong>h<br />
Typically you know what you’re looking for<br />
Chapter 1 27<br />
Digital Forensics <strong>and</strong> Related<br />
Fields<br />
Digital <strong>forensics</strong><br />
Overall umbrella term that includes <strong>computer</strong>,<br />
network, memory, etc., <strong>forensics</strong><br />
Evidence can be inculpatory (“incriminating”) or<br />
exculpatory<br />
Dis<strong>as</strong>ter recovery<br />
Uses <strong>computer</strong> <strong>forensics</strong> techniques to retrieve<br />
information their clients have lost<br />
Investigators often work <strong>as</strong> a team to help secure<br />
<strong>computer</strong>s <strong>and</strong> networks in an organization<br />
Chapter 1 28<br />
Chapter 01 14
Digital Forensics<br />
Digital Forensics in the<br />
Enterprise<br />
Enterprise network environment<br />
Chapter 1 29<br />
Large corporate computing systems that might<br />
include disparate or formerly independent systems<br />
Vulnerability <strong>as</strong>sessment <strong>and</strong> risk<br />
management group<br />
Tests <strong>and</strong> verifies the integrity of st<strong>and</strong>alone<br />
workstations <strong>and</strong> network servers<br />
Professionals in this group have skills in network<br />
intrusion detection <strong>and</strong> incident response<br />
Chapter 1 30<br />
Chapter 01 15
Digital Forensics in the<br />
Enterprise<br />
Litigation<br />
Legal process of deciding a question of fact <strong>and</strong> its<br />
consequences<br />
Computer <strong>investigations</strong> group<br />
Manages <strong>investigations</strong> <strong>and</strong> conducts forensic<br />
analysis of systems suspected of containing evidence<br />
related to an incident or a crime<br />
Chapter 1 31<br />
A Brief History of Computer<br />
Forensics<br />
By the 1970s, electronic crimes were incre<strong>as</strong>ing,<br />
especially in the financial sector<br />
Most law enforcement officers didn’t know enough<br />
about <strong>computer</strong>s to <strong>as</strong>k the right questions<br />
Or to preserve evidence for trial<br />
1980s<br />
PCs gained popularity <strong>and</strong> different OSs emerged<br />
Disk Operating System (DOS) w<strong>as</strong> available<br />
Forensics tools were simple, <strong>and</strong> most were generated<br />
by government agencies<br />
Chapter 1 32<br />
Chapter 01 16
A Brief History of Computer<br />
Forensics<br />
Mid-1980s<br />
Xtree Gold appeared on the market<br />
Recognized file types <strong>and</strong> retrieved lost or deleted files<br />
Norton DiskEdit soon followed<br />
And became the best tool for finding deleted files<br />
1987<br />
Apple produced the Mac SE<br />
A Macintosh with an external E<strong>as</strong>yDrive hard disk with<br />
60 MB of storage<br />
Chapter 1 33<br />
A Brief History of Computer<br />
Forensics<br />
Chapter 1 34<br />
Chapter 01 17
A Brief History of Computer<br />
Forensics<br />
Chapter 1 35<br />
A Brief History of Computer<br />
Forensics<br />
Early 1990s<br />
Tools for <strong>computer</strong> <strong>forensics</strong> were available<br />
International Association of Computer Investigative<br />
Specialists (IACIS)<br />
Training on software for <strong>forensics</strong> <strong>investigations</strong><br />
IRS created search-warrant programs<br />
ExpertWitness for the Macintosh<br />
First commercial GUI software for <strong>computer</strong> <strong>forensics</strong><br />
Created by ASR Data<br />
Chapter 1 36<br />
Chapter 01 18
A Brief History of Computer<br />
Forensics<br />
Early 1990s<br />
ExpertWitness for the Macintosh<br />
Recovers deleted files <strong>and</strong> fragments of deleted files<br />
Large hard disks posed problems for investigators<br />
Other software<br />
iLook<br />
AccessData Forensic Toolkit (FTK)<br />
Underst<strong>and</strong>ing C<strong>as</strong>e Law<br />
Technology is evolving at a rapid pace<br />
Chapter 1 37<br />
Existing laws <strong>and</strong> statutes are lagging the technology<br />
C<strong>as</strong>e (or judge-made) law used when specific<br />
statutes or regulations don’t exist<br />
C<strong>as</strong>e law allows courts to use previous c<strong>as</strong>es<br />
similar to the current one<br />
Because the laws don’t yet exist<br />
Each c<strong>as</strong>e is evaluated on its own merit <strong>and</strong><br />
issues<br />
Chapter 1 38<br />
Chapter 01 19
Developing Computer<br />
Forensics Resources<br />
You must know more than one computing<br />
platform<br />
Be familiar with the platforms used in your<br />
organization <strong>as</strong> well <strong>as</strong> other common ones<br />
Join applicable <strong>profession</strong>al <strong>as</strong>sociations<br />
Computer Technology Investigators Network<br />
(CTIN)<br />
Meets monthly to discuss problems that law<br />
enforcement <strong>and</strong> corporations face<br />
Chapter 1 39<br />
Developing Computer Forensics<br />
Resources<br />
High Technology Crime Investigation Association<br />
(HTCIA)<br />
Exchanges information about techniques related to <strong>computer</strong><br />
<strong>investigations</strong> <strong>and</strong> security<br />
Restrictions on members working on criminal defense c<strong>as</strong>es<br />
User groups can be helpful<br />
Build a network of <strong>computer</strong> <strong>forensics</strong> experts <strong>and</strong> other<br />
<strong>profession</strong>als<br />
And keep in touch through e-mail, listservs, social networks, etc<br />
Outside experts can provide detailed information you<br />
need to retrieve digital evidence<br />
Chapter 1 40<br />
Chapter 01 20
Preparing for Computer<br />
Investigations<br />
Computer <strong>investigations</strong> <strong>and</strong> <strong>forensics</strong> falls into<br />
two distinct (but non-exclusive) categories<br />
Public <strong>investigations</strong><br />
Private or corporate <strong>investigations</strong><br />
Public <strong>investigations</strong><br />
Involve government agencies responsible for criminal<br />
<strong>investigations</strong> <strong>and</strong> prosecution<br />
Stringent set of legal requirements<br />
Law of search <strong>and</strong> seizure<br />
Protects rights of all people, including suspects<br />
Preparing for Computer<br />
Investigations<br />
Chapter 1 41<br />
Chapter 1 42<br />
Chapter 01 21
Preparing for Computer<br />
Investigations<br />
Preparing for Computer<br />
Investigations<br />
Private or corporate <strong>investigations</strong><br />
Chapter 1 43<br />
Deal with private companies, non-law-enforcement<br />
government agencies, <strong>and</strong> lawyers<br />
Aren’t directly governed directly by criminal law or<br />
Fourth Amendment issues<br />
Governed by internal policies that define expected<br />
employee behavior <strong>and</strong> conduct in the workplace<br />
Private corporate <strong>investigations</strong> also involve<br />
litigation disputes<br />
Investigations are usually conducted in civil c<strong>as</strong>es<br />
Chapter 1 44<br />
Chapter 01 22
Flow of Investigation<br />
Chapter 01 23<br />
Chapter 1<br />
Underst<strong>and</strong>ing Law<br />
Enforcements Agency<br />
Investigations<br />
In a criminal c<strong>as</strong>e, a suspect is tried for a criminal<br />
offense<br />
Such <strong>as</strong> burglary, murder, or molestation<br />
Computers <strong>and</strong> networks might be the only tools<br />
that can be used to commit certain crimes<br />
Many states have added specific language to criminal<br />
codes to define crimes involving <strong>computer</strong>s<br />
Following the legal process<br />
Legal processes depend on local custom, legislative<br />
st<strong>and</strong>ards, <strong>and</strong> rules of evidence<br />
Chapter 1 46<br />
45
Underst<strong>and</strong>ing Law Enforcements<br />
Agency Investigations<br />
Following the legal process<br />
Criminal c<strong>as</strong>e follows three stages<br />
The complaint, the investigation, <strong>and</strong> the<br />
prosecution<br />
Chapter 1 47<br />
Underst<strong>and</strong>ing Law Enforcements<br />
Agency Investigations<br />
Following the legal process<br />
A criminal c<strong>as</strong>e begins when someone believes an<br />
illegal act h<strong>as</strong> occurred<br />
Complainant makes an allegation<br />
A police officer interviews the complainant <strong>and</strong><br />
writes a report about the crime<br />
Investigators delegate, collect, <strong>and</strong> process the<br />
information related to the complaint<br />
Chapter 1 48<br />
Chapter 01 24
Underst<strong>and</strong>ing Law Enforcements<br />
Agency Investigations<br />
Following the legal process<br />
After building the c<strong>as</strong>e, the information is turned<br />
over to the prosecutor<br />
Affidavit<br />
Sworn statement of support of facts about or<br />
evidence of a crime<br />
Example: Probable-cause affidavit submitted to a<br />
judge in requesting a search warrant<br />
Judge must approve <strong>and</strong> sign a search warrant<br />
Before authorized to collect evidence<br />
Chapter 1 49<br />
Requirements for Warrant<br />
Probable cause to believe:<br />
A crime is being/h<strong>as</strong> been committed<br />
Relevant evidence exists at a particular place<br />
Must identify specifically what is to be<br />
searched for which<br />
“Fishing expeditions” are prohibited<br />
Challenge is to be general enough to include all<br />
relevant items while specific enough to p<strong>as</strong>s the<br />
test<br />
Chapter 1 50<br />
Chapter 01 25
Example of Comprehensive<br />
Language<br />
1. Computer hardware to include any <strong>and</strong> all <strong>computer</strong> equipment used to collect, analyze, create, display, convert, store,<br />
conceal, or transmit electronic, magnetic, optical, or similar <strong>computer</strong> impulses or data. Hardware includes (but is not<br />
limited to) any data-processing devices (such <strong>as</strong> central processing units, personal <strong>computer</strong>s to include "laptop" or<br />
"notebook" <strong>computer</strong>s); internal <strong>and</strong> peripheral storage devices (such <strong>as</strong> fixed disks, external hard disks, floppy disk drives<br />
<strong>and</strong> diskettes, tape drives <strong>and</strong> tapes, optical storage devices, <strong>and</strong> other electronic media devices); peripheral input/output<br />
devices (such <strong>as</strong> keyboards, printers, scanners, plotters, video display monitors, <strong>and</strong> optical readers); <strong>and</strong> related<br />
communications devices (such <strong>as</strong> modems, cables <strong>and</strong> connections, <strong>and</strong> recording equipment,); <strong>as</strong> well <strong>as</strong> any devices,<br />
mechanisms, or parts that can be used to restrict access to <strong>computer</strong> hardware (such <strong>as</strong> physical keys <strong>and</strong> locks).<br />
2. Computer software required to run the above hardware <strong>and</strong>/or access data from the hardware, e.g., software required to run<br />
operating systems, applications (like word-processing, graphics, or spreadsheet programs), utilities, compilers,<br />
interpreters, <strong>and</strong> communications programs.<br />
3. Computer-related documentation such <strong>as</strong> written, recorded, printed, or electronically stored material which explains or<br />
illustrates how to configure or use <strong>computer</strong> hardware, software, or other related items.<br />
4. Data maintained on the <strong>computer</strong>, or <strong>computer</strong> related storage devices such <strong>as</strong> floppy diskettes, tape backups, <strong>computer</strong><br />
printouts, <strong>and</strong> “zip” drive diskettes. In particular, data in the form of images, <strong>and</strong>/or log files recording the transmission of<br />
images <strong>as</strong> they relate to violations of Florida law.<br />
5. Documents, notes, or equipment relating to p<strong>as</strong>swords <strong>and</strong> data security devices which may restrict access to the hardware,<br />
software or data.<br />
6. All <strong>computer</strong> files <strong>as</strong>sociated with the accounts listed above, including p<strong>as</strong>sword protected files, both text <strong>and</strong> image types<br />
that may include, but are not limited to: “.doc, .txt, .gif, .bmp, .tif, .pcs, .pic, .png, .dcs, .art or .jpeg.”, that can be stored or<br />
saved by these suffixes or they can be renamed <strong>and</strong> saved under different titles<br />
Graciously provided courtesy of Dennis Nicew<strong>and</strong>er, Assistant State Attorney,<br />
State of Florida<br />
Chapter 01 26<br />
Chapter 1<br />
Following the Legal Process<br />
The Search Warrant<br />
UNITED STATES DISTRICT COURT<br />
District of Arizona<br />
In the matter of the Search of<br />
(Name, address or brief description of person or property to be searched)<br />
SEARCH WARRANT 12345 E<strong>as</strong>t Hacker Street Apt. 866 C<strong>as</strong>e Number:#### 98-5887MB Phoenix, Arizona TO: Bill<br />
F. Scrotum, III <strong>and</strong> any Authorized Officer of the United States Affidavit(s) having been made before me by affiant,<br />
Bill F. Scrotum, III, who h<strong>as</strong> re<strong>as</strong>on to believe that /_/ on the person of or /X/ on the premises known <strong>as</strong> (name,<br />
description <strong>and</strong>/or location)<br />
SEE ATTACHMENT A.<br />
in the District of Arizona there is now concealed a certain person or property namely (describe the person or<br />
property)<br />
SEE ATTACHMENT C.<br />
I am satisfied that the affidavit(s) <strong>and</strong> any recorded testimony establish probably cause to believe that the person<br />
or property so described is now concealed on the person or premises above-described <strong>and</strong> establish grounds for<br />
the issuance of this warrant.<br />
YOU ARE HEREBY COMMANDED to search on or before _______12-20-98__at__11:15a.m.________ Date<br />
http://all.net/books/<strong>forensics</strong>/warrant.html<br />
Chapter 1<br />
51<br />
52
Underst<strong>and</strong>ing Corporate<br />
Investigations<br />
Private or corporate <strong>investigations</strong><br />
Involve organizations <strong>and</strong> attorneys h<strong>and</strong>ling policy<br />
violations <strong>and</strong> litigation<br />
Corporate <strong>computer</strong> crimes can involve:<br />
E-mail har<strong>as</strong>sment<br />
Falsification of data<br />
Gender <strong>and</strong> age discrimination<br />
Embezzlement<br />
Sabotage<br />
Industrial espionage<br />
Establishing Company<br />
Policies<br />
Policies minimize risk of litigation<br />
Policies provide:<br />
Chapter 1 53<br />
Defines how company <strong>computer</strong>s <strong>and</strong> networks<br />
should be used<br />
Line of authority for internal <strong>investigations</strong><br />
Who h<strong>as</strong> the authority to initiate an investigation<br />
Who can take possession of evidence<br />
Who can have access to evidence<br />
Chapter 01 27<br />
Chapter 1<br />
54
Know Where the Line Is<br />
Criminal matters MUST be reported to law<br />
enforcement<br />
Accessory after the fact<br />
Conspiracy to conceal the commission of a crime<br />
Child pornography is the text-book c<strong>as</strong>e<br />
Chapter 01 28<br />
Chapter 1<br />
Silver Platter Doctrine<br />
Originally, state agencies could illegally obtain evidence<br />
<strong>and</strong> have it admitted in Federal court since Federal<br />
officials had not participated in the violation of the<br />
defendant’s rights . Since repudiated in Elkins v U.S.<br />
(Black’s, 5ed, p.1240)<br />
Text (wrongly) uses it in the sense of evidence presented<br />
to LE “on a silver platter” by a civilian<br />
Typically immune to challenge on constitutional grounds<br />
regarding search <strong>and</strong> seizure IF done independent of <strong>and</strong><br />
not at the request of law enforcement<br />
Can be challenged on authenticity <strong>and</strong> integrity<br />
May be challenged b<strong>as</strong>ed on policy support for its original<br />
collection<br />
Evolving area of law – stay current!!!<br />
Chapter 1<br />
55<br />
56
How We See Each Other<br />
Keystone Kops<br />
Scenario<br />
Detective “Wanna-be’s”<br />
Buster Keaton, Sherlock Jr., 1924<br />
Chapter 01 29<br />
Chapter 1<br />
You are a <strong>forensics</strong> consultant retained to<br />
investigate Joe’s <strong>computer</strong> for evidence of<br />
theft of trade secrets<br />
In the course of your examination, you<br />
discover over 100 photographs of prepubescent<br />
males in lewd sexual situations<br />
What actions do you take?<br />
Chapter 1<br />
57<br />
58
Underst<strong>and</strong>ing Corporate<br />
Investigations<br />
Displaying Warning Banners<br />
Deals with the expectation of privacy<br />
Helps avoid litigation over whether or not the<br />
evidence w<strong>as</strong> legally acquired<br />
Underst<strong>and</strong>ing Corporate<br />
Investigations<br />
Displaying Warning Banners<br />
Warning banner<br />
Chapter 1 59<br />
Usually appears when a <strong>computer</strong> starts or connects to the<br />
company intranet, network, or virtual private network<br />
Informs end users that the organization reserves the right<br />
to inspect <strong>computer</strong> systems <strong>and</strong> network traffic at will<br />
Establishes the right to conduct an investigation<br />
As a corporate <strong>computer</strong> investigator<br />
Make sure company displays well-defined warning<br />
banners<br />
Chapter 1 60<br />
Chapter 01 30
Underst<strong>and</strong>ing Corporate<br />
Investigations<br />
A sample banner from a US Government-owned system<br />
Chapter 1 61<br />
Underst<strong>and</strong>ing Corporate<br />
Investigations<br />
Designating an authorized requester<br />
Authorized requester h<strong>as</strong> the power to request<br />
<strong>investigations</strong><br />
Policy should be defined by executive management<br />
Groups that commonly have direct authority to request<br />
<strong>computer</strong> <strong>investigations</strong><br />
Corporate Security Investigations<br />
Corporate Ethics Office<br />
Corporate Equal Employment Opportunity Office<br />
Internal Auditing<br />
The general counsel or Legal Department<br />
Chapter 1 62<br />
Chapter 01 31
Underst<strong>and</strong>ing Corporate<br />
Investigations<br />
Conducting security <strong>investigations</strong><br />
Types of situations<br />
Abuse or misuse of corporate <strong>as</strong>sets<br />
E-mail abuse<br />
Internet abuse<br />
Be sure to distinguish between a company’s policy<br />
violations <strong>and</strong> potential criminal issues<br />
Corporations may provide evidence to LE if a crime is<br />
involved<br />
What happens when a civilian or corporate investigative<br />
agent delivers evidence to a law enforcement officer?<br />
Chapter 1 63<br />
Underst<strong>and</strong>ing Corporate<br />
Investigations<br />
Distinguishing personal <strong>and</strong> company property<br />
Many company policies distinguish between personal <strong>and</strong><br />
company digital property<br />
One area that’s difficult to distinguish involves<br />
PDAs/smartphones, cell phones, <strong>and</strong> personal<br />
notebook/tablet <strong>computer</strong>s<br />
The safe policy is to not allow any personally owned devices<br />
to be connected to company-owned resources<br />
Limiting the possibility of commingling personal <strong>and</strong> company<br />
data<br />
This is incre<strong>as</strong>ingly a counsel of perfection so don’t bet the<br />
farm on it<br />
Chapter 1 64<br />
Chapter 01 32
Maintaining Professional<br />
St<strong>and</strong>ards<br />
Professional conduct<br />
Determines your credibility<br />
Includes ethics, morals, <strong>and</strong> st<strong>and</strong>ards of behavior<br />
Maintaining objectivity means you must form <strong>and</strong><br />
sustain unbi<strong>as</strong>ed opinions of your c<strong>as</strong>es<br />
Maintain an investigation’s credibility by keeping<br />
the c<strong>as</strong>e confidential<br />
In the corporate environment, confidentiality is critical<br />
In rare instances, your corporate c<strong>as</strong>e might<br />
become a criminal c<strong>as</strong>e <strong>as</strong> serious <strong>as</strong> murder<br />
Objectivity<br />
Chapter 1 65<br />
If the law h<strong>as</strong> made you a witness, remain a<br />
man of science, you have no victim to<br />
avenge, no guilty or innocent person to<br />
convict or save – you must bear testimony<br />
within the limits of science.<br />
-- Dr. P. C. Brouardel, 19 th century French forensic scientist<br />
Chapter 1 66<br />
Chapter 01 33
Maintaining Professional<br />
St<strong>and</strong>ards<br />
Maintaining objectivity<br />
Sustain unbi<strong>as</strong>ed opinions of your c<strong>as</strong>es<br />
You are an INVESTIGATOR not the JUDGE or JURY<br />
Brady doctrine requires discovery <strong>and</strong> disclosure of evidence that may<br />
disprove an allegation<br />
Avoid making conclusions about the findings until all<br />
relevant information h<strong>as</strong> been examined<br />
Consider ALL the available facts – not just those that<br />
support the prevailing theory<br />
Ignore external bi<strong>as</strong>es to maintain the integrity of the<br />
fact-finding in all <strong>investigations</strong><br />
Keep the c<strong>as</strong>e confidential<br />
Why does this matter?<br />
Scenario<br />
Chapter 01 34<br />
Chapter 1<br />
Investigator Smith approached a colleague of<br />
Jane<br />
I’m investigating Jane for sexual har<strong>as</strong>sment …<br />
Smith is at a cocktail party “You’ll never<br />
believe what I found on Joe’s <strong>computer</strong> …”<br />
What are the consequences of such<br />
un<strong>profession</strong>al behavior?<br />
Chapter 1<br />
67<br />
68
Maintaining Professional<br />
St<strong>and</strong>ards<br />
Enhance your <strong>profession</strong>al skills through<br />
continuing education<br />
Record your fact-finding methods in a journal<br />
Attend workshops, conferences, <strong>and</strong> vendor<br />
courses<br />
Membership in <strong>profession</strong>al organizations adds to<br />
your credentials<br />
Achieve a high public <strong>and</strong> private st<strong>and</strong>ing <strong>and</strong><br />
maintain honesty <strong>and</strong> integrity<br />
Summary<br />
Chapter 1 69<br />
Computer <strong>forensics</strong> applies <strong>forensics</strong> procedures<br />
to digital evidence<br />
Laws about digital evidence established in the<br />
1970s<br />
To be a successful <strong>computer</strong> <strong>forensics</strong><br />
investigator, you must know more than one<br />
computing platform<br />
Public <strong>and</strong> private <strong>computer</strong> <strong>investigations</strong> are<br />
different in some ways but alike in others<br />
Chapter 1 70<br />
Chapter 01 35
Summary<br />
Use warning banners to remind employees <strong>and</strong><br />
visitors of policy on <strong>computer</strong> <strong>and</strong> Internet use<br />
Companies should define <strong>and</strong> limit the number of<br />
authorized requesters who can start an<br />
investigation<br />
Digital <strong>forensics</strong> investigators must maintain<br />
<strong>profession</strong>al conduct to protect their credibility<br />
Chapter 1 71<br />
Chapter 01 36