- Page 1 and 2:
I know what you have done in your l
- Page 3 and 4:
This is actually not from a horror
- Page 5 and 6:
This is actually not from a horror
- Page 7 and 8:
. . . yet it is as scary, at least.
- Page 9 and 10:
. . . yet it is as scary, at least.
- Page 11 and 12:
Authenticity of images in the digit
- Page 13 and 14:
Digital image forensics: a first gl
- Page 15 and 16:
Digital image forensics: a first gl
- Page 17 and 18:
Digital image forensics: a first gl
- Page 19 and 20:
Two introductory examples ◮ digit
- Page 21 and 22:
Two introductory examples ◮ digit
- Page 23 and 24:
Two introductory examples ◮ digit
- Page 25 and 26:
1 After all, it’s all about bits
- Page 27 and 28:
By the way, what is computer forens
- Page 29 and 30:
By the way, what is computer forens
- Page 31 and 32:
Digital forensics: proposed ontolog
- Page 33 and 34:
WARNING! The following slides inten
- Page 35 and 36:
Computer forensics = Image forensic
- Page 37 and 38:
Computer forensics = Image forensic
- Page 39 and 40:
Computer forensics: a closer look p
- Page 41 and 42:
suspicious traces? Computer forensi
- Page 43 and 44:
suspicious traces? Computer forensi
- Page 45 and 46:
Image forensics: a closer look orig
- Page 47 and 48:
Image forensics: a closer look orig
- Page 49 and 50:
Sensors: a source of uncertainty
- Page 51 and 52:
Sensors: a source of uncertainty
- Page 53 and 54:
Models: yet another dimensionality
- Page 55 and 56: Models: yet another dimensionality
- Page 57 and 58: Fundamentals of digital image foren
- Page 59 and 60: Fundamentals of digital image foren
- Page 61 and 62: Fundamentals of digital image foren
- Page 63 and 64: Fundamentals of digital image foren
- Page 65 and 66: Fundamentals of digital image foren
- Page 67 and 68: Fundamentals of digital image foren
- Page 69 and 70: Fundamentals of digital image foren
- Page 71 and 72: Fundamentals of digital image foren
- Page 73 and 74: Fundamentals of digital image foren
- Page 75 and 76: Image source identification goal: d
- Page 77 and 78: Intra- and inter-model similarities
- Page 79 and 80: Camera model identification ◮ mos
- Page 81 and 82: Some results on camera model identi
- Page 83 and 84: Camera model identification: overal
- Page 85 and 86: Camera device identification ◮ mo
- Page 87 and 88: Camera device identification ◮ mo
- Page 89 and 90: A typical noise residual Wavelet de
- Page 91 and 92: correlation coefficient Was it your
- Page 93 and 94: Image source identfication: Summary
- Page 95 and 96: Need a break? Ooops. . . submission
- Page 97 and 98: Image manipulation detection Digita
- Page 99 and 100: Image manipulation detection Digita
- Page 101 and 102: Image manipulation detection Digita
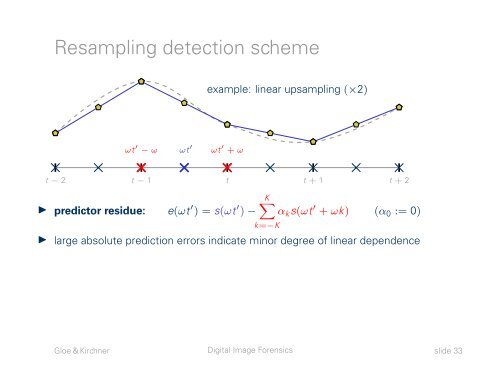
- Page 103 and 104: Resampling detection ◮ image mani
- Page 105: Resampling detection scheme example
- Page 109 and 110: Resampling detection scheme ωt ′
- Page 111 and 112: It’s not only the biggest potato
- Page 113 and 114: Color filter array interpolation
- Page 115 and 116: Example application of CFA artifact
- Page 117 and 118: Example application of CFA artifact
- Page 119 and 120: Double JPEG compression Main idea /
- Page 121 and 122: Double JPEG compression artifacts Q
- Page 123 and 124: Church of our Ladies, Dresden A typ
- Page 125 and 126: . . . and a practical application J
- Page 127 and 128: 3Digital image forensics requires i
- Page 129 and 130: How does your algorithm know that t
- Page 131 and 132: How to capture 14 000 images . . .
- Page 133: min / max temperature [ ◦ C] 8 4
- Page 136 and 137: DOCMA Award Background ◮ creating
- Page 138 and 139: DOCMA Award: some examples Original
- Page 140 and 141: DOCMA Award: some examples Original
- Page 142 and 143: DOCMA Award: some examples Original
- Page 144 and 145: 4Now that we have the theory behind
- Page 146 and 147: Digital forensics: proposed ontolog
- Page 148 and 149: Counter-forensics: computer forensi
- Page 150 and 151: Counter-forensics: computer forensi
- Page 152 and 153: Counter-forensics: computer forensi
- Page 154 and 155: Counter-forensics: image forensics
- Page 156 and 157:
Attacks: practical considerations W
- Page 158 and 159:
fin Concluding remarks
- Page 160 and 161:
Multimedia forensics: a growing fie
- Page 162 and 163:
A broader view 2 2 7 7 ICSI 2010 2A
- Page 164 and 165:
Computer forensics in a broader sen
- Page 166 and 167:
Computer forensics in a broader sen
- Page 168:
Image sources ⊲ Photoshop logo (t