Obfuscation of Abstract Data-Types - Rowan
Obfuscation of Abstract Data-Types - Rowan
Obfuscation of Abstract Data-Types - Rowan
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
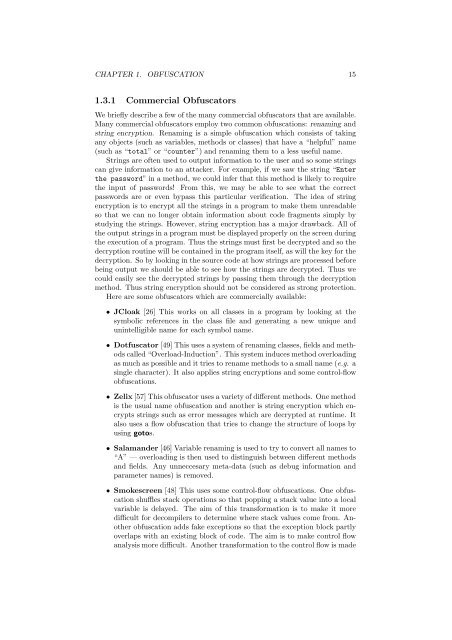
CHAPTER 1. OBFUSCATION 15<br />
1.3.1 Commercial Obfuscators<br />
We briefly describe a few <strong>of</strong> the many commercial obfuscators that are available.<br />
Many commercial obfuscators employ two common obfuscations: renaming and<br />
string encryption. Renaming is a simple obfuscation which consists <strong>of</strong> taking<br />
any objects (such as variables, methods or classes) that have a “helpful” name<br />
(such as “total” or “counter”) and renaming them to a less useful name.<br />
Strings are <strong>of</strong>ten used to output information to the user and so some strings<br />
can give information to an attacker. For example, if we saw the string “Enter<br />
the password” in a method, we could infer that this method is likely to require<br />
the input <strong>of</strong> passwords! From this, we may be able to see what the correct<br />
passwords are or even bypass this particular verification. The idea <strong>of</strong> string<br />
encryption is to encrypt all the strings in a program to make them unreadable<br />
so that we can no longer obtain information about code fragments simply by<br />
studying the strings. However, string encryption has a major drawback. All <strong>of</strong><br />
the output strings in a program must be displayed properly on the screen during<br />
the execution <strong>of</strong> a program. Thus the strings must first be decrypted and so the<br />
decryption routine will be contained in the program itself, as will the key for the<br />
decryption. So by looking in the source code at how strings are processed before<br />
being output we should be able to see how the strings are decrypted. Thus we<br />
could easily see the decrypted strings by passing them through the decryption<br />
method. Thus string encryption should not be considered as strong protection.<br />
Here are some obfuscators which are commercially available:<br />
• JCloak [26] This works on all classes in a program by looking at the<br />
symbolic references in the class file and generating a new unique and<br />
unintelligible name for each symbol name.<br />
• Dotfuscator [49] This uses a system <strong>of</strong> renaming classes, fields and methods<br />
called “Overload-Induction”. This system induces method overloading<br />
as much as possible and it tries to rename methods to a small name (e.g. a<br />
single character). It also applies string encryptions and some control-flow<br />
obfuscations.<br />
• Zelix [57] This obfuscator uses a variety <strong>of</strong> different methods. One method<br />
is the usual name obfuscation and another is string encryption which encrypts<br />
strings such as error messages which are decrypted at runtime. It<br />
also uses a flow obfuscation that tries to change the structure <strong>of</strong> loops by<br />
using gotos.<br />
• Salamander [46] Variable renaming is used to try to convert all names to<br />
“A” — overloading is then used to distinguish between different methods<br />
and fields. Any unneccesary meta-data (such as debug information and<br />
parameter names) is removed.<br />
• Smokescreen [48] This uses some control-flow obfuscations. One obfuscation<br />
shuffles stack operations so that popping a stack value into a local<br />
variable is delayed. The aim <strong>of</strong> this transformation is to make it more<br />
difficult for decompilers to determine where stack values come from. Another<br />
obfuscation adds fake exceptions so that the exception block partly<br />
overlaps with an existing block <strong>of</strong> code. The aim is to make control flow<br />
analysis more difficult. Another transformation to the control flow is made