Obfuscation of Abstract Data-Types - Rowan
Obfuscation of Abstract Data-Types - Rowan
Obfuscation of Abstract Data-Types - Rowan
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
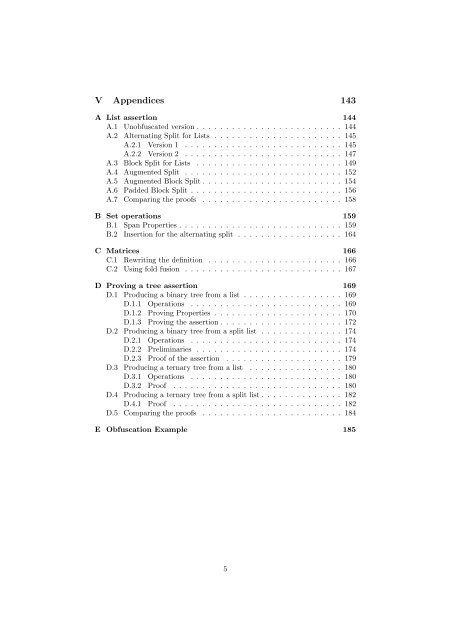
V Appendices 143<br />
A List assertion 144<br />
A.1 Unobfuscated version . . . . . . . . . . . . . . . . . . . . . . . . . 144<br />
A.2 Alternating Split for Lists . . . . . . . . . . . . . . . . . . . . . . 145<br />
A.2.1 Version 1 . . . . . . . . . . . . . . . . . . . . . . . . . . . 145<br />
A.2.2 Version 2 . . . . . . . . . . . . . . . . . . . . . . . . . . . 147<br />
A.3 Block Split for Lists . . . . . . . . . . . . . . . . . . . . . . . . . 149<br />
A.4 Augmented Split . . . . . . . . . . . . . . . . . . . . . . . . . . . 152<br />
A.5 Augmented Block Split . . . . . . . . . . . . . . . . . . . . . . . . 154<br />
A.6 Padded Block Split . . . . . . . . . . . . . . . . . . . . . . . . . . 156<br />
A.7 Comparing the pro<strong>of</strong>s . . . . . . . . . . . . . . . . . . . . . . . . 158<br />
B Set operations 159<br />
B.1 Span Properties . . . . . . . . . . . . . . . . . . . . . . . . . . . . 159<br />
B.2 Insertion for the alternating split . . . . . . . . . . . . . . . . . . 164<br />
C Matrices 166<br />
C.1 Rewriting the definition . . . . . . . . . . . . . . . . . . . . . . . 166<br />
C.2 Using fold fusion . . . . . . . . . . . . . . . . . . . . . . . . . . . 167<br />
D Proving a tree assertion 169<br />
D.1 Producing a binary tree from a list . . . . . . . . . . . . . . . . . 169<br />
D.1.1 Operations . . . . . . . . . . . . . . . . . . . . . . . . . . 169<br />
D.1.2 Proving Properties . . . . . . . . . . . . . . . . . . . . . . 170<br />
D.1.3 Proving the assertion . . . . . . . . . . . . . . . . . . . . . 172<br />
D.2 Producing a binary tree from a split list . . . . . . . . . . . . . . 174<br />
D.2.1 Operations . . . . . . . . . . . . . . . . . . . . . . . . . . 174<br />
D.2.2 Preliminaries . . . . . . . . . . . . . . . . . . . . . . . . . 174<br />
D.2.3 Pro<strong>of</strong> <strong>of</strong> the assertion . . . . . . . . . . . . . . . . . . . . 179<br />
D.3 Producing a ternary tree from a list . . . . . . . . . . . . . . . . 180<br />
D.3.1 Operations . . . . . . . . . . . . . . . . . . . . . . . . . . 180<br />
D.3.2 Pro<strong>of</strong> . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 180<br />
D.4 Producing a ternary tree from a split list . . . . . . . . . . . . . . 182<br />
D.4.1 Pro<strong>of</strong> . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 182<br />
D.5 Comparing the pro<strong>of</strong>s . . . . . . . . . . . . . . . . . . . . . . . . 184<br />
E <strong>Obfuscation</strong> Example 185<br />
5