mGuard Dokumentation - Innominate Security Technologies AG
mGuard Dokumentation - Innominate Security Technologies AG
mGuard Dokumentation - Innominate Security Technologies AG
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
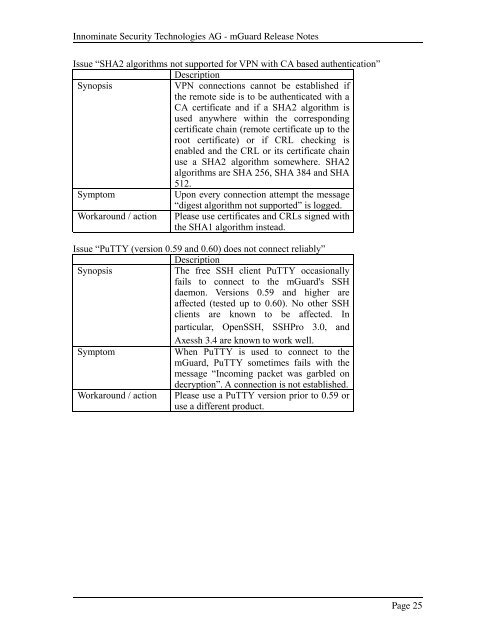
<strong>Innominate</strong> <strong>Security</strong> <strong>Technologies</strong> <strong>AG</strong> <strong>mGuard</strong> Release Notes<br />
Issue “SHA2 algorithms not supported for VPN with CA based authentication”<br />
Description<br />
Synopsis<br />
VPN connections cannot be established if<br />
the remote side is to be authenticated with a<br />
CA certificate and if a SHA2 algorithm is<br />
used anywhere within the corresponding<br />
certificate chain (remote certificate up to the<br />
root certificate) or if CRL checking is<br />
enabled and the CRL or its certificate chain<br />
use a SHA2 algorithm somewhere. SHA2<br />
algorithms are SHA 256, SHA 384 and SHA<br />
512.<br />
Symptom<br />
Upon every connection attempt the message<br />
“digest algorithm not supported” is logged.<br />
Workaround / action Please use certificates and CRLs signed with<br />
the SHA1 algorithm instead.<br />
Issue “PuTTY (version 0.59 and 0.60) does not connect reliably”<br />
Description<br />
Synopsis<br />
The free SSH client PuTTY occasionally<br />
fails to connect to the <strong>mGuard</strong>'s SSH<br />
daemon. Versions 0.59 and higher are<br />
affected (tested up to 0.60). No other SSH<br />
clients are known to be affected. In<br />
particular, OpenSSH, SSHPro 3.0, and<br />
Axessh 3.4 are known to work well.<br />
Symptom<br />
When PuTTY is used to connect to the<br />
<strong>mGuard</strong>, PuTTY sometimes fails with the<br />
message “Incoming packet was garbled on<br />
decryption”. A connection is not established.<br />
Workaround / action Please use a PuTTY version prior to 0.59 or<br />
use a different product.<br />
Page 25