Infosecurity Professional - Issue 9 - ISC
Infosecurity Professional - Issue 9 - ISC
Infosecurity Professional - Issue 9 - ISC
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
trating on brain surgery,” he explains.<br />
“Humans are part of the IT infrastructure,<br />
and the big mistake we’ve<br />
been making so far is to consider them<br />
separate,” Davidoff says. She places more<br />
of the blame on business executives,<br />
however. “The problem with managing<br />
employees is managing the motivation of<br />
the company itself,” she says. And at this<br />
point, many companies are motivated to<br />
create policy—not enforce it. “They’re<br />
still in the position that if numbers get<br />
stolen and nobody finds out about it<br />
outside of the organization, they don’t<br />
care—because they don’t have an incentive<br />
to,” she adds.<br />
How To Get It Right<br />
Although it’s impossible to write a<br />
string of code that will stop someone<br />
in marketing from spilling company<br />
secrets, there are ways to address the<br />
human side of security. Stewart recommends<br />
using psychology—specifically,<br />
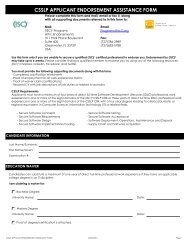
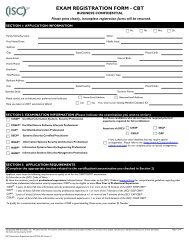
Use yoUr CIssP to save tIme<br />
and money.<br />
Qualify and redeem one seminar waiver for a savings of approximately $5,000.<br />
This program can be completed in as little as 15 months.<br />
Developed and taught by leaders in the field and backed by 189 years of<br />
academic heritage, this program enhances your technical and business<br />
management expertise as you gain consultancy experience through an<br />
organization-wide integrated information security project. Customize your<br />
degree with a specialization in either Business Continuity Management or<br />
Managing Cyber Crime and Digital Incidents.<br />
Norwich University was among the first 23 institutions to receive<br />
the National Security Agency’s designation as a Center of Academic Excellence<br />
in Information Assurance Education.<br />
To learn more please visit<br />
www.msia.norwich.edu/isc<br />
operant conditioning—to promote real<br />
behavioral change.<br />
In layman’s terms, operant conditioning<br />
is like the carrot-and-stick model<br />
of reward and punishment for behavior:<br />
You push for information security<br />
compliance by either punishing bad<br />
behavior or rewarding good. Operant<br />
conditioning shows that the effects of<br />
punishments and rewards are not symmetrical.<br />
Punishments must be consistently<br />
applied to be effective, whereas<br />
rewards can still be effective even if they<br />
are rare or intermittent.<br />
Stewart posits that you’re better off<br />
focusing on rewards. “Fear and the<br />
threat of sanctions are incentives not<br />
to report incidents,” he says. Another<br />
problem with the stick approach is that<br />
the punishment must be consistent to be<br />
effective—something that can be tough<br />
for many organizations. “Noncompliance<br />
may be difficult to detect, or punishment<br />
may not be viable for some user<br />
groups, such as customers,” Stewart says.<br />
“The use of praise or reward offers an<br />
organization a way of avoiding expensive<br />
auditing systems to consistently detect<br />
noncompliant behavior,” he says.<br />
Williamson agrees the carrot is the<br />
better option. “Rather than saying, ‘If<br />
you do this bad thing, here’s what will<br />
happen,’ we have found just the opposite<br />
to be effective,” he says. Take passwords<br />
as an example: Instead of punishing<br />
employees for using “12345” as a password,<br />
he recommends providing examples<br />
of what good passwords are—and<br />
rewarding employees who then follow<br />
those examples.<br />
It’s helpful to appeal to employees<br />
on a human level. Such security training<br />
“should describe how it will benefit<br />
the employee personally as opposed to<br />
the company,” Williamson says. “The<br />
same security countermeasures or the<br />
same best business practices that you’re<br />
asking your employees to practice at<br />
work—they should really practice those<br />
in their homes as well.” Rather than tell<br />
users to be wary of unfamiliar e-mail<br />
because it could negatively affect the<br />
company’s bottom line, explain to them<br />
that such behavior will ultimately affect<br />
their own.<br />
Smith uses similar tactics, but takes<br />
things a step further, appealing to a per-<br />
ISSUE NUMBER 9 InfoSecurity <strong>Professional</strong> 11<br />
IA 4.625X7_ May 28 09.indd 1<br />
5/28/09 9:59:01 AM