Infosecurity Professional - Issue 9 - ISC
Infosecurity Professional - Issue 9 - ISC
Infosecurity Professional - Issue 9 - ISC
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
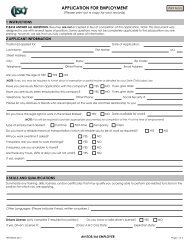
First Things First<br />
Rich Baich, CISSP, CISM, and principal<br />
at Deloitte & Touche LLP, was CISO with<br />
data broker ChoicePoint in 2005 when a<br />
significant case of fraud at the company<br />
unleashed a firestorm.<br />
Baich says the fraud stemmed from a<br />
Nigerian national who entered the U.S.<br />
illegally and obtained a business license<br />
using doctored phone and utility bills, and<br />
then became a valid user of ChoicePoint’s<br />
credit service. Once he was an authorized<br />
customer, he was able to access enough<br />
personal information—such as names,<br />
addresses and Social Security numbers—<br />
to carry out malicious, fraudulent acts<br />
including identity theft.<br />
“That was a direct relationship with<br />
someone who became a valid user of<br />
credit services,” says Baich. “And it was<br />
one of the shots heard around the world.”<br />
Published reports indicate the breach<br />
compromised the information of an<br />
estimated 163,000 people and resulted in<br />
800 cases of identity fraud. ChoicePoint<br />
was ordered to pay $10 million in civil<br />
penalties, and $5 million to consumers.<br />
One of the biggest lessons Baich<br />
learned: to institute an appropriate incident<br />
response and assemble the best<br />
team, you must clearly spell out what an<br />
incident is. “How an organization defines<br />
an incident is at the core of how they<br />
develop a response program,” he says.<br />
Brandon Dunlap, managing director<br />
of research at Brightfly, an information<br />
security advisory and research firm,<br />
agrees. He suggests defining each type of<br />
incident—from an employee participating<br />
in online gambling at work to a major<br />
denial-of-service attack—and then using<br />
those definitions to create a “triage map.”<br />
The map should describe each type of<br />
incident, the individuals or teams who<br />
should be involved in the response, and<br />
the processes included in the response.<br />
“The point of the triage map is to<br />
ensure that your countermeasures are<br />
commensurate with what is at risk,” says<br />
Dunlap. An employee downloading pornography,<br />
for example, would not likely<br />
carry the same risk as a hack attack on<br />
the company servers.<br />
Early Detection is Critical<br />
Once your plan is defined, you should<br />
focus on early detection.<br />
In the past year, MANDIANT has<br />
responded to approximately 40 incidents<br />
involving everything from financerelated<br />
attacks to advanced persistent<br />
threats that are extremely complex in<br />
nature and that attack both commercial<br />
and government systems. If you want<br />
to catch these “cancers” early, Lee says,<br />
“50 percent of your time and discussions<br />
should be focused on determining<br />
whether you are detecting properly.”<br />
Typically, law enforcement is first to<br />
detect a data breach and report it to a<br />
business—and often the first to leak it to<br />
the press due to data breach notification<br />
laws. Lee suggests building relationships<br />
with law enforcement now, rather than in<br />
the midst of an incident. A side benefit is<br />
that they may be working on cybercrime<br />
investigations, and this knowledge could<br />
better help you prepare.<br />
But so much the better if your company<br />
is able to detect an incident first.<br />
Early internal detection gives you control<br />
in terms of mitigating damage to<br />
your business, partners and customers.<br />
(For instance, negative press surrounding<br />
the ChoicePoint incident harmed<br />
the company’s reputation and led to an<br />
immediate 10 percent drop in its stock<br />
value.) “You must have individuals manning<br />
your systems who are truly dedicated<br />
to monitoring your network for<br />
potential evil that is out there and running<br />
rampant,” says Lee.<br />
Lee suggests housing all applications<br />
and resources in one building. This centralized<br />
approach requires a cultural shift<br />
and “a ton of work,” he adds. For instance,<br />
the infrastructure group often manages<br />
company firewalls, while the security<br />
group manages intrusion detection centers.<br />
“These two groups don’t typically<br />
talk to one another,” Lee says. “So how<br />
can you correlate data between them?”<br />
Letting go of certain gear and services<br />
is a necessary part of the process.<br />
“When [someone else] takes over it can<br />
be like swallowing a bitter pill, but it’s the<br />
only way to effectively monitor your network,”<br />
says Lee.<br />
The Response Team<br />
Hansen advises putting together a security<br />
team that works together seamlessly<br />
and executes quickly because “time is,<br />
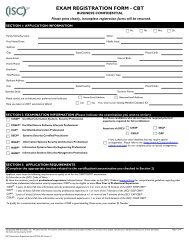
The Ingredients to Incident Response<br />
Rich Baich, principal at Deloitte & Touche LLP, says organizations are more proficient at<br />
declaring and responding to incidents because they do a better job of fusing disparate<br />
data. According to Baich, the next level of maturity requires an organization to have<br />
appropriate intelligence collection techniques in place to collect data and perform<br />
analysis to be proactive in their approach rather than reactive. He defines appropriate<br />
incident response as the practice of detecting a problem, determining its cause,<br />
minimizing the damage it causes, resolving the problem, and documenting each step<br />
of the response for future reference.<br />
“Keep it simple, and check off each box as you respond to these incidents. That allows<br />
you to gather a proper chain of evidence if there’s a need to prosecute someone,” he says.<br />
“Good, diligent practices not only demonstrate a focused response, but also allow you to<br />
go back and review for lessons learned, or identify critical steps that were missed.”<br />
Following are what Baich considers essential steps for an immediate data breach<br />
response action plan:<br />
1. Assemble the response team<br />
2. Review and evaluate the report prepared by the investigation team<br />
3. Isolate and contain the incident<br />
4. Determine the level of severity<br />
5. Assess the legal and financial consequences<br />
6. Implement escalation and notification procedures<br />
ISSUE NUMBER 9 InfoSecurity <strong>Professional</strong> 15