Security of Radioactive Sources in Radiation Facilities
Security of Radioactive Sources in Radiation Facilities
Security of Radioactive Sources in Radiation Facilities
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
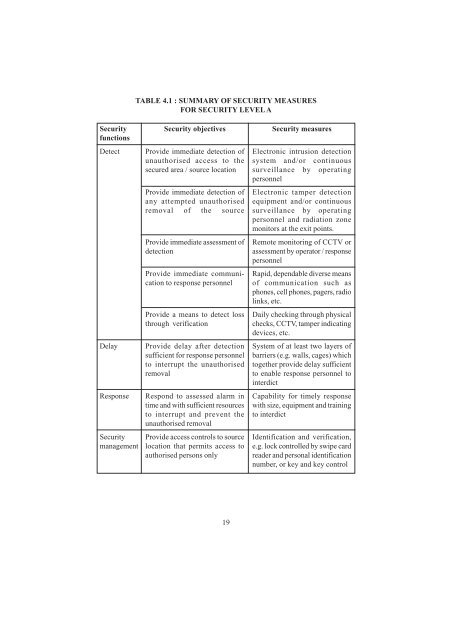
TABLE 4.1 : SUMMARY OF SECURITY MEASURES<br />
FOR SECURITY LEVEL A<br />
<strong>Security</strong><br />
functions<br />
Detect<br />
Delay<br />
Response<br />
<strong>Security</strong><br />
management<br />
<strong>Security</strong> objectives<br />
Provide immediate detection <strong>of</strong><br />
unauthorised access to the<br />
secured area / source location<br />
Provide immediate detection <strong>of</strong><br />
any attempted unauthorised<br />
removal <strong>of</strong> the source<br />
Provide immediate assessment <strong>of</strong><br />
detection<br />
Provide immediate communication<br />
to response personnel<br />
Provide a means to detect loss<br />
through verification<br />
Provide delay after detection<br />
sufficient for response personnel<br />
to <strong>in</strong>terrupt the unauthorised<br />
removal<br />
Respond to assessed alarm <strong>in</strong><br />
time and with sufficient resources<br />
to <strong>in</strong>terrupt and prevent the<br />
unauthorised removal<br />
Provide access controls to source<br />
location that permits access to<br />
authorised persons only<br />
<strong>Security</strong> measures<br />
Electronic <strong>in</strong>trusion detection<br />
system and/or cont<strong>in</strong>uous<br />
surveillance by operat<strong>in</strong>g<br />
personnel<br />
Electronic tamper detection<br />
equipment and/or cont<strong>in</strong>uous<br />
surveillance by operat<strong>in</strong>g<br />
personnel and radiation zone<br />
monitors at the exit po<strong>in</strong>ts.<br />
Remote monitor<strong>in</strong>g <strong>of</strong> CCTV or<br />
assessment by operator / response<br />
personnel<br />
Rapid, dependable diverse means<br />
<strong>of</strong> communication such as<br />
phones, cell phones, pagers, radio<br />
l<strong>in</strong>ks, etc.<br />
Daily check<strong>in</strong>g through physical<br />
checks, CCTV, tamper <strong>in</strong>dicat<strong>in</strong>g<br />
devices, etc.<br />
System <strong>of</strong> at least two layers <strong>of</strong><br />
barriers (e.g. walls, cages) which<br />
together provide delay sufficient<br />
to enable response personnel to<br />
<strong>in</strong>terdict<br />
Capability for timely response<br />
with size, equipment and tra<strong>in</strong><strong>in</strong>g<br />
to <strong>in</strong>terdict<br />
Identification and verification,<br />
e.g. lock controlled by swipe card<br />
reader and personal identification<br />
number, or key and key control<br />
19