- Page 3 and 4: CIICT 2009Proceedings of the China-
- Page 5 and 6: ForewordOn behalf of the organising
- Page 7 and 8: TABLE OF CONTENTSSection 1A: ANTENN
- Page 9 and 10: Section 3B: COMPUTER VISION 133A ne
- Page 11 and 12: Section 1AANTENNAS AND CIRCUITS 11
- Page 13 and 14: A block diagram of the platform is
- Page 15 and 16: These two paths are averaged to red
- Page 18 and 19: 4 mm -10 0 , -8 0 , -3 mm -8 0 , -6
- Page 20 and 21: The results show that the separatio
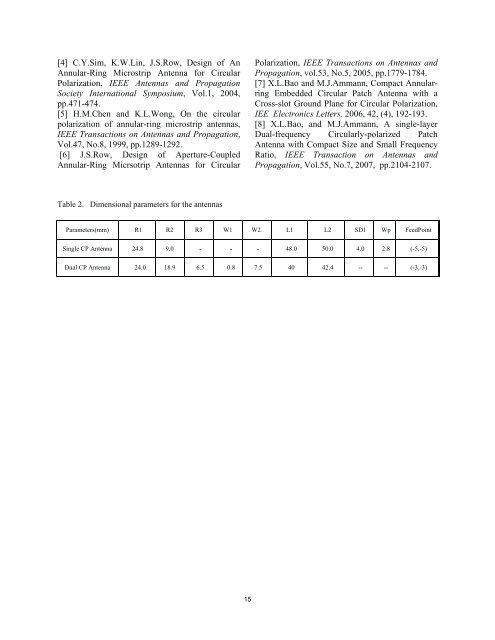
- Page 22 and 23: same size of annular-ring outer rad
- Page 26 and 27: Section 1BLOCATION-BASED SYSTEMS16
- Page 28: device in relation to the objects w
- Page 31 and 32: segments. The process of data colle
- Page 33 and 34: Wiimote as a Navigation tool for Pe
- Page 35 and 36: Feedback Control Models and Their A
- Page 37 and 38: A. User FeedbackBecause pedestrians
- Page 39 and 40: Tram and Bus Tracker: A Dynamic Web
- Page 41 and 42: departure times are quoted in the p
- Page 43 and 44: Section 1CSIGNAL PROCESSING33
- Page 45 and 46: itself modified in a controlled man
- Page 47 and 48: human hearing range of 100 Hz to 20
- Page 49 and 50: value used as a basis for calculati
- Page 51 and 52: USING CONVOLUTIVE NON-NEGATIVE MATR
- Page 53 and 54: Equation 5 is a summation of convol
- Page 55 and 56: 6. RESULTS AND DISCUSSIONThe result
- Page 57 and 58: Using Apodization to improve the pe
- Page 59 and 60: Notice too in Figure 2 that at the
- Page 61 and 62: aised to a cubic power, α =3, with
- Page 63 and 64: The spectrum of this pulse train is
- Page 65 and 66: −1( + 1) + log ( I′( m)) − (
- Page 67 and 68: Wireless Billboard Channels over T-
- Page 69 and 70: 10 0 SNR[dB]10 -1IPDC mode IPacket
- Page 71 and 72: RF SDR for Wideband PMRLing Gao, Ro
- Page 73 and 74: RxSensitivity(dBm)Efficiency(bits/H
- Page 75 and 76:
way. This will limit our ability to
- Page 77 and 78:
Q-Learning for Cognitive RadiosNeil
- Page 79 and 80:
the time and another action is chos
- Page 81 and 82:
network reduced as the agents neare
- Page 83 and 84:
assignment, so much so as to pursue
- Page 85 and 86:
Extracting Localised Mobile Activit
- Page 87 and 88:
localisation is almost exclusively
- Page 89 and 90:
s(k)s (k)s b (k)s f (k)Geo-Spacial
- Page 91 and 92:
BAB4123A(b) Sampled at 12.5s (c) Sa
- Page 93 and 94:
Evaluating Twitter for Use in Envir
- Page 95 and 96:
API provides geocoding based on a u
- Page 97 and 98:
Research on Unmanned Airship Low-al
- Page 99 and 100:
f ⋅Wf ⋅ 445.5H = = = 299mN ⋅
- Page 101 and 102:
control measures and so on [13, 14]
- Page 103 and 104:
There are forty points be selected
- Page 105 and 106:
TABLE III.SPREADING RATES OF SANDY
- Page 107 and 108:
Section 2CCOMPUTER NETWORKS 197
- Page 109 and 110:
One major wireless communication ri
- Page 111 and 112:
Fig. 5.1: Block Diagram of DPDC SCA
- Page 113 and 114:
e more If RT Linux takes the action
- Page 115 and 116:
9 CONCLUSIONSCADA system is a commu
- Page 117 and 118:
y 1pky s kInterleaverRSC encoderRSC
- Page 119 and 120:
BER10 −1 10 −20.0 dB0.5 dB10
- Page 121 and 122:
fragment distribution of some popul
- Page 123 and 124:
paper. [Online]. Available:http://w
- Page 125 and 126:
Research on the Gain flatness of Fi
- Page 127 and 128:
iκmlm-iΦm-2 iψiγαPPm1 2em43= e
- Page 129 and 130:
ISIS - Urban Radio plan and time-va
- Page 131 and 132:
Fig4. Prediction of radio propagati
- Page 133 and 134:
Investigation of Dispersive Fading
- Page 135 and 136:
ias points and cause the dispersive
- Page 137 and 138:
with the frequency response graphs
- Page 139 and 140:
An Efficient Consolidated Authentic
- Page 141 and 142:
not applicable here, because the au
- Page 143 and 144:
Section 3BCOMPUTER VISION133
- Page 145 and 146:
practical application work, it is a
- Page 147 and 148:
edge is complex, the edge detected
- Page 149 and 150:
2 Theory of G1 continuity condition
- Page 151 and 152:
the basis functions of B-spline. Wi
- Page 153 and 154:
search algorithm [14]. A HMM is a c
- Page 155 and 156:
vector with a range of different wi
- Page 157 and 158:
frame is reached (based on either p
- Page 159 and 160:
Section 3CGEOSENSORS149
- Page 161 and 162:
communication overhead involved. Ou
- Page 163 and 164:
in the distance results in a decrea
- Page 165 and 166:
TABLE ICROSS-CORRELATION BASED PHAS
- Page 167 and 168:
Wavelength modulated off-axis integ
- Page 169 and 170:
πwhere B(P,T) g[ v v0 acos(u)]co
- Page 171 and 172:
[5] Keefe, A.O’, Deacon, D.A.G.,
- Page 173 and 174:
One example of a remote sensing sat
- Page 175 and 176:
5. References[1] The Adaptive Senso
- Page 177 and 178:
P output portsCarriedF IF N Output
- Page 179 and 180:
Blocking Probability10 -210 -310 -4
- Page 181 and 182:
Design of Integrated Stacked Spiral
- Page 183 and 184:
The whole structure consists of 10
- Page 185 and 186:
Equivalent Circuit Modeling for On-
- Page 187 and 188:
substrate effect and distributed ef
- Page 189 and 190:
Real(Y 1,1 )Imag(Y 1,1 )Real(Y 1,2
- Page 191 and 192:
Assessing Power Saving Techniques a
- Page 193 and 194:
Streaming andLocal PlaybackTABLE IE
- Page 195 and 196:
Battery Level [%]Battery Level [%]B
- Page 197 and 198:
V. CONCLUSION AND FUTURE WORKThe go
- Page 199 and 200:
Figure 1 Multiple network selection
- Page 201 and 202:
learner device has access to. It al
- Page 203 and 204:
Figure 4b Estimated price for time
- Page 205 and 206:
Mobile Mobile Device. A SOA Approac
- Page 207 and 208:
A Blind Detection Method of Non-Per
- Page 209 and 210:
( t) = s( t)n( t)mˆ 4x( 0,0,τ )x
- Page 211 and 212:
Power Consumption Analysis of Bluet
- Page 213 and 214:
Fig.4 where the recover timing wind
- Page 215 and 216:
the slave device always receive the
- Page 217 and 218:
shortcomings are discussed. In addi
- Page 219 and 220:
Error ModelMarco Fiero packageWired
- Page 221 and 222:
#Bandwidth (median, Mbps)Video Cros
- Page 223 and 224:
Quality of Service in IMS based Con
- Page 225 and 226:
3.2 CNF and CSCFCNF is an Applicati
- Page 227 and 228:
User BGF PD-FE CSCF CNF(AS)HSSConte
- Page 229 and 230:
The Enhanced Dv-Hop Algorithm in Ad
- Page 231 and 232:
Figure 1: Node distribution for Dv-
- Page 233 and 234:
Figure 1. Class Design of PDG Passa
- Page 235 and 236:
Figure 4. PDG of IPv4 Packet Forwar
- Page 237 and 238:
Segmentation and three-dimensional
- Page 239 and 240:
[17], and out-of-focus features the
- Page 241 and 242:
Figure 9. A,B are thresholds of Fig
- Page 243 and 244:
[22] W. E. Lorensen and H. W. Cline
- Page 245 and 246:
second chirp and the constant facto
- Page 247 and 248:
2009 China-Ireland International Co
- Page 249 and 250:
2009 China-Ireland International Co
- Page 251 and 252:
Review of Twin Reduction and Twin R
- Page 253 and 254:
Advances were made in understanding
- Page 255 and 256:
5[48] J.C.H. Spence, X. Zhang and W
- Page 257 and 258:
Generating Initial Codebook of Vect
- Page 259 and 260:
Figure 2. Training points within a
- Page 261 and 262:
this case is quite small. So, from
- Page 263 and 264:
the success of the GeneRepair templ
- Page 265 and 266:
When the results are next sampled a
- Page 267 and 268:
One central element of research whi
- Page 269 and 270:
REFERENCES:[1] Anderson, T. (Ed.) (
- Page 271 and 272:
as stiffness, friction and penetrab
- Page 273 and 274:
Table 1. Algorithms’ PerformanceA
- Page 275:
2create small corpus subsets. Most