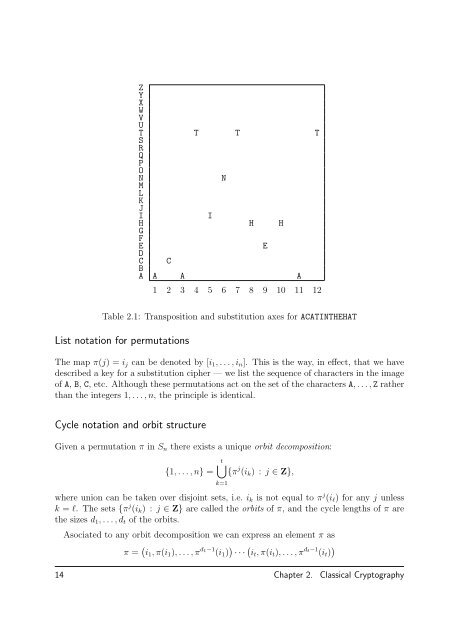
As a special case, consider 2-character polygrams, so thatAA = (0, 0), . . . , ZY = (25, 24), ZZ = (25, 25).The matrix A given by ( 1 821 3and vector v = (13, 14) defines a map)AA = ( 0, 0) ↦→ (13, 14) = NO..ZY = (25, 24) ↦→ (18, 23) = WAZZ = (25, 25) ↦→ (18, 23) = RDwhich is a simple substitution on the 2-character polygrams. Note that the number ofaffine ciphers is much less than all possible substutions, but grows exponentially in thenumber n of characters.2.2 Transposition CiphersRecall that a substitution cipher permutes the characters of the plaintext alphabet, ormay, more generally, map the plaintext characters into a different ciphertext alphabet. Ina transposition cipher, the symbols of the plaintext remain the same unchanged, but theirorder is permuted by a permutation of the index positions. Unlike substitution ciphers,transposition ciphers are block ciphers.The relation between substitution ciphers and transposition ciphers is illustrated in Table2.1. The characters and their positions of the plaintext string ACATINTHEHAT appear ina graph with a character axis c and a position index i for the 12 character block 1 ≤ i ≤ n.We represented as a graph a substitution cipher (with equal plaintext and ciphertext alphabets)is realised as a permutation of the rows of the array, while a transposition cipheris realised by permuting the columns in fixed size blocks, in this case 12.Permutation groupsThe symmetric group S n is the set of all bijective maps from the set {1, . . . , n} to itself,and we call an elements π of S n a permutation. We denote the n-th composition of π withitself by π n . As a function write π on the left, so that the image of j is π(j). An elementof S n is called a transposition if and only if it exhanges exactly two elements, leaving allothers fixed.2.2. Transposition Ciphers 13
ZYXWVUT T T TSRQPONNMLKJIIH H HGFEEDC CBA A A A1 2 3 4 5 6 7 8 9 10 11 12Table 2.1: Transposition and substitution axes for ACATINTHEHATList notation for permutationsThe map π(j) = i j can be denoted by [i 1 , . . . , i n ]. This is the way, in effect, that we havedescribed a key for a substitution cipher — we list the sequence of characters in the imageof A, B, C, etc. Although these permutations act on the set of the characters A, . . . , Z ratherthan the integers 1, . . . , n, the principle is identical.Cycle notation and orbit structureGiven a permutation π in S n there exists a unique orbit decomposition:{1, . . . , n} =t⋃{π j (i k ) : j ∈ Z},k=1where union can be taken over disjoint sets, i.e. i k is not equal to π j (i l ) for any j unlessk = l. The sets {π j (i k ) : j ∈ Z} are called the orbits of π, and the cycle lengths of π arethe sizes d 1 , . . . , d t of the orbits.Asociated to any orbit decomposition we can express an element π asπ = ( i 1 , π(i 1 ), . . . , π d 1−1 (i 1 ) ) · · · (it , π(i t ), . . . , π dt−1 (i t ) )14 Chapter 2. Classical <strong>Cryptography</strong>
- Page 1 and 2: Author (David R. Kohel) /Title (Cry
- Page 4 and 5: CONTENTS1 Introduction to Cryptogra
- Page 6: PrefaceWhen embarking on a project
- Page 10 and 11: information. We introduce here some
- Page 12 and 13: ut strings in A ∗ map injectively
- Page 14 and 15: CHAPTERTWOClassical Cryptography2.1
- Page 16 and 17: LV MJ CW XP QO IG EZ NB YH UA DS RK
- Page 20 and 21: Note that if d k = 1, then we omit
- Page 22: ExercisesSubstitution ciphersExerci
- Page 25 and 26: Ciphertext-only AttackThe cryptanal
- Page 27 and 28: of size n, suppose that p i is the
- Page 29 and 30: Note that ZKZ and KZA are substring
- Page 31: Checking possible keys, the partial
- Page 34 and 35: sage: X = pt.frequency_distribution
- Page 36 and 37: CHAPTERFOURInformation TheoryInform
- Page 38 and 39: For each of these we can extend our
- Page 40 and 41: in terms of the cryptosystem), then
- Page 42 and 43: CHAPTERFIVEBlock CiphersData Encryp
- Page 44 and 45: Deciphering. Suppose we begin with
- Page 46 and 47: The Advanced Encryption Standard al
- Page 48 and 49: 1. Malicious substitution of a ciph
- Page 50 and 51: locks M j−1 , . . . , M 1 as well
- Page 52: where X = K ⊕ M = (X 1 , X 2 , X
- Page 55 and 56: 6.2 Properties of Stream CiphersSyn
- Page 57 and 58: Exercise. Verify that the equality
- Page 59 and 60: n 2 n − 11 12 33 74 155 316 637 1
- Page 61 and 62: Exercise 6.6 In the previous exerci
- Page 63 and 64: Exercise 6.9 Compute the first 8 te
- Page 65 and 66: which holds since −4 = 17 + (−1
- Page 67 and 68: must therefore have a divisor of de
- Page 69 and 70:
Shrinking Generator cryptosystemLet
- Page 72 and 73:
CHAPTEREIGHTPublic Key Cryptography
- Page 74 and 75:
Initial setup:1. Alice and Bob publ
- Page 76 and 77:
We apply this rule in the RSA algor
- Page 78 and 79:
the discrete logarithm problem (DLP
- Page 80 and 81:
Man in the Middle AttackThe man-in-
- Page 82:
Exercise 8.6 Fermat’s little theo
- Page 85 and 86:
k < p − 1 with GCD(k, p − 1) =
- Page 88 and 89:
CHAPTERTENSecret SharingA secret sh
- Page 90:
using any t shares (x 1 , y 1 ), .
- Page 93 and 94:
sage-------------------------------
- Page 95 and 96:
sage: x.is_unit?Type:builtin_functi
- Page 97 and 98:
Python (hence SAGE) has useful data
- Page 99 and 100:
sage: n = 12sage: for i in range(n)
- Page 101 and 102:
sage: I = [55+i for i in range(3)]
- Page 103 and 104:
sage: I = [7, 4, 11, 11, 14, 22, 14
- Page 105 and 106:
ExercisesRead over the above SAGE t
- Page 107 and 108:
102
- Page 109 and 110:
Solution. The block length is the n
- Page 111 and 112:
Solution.below.The coincidence inde
- Page 113 and 114:
analysis of the each of the decimat
- Page 115 and 116:
arbitrary permutation of the alphab
- Page 117 and 118:
In order to understand naturally oc
- Page 119 and 120:
We do this by first verifying the e
- Page 121 and 122:
Solution.None provided.Linear feedb
- Page 123 and 124:
Multiplying each through by the con
- Page 125 and 126:
Solution. The linear complexity of
- Page 127 and 128:
If a, b, and c are as above, then f
- Page 129 and 130:
Exercise 8.5 Use SAGE to find a lar
- Page 131 and 132:
Solution. Now we can verify that e
- Page 133 and 134:
which has no common factors with p
- Page 135 and 136:
sage: p = 2^32+61sage: m = (p-1).qu
- Page 137 and 138:
sage: a5 := a^n5sage: c5 := c^n5sag
- Page 139 and 140:
The application of this function E
- Page 141 and 142:
5. (∗) How many elements a of G h
- Page 143:
1. The value f(0) of the polynomial